In the rapidly evolving landscape of unmanned aerial vehicles (UAVs), the interface between the pilot and the machine has shifted from simple radio transmitters to sophisticated, high-definition touchscreens. As drone technology integrates deeper into professional workflows—from infrastructure inspection to emergency response—the software applications used to control these aircraft have become repositories of sensitive data. In this context, “User Authentication in Screen Time” refers to the security protocols and access management systems embedded within drone control apps and smart controllers.
As part of the broader drone accessories ecosystem, specifically focusing on controllers and flight applications, user authentication serves as the digital gatekeeper. It ensures that only authorized personnel can access flight systems, telemetry data, and mission-critical settings. This article explores the technical nuances of authentication within the “screen time” of a drone pilot, the safety implications of restricted access, and how these systems are revolutionizing fleet management.

Defining User Authentication within Drone Control Applications
User authentication is the process of verifying the identity of a person attempting to access the control interface of a drone. In the early days of hobbyist flight, anyone with a matching transmitter could theoretically fly a drone. Today, the “screen” on a smart controller or a connected smartphone is a sophisticated portal that requires rigorous verification before the motors can even be armed.
The Shift from Hardware to Software-Centric Security
Modern drone accessories, particularly smart controllers like the DJI RC Pro or the Autel Smart Controller, operate on customized versions of Android or proprietary operating systems. This transition from hardware-bound signals to software-driven flight means that the “screen” is now the primary vulnerability. User authentication protocols—such as alphanumeric passwords, pattern locks, or biometric scans—are integrated into the app’s startup sequence. This ensures that if a controller is lost or stolen in the field, the drone itself cannot be hijacked or used for malicious purposes.
Multi-Factor Authentication (MFA) in High-Stakes Flight Data
For enterprise-level drone operations, a simple password is often insufficient. Many professional drone apps now implement Multi-Factor Authentication (MFA). When a pilot logs into the “screen time” environment of an app like DJI Pilot 2 or QGroundControl, they may be required to provide a secondary code sent via SMS or generated by an authenticator app. This is particularly vital when the drone is connected to a corporate cloud, as it prevents unauthorized access to sensitive maps, thermal imagery, and GPS coordinates stored within the controller’s cache.
Role-Based Access Control (RBAC)
Within the “screen time” of a drone application, authentication is often tied to specific user roles. A “Lead Pilot” may have full access to flight settings and firmware updates, while a “Junior Observer” might only have permission to view the live camera feed on a secondary screen. Authentication facilitates this hierarchy, ensuring that critical flight parameters cannot be altered by inexperienced users, thereby maintaining the integrity of the mission and the safety of the hardware.
Managing Screen Time and Access Limits in Professional Drone Operations
While the term “screen time” is often associated with digital wellness in consumer electronics, in the drone industry, it takes on a more functional meaning: the duration and quality of a pilot’s interaction with the flight interface. Managing this time through authentication is a key component of operational safety and regulatory compliance.
Operational Fatigue and Digital Wellness for Pilots
Flight fatigue is a significant risk factor in UAV operations. Advanced drone control apps are beginning to incorporate “screen time” management features that track how long a pilot has been actively engaged with the controller. Through user authentication, the system can log the active hours of a specific individual. If a pilot exceeds a safe operational threshold—for example, four hours of continuous flight—the system can trigger an alert or require a mandatory “lockout” period. This prevents the cognitive decline associated with prolonged screen focus, ensuring that every takeoff is handled by a refreshed operator.
