The landscape of modern technology, particularly within specialized domains like flight technology, drones, and remote sensing, relies heavily on robust, secure, and efficient communication protocols. At the heart of managing and interacting with Linux-based systems, which often power the servers, embedded devices, and specialized hardware fundamental to these innovations, lies SSH: the Secure Shell protocol. SSH is not merely a tool for system administrators; it’s a foundational technology that enables secure remote operations, data transfer, and automation, thereby underpinning much of the collaborative development and operational capabilities in today’s tech and innovation ecosystem.
Understanding SSH: The Secure Shell Protocol
SSH, or Secure Shell, is a cryptographic network protocol that enables secure data communication between two networked devices. It provides a secure channel over an unsecured network by using strong encryption. Before SSH became ubiquitous, administrators often relied on protocols like Telnet and FTP for remote access and file transfer. However, these older protocols transmitted data, including passwords, in plain text, making them highly vulnerable to eavesdropping and interception. The introduction of SSH fundamentally changed this, offering a robust solution for maintaining confidentiality and integrity in remote interactions.

In a Linux environment, SSH is the de facto standard for remote access, allowing users to execute commands, manage files, and interact with a remote machine as if they were sitting directly in front of it. Its design prioritates security, making it indispensable for any organization dealing with sensitive data, managing critical infrastructure, or developing innovative solutions that require secure communication channels across distributed systems. From managing cloud instances that process vast datasets from drone-based LiDAR to securely updating firmware on remote autonomous vehicles, SSH provides the encrypted backbone that ensures operations remain secure and uninterrupted, driving forward advancements in tech and innovation.
The Architecture of Secure Communication: How SSH Works
The power of SSH lies in its sophisticated cryptographic architecture, which transforms an inherently insecure network into a secure communication channel. Understanding its operational principles reveals why it’s a cornerstone of secure tech infrastructure.
Client-Server Model
SSH operates on a client-server model. An SSH client initiates a connection to an SSH server (often referred to as sshd, the SSH daemon) running on the remote machine. Once the connection is established, the client and server negotiate a secure session, authenticating each other and setting up encrypted channels for communication. This model allows for centralized management and distributed access, critical for complex systems often found in fields like remote sensing and autonomous systems, where a central server might manage numerous edge devices.
Cryptographic Foundations
The security of SSH is built upon three core cryptographic principles:
- Encryption: SSH uses strong encryption algorithms to protect data confidentiality. This involves a mix of symmetric and asymmetric encryption. Asymmetric encryption (using public and private key pairs) is primarily used during the initial setup phase to securely exchange a symmetric key. Once established, symmetric encryption, which is much faster, is used for encrypting all subsequent data transmitted during the session. This ensures that even if an attacker intercepts the data stream, they cannot decipher its contents without the appropriate key. This level of data protection is vital when handling sensitive sensor data, flight plans, or proprietary algorithms.
- Authentication: SSH offers robust mechanisms to verify the identity of both the client and the server.
- Server Authentication: When a client first connects to an SSH server, the server presents its public key. The client stores this key to verify the server’s identity in future connections, preventing “man-in-the-middle” attacks where an impostor server might try to intercept communications.
- User Authentication: The most common methods are password authentication and public-key authentication. While password authentication is familiar, public-key authentication is significantly more secure. Here, the user generates a pair of cryptographic keys: a private key (kept secret on the client machine) and a public key (uploaded to the server). When connecting, the server uses the public key to challenge the client, and the client proves its identity by cryptographically signing the challenge using its private key. This method eliminates the risk associated with transmitting passwords over the network and provides a much stronger authentication factor. For automated systems or high-security deployments common in cutting-edge tech, public-key authentication is indispensable.
- Integrity: SSH employs Message Authentication Codes (MACs) to ensure data integrity. MACs are cryptographic checksums calculated for each data packet. If even a single bit of data is altered during transmission, the MAC check will fail, alerting both ends of the connection to the tampering. This guarantees that commands sent to a remote system, or data received from it, remain unaltered and reliable, which is paramount for controlling expensive equipment or processing critical data.
The Handshake Process
The secure SSH session establishment involves a complex handshake process. Initially, the client and server negotiate the SSH protocol version. Then, they exchange encryption algorithms, hash algorithms, and compression methods they will use. Subsequently, the server sends its host key to the client for verification. Following this, a Diffie-Hellman key exchange algorithm is often used to securely generate a shared secret key, which is then used for symmetric encryption of the session. Finally, user authentication takes place. Once all these steps are successfully completed, a secure, encrypted, and authenticated session is ready for command execution and data transfer. This meticulous process ensures that every SSH session starts with a strong security posture.
