The intricate landscape of modern cybersecurity demands vigilance, expertise, and continuous adaptation. As digital infrastructures expand and threat actors grow more sophisticated, maintaining a robust Security Operations Center (SOC) has become an imperative for organizations of all sizes. However, the operational complexities, staffing challenges, and prohibitive costs associated with an in-house SOC often place it out of reach for many. This is where “SOC as a Service” (SOCaaS) emerges as a transformative innovation, democratizing advanced security operations and embodying a significant evolution in how technology delivers protection.
The Evolution of Security Operations in the Digital Age
For decades, the concept of a dedicated security operations center has been the gold standard for monitoring, detecting, and responding to cyber threats. A traditional SOC functions as a centralized command hub, staffed by security analysts, engineers, and incident responders who leverage an array of tools to safeguard an organization’s digital assets. Yet, the traditional model, while effective for large enterprises with substantial resources, faced increasing limitations in a rapidly evolving threat environment.

Traditional SOC Limitations
The primary hurdles for an in-house SOC include the severe cybersecurity talent shortage, which makes recruiting and retaining skilled professionals incredibly difficult and expensive. Furthermore, establishing a comprehensive SOC requires significant capital investment in hardware, software, and specialized infrastructure, followed by continuous operational expenses for licenses, updates, and maintenance. The 24/7 nature of threat monitoring also necessitates large teams working in shifts, a logistical and financial burden that many organizations, particularly small and medium-sized enterprises (SMEs), simply cannot bear. This creates a critical security gap, leaving many vulnerable to persistent and evolving cyber threats. The sheer volume of alerts generated by various security tools can also overwhelm human analysts, leading to alert fatigue and the potential for legitimate threats to be missed amidst the noise.
The Rise of the “as a Service” Model
The advent of cloud computing fundamentally reshaped the delivery of technology, giving rise to the “as a Service” (aaS) model. From Infrastructure as a Service (IaaS) to Software as a Service (SaaS) and Platform as a Service (PaaS), this paradigm shift enabled businesses to consume technology capabilities as a utility, rather than owning and managing the underlying infrastructure. This model champions scalability, flexibility, and cost-efficiency, providing access to cutting-edge technology without the heavy upfront investment or operational overhead. It was a natural progression for security operations to adopt this model, leading to the development of SOC as a Service. SOCaaS represents an innovative approach to security, leveraging external expertise, advanced technology stacks, and shared service models to provide robust cyber defense capabilities that would otherwise be unattainable for many organizations. It’s a prime example of how innovation in service delivery can democratize access to critical technologies.
Deconstructing SOC as a Service (SOCaaS)
SOCaaS providers deliver a comprehensive suite of security operations capabilities, often leveraging a multi-tenant cloud-native architecture. This managed service typically encompasses threat detection, monitoring, analysis, and response, all delivered remotely by a team of expert security professionals using advanced technological platforms.
Core Components and Offerings
At its heart, SOCaaS offers continuous monitoring of an organization’s IT environment, including network traffic, endpoints, cloud resources, and applications, for suspicious activities and indicators of compromise. Key offerings typically include:
- 24/7/365 Monitoring: Expert security analysts continuously monitor security events across an organization’s infrastructure.
- Threat Detection and Alerting: Utilizing sophisticated tools and human intelligence to identify real threats amidst millions of events, and notify clients promptly.
- Incident Response and Management: Guiding clients through the immediate steps to contain and remediate security incidents, or even performing these actions directly in some advanced offerings.
- Vulnerability Management: Identifying and prioritizing vulnerabilities within the system that could be exploited.
- Log Management and Analysis: Centralized collection, storage, and analysis of logs from various sources for security intelligence and forensic purposes.
- Compliance Reporting: Assisting organizations in meeting regulatory compliance requirements by providing audit trails and security posture reports.
- Threat Intelligence Integration: Leveraging global and industry-specific threat intelligence feeds to proactively identify emerging threats.
The Technology Stack Powering SOCaaS
The effectiveness of SOCaaS is rooted deeply in the sophisticated technology stack it employs. These providers invest heavily in cutting-edge tools and platforms that leverage the latest advancements in artificial intelligence, cloud computing, and automation to deliver superior security outcomes.