Restricting Access Through Time-Bound Authentication
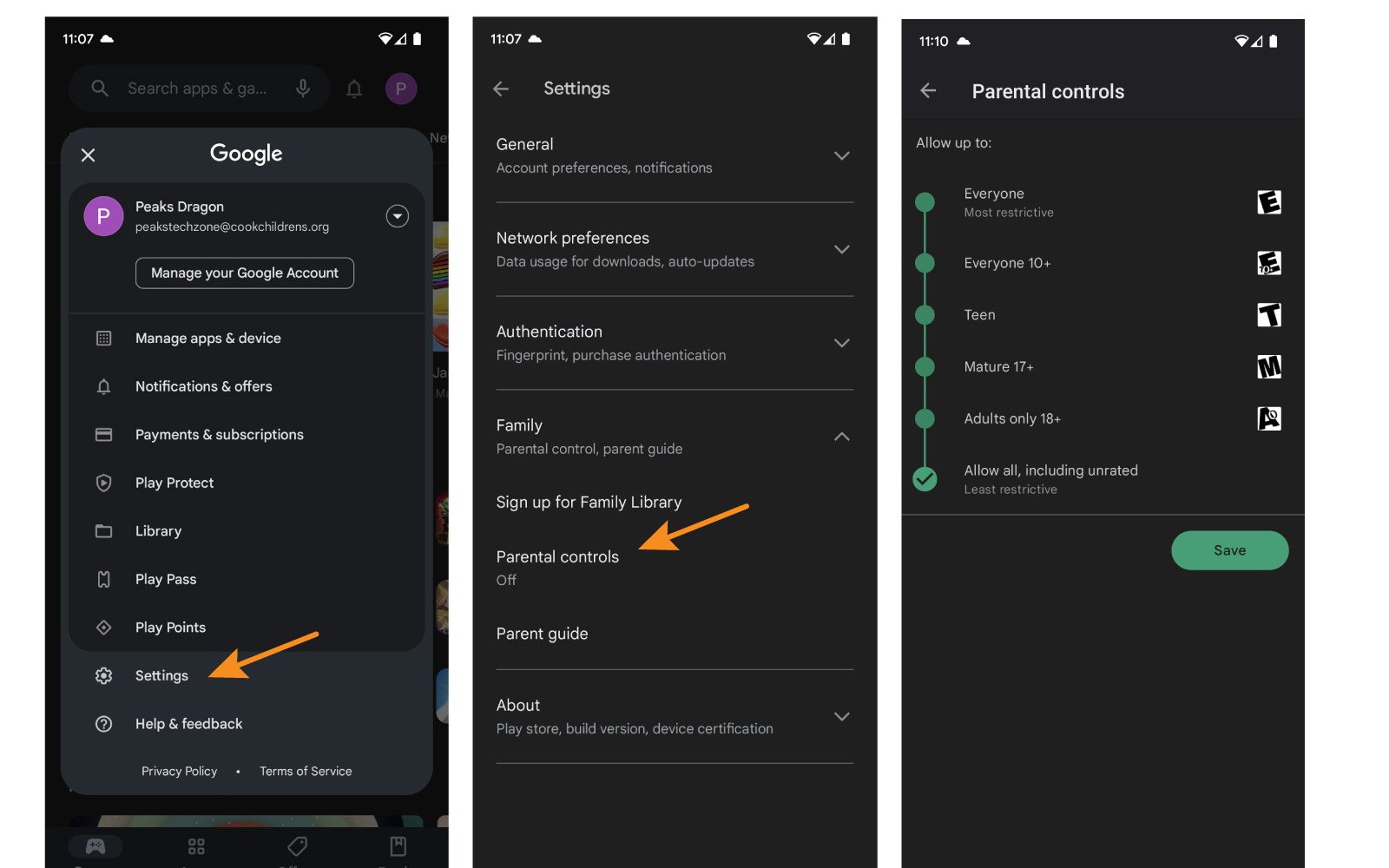
In many industrial settings, drones are shared among teams. Authentication allows for “time-bound” access, where a pilot’s credentials are only valid during their scheduled shift. This is a crucial accessory feature for companies managing large fleets. By controlling screen time access, managers ensure that no unauthorized flights occur after hours. This not only protects the equipment from wear and tear but also ensures that the company remains compliant with local aviation laws regarding daylight operations or specific flight windows.
