The Foundation of Local Drone Communication
In the intricate world of drone technology, where seamless communication is paramount for everything from basic flight control to advanced autonomous operations, fundamental networking protocols often work silently in the background, enabling the magic to happen. Among these, the Address Resolution Protocol (ARP) stands out as a critical, albeit often unheralded, component of any IP-based communication. For drones, which increasingly rely on Wi-Fi, Ethernet, or other IP-based links for their local network interactions, understanding ARP is essential to grasp the reliability, efficiency, and security of their operational frameworks.
ARP’s primary function is to translate logical addresses (IP addresses) into physical addresses (MAC addresses) on a local area network (LAN). Imagine a drone controller sending a command to a drone over a Wi-Fi network. While the controller knows the drone’s IP address, the underlying network hardware needs the drone’s unique Media Access Control (MAC) address to correctly deliver the data packet. ARP acts as the crucial intermediary, ensuring that data packets reach their intended destination within the local network segment. Without ARP, IP communication on local networks would be impossible, effectively crippling much of modern drone functionality.

Bridging Logical and Physical Addresses
Every device connected to an IP network has at least two key identifiers: an IP address and a MAC address. An IP address is a logical identifier assigned at the network layer, used for routing data across different networks. It’s akin to a postal address that helps mail get from one city to another. A MAC address, conversely, is a physical, hardware-encoded identifier unique to each network interface card (NIC) or Wi-Fi module. It operates at the data link layer and is used for direct communication between devices within the same local network, much like a specific house number on a street.
ARP’s role is to bridge this gap. When a drone’s ground control station (GCS) wants to send a data packet to the drone, and it only knows the drone’s IP address, it needs to discover the drone’s corresponding MAC address. This translation is fundamental for the data packet to be encapsulated correctly and put onto the physical network medium (e.g., Wi-Fi radio waves). ARP essentially performs a lookup, asking, “Who has this IP address? Tell me your MAC address.” The device with that IP address then responds with its MAC address, allowing the sender to build a complete data link layer frame and transmit the data.
