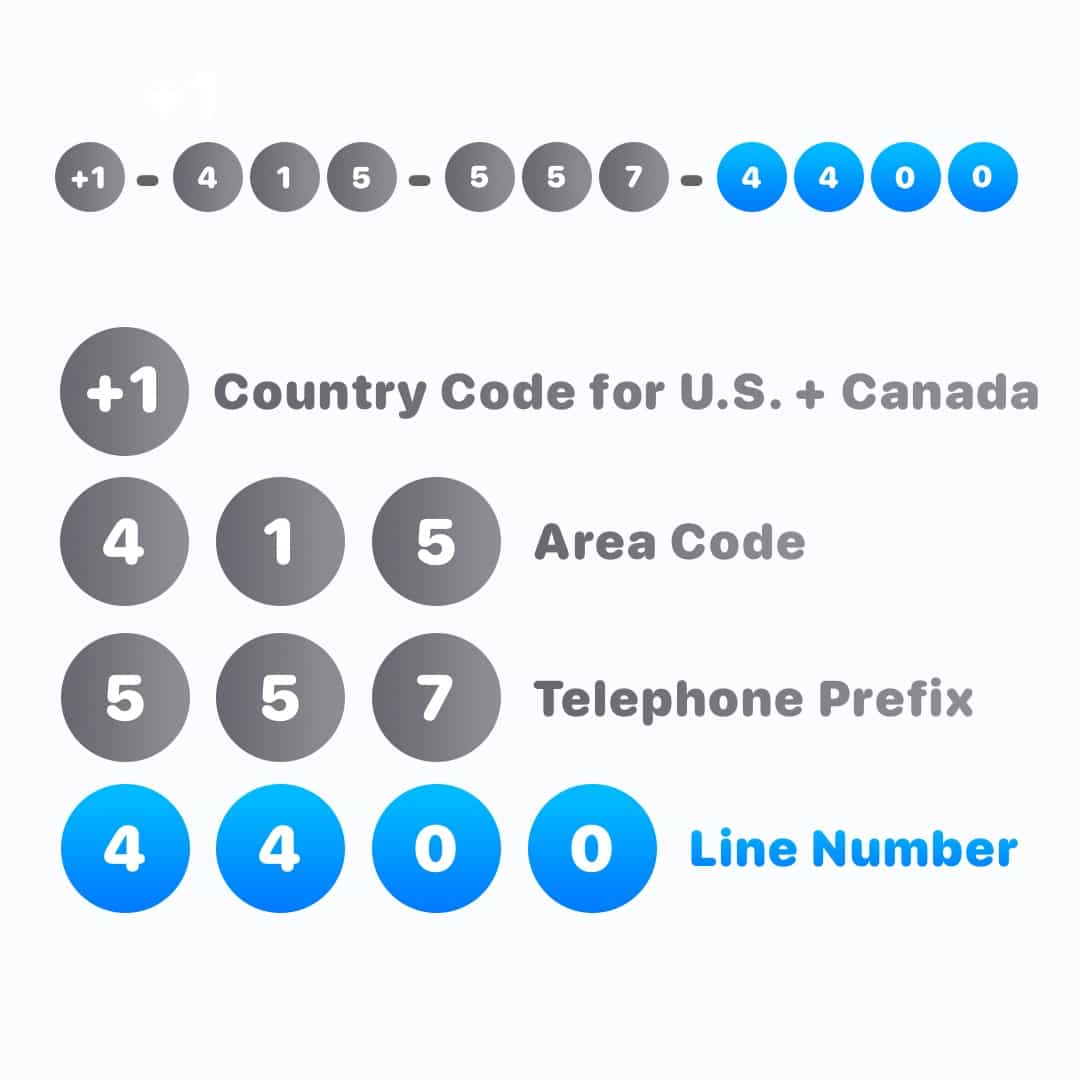
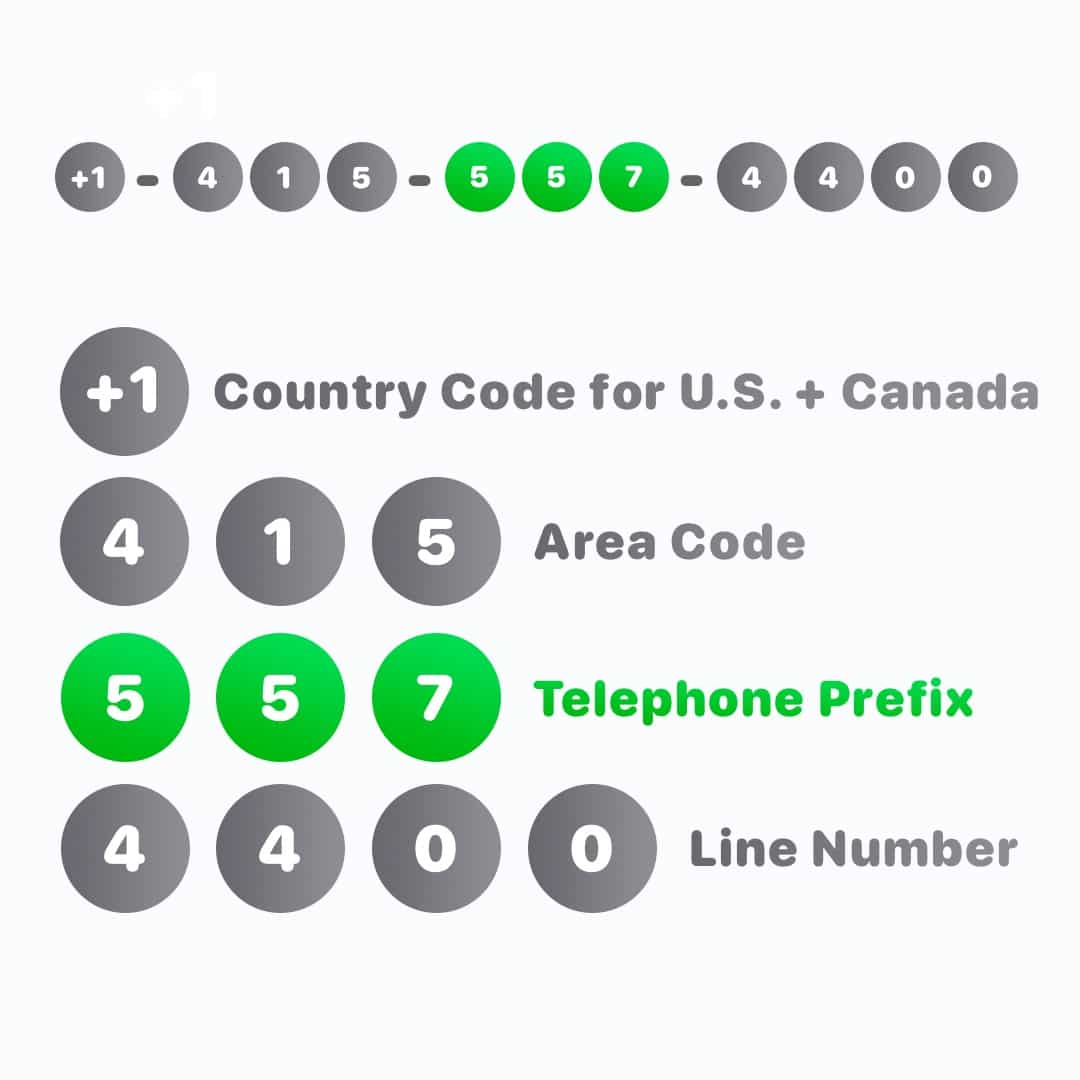
The Digital Signature: Identifying Autonomous Entities
In an increasingly connected world, the concept of a “phone number” serves as a unique identifier, a digital address that points to a specific entity within a vast network. Within the realm of advanced drone technology and innovation, this principle translates into a complex ecosystem of identification protocols essential for autonomous operation, seamless integration, and regulatory compliance. Every drone, from a micro-UAV to a sophisticated aerial platform for remote sensing, possesses a unique digital signature that defines its presence and capabilities within the operational airspace and data networks. This foundational layer of identification enables everything from secure communication to the attribution of collected data, underpinning the very fabric of autonomous flight and AI-driven functionalities. Without robust identification mechanisms, the potential for chaotic airspace, data integrity breaches, and operational inefficiencies would be immense, hindering the progression of truly intelligent aerial systems.