Unleashing Efficiency and Innovation: Key SSH Use Cases in Linux
SSH’s capabilities extend far beyond simple remote login, acting as a versatile tool that enhances productivity, security, and the development of innovative solutions in Linux environments.
Remote System Administration
For IT professionals managing server farms, cloud infrastructure, or fleets of specialized Linux-based devices (such as those found in smart cities, autonomous drones, or remote sensor networks), SSH is the primary tool. It allows administrators to securely configure systems, install software updates, diagnose issues, and monitor performance from any location with internet access. This capability is crucial for maintaining uptime and ensuring the smooth operation of distributed systems that form the backbone of modern technological advancements.
Secure File Transfer (SFTP & SCP)
SSH doesn’t just provide command-line access; it also facilitates secure file transfers. SCP (Secure Copy Protocol) and SFTP (SSH File Transfer Protocol) are built on top of SSH, encrypting file transfers to protect data in transit. This is invaluable for transferring large datasets collected by high-resolution cameras, thermal imaging sensors, or LiDAR units on UAVs to powerful processing servers. It ensures that valuable data—be it for mapping, surveillance, or scientific research—is moved securely and reliably.
Port Forwarding and Tunnelling
One of SSH’s most powerful features is its ability to create secure tunnels for other network services. SSH port forwarding allows users to “tunnel” otherwise insecure network traffic through an encrypted SSH connection. This can be used to securely access internal web interfaces, databases, or other services that are not directly exposed to the public internet. For example, a developer might use SSH tunneling to securely connect to a development server’s internal database or a ground control station might use it to securely communicate with a drone’s embedded Linux system over a public network without exposing the internal control protocols. This capability significantly enhances security for complex, interconnected systems typical in high-tech deployments.
Automated Tasks and Scripting
SSH is highly scriptable, making it a critical component for automation. Developers and operations teams can write scripts that leverage SSH to execute commands on remote servers automatically. This is fundamental for continuous integration/continuous deployment (CI/CD) pipelines, automated software deployments, backup routines, and orchestrating complex workflows across multiple machines. For innovations requiring rapid iteration and deployment, such as AI model updates for autonomous systems or new algorithms for image processing, SSH-driven automation accelerates development cycles and reduces manual errors, thereby fostering a more agile and innovative environment.
Git and Version Control
In collaborative software development, Git is the dominant version control system. SSH provides a secure method for interacting with Git repositories hosted on platforms like GitHub, GitLab, or Bitbucket, or even self-hosted Git servers. Developers use SSH keys to authenticate their Git clients with the repository server, ensuring that only authorized individuals can push code, manage branches, and collaborate on projects. This secure workflow is vital for managing the complex codebases behind AI algorithms, flight control software, and other innovative applications.
Practical Implementation: Getting Started with SSH on Linux
Implementing SSH on Linux is straightforward, thanks to the widely adopted OpenSSH suite.
Installing SSH
Most modern Linux distributions come with the OpenSSH client pre-installed. The server component, sshd, might also be pre-installed or can be easily installed using the distribution’s package manager. For Debian/Ubuntu-based systems, this is typically done via sudo apt install openssh-server. For Red Hat/Fedora-based systems, it’s sudo dnf install openssh-server.