Digital Logs and Accountability
Every second of “screen time” spent on a drone controller is a record of pilot intent. When a pilot authenticates their session, every stick movement, camera adjustment, and flight path change is logged under their unique ID. This creates a transparent audit trail. In the event of an incident or crash, investigators can look at the authenticated logs to determine exactly who was at the controls and what commands were issued. This accountability is a cornerstone of modern drone insurance and legal compliance.
The Role of Biometrics in Modern Remote Controllers
As drone controllers become more advanced accessories, the methods of user authentication are evolving to be more seamless and secure. Biometrics—using physical characteristics for verification—is becoming the gold standard for high-end drone interfaces.
Fingerprint and Facial Recognition for Rapid Deployment
In emergency response scenarios, such as search and rescue or firefighting, every second counts. Fumbling with a password on a touchscreen in the rain or while wearing gloves is impractical. High-end smart controllers are now integrating fingerprint sensors and infrared facial recognition. These allow for “instant-on” authentication. A pilot can pick up the controller, have their identity verified in milliseconds, and be in the air immediately. This integration of biometric authentication into the “screen time” workflow maximizes efficiency without compromising security.
Enhancing Fleet Management via User-Specific Profiles
Biometric authentication allows for the immediate loading of user-specific profiles. When a pilot authenticates via their fingerprint, the “screen” automatically adjusts to their preferred layout. This includes custom button mapping on the controller, specific gimbal sensitivity settings, and even preferred telemetry overlays. This level of personalization, tied directly to the authentication process, makes the drone accessory feel like a bespoke tool for every individual in a large organization.
Securing the “Return to Home” and Emergency Protocols
Authentication also plays a role in sensitive flight commands. For instance, certain “screen time” actions, such as changing the Home Point or initiating a remote self-destruct (in military/government contexts), may require a secondary biometric confirmation. This ensures that accidental touches on the screen do not trigger catastrophic or irreversible actions, adding a layer of physical verification to the most critical software commands.
Security Protocols for Cloud-Synced Flight Data
The “screen” of a drone controller is often just the edge of a much larger data ecosystem. Most modern drone apps sync data to the cloud in real-time. Authentication is the primary shield protecting this data pipeline from interception or unauthorized viewing.
Encrypting the Transmission Pipeline
When a pilot authenticates their session, an encrypted handshake is established between the drone accessory (the controller) and the cloud servers. This ensures that the video downlink and telemetry data displayed on the screen are encrypted end-to-end. Without proper user authentication, the data stream remains a scrambled mess of packets, protecting the privacy of the mission. This is especially critical for drones used in sensitive infrastructure inspections where the imagery could be used for corporate espionage.
Compliance and Regulatory Standards in User Access
Government regulations, such as the FAA’s Remote ID requirements in the United States, are increasingly demanding more robust identification of drone operators. User authentication in the flight app provides a mechanism for drones to broadcast “authenticated” pilot information to authorities if required. This digital “license plate” is tied to the screen-time session of the pilot, ensuring that the person registered to the drone is the one actually operating it.
The Future of Blockchain in Flight Authentication
Looking ahead, the drone industry is exploring decentralized authentication methods. By using blockchain technology, a pilot’s “screen time” and flight credentials could be verified across different platforms and accessories without a central server. This would allow a pilot to move from one brand of controller to another, using a single, unhackable digital identity. This “universal authentication” would streamline operations for massive drone delivery networks and urban air mobility (UAM) systems of the future.
Conclusion: The Interface of Security and Utility
User authentication in the context of drone “screen time” is far more than a simple login screen; it is the fundamental framework that enables safe, accountable, and professional UAV operations. As drone accessories—particularly apps and controllers—become more powerful, the need to secure the interface becomes paramount. By implementing biometric verification, time-bound access, and encrypted cloud syncing, the drone industry is ensuring that these “flying computers” remain under the control of the right people at the right time. For the modern pilot, understanding and utilizing these authentication tools is just as important as mastering the flight sticks themselves. Security is not just a feature; in the world of professional drones, it is a prerequisite for flight.