Unique Hardware and Software IDs
At the most granular level, each drone is endowed with unique hardware identifiers, akin to a device’s MAC address or a processor’s serial number. These immutable markers are embedded during manufacturing, providing a fundamental layer of distinction. Complementing this are software IDs, which manifest as unique registration numbers, cryptographic keys, or proprietary network addresses. For instance, in a drone swarm operating autonomously, each unit leverages these IDs to establish its identity within the collective, facilitating resource allocation, task distribution, and collision avoidance through shared positional awareness. These identifiers are crucial for verifying the authenticity of a drone, preventing unauthorized units from joining a mission, and ensuring that commands are directed to the correct recipient, critical for sensitive operations like precision agriculture or infrastructure inspection. The integration of secure element chips further enhances this by providing tamper-resistant storage for cryptographic keys and identity certificates, bolstering the integrity of the drone’s digital signature.
Network Addressing in Drone Swarms
The orchestration of drone swarms necessitates sophisticated network addressing schemes, far beyond simple IP addresses. In these complex systems, each drone acts as a node, requiring a unique address not only for individual communication but also for group messaging and dynamic role assignment. Technologies such as IPv6 are often employed, offering an expansive address space capable of accommodating vast numbers of interconnected UAVs. However, innovative approaches extend to mesh networking protocols, where drones dynamically discover and route data through neighboring units, creating resilient and self-healing communication networks. This distributed addressing ensures that even if certain nodes fail, the swarm maintains connectivity and operational coherence. Furthermore, specialized routing algorithms are developed to optimize communication pathways for low latency and high bandwidth, essential for real-time data exchange in applications like search and rescue or coordinated aerial displays, where precise timing and synchronized actions are paramount.
Regulatory Identification and Airspace Integration
The concept of a “phone number” extends to the regulatory domain, where drones must possess verifiable digital identities to operate legally and safely within national and international airspace. Systems for Remote ID (Remote Identification) are being developed globally, mandating that drones broadcast their unique identifier, location, and sometimes velocity, making them “visible” to air traffic management systems and law enforcement. This is critical for preventing unauthorized flights, ensuring accountability, and facilitating integration with traditional aviation. These digital identities are often linked to a pilot’s registration or an operator’s license, creating a clear chain of responsibility. Furthermore, initiatives like UTM (Unmanned Aircraft System Traffic Management) rely heavily on these unique identifiers to manage drone traffic flow, allocate airspace, and provide real-time conflict resolution services, establishing a virtual “phone book” of airborne entities that enables safer, more scalable autonomous operations across various industries.
Precision Beyond Coordinates: Tracking and Locating
Just as a phone number connects us to a specific individual, advanced drone technology relies on intricate systems to precisely identify, track, and locate not just the drone itself, but also its targets and surrounding environment. This goes far beyond mere GPS coordinates, delving into the realm of multi-dimensional recognition and real-time spatial awareness. For AI follow mode to be effective, or for autonomous flight to navigate complex urban landscapes, the drone must possess the capability to identify and maintain a ‘lock’ on dynamic subjects or predefined points of interest. This sophisticated identification process is critical for enabling intelligent interaction with the physical world, transforming raw sensor data into actionable information that drives autonomous decisions. The evolution of these tracking and locating capabilities forms the backbone of next-generation drone applications, pushing the boundaries of what is possible in aerial robotics and intelligent systems.
