Defining User Identity in the Drone Ecosystem
In the rapidly evolving world of drone technology and innovation, the concept of “user identity” extends far beyond a simple login and password. It forms the intelligent bedrock upon which advanced features, security protocols, and personalized experiences are built. Within the drone ecosystem, a “user” isn’t solely defined as the pilot or operator. It encompasses anyone whose identity influences or is influenced by drone operations: the individual being tracked by AI follow mode, the beneficiary of a drone service, the owner of property being mapped, or the authorized recipient of sensitive data.

User identity in this context is a multifaceted digital persona, often comprising a combination of explicit credentials (like account details), implicit behavioral patterns (flight styles, preferred settings), biometric data (facial recognition for AI tracking), device registration details, and even unique signal patterns. This dynamic identity is pivotal for how intelligent drone systems perceive, interact with, and ultimately serve their human counterparts. It marks a significant shift from drones being merely remote-controlled devices to sophisticated, autonomous or semi-autonomous agents that require an understanding of who they are interacting with to function effectively and responsibly within the sphere of tech innovation.
The Role of Identity in Autonomous Flight and AI Integration
The frontier of drone technology is increasingly defined by autonomy and artificial intelligence, making user identity an indispensable component of these advancements. Without robust identity management, the full potential of AI-driven drone capabilities remains unlocked.
Autonomous Flight Authorization
Autonomous drones are designed to execute missions with minimal human intervention. However, initiating, overseeing, or modifying these missions necessitates clear authorization. User identity serves as the fundamental key to unlocking these capabilities. An autonomous drone system must unequivocally know who is authorized to command it. This could involve secure digital certificates tied to a specific pilot’s identity for executing missions in sensitive airspace, company-wide access permissions for enterprise drone fleets, or even geo-fenced authorizations linked to the identity of a property owner. The integrity of autonomous flight hinges on verifying the legitimate user before any operation commences, ensuring compliance and preventing unauthorized command.
AI Follow Mode and Subject Recognition
One of the most compelling AI-driven features, AI follow mode, relies entirely on the drone’s ability to identify and differentiate a specific user from their environment. This advanced functionality transcends basic object tracking. It often integrates sophisticated computer vision algorithms for facial recognition, gait analysis, or the detection of unique wearables that signal “this is the user to follow.” Furthermore, some systems may use unique signal emitters carried by the user, providing a more reliable and consistent form of identification even in complex visual environments. The drone’s AI isn’t just following a generic moving object; it’s following an identified individual, making the concept of user identity central to its operation.
Personalized Mission Planning
Advanced drone systems leverage user identity to offer highly personalized experiences. This involves storing and recalling individual user preferences, frequently visited locations, custom flight parameters, or specific mapping requirements. AI systems can then learn from a user’s historical actions, suggesting optimized flight paths, recommending specific data collection strategies based on past successes, or pre-loading settings for recurring tasks. This personalization, powered by a persistent understanding of user identity, drastically enhances efficiency and user satisfaction, transforming generic drone operations into tailored, intelligent workflows.
Human-Drone Interaction
As drones become more integrated into daily life, human-drone interaction paradigms are evolving. Voice commands, gesture recognition, and even biometric inputs are becoming viable control methods. For these interactions to be secure and effective, the drone’s AI must often recognize who is giving the command. This ensures that only authorized individuals can alter flight paths, initiate emergency procedures, or access sensitive functions, prioritizing instructions based on the identified user’s permissions and roles.
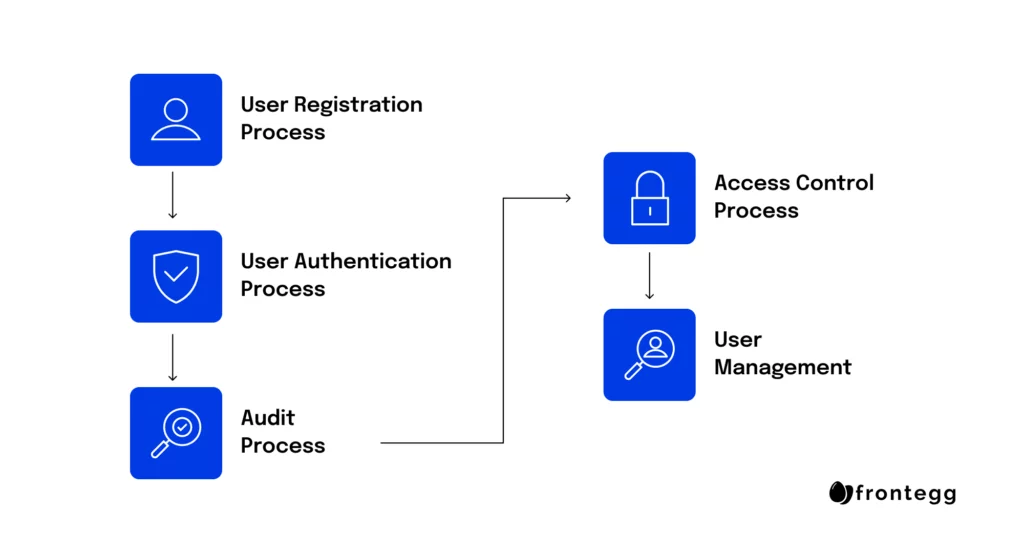
Securing Drone Operations Through Robust User Identification
Security is paramount in the realm of advanced drone technology, and robust user identification is the cornerstone of protecting both the drone and the data it collects. As drones become more sophisticated and operate in critical applications, preventing unauthorized access and ensuring accountability are non-negotiable.