How ARP Works: A Step-by-Step Overview
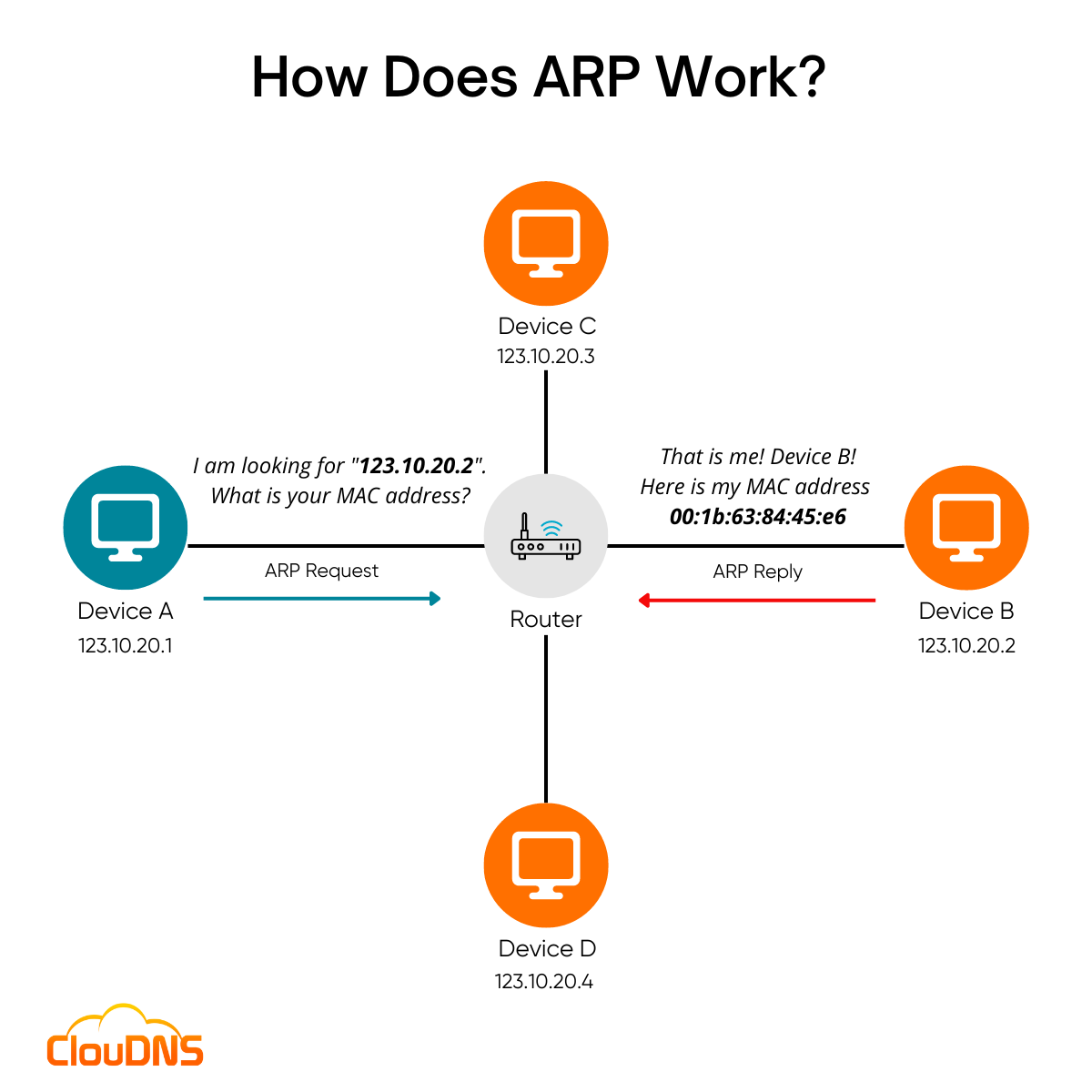
The ARP process is straightforward and typically happens in milliseconds, transparent to the user:
- ARP Request: A device (e.g., GCS) wants to communicate with another device (e.g., drone) on the same local network and knows its IP address but not its MAC address. The GCS broadcasts an ARP request packet to all devices on the local network. This request typically contains the source device’s IP and MAC address, and the target device’s IP address, asking, “Who owns this IP address? Please send me your MAC address.”
- ARP Response: All devices on the local network receive the ARP request. Only the device whose IP address matches the target IP in the request will process it. This target device (the drone, in our example) then sends an ARP response packet directly back to the requesting device (GCS). The response contains the drone’s IP address and its MAC address.
- ARP Cache: Upon receiving the ARP response, the GCS stores the IP-to-MAC address mapping in its local ARP cache. This cache is a temporary memory where recently resolved mappings are stored. This prevents the need to send an ARP request every time the GCS wants to communicate with the drone, significantly improving efficiency. Entries in the ARP cache typically have a timeout period and are flushed periodically or when errors occur.
- Data Transmission: With the MAC address resolved and stored in the cache, the GCS can now encapsulate its data (e.g., flight commands, telemetry requests) into Ethernet (or Wi-Fi) frames, addressing them to the drone’s MAC address, and transmit them directly.
This entire process ensures efficient local network communication, forming the bedrock for higher-level protocols and applications that drive drone functionality.
ARP’s Crucial Role in Drone Operations
The seemingly simple function of ARP belies its critical importance in the complex ecosystem of drone technology. From the initial connection between a drone and its controller to the sophisticated dance of multi-drone swarms, ARP underpins the reliability and responsiveness of these systems.