Advanced Sensor Fusion for Target Recognition
The “identification” of targets in a dynamic environment is a multi-modal challenge addressed through advanced sensor fusion. Drones integrate an array of sensors—including high-resolution optical cameras, thermal imagers, LiDAR, and radar—to create a comprehensive understanding of their surroundings. For instance, in an AI follow mode scenario, a drone might use a combination of optical tracking to identify the subject’s visual features, LiDAR to ascertain its depth and form, and even radar for velocity and direction in challenging light conditions. The data from these disparate sensors is then fused and processed by powerful onboard AI algorithms, which learn to recognize and distinguish between potential targets and background noise. This fusion allows for robust identification even when one sensor’s input is compromised, such as low light affecting an optical camera or heavy foliage obscuring LiDAR returns, ensuring a consistent and reliable “lock” on the intended subject.
AI-Driven Object Identification in Dynamic Environments
The ability of drones to “know what’s what” in real-time is pivotal for their advanced functionalities. AI-driven object identification, powered by deep learning and neural networks, allows drones to classify objects with remarkable accuracy, ranging from identifying specific individuals for AI follow mode to discerning various types of infrastructure damage during inspection flights. In autonomous flight, this means instantly recognizing and categorizing potential obstacles—be it a bird, another drone, or a tree branch—and predicting their trajectories to execute evasive maneuvers. For mapping and remote sensing, AI can automatically identify specific crop types, differentiate between healthy and diseased plants, or detect anomalies in geological formations. This constant, intelligent object identification is like the drone building a real-time, dynamic “contact list” of everything important in its operational sphere, making informed decisions based on what it “sees” and “understands.”
Real-time Communication Channels for Positional Data
Effective tracking and locating are inextricably linked to robust, real-time communication channels that transmit precise positional and identification data. For example, in swarm robotics or coordinated multi-drone operations, each unit continuously broadcasts its precise location, velocity, and identified targets to a central controller or directly to other swarm members. This allows the collective to build a shared operational picture, enabling synchronized actions or collaborative mapping efforts. Furthermore, for AI follow mode, the target itself might wear a small, lightweight beacon that actively communicates its position to the drone, augmenting visual tracking with a direct digital link. These communication channels often leverage advanced radio frequency technologies, secure data encryption, and low-latency protocols to ensure that critical identification and positional updates are delivered instantaneously and reliably, regardless of environmental interference or operational range.
AI’s Intelligent Connection: Decoding Interaction Protocols
Within the intricate tapestry of drone innovation, the concept of “what phone number is” resonates deeply with how Artificial Intelligence establishes and maintains intelligent connections, decoding interaction protocols for seamless operation. Just as a phone number enables direct communication, AI systems on drones employ sophisticated algorithms to “understand” and react to their environment, subjects, and human operators. This involves not just recognizing patterns but interpreting intentions and predicting behaviors, laying the groundwork for truly autonomous and intuitive drone interactions. Whether it’s a drone intuitively following a subject, navigating through complex airspace without human intervention, or processing vast datasets for actionable insights, the underlying principle is the AI’s ability to establish and maintain a purposeful “connection” with the relevant entities and data streams.

Machine Vision and Feature Extraction for Follow Mode
For AI follow mode, the drone’s “connection” to its subject is established primarily through advanced machine vision and feature extraction. Instead of a direct digital identifier like a phone number, the AI identifies its target by learning its unique visual characteristics. Deep neural networks are trained on vast datasets to recognize human forms, specific objects, or even individual faces. Feature extraction algorithms then pinpoint distinguishing attributes – color patterns, shape contours, movement dynamics – that differentiate the target from its background. The drone continuously extracts these features, comparing them against its learned model to maintain a persistent “lock,” even if the subject briefly moves behind an obstruction or changes orientation. This allows the drone to anticipate movement, maintain optimal framing for aerial filmmaking, or track assets for security monitoring, effectively “calling” and “staying connected” to its subject through visual intelligence.