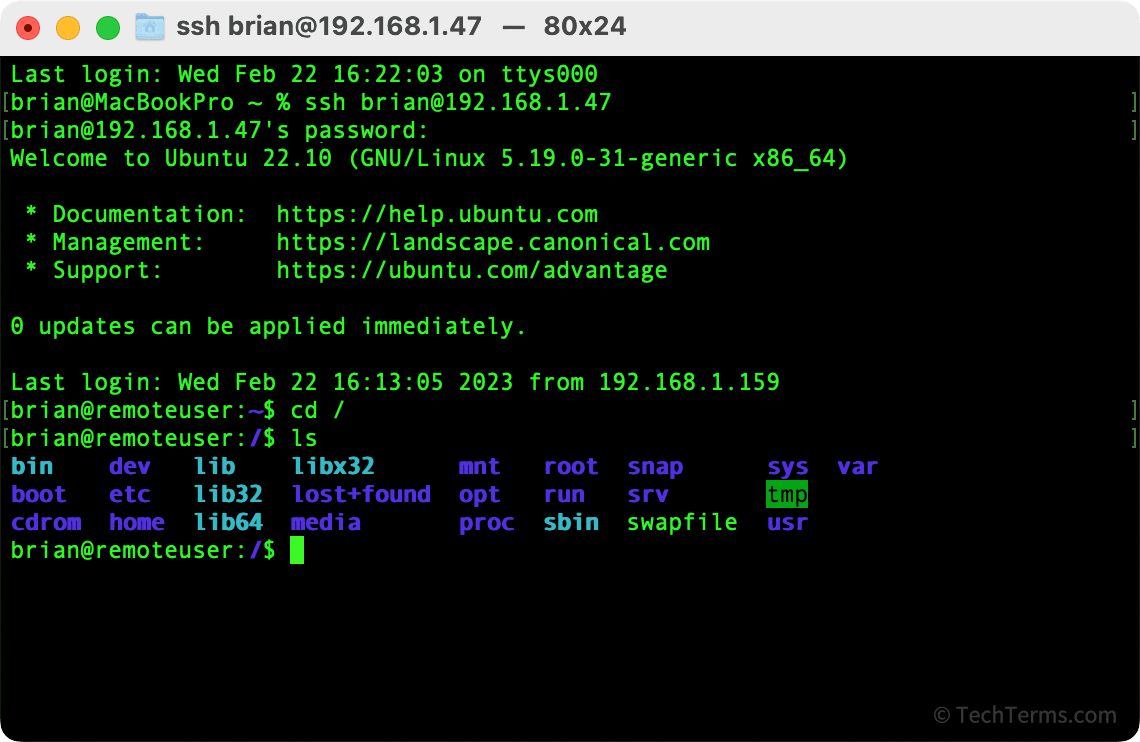
Basic Connection
To connect to a remote Linux machine, you use the ssh command followed by the username and the hostname or IP address of the remote server:
ssh username@hostname_or_ip
For example, ssh user@192.168.1.100 or ssh admin@myremoteserver.com. The first time you connect to a new server, you’ll be prompted to verify the server’s host key fingerprint. If you accept, the key is stored in your ~/.ssh/known_hosts file, and subsequent connections will automatically verify the server’s identity.
Public-Key Authentication Setup
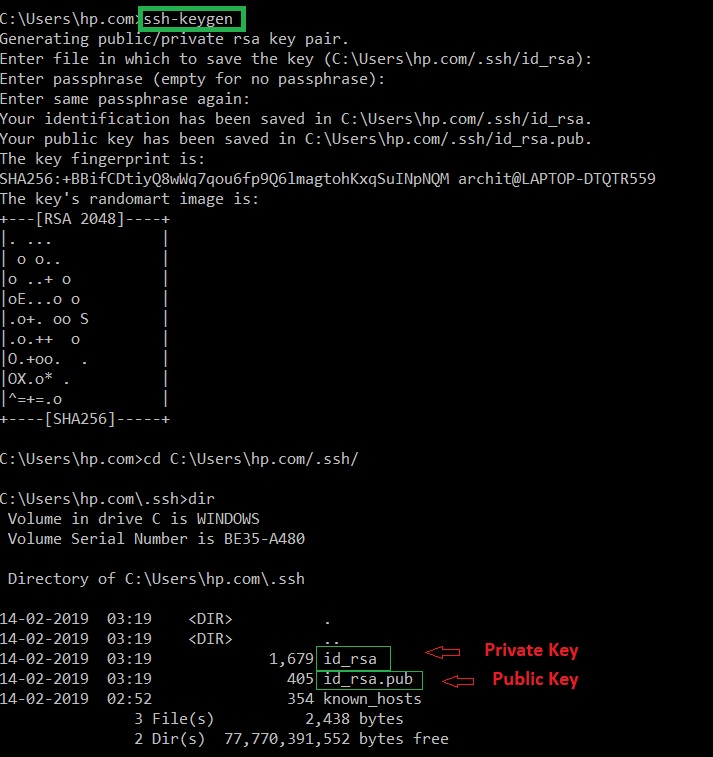
Public-key authentication is the recommended and most secure method for SSH.