Command and Control Link Integrity
The fundamental ability of a pilot to control a drone relies on a robust and instantaneous command and control (C2) link. Whether using a dedicated radio link that bridges to an IP network, Wi-Fi, or cellular connectivity, many modern drone C2 systems operate over IP. When the ground control station sends a “climb” or “move forward” command, these instructions are encapsulated in IP packets. For these packets to traverse the local network segment between the controller and the drone’s receiver, ARP performs the necessary IP-to-MAC address resolution. A failure in ARP or an incorrect ARP entry can lead to lost commands, delayed responses, or even a complete loss of control, posing significant safety and operational risks. The integrity of the C2 link is directly tied to the efficient and correct functioning of ARP.
Real-time Data Transmission (Telemetry and Video)
Drones are prolific data gatherers. They constantly transmit telemetry data (altitude, speed, battery status, GPS coordinates) back to the GCS, and many stream high-definition video in real-time. This real-time data flow is critical for situational awareness, mission execution, and post-flight analysis. For instance, a drone mapping a large agricultural field sends back continuous imagery, while a search and rescue drone streams live thermal video. All this data, packaged into IP packets, must find its way across the local network to the GCS or a relay point.
ARP facilitates this by ensuring that the drone can correctly address the GCS (or vice-versa for requests) at the data link layer. Without a functioning ARP mechanism, IP packets containing vital telemetry or video frames would fail to be delivered, leading to data loss, buffering, or a complete communication breakdown. The low latency and high bandwidth requirements of drone video streaming, in particular, demand an extremely efficient underlying network, where ARP’s swift address resolution is a key enabler.
Swarm Robotics and Multi-Drone Coordination
The future of drone technology increasingly points towards autonomous swarms and multi-drone operations. From synchronized light shows to coordinated search patterns and automated inspections, these applications require drones to communicate not only with a central controller but also extensively with each other. In a drone swarm, individual units often need to share location data, synchronize movements, assign tasks, and even relay information about obstacles or targets.