Predictive Analytics for Autonomous Navigation
Autonomous flight demands that drones possess a profound understanding of their operational environment, which the AI achieves through predictive analytics. Here, the “phone number” metaphor extends to the AI’s ability to predict the “trajectory” or “next move” of dynamic elements within its airspace. By analyzing historical data, real-time sensor inputs (e.g., weather patterns, air traffic, ground obstacles), and learned behavioral models, the AI can forecast potential conflicts or optimal flight paths. For instance, in an urban delivery scenario, the drone’s AI might predict pedestrian movements, anticipate wind gusts, and identify temporary no-fly zones based on live event data, all while navigating towards its destination. This foresight allows the drone to make proactive adjustments, ensuring safety and efficiency, akin to knowing the “intent” behind a “phone call” before it’s even fully articulated.
Human-Machine Interface for Seamless Control
The human-machine interface (HMI) serves as the “communication device” through which operators interact with and control sophisticated drones. Innovative HMI designs aim to make this “connection” as intuitive and seamless as a phone conversation. This involves more than just joysticks and buttons; it encompasses gesture control, voice commands, and augmented reality (AR) interfaces that overlay critical flight information directly onto the operator’s view. For complex operations like remote sensing or mapping missions, operators can specify entire flight plans through touchscreens, with the AI translating high-level commands into precise flight parameters. The AI continuously provides feedback, reporting on drone status, mission progress, and detected anomalies, ensuring the human operator is always “on the line” with comprehensive situational awareness, thereby reducing cognitive load and enhancing operational precision.
Remote Sensing’s Data Fingerprint: Attributing Information
In the domain of remote sensing, the question “what phone number is” takes on a critical meaning related to data integrity, attribution, and traceability. Every piece of information collected by a drone — whether it’s an image, a spectral reading, or a LiDAR point cloud — carries a unique digital fingerprint, much like how a phone number uniquely identifies a caller or a data stream. This fingerprint ensures that data can be precisely linked to its origin, time, and specific operational parameters, establishing an unbreakable chain of provenance. For applications ranging from agricultural monitoring to environmental assessment and infrastructural inspection, the ability to accurately attribute and verify data is paramount for scientific validity, regulatory compliance, and informed decision-making. Without this sophisticated level of data identification, the vast quantities of information gathered by remote sensing drones would lose their contextual value and reliability.
Geospatial Tagging and Metadata Management
The fundamental “phone number” of remote sensing data is its geospatial tag, which precisely identifies the location and altitude from which each data point or image was acquired. Every pixel in an orthomosaic, every point in a LiDAR cloud, and every spectral reading is stamped with GPS coordinates, time, and sometimes even sensor orientation. This is complemented by rich metadata management, which includes details about the drone platform used, sensor calibration parameters, atmospheric conditions at the time of acquisition, and the mission objectives. This comprehensive digital record ensures that the data’s context is fully preserved, allowing researchers and analysts to accurately interpret findings, compare data over time, and reconstruct the exact circumstances of data collection. It’s the equivalent of having a detailed call record for every piece of information, ensuring full transparency and reproducibility in scientific and commercial applications.
Multispectral and Hyperspectral Data Linkage
When drones are equipped with advanced multispectral and hyperspectral sensors, the “identification” of data becomes even more nuanced. These sensors capture light across dozens or even hundreds of discrete spectral bands, revealing information invisible to the human eye. Each spectral measurement is intricately linked to its precise spatial location, creating a multi-dimensional dataset where every pixel has a unique spectral signature – its “spectral phone number.” For example, in precision agriculture, these signatures can identify specific crop health indicators, nitrogen levels, or the presence of pests and diseases long before they are visually apparent. In environmental monitoring, they can differentiate between various types of vegetation, soil composition, or water quality parameters. The challenge lies in accurately correlating these complex spectral fingerprints with their corresponding geographical coordinates and then reliably interpreting what these unique “calls” from the environment signify.
