Spectrum Security Suite is a comprehensive cybersecurity solution designed to protect organizations from a wide range of digital threats. In today’s interconnected world, where businesses increasingly rely on digital infrastructure and data, robust security measures are paramount. This suite offers a multi-layered approach, integrating various security technologies and services to create a formidable defense against malware, phishing attacks, ransomware, data breaches, and other sophisticated cyber threats. Its aim is to provide businesses with the peace of mind that comes from knowing their valuable assets and sensitive information are safeguarded.
The development of Spectrum Security Suite stems from the evolving landscape of cyber warfare. As cybercriminals become more adept and their methods more advanced, traditional, single-point security solutions often prove insufficient. Spectrum Security Suite addresses this challenge by consolidating essential security functionalities into a unified platform. This not only simplifies security management for IT departments but also enhances the overall effectiveness of the security posture by ensuring that different security layers work in concert. It’s built for modern businesses, from small startups to large enterprises, recognizing that the need for security is universal, regardless of an organization’s size or industry.

Core Components and Functionality
Spectrum Security Suite is not a single product but rather a collection of integrated modules, each designed to tackle a specific aspect of cybersecurity. This modularity allows organizations to tailor the suite to their unique needs, deploying only the components that are most relevant to their risk profile. The core of the suite typically includes advanced threat detection and prevention mechanisms, data protection tools, identity and access management features, and robust endpoint security.
Advanced Threat Prevention and Detection
At the forefront of Spectrum Security Suite’s capabilities is its proactive approach to threat prevention and detection. This involves a combination of signature-based detection, which identifies known malware, and behavioral analysis, which looks for suspicious activities that might indicate new or zero-day threats.
Real-time Monitoring and Analysis
The suite continuously monitors network traffic, system logs, and endpoint activities for anomalies. This real-time analysis is powered by sophisticated algorithms and artificial intelligence, enabling it to identify potential threats as they emerge, rather than after a compromise has occurred. Alerts are generated promptly, allowing security teams to respond swiftly.
Intrusion Detection and Prevention Systems (IDPS)
Spectrum Security Suite incorporates advanced IDPS to identify and block malicious network traffic. These systems analyze incoming and outgoing network packets, comparing them against a database of known attack patterns and behavioral anomalies. When suspicious activity is detected, the system can either alert administrators or automatically block the malicious traffic, preventing it from reaching its intended target.
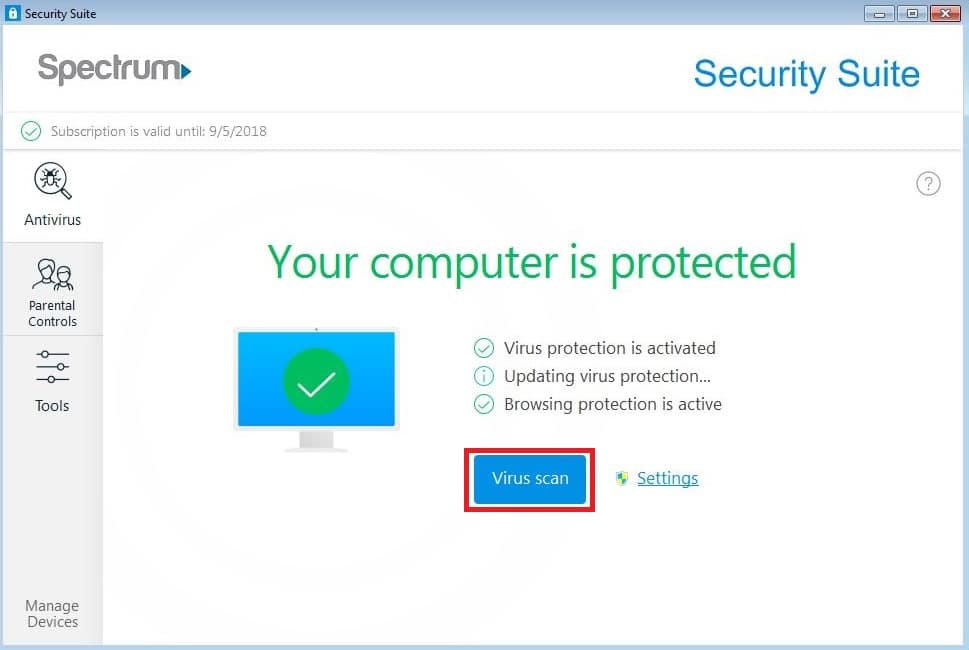
Malware and Virus Protection
Comprehensive anti-malware and antivirus capabilities are a cornerstone of the suite. This includes scanning files, applications, and system processes for known viruses, worms, Trojans, and other malicious software. The protection extends to real-time scanning, scheduled scans, and on-demand scanning, ensuring that systems are protected against both common and emerging malware threats.
Data Protection and Privacy
Protecting sensitive data from unauthorized access, modification, or exfiltration is a critical function of Spectrum Security Suite. This involves a range of measures designed to secure data at rest, in transit, and in use.
Encryption Technologies
The suite employs robust encryption protocols to protect data. This includes full-disk encryption for laptops and servers, as well as encryption for data in transit, such as communications over the internet using TLS/SSL. Sensitive files and databases can also be individually encrypted, ensuring that even if unauthorized access occurs, the data remains unintelligible.
Data Loss Prevention (DLP)
DLP solutions are integrated to prevent sensitive information from leaving the organization’s network or being misused. This involves identifying, monitoring, and protecting data in three states: data in use (e.g., when an endpoint user is working with a file), data in motion (e.g., data being transferred over a network), and data at rest (e.g., data stored on servers or endpoints). Policies can be configured to prevent the unauthorized sharing, copying, or transmission of confidential information.