This inter-drone communication, especially within a localized group operating in close proximity, frequently occurs over IP networks. For drones within the same subnetwork to identify and communicate with each other, ARP is indispensable. Each drone needs to resolve the IP addresses of its fellow swarm members to their corresponding MAC addresses to send and receive commands, status updates, or sensor data. The efficiency and reliability of ARP in a dynamic, multi-device environment are paramount for maintaining the coherence and effectiveness of a drone swarm, where rapid address resolution prevents communication bottlenecks and enables complex synchronized behaviors.
Securing Drone Networks: Understanding ARP Vulnerabilities
While ARP is fundamental to IP networking, its inherent design, predating many modern security considerations, makes it vulnerable to certain types of attacks. In the context of drone operations, especially those involving sensitive data or critical missions, understanding and mitigating these vulnerabilities is paramount for maintaining the security and integrity of drone networks.
ARP Spoofing and Its Implications
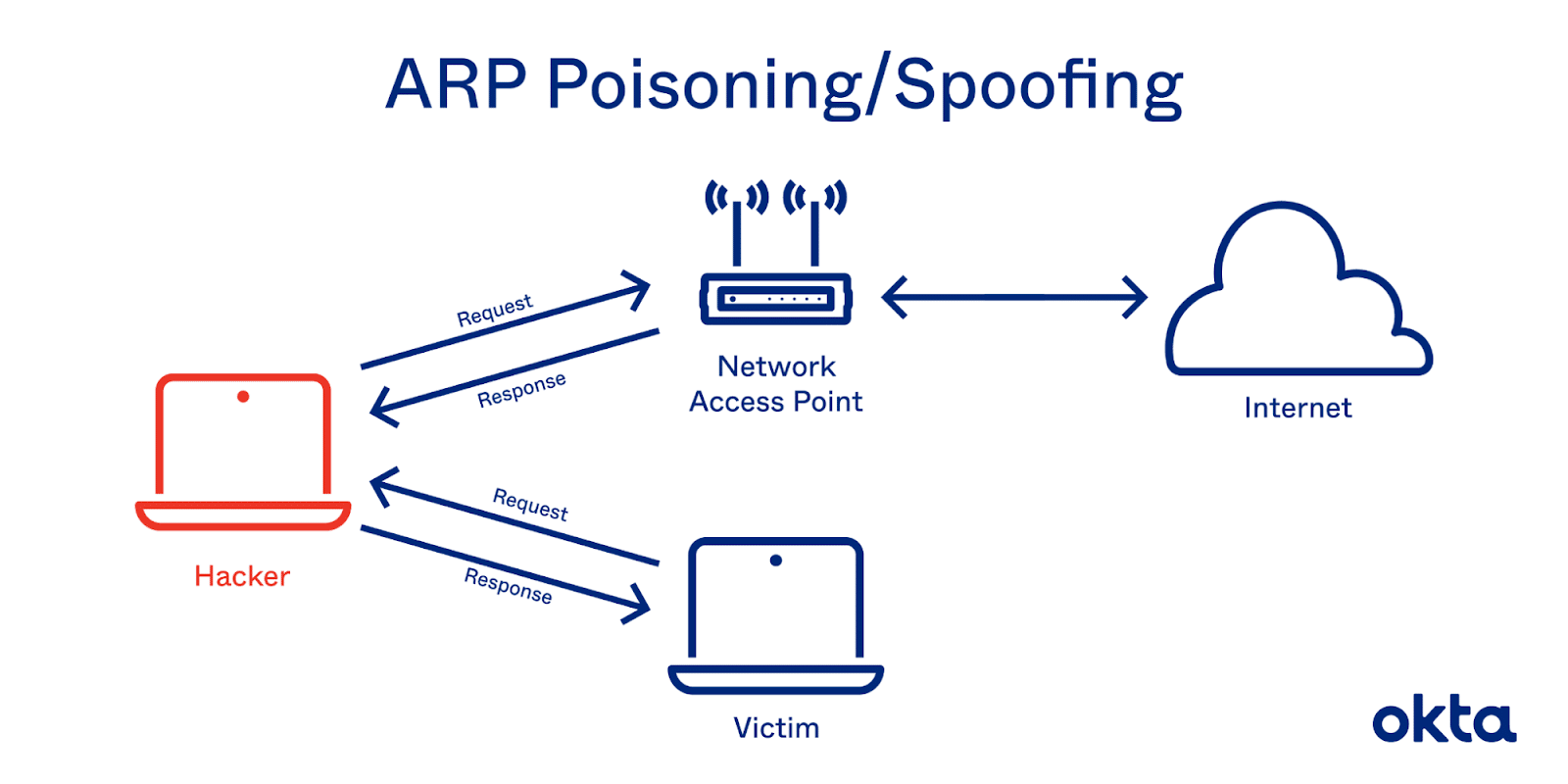
The primary vulnerability associated with ARP is ARP spoofing (also known as ARP poisoning). Because ARP is stateless and trusts responses, a malicious actor within the same local network can send forged ARP response packets. These forged responses claim that the attacker’s MAC address is associated with another device’s IP address (e.g., the drone’s IP address or the GCS’s IP address).
For example, an attacker could send an ARP response to the GCS claiming to have the drone’s MAC address, and simultaneously send another ARP response to the drone claiming to have the GCS’s MAC address. If successful, both the GCS and the drone update their ARP caches with the attacker’s MAC address for the other’s IP. As a result, all traffic between the GCS and the drone would be routed through the attacker’s device.
The implications of ARP spoofing in a drone environment are severe:
- Man-in-the-Middle (MITM) Attacks: The attacker can intercept, view, modify, or even inject commands and data packets exchanged between the drone and the GCS. This could lead to unauthorized control, data exfiltration, or the injection of malicious commands that could compromise the drone’s mission or safety.
- Denial of Service (DoS): An attacker could flood the network with ARP requests or responses, or redirect traffic to a non-existent host, effectively disrupting communication and rendering the drone uncontrollable.
- Session Hijacking: By intercepting credentials or session tokens, an attacker could gain unauthorized access to the drone control interface.