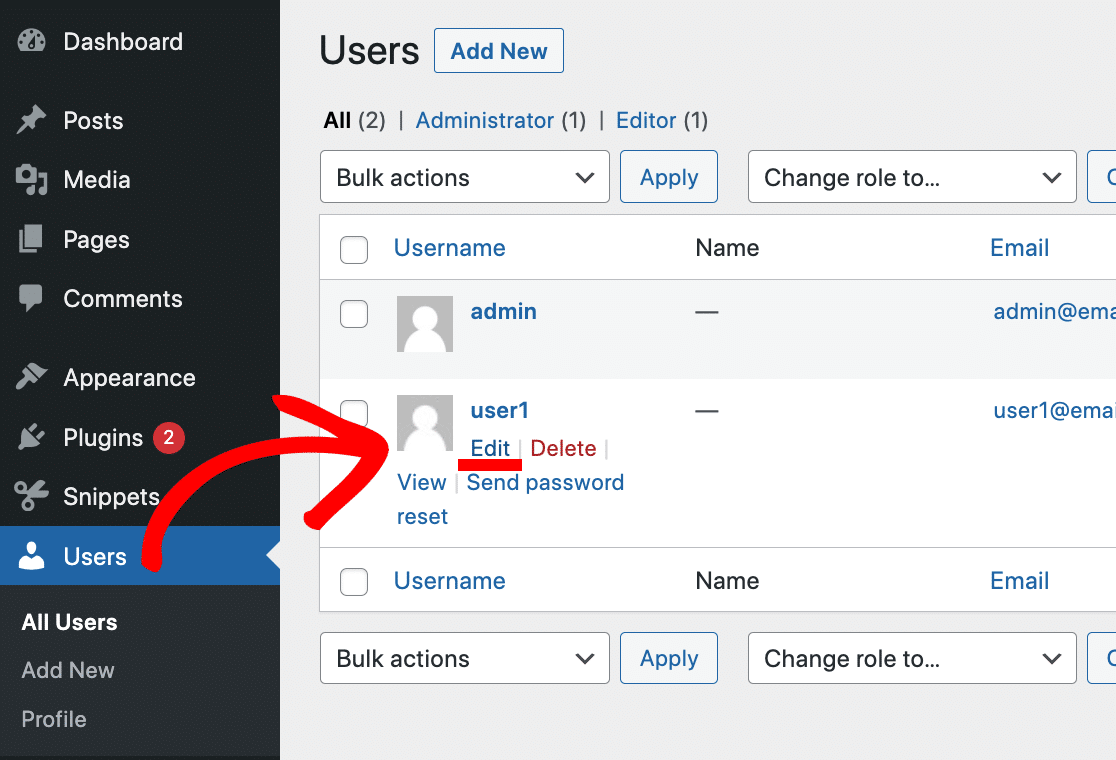
Access Control and System Integrity
The prevention of unauthorized drone operation is a primary concern, especially for commercial, industrial, and government applications where drones handle sensitive data or operate in critical infrastructure. User identity acts as the first line of defense, ensuring that only certified and authorized personnel can power on, control, or interact with a drone. This prevents malicious actors from hijacking drones, altering their missions, or compromising system integrity. Advanced systems often employ multi-factor authentication, biometric verification, or hardware security modules tied to specific user identities.
Regulatory Compliance and Accountability
The regulatory landscape for drone operations is complex and ever-evolving. User identity is crucial for establishing clear accountability. Every flight, every data point collected, and every operational incident needs to be traceable to a specific, identified operator. This traceability is essential for compliance with airspace regulations, incident investigations, and ensuring that operators adhere to safety protocols and legal mandates. By linking flight logs and telemetry to a verified user identity, regulatory bodies can maintain order and enforce standards effectively.
Data Security for Mapping and Remote Sensing
Drones are powerful tools for data collection, from high-resolution mapping of critical infrastructure to agricultural yield analysis and surveillance. Much of this data can be highly sensitive or proprietary. User identity plays a critical role in managing who can view, download, process, or share this information. Secure cloud platforms and ground stations implement identity-based access controls, ensuring that only authorized users with appropriate permissions can interact with the collected data, thereby safeguarding intellectual property and privacy.