Blockchain for Data Integrity and Provenance
To further secure the “data fingerprint” and enhance trust in remote sensing information, innovative approaches are exploring the use of blockchain technology. By recording each data acquisition event as a cryptographic hash on an immutable distributed ledger, blockchain can provide an unalterable record of data provenance. This means that every step in the data lifecycle – from initial capture to processing, analysis, and sharing – can be securely traced and verified. This is particularly valuable for sensitive applications where data integrity is critical, such as regulatory compliance, insurance claims, or legal disputes involving environmental impact. Blockchain effectively acts as an incorruptible “public directory” for drone-collected data, ensuring that the “phone number” (the data’s unique identifier and context) cannot be tampered with, thereby establishing an unparalleled level of transparency and accountability.
The Evolving Directory: Future of Drone Identification and Interaction
As drone technology rapidly advances, the question “what phone number is” transcends its current interpretations and points towards future innovations in how drones are identified, how they interact, and how their data is managed across global systems. The exponential growth in the number of UAVs, coupled with increasingly complex autonomous operations, necessitates the development of sophisticated, standardized, and secure identification and communication protocols. This future “directory” will not only facilitate safer and more efficient airspace integration but also enable groundbreaking applications in areas like urban air mobility, global remote sensing networks, and decentralized drone swarms. The trajectory of drone innovation is defined by the continuous evolution of these digital identifiers and interaction paradigms, pushing towards a future where every drone has a clear, verifiable “identity” within a highly interconnected ecosystem.
Standardized Global Drone Identification Systems
The fragmented landscape of national drone registration and identification systems is giving way to the urgent need for standardized global protocols. Future innovations will likely involve internationally recognized digital identifiers, potentially leveraging biometrics for operator authentication and digital certificates for drone identity, similar to how secure websites use SSL. This universal “phone number” for drones would allow for seamless cross-border operations, simplified regulatory compliance, and enhanced security against malicious use. Organizations like ICAO (International Civil Aviation Organization) are working towards frameworks that establish a common language for drone identification, ensuring that an autonomous delivery drone in one country can be recognized and managed consistently across different jurisdictions, much like how international mobile numbers enable global communication.
Quantum-Resistant Communication Protocols
As the computational power of quantum computers grows, current encryption methods that protect drone communication and data identifiers are at risk. Future drone innovation will necessitate the adoption of quantum-resistant cryptographic algorithms to secure all forms of identification and interaction. This means developing new communication protocols that can withstand attacks from quantum computers, protecting drone control links, data transmissions, and the unique digital signatures that verify a drone’s identity. Implementing such robust security measures is paramount to preventing unauthorized access, ensuring the integrity of autonomous missions, and safeguarding sensitive remote sensing data against future cyber threats, ensuring that a drone’s “phone number” remains private and secure.
Decentralized Autonomous Organization (DAO) Models for Swarms
Looking further into the future, the concept of a “phone number” for drones might evolve into decentralized autonomous organization (DAO) models for drone swarms. In this paradigm, individual drones within a swarm could operate not just as nodes in a network but as autonomous agents within a self-governing entity. Each drone would have a unique identity, but its operational directives and resource allocation would be determined by consensus mechanisms within the swarm, governed by smart contracts on a blockchain. This would enable highly resilient, adaptable, and scalable autonomous operations, where the swarm itself operates with a collective “identity” and decision-making capability. This distributed intelligence could revolutionize complex tasks such as large-scale environmental monitoring, disaster response, and even space exploration, creating a truly distributed and self-organizing “network of numbers.”