-
Generate Key Pair: On your local machine, open a terminal and run
ssh-keygen. This will prompt you for a location to save the keys (default is~/.ssh/id_rsa) and an optional passphrase. A strong passphrase adds an extra layer of security, encrypting your private key. -
Copy Public Key to Server: Use
ssh-copy-idto easily transfer your public key to the remote server:ssh-copy-id username@hostname_or_ipYou’ll be prompted for your password (for the remote user) once. This command appends your public key (
id_rsa.pub) to the~/.ssh/authorized_keysfile on the remote server. -
Connect Using Key: After copying the key, you can connect to the server without needing a password:
ssh username@hostname_or_ipIf your private key is protected by a passphrase, you’ll be prompted for it when you first use the key in a session.
Basic Server Configuration (sshd_config)
The SSH server configuration file is typically located at /etc/ssh/sshd_config. For enhanced security, consider these modifications:
- Disable Password Authentication: Change
PasswordAuthentication yestoPasswordAuthentication no. This forces the use of public-key authentication, significantly reducing the risk of brute-force attacks. - Change Default Port: While not a security panacea, changing
Port 22to a non-standard port (e.g.,Port 2222) can reduce exposure to automated scanning bots. Remember to specify the new port with the-pflag when connecting (ssh -p 2222 user@host). - Permit Specific Users: Use
AllowUsers username1 username2to restrict SSH access to only specified users.
After making changes to sshd_config, you must restart the SSH service: sudo systemctl restart sshd.
Advanced Security and Management for Modern Tech Infrastructures
As reliance on remote Linux systems grows, especially within innovative tech spheres, advanced SSH features become crucial for robust security and efficient management.
SSH Agents
An SSH agent is a program that holds private keys in memory, preventing you from having to enter your passphrase every time you use your key. Once a private key is added to the agent (e.g., using ssh-add), it remains unlocked for the duration of your session or until the agent is stopped. This provides a balance between convenience and security, especially when using keys with strong passphrases for automated scripts or frequent connections.
SSH Configuration File (~/.ssh/config)
The SSH client configuration file (~/.ssh/config) is a powerful tool for streamlining connections. You can define aliases, specific user names, ports, identity files, and other parameters for different hosts. This simplifies complex connection commands into short, memorable aliases, improving workflow for managing multiple remote systems.
Host myprojectserver
Hostname 192.168.1.200
User devuser
Port 2222
IdentityFile ~/.ssh/id_rsa_project
Host droneserver
Hostname drone-control.company.com
User droneadmin
IdentityFile ~/.ssh/id_rsa_drone
Now, connecting is as simple as ssh myprojectserver or ssh droneserver.
Two-Factor Authentication (2FA) with SSH
For environments demanding the highest security, integrating Two-Factor Authentication (2FA) with SSH adds an extra layer of protection. This typically involves requiring a time-based one-time password (TOTP) from an authenticator app in addition to a password or SSH key. This significantly reduces the risk of unauthorized access, even if a private key is compromised. Technologies like Google Authenticator can be integrated with PAM (Pluggable Authentication Modules) to enforce 2FA for SSH logins on Linux servers.
Limiting User Access and Commands
For specific use cases, such as granting limited access to automated processes or external partners, SSH allows fine-grained control over what a user can do. By modifying the authorized_keys file or sshd_config, you can restrict a user to executing only a specific command (e.g., command="/usr/local/bin/run_sensor_data_pull.sh" ssh-rsa AAAAB3N...) or force them to use a specific port forwarding setup, enhancing security for specialized roles within a system. This is particularly valuable for protecting sensitive components of an innovative tech deployment, where access needs to be tightly controlled.
Monitoring and Auditing SSH Access
Maintaining robust security requires constant vigilance. SSH logs provide critical information about connection attempts, successful logins, and authentication failures. These logs, usually found in /var/log/auth.log or /var/log/secure on Linux, should be regularly monitored for suspicious activity. Integrating these logs with centralized logging systems and intrusion detection systems is a best practice for any serious tech infrastructure, ensuring that any anomalies related to remote access are immediately flagged and investigated.
In conclusion, SSH is far more than a simple command-line utility; it is a critical enabling technology for modern “Tech & Innovation.” By providing secure, efficient, and flexible remote access, it underpins the development, deployment, and management of complex Linux-based systems—from cloud servers processing AI algorithms to embedded systems controlling autonomous drones. Its robust cryptographic foundations and versatile features make it an indispensable tool for securing the digital frontier of innovation.