Cloud Infrastructure and Scalability
Cloud-native architecture is fundamental to SOCaaS. By operating in the cloud, providers can achieve unparalleled scalability, allowing them to rapidly onboard new clients and dynamically adjust resources to meet fluctuating demands without incurring significant hardware costs. This infrastructure also enables geographic redundancy and high availability, ensuring continuous service delivery and data resilience. The multi-tenant nature of cloud environments allows providers to achieve economies of scale, distributing the cost of expensive security tools and expert personnel across a broad client base, which directly translates into more affordable services for individual organizations.
Artificial Intelligence and Machine Learning
AI and Machine Learning (ML) are the bedrock of modern threat detection within SOCaaS. These technologies are crucial for processing vast quantities of security data – far more than human analysts could ever manually review. ML algorithms can identify subtle patterns and anomalies that indicate malicious activity, often before they escalate into full-blown breaches. They are trained on massive datasets of benign and malicious behaviors, allowing them to learn and adapt to new threats. AI-driven analytics can prioritize alerts, reduce false positives, and significantly improve the speed and accuracy of threat identification, making the security operations more efficient and effective. This predictive capability marks a significant innovation in cybersecurity defense.
Security Orchestration, Automation, and Response (SOAR)
SOAR platforms are a game-changer for SOCaaS, automating routine security tasks and orchestrating complex incident response workflows. Automation handles repetitive, mundane tasks such as collecting data, enriching alerts with threat intelligence, and performing initial containment actions. Orchestration connects disparate security tools and systems, allowing them to share information and act in concert. Response capabilities within SOAR enable predefined playbooks to execute actions automatically or with minimal human intervention, dramatically reducing response times from hours to minutes or even seconds. This efficiency not only frees up human analysts to focus on more complex investigations but also significantly reduces the window of opportunity for attackers.
Advanced Threat Intelligence Integration
Effective SOCaaS relies heavily on integrating real-time, actionable threat intelligence from various global and industry-specific sources. This intelligence provides context to alerts, helping analysts understand the nature of a threat, its origins, and potential impact. By correlating internal security events with external threat intelligence, SOCaaS providers can proactively identify indicators of compromise (IOCs) and tactics, techniques, and procedures (TTPs) used by known threat groups, enabling them to anticipate and defend against attacks more effectively. This continuous influx of external knowledge is a key innovation, allowing defense mechanisms to evolve at pace with the global threat landscape.
The Strategic Advantages and Innovation Drive of SOCaaS
SOCaaS is more than just outsourcing security; it represents a strategic innovation that empowers organizations to fortify their defenses, optimize resource allocation, and remain competitive in a digital-first world.
Bridging the Talent Gap
One of the most significant advantages of SOCaaS is its ability to effectively bridge the critical cybersecurity talent gap. Organizations gain immediate access to a team of highly skilled and experienced security professionals, including ethical hackers, incident responders, and forensic analysts, without the monumental challenge and expense of recruiting, training, and retaining them in-house. These teams often possess diverse expertise and are continuously updated on the latest threat vectors and defense strategies, providing a level of collective knowledge that few individual organizations could replicate. This access to top-tier human capital, combined with cutting-edge technology, is a powerful innovation.
Cost Efficiency and Predictable Spending
The subscription-based model of SOCaaS transforms security expenditure from a fluctuating capital investment to a predictable operational expense. This eliminates the need for significant upfront investments in hardware, software licenses, and infrastructure. Furthermore, organizations save on salaries, benefits, and training costs associated with an in-house security team. The shared service model allows providers to distribute the cost of advanced tools and technologies across multiple clients, making sophisticated security capabilities accessible at a fraction of the cost of building them internally. This financial innovation allows businesses to allocate their precious capital to core business development and growth.
Enhanced Threat Detection and Response Capabilities
By leveraging advanced technologies like AI/ML, SOAR, and robust threat intelligence, SOCaaS offers superior threat detection and faster response capabilities than what most organizations could achieve independently. The 24/7 monitoring ensures that threats are identified and addressed around the clock, minimizing the dwell time of attackers within a network. Rapid incident response significantly reduces the potential damage and disruption caused by a breach, protecting reputation, data, and financial stability. This comprehensive and proactive defense posture represents a significant leap in security effectiveness.
Focus on Core Business Innovation
By offloading the complex and demanding task of security operations to a specialized provider, organizations can free up their internal IT teams to focus on strategic initiatives that drive business innovation and growth. Instead of being bogged down by security alerts and patch management, internal teams can concentrate on developing new products, improving customer experiences, and optimizing operational efficiencies. This strategic shift allows businesses to fully embrace digital transformation without the burden of managing an ever-escalating security arms race.