Anti-Theft and Device Security
Beyond operational security, user identity can also protect the physical drone itself. Registering drone ownership and linking it to specific user credentials can deter theft and aid in recovery. Advanced systems can require operator authentication for initial activation or remote unlocking, effectively tying the device to its legitimate owner and rendering it inoperable for unauthorized users, thus enhancing overall device security.
Personalization and the Future of User-Centric Drone Experiences
The future of drone technology, particularly within the ‘Tech & Innovation’ sphere, is undeniably user-centric. User identity is the engine driving personalization, creating more intuitive, efficient, and enjoyable drone experiences.
Tailored User Interfaces
Drone control applications and ground station software can be dynamically customized based on an individual user’s identity. A novice pilot might encounter a simplified interface with essential controls and automated safety features, while an experienced professional receives access to advanced telemetry, granular flight parameters, and specialized mission planning tools. This tailored experience, made possible by recognizing the user, minimizes cognitive load and maximizes operational efficiency for all skill levels.
Adaptive Drone Behavior
Imagine a drone that learns and adapts to your unique flying style, preferred camera settings, or common operational environments. This goes beyond simple preference storage; it involves the drone’s AI continuously analyzing your interaction patterns, decision-making processes, and typical mission objectives. Over time, the drone can proactively adjust its flight dynamics, suggest optimal camera angles for cinematic shots, or even anticipate your next move, creating a truly symbiotic human-drone partnership. This adaptive behavior is entirely predicated on a deep and ongoing understanding of your individual user identity.
Seamless Integration with Personal Ecosystems
The vision for future drone innovation includes seamless integration into broader personal digital ecosystems. A drone that recognizes its owner could automatically sync captured media to their preferred cloud storage, integrate with smart home security systems, or respond to voice commands only from identified family members. This level of integration transforms the drone from a standalone device into an intelligent extension of the user’s personal technology suite, blurring the lines between individual devices and creating a truly interconnected experience.
Predictive Assistance
Leveraging historical data linked to a specific user identity, advanced drone systems can offer predictive assistance. This might involve proactive suggestions for optimal battery swaps based on past mission durations, pre-flight checks tailored to a user’s typical operational environment, or even predicting potential hardware issues before they arise. By understanding a user’s habits and operational patterns, the drone can provide intelligent, context-aware support, enhancing both safety and efficiency without explicit commands.
Data Governance, Privacy, and Ethical Considerations of User Identity
As drones become increasingly capable of identifying, tracking, and interacting with users, the ethical implications, data privacy concerns, and governance frameworks surrounding user identity become critically important. Tech innovation must walk hand-in-hand with responsible implementation.
The Privacy Imperative
The ability of drones to collect identity-related data, whether through facial recognition in AI follow modes or through tracking personal device signals, raises significant privacy concerns. How is this data stored? Who has access? For how long? These questions underscore the imperative for robust privacy-by-design principles in all drone-related technologies that handle user identity. Companies must prioritize safeguarding personal information against unauthorized access, use, or disclosure.
Consent and Transparency
Ethical drone operations demand transparency. Users must be clearly informed about what identity-related data is being collected by their drones or by drone services they interact with. Furthermore, clear mechanisms for obtaining informed consent for data collection, storage, and processing are essential. This ensures individuals maintain agency over their digital footprint in the drone ecosystem. Without transparency and consent, public trust in drone technology, particularly advanced innovations, will erode.
Anonymization and De-identification
In scenarios involving large-scale data collection, such as urban mapping or public safety surveillance, the ethical use of drone technology often necessitates anonymization or de-identification of user identity data. While valuable insights can be derived from aggregated data, protecting individual privacy requires careful processing to ensure that personal identities cannot be re-linked to the data. Developing robust techniques for privacy-preserving data analytics is a key area of innovation.
Regulatory Frameworks
The rapid pace of drone innovation often outstrips regulatory development. However, existing and emerging data protection regulations, such as GDPR, already have significant implications for how user identity data collected by drones must be handled. Companies operating in the drone sector must proactively implement secure data management practices and ensure compliance with these frameworks, which often dictate strict rules for data collection, storage, transfer, and deletion related to identified or identifiable individuals.
Ethical AI
Developing AI systems within drones that can identify and interact with users in an ethical manner is a profound challenge. This involves training AI models to avoid bias, ensure fairness in recognition and decision-making, and respect individual rights. Ethical AI considerations extend to preventing the unintended identification of individuals, safeguarding against the misuse of identity data, and establishing clear guidelines for the deployment of identity-aware drone technologies in sensitive contexts. The responsible integration of user identity into drone innovation is not just a technical challenge, but a fundamental ethical one.