For enterprise drones, military UAVs, or drones handling sensitive data (e.g., infrastructure inspection, surveillance), ARP spoofing represents a significant cybersecurity threat that demands careful consideration.
Mitigation Strategies for Enhanced Security
Protecting drone networks from ARP-related attacks requires a multi-layered approach:
- Static ARP Entries: For critical connections, such as between a GCS and its drone, administrators can configure static ARP entries in the devices’ ARP caches. A static entry manually binds an IP address to a specific MAC address, preventing the device from accepting dynamic ARP updates for that mapping. While effective, this approach can be cumbersome to manage in large, dynamic networks.
- ARP Inspection (Dynamic ARP Inspection – DAI): On managed network switches (if the drone network uses one), Dynamic ARP Inspection (DAI) can be enabled. DAI works by intercepting ARP requests and responses, validating them against trusted bindings in a DHCP snooping database, and dropping invalid ARP packets. This prevents malicious ARP packets from propagating through the network.
- Network Segmentation and VLANs: Isolating drone traffic on separate Virtual Local Area Networks (VLANs) or physically segmenting the network limits the scope of an ARP spoofing attack. If an attacker gains access to one segment, they cannot easily spoof ARP entries for devices in another segment.
- Encryption and Authentication: While ARP spoofing operates at a lower layer, encrypting data at higher layers (e.g., using Transport Layer Security/SSL or VPNs) can mitigate the impact of MITM attacks. Even if an attacker intercepts traffic, they cannot read or modify the encrypted content without the decryption key. Strong authentication mechanisms for control links also add an extra layer of defense against unauthorized access.
- Security Information and Event Management (SIEM): Monitoring network traffic for unusual ARP activity (e.g., excessive ARP requests, unsolicited ARP replies) can help detect ongoing attacks, allowing for rapid response and mitigation.
- Physical Security: Preventing unauthorized access to the physical network infrastructure or drone components is a fundamental step in preventing local network attacks like ARP spoofing.
Implementing these strategies helps to fortify drone communication links, ensuring that critical data and commands remain secure and untampered with during flight operations.
The Future of ARP in Evolving Drone Tech
As drone technology continues its rapid evolution, particularly towards greater autonomy, swarm intelligence, and integration with broader IoT ecosystems, the underlying networking protocols like ARP will remain foundational. Their robustness, efficiency, and security will dictate the capabilities and reliability of future drone applications.
Impact on Autonomous Systems and IoT Integration
Autonomous drones, capable of making independent decisions and operating without constant human oversight, rely heavily on intricate network interactions. This includes internal communication between various onboard sensors, processors, and actuators, as well as external communication with other autonomous agents, cloud-based AI, and ground infrastructure. As these systems become more complex and distributed, the efficiency of local address resolution via ARP will be critical. Any latency or unreliability in ARP could translate to delayed decisions or failed coordinations, compromising mission success and safety.
Furthermore, drones are increasingly being integrated into the Internet of Things (IoT). They act as mobile IoT sensors, data gatherers, and even delivery platforms. In an IoT environment, drones might need to communicate with a myriad of smart devices, network edge gateways, or other connected infrastructure. Each of these interactions, if occurring within a local IP network segment, will inevitably leverage ARP. The scalability of ARP, especially in dense IoT deployments with numerous connected devices including drones, will be a key consideration.
The development of IPv6, which uses Neighbor Discovery Protocol (NDP) instead of ARP for address resolution, will gradually impact drone networking. As drones adopt IPv6, NDP will take over the role of ARP, offering improvements in efficiency and security features. However, for the foreseeable future, especially in mixed IPv4/IPv6 environments, ARP will continue to be a vital component.
As drone technology pushes the boundaries of what’s possible, from delivery services to urban air mobility, the seemingly low-level functionality of ARP will persist as a silent, yet indispensable, enabler. Understanding its mechanics, appreciating its vulnerabilities, and proactively implementing security measures will be crucial for the continued safe, efficient, and innovative deployment of drones across diverse sectors.