Challenges and the Future Landscape of SOCaaS
While SOCaaS offers compelling advantages, organizations considering this innovative solution must also be aware of potential challenges and the future trajectory of the service.
Data Privacy and Compliance Considerations
When entrusting sensitive security data to a third-party provider, data privacy and compliance become paramount concerns. Organizations must meticulously vet SOCaaS providers to ensure they adhere to relevant industry regulations (e.g., GDPR, HIPAA, PCI DSS) and maintain robust data protection policies. Clear contractual agreements outlining data ownership, access, storage, and breach notification procedures are essential. This requires careful due diligence and a deep understanding of legal and regulatory frameworks surrounding data.
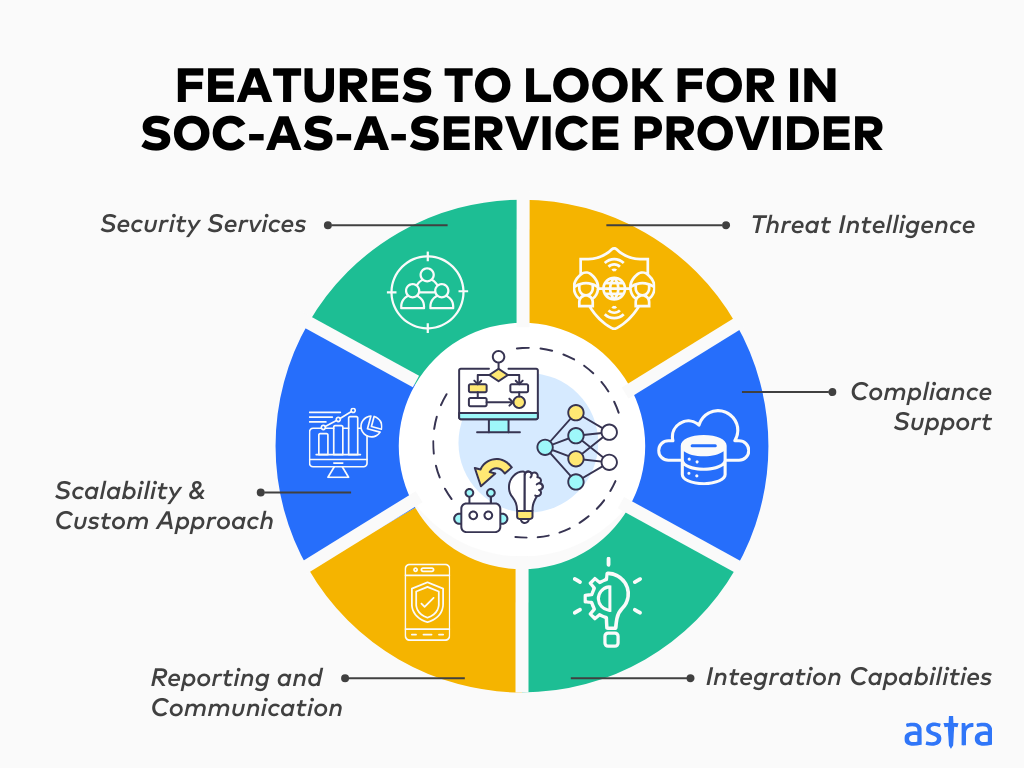
Vendor Selection and Integration
Choosing the right SOCaaS provider is a critical decision. Organizations need to assess providers based on their technical capabilities, experience, service level agreements (SLAs), scalability, and cultural fit. Seamless integration with existing IT infrastructure and security tools is also crucial to ensure comprehensive coverage and efficient operations. A robust proof of concept and clear communication channels are vital for a successful partnership.

Future Innovations: Proactive Defense and Predictive Analytics
The future of SOCaaS is poised for even greater innovation, driven by advancements in AI, predictive analytics, and contextual intelligence. We can expect to see SOCaaS solutions becoming even more proactive, moving beyond detection and response to predictive threat prevention. This will involve leveraging advanced behavioral analytics to anticipate potential attacks, identifying vulnerabilities before they are exploited, and implementing automated countermeasures at machine speed. The integration of highly sophisticated contextual awareness, combining business context with threat intelligence, will allow for more intelligent and prioritized responses. Furthermore, the rise of sovereign cloud solutions and specialized SOCaaS providers catering to highly regulated industries will likely shape the market, offering tailored solutions that meet stringent data residency and compliance requirements. This ongoing evolution underscores SOCaaS not merely as a service, but as a continuously evolving technological innovation at the forefront of cybersecurity.