Secure Data Storage and Backup
Spectrum Security Suite often includes features for secure data storage and regular, encrypted backups. This ensures that even in the event of a ransomware attack or hardware failure, critical data can be recovered quickly and securely, minimizing downtime and potential financial losses.
Identity and Access Management
Controlling who has access to what resources is fundamental to any security strategy. Spectrum Security Suite provides advanced tools to manage user identities, authenticate users, and enforce granular access controls, ensuring that only authorized personnel can access sensitive systems and data.
User Authentication and Authorization
The suite supports various authentication methods, including multi-factor authentication (MFA), which adds an extra layer of security beyond just a password. This makes it significantly harder for unauthorized individuals to gain access, even if they have compromised a user’s credentials. Once authenticated, users are granted specific permissions based on their roles and responsibilities within the organization.
Single Sign-On (SSO)
For improved user experience and enhanced security, Spectrum Security Suite often integrates with Single Sign-On (SSO) solutions. SSO allows users to log in once with a single set of credentials and gain access to multiple applications and systems without needing to re-enter their login information for each. This reduces password fatigue and minimizes the risk of weak or reused passwords.
Role-Based Access Control (RBAC)
RBAC is a crucial feature that simplifies the management of permissions. Users are assigned roles, and permissions are assigned to those roles. This ensures that users only have access to the resources they need to perform their job functions, adhering to the principle of least privilege.

Endpoint Security and Management
Endpoints, such as desktops, laptops, smartphones, and servers, are often the first line of defense and also the most vulnerable points in an organization’s IT infrastructure. Spectrum Security Suite offers robust protection for these devices.
Endpoint Detection and Response (EDR)
EDR capabilities provide advanced threat detection, investigation, and response for endpoints. This goes beyond traditional antivirus by continuously monitoring endpoint activity, collecting data, and using advanced analytics to detect and respond to threats that may have bypassed initial defenses. EDR allows for rapid identification of compromised devices and facilitates swift remediation actions.
Vulnerability Management
Spectrum Security Suite often includes tools for identifying and prioritizing vulnerabilities on endpoints and across the network. Regular scanning and assessment help organizations understand their security weaknesses and address them proactively before they can be exploited by attackers.
Device Hardening and Configuration Management
The suite can assist in hardening endpoints by enforcing security policies, such as disabling unnecessary services, configuring firewalls, and ensuring up-to-date patch management. Consistent configuration management across all endpoints helps maintain a strong and uniform security posture.
Benefits of Spectrum Security Suite
Implementing Spectrum Security Suite provides a multitude of benefits for organizations looking to bolster their cybersecurity defenses. These benefits extend beyond mere threat mitigation to encompass operational efficiency, compliance, and strategic advantage.
Centralized Management and Visibility
One of the most significant advantages is the centralized management console. This allows IT and security teams to monitor, manage, and report on all security functions from a single interface. This consolidated view provides much-needed visibility into the organization’s security posture, making it easier to identify risks, detect threats, and respond to incidents.
Reduced Attack Surface
By providing a comprehensive suite of security tools, Spectrum Security Suite helps reduce the overall attack surface of an organization. Each layer of defense, from endpoint protection to network security and data encryption, contributes to making it harder for attackers to find and exploit vulnerabilities.
Enhanced Compliance
Many industries are subject to stringent regulatory compliance requirements regarding data protection and cybersecurity (e.g., GDPR, HIPAA, PCI DSS). Spectrum Security Suite is often designed to help organizations meet these compliance mandates by providing the necessary controls and audit trails for data security, privacy, and incident reporting.
Cost-Effectiveness and Scalability
While the initial investment may seem substantial, Spectrum Security Suite can be more cost-effective in the long run compared to purchasing and integrating multiple disparate security solutions. The unified platform often reduces administrative overhead and simplifies maintenance. Furthermore, the modular design allows the suite to scale with the organization’s growth, adding or upgrading components as needed.
Improved Incident Response
With real-time threat intelligence, automated response capabilities, and detailed logging, Spectrum Security Suite significantly enhances an organization’s ability to respond to security incidents. Faster detection and more effective containment measures minimize the damage caused by breaches, reducing recovery time and associated costs.
Implementation and Support
The successful deployment and ongoing management of Spectrum Security Suite are crucial for realizing its full potential. Most vendors offer professional services, training, and ongoing support to ensure that clients can effectively utilize the suite’s features and adapt to evolving threat landscapes.
Deployment Options
Spectrum Security Suite can often be deployed in various ways, including on-premises, in the cloud, or as a hybrid model. The choice of deployment depends on an organization’s existing infrastructure, budget, and specific security requirements. Cloud-based deployments offer scalability and accessibility, while on-premises solutions provide greater control over data.
Ongoing Updates and Threat Intelligence
The cybersecurity landscape is constantly changing, with new threats emerging daily. Spectrum Security Suite is continuously updated with the latest threat intelligence, new detection signatures, and software patches to ensure that it remains effective against the most current threats. This continuous improvement is vital for maintaining a robust security posture.
Expert Support and Training
Reputable vendors provide comprehensive support channels, including technical assistance, knowledge bases, and community forums. Training programs are also often available to educate IT staff on how to effectively configure, manage, and troubleshoot the suite, ensuring maximum utilization of its advanced features.
In conclusion, Spectrum Security Suite represents a modern, integrated approach to cybersecurity. By consolidating a wide array of essential security functionalities into a cohesive platform, it empowers organizations to build resilient defenses, protect their valuable assets, and navigate the complex challenges of the digital age with greater confidence and security. Its comprehensive nature, from advanced threat prevention to robust data protection and identity management, makes it an indispensable tool for any organization serious about safeguarding its digital future.
