The Ground Station’s Gatekeeper: Securing Your Drone Operations
In the rapidly evolving landscape of drone technology and innovation, the seemingly simple question, “what is my windows password,” transcends its typical context of personal computer access to become a foundational pillar of operational security for serious drone professionals and innovators. For many, a Windows-based laptop or desktop serves as the central command and control hub—the ground station—for their unmanned aerial systems (UAS). This includes everything from planning complex autonomous flight missions and programming AI follow modes to processing intricate photogrammetry data for 3D mapping and analyzing sensitive remote sensing information. The integrity of this ground station directly dictates the success, safety, and security of every aerial endeavor.
The Windows operating system, due to its widespread adoption and versatile software ecosystem, is often the environment where mission-critical drone applications reside. Flight planning software, ground control station (GCS) interfaces, data processing suites, and advanced analytics tools typically run on Windows. Consequently, the password protecting this operating system is not merely a login credential; it is the primary gatekeeper to your entire drone operation. An unsecure or easily compromised Windows password can open the door to unauthorized access, potentially leading to devastating consequences: compromised flight plans, manipulated data, stolen intellectual property, or even malicious control of a drone. Understanding and meticulously managing this digital access point is therefore not an option, but an imperative for anyone engaged in the cutting edge of drone technology.
The Windows OS as a Core Component of Drone Ecosystems
Modern drone operations extend far beyond the drone itself. They encompass sophisticated software platforms for everything from pre-flight checks and real-time monitoring to post-flight data analysis and archival. Many high-end commercial drone systems, especially those involved in mapping, surveying, agriculture, and infrastructure inspection, rely heavily on Windows-based PCs to run specialized software. These applications might include photogrammetry software like Pix4D or Agisoft Metashape, GIS platforms, custom scripting environments for AI algorithm development, or proprietary ground control software. The seamless integration and robust capabilities offered by these Windows applications make the operating system an indispensable tool for unlocking the full potential of UAS technology.
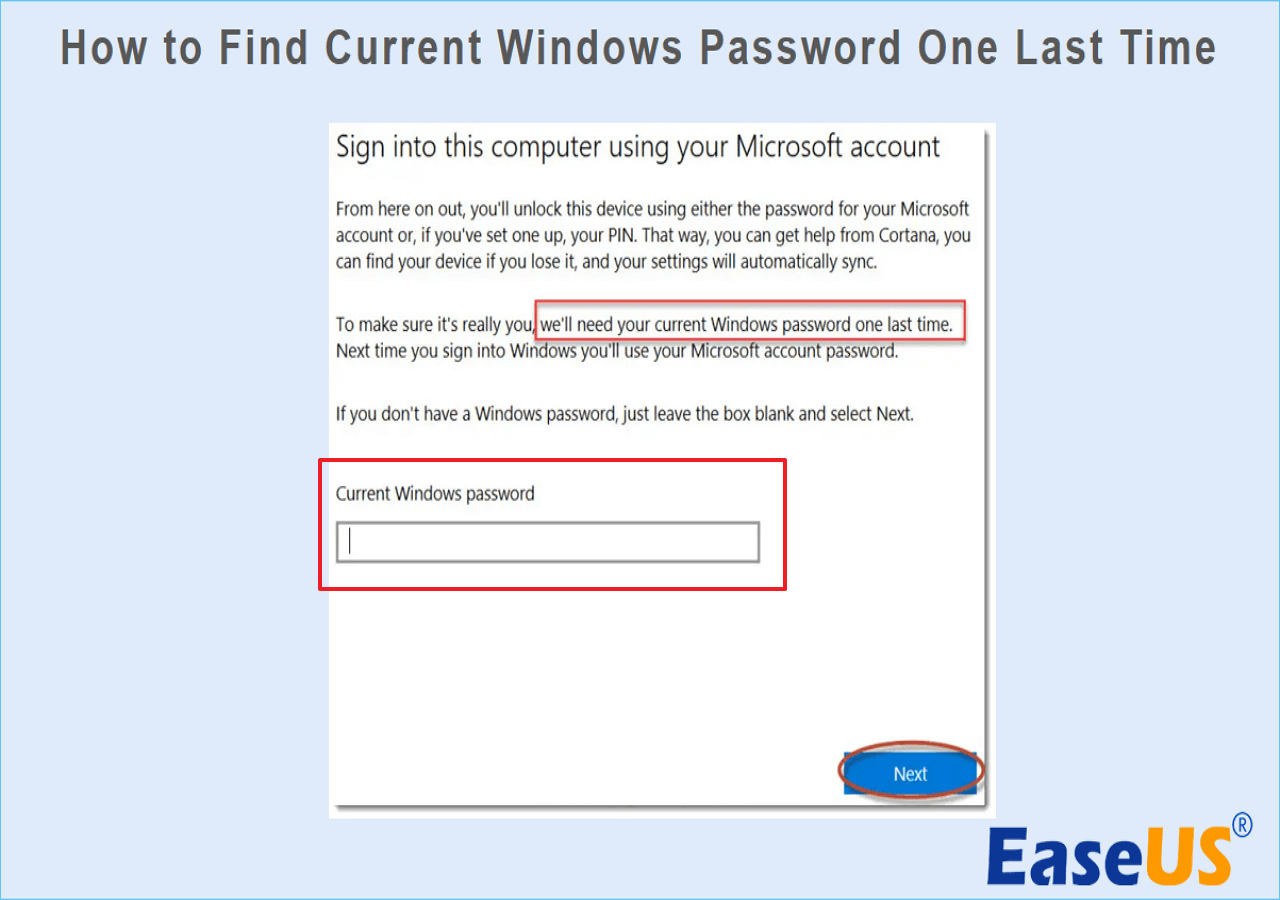
The Critical Role of User Authentication
User authentication, spearheaded by your Windows password, acts as the initial and often most crucial layer of defense for your digital assets. It ensures that only authorized personnel can access the computer hosting your drone operation’s nerve center. This isn’t just about preventing a casual snooper; it’s about thwarting targeted attempts by competitors, malicious actors, or even disgruntled former employees who might seek to disrupt your operations, steal your data, or compromise your equipment. In the context of drone tech, where innovation often means proprietary algorithms, unique data sets, and sensitive client projects, robust user authentication is paramount. It protects not only the hardware but also the invaluable intellectual capital stored within.
Preventing Unauthorized Access to Flight Parameters and Sensitive Data
Imagine a scenario where a competitor gains access to your Windows ground station. They could potentially steal your meticulously planned autonomous flight paths, learn your unique data acquisition methodologies for remote sensing, or even upload corrupted firmware updates. For operations involving AI Follow Mode, unauthorized access could mean the theft of the AI’s training data or algorithmic secrets. In sectors like defense, critical infrastructure inspection, or sensitive research, the implications of such a breach are catastrophic, ranging from severe financial losses and reputational damage to national security risks. Your Windows password, therefore, directly safeguards the integrity of your flight parameters, your collected data, and the sensitive operational details that underpin your technological advantage.
Protecting Intellectual Property and Mission-Critical Data
The cutting edge of drone technology thrives on innovation, which inherently generates valuable intellectual property (IP) and mission-critical data. From proprietary AI algorithms guiding autonomous flight to high-resolution data sets used for precision agriculture or urban planning, the information stored and processed on a Windows ground station is often the lifeblood of a drone enterprise. Answering “what is my windows password” with a strong, unique, and well-managed solution is fundamental to protecting these invaluable assets from theft, corruption, or unauthorized disclosure, thereby safeguarding the very foundation of your drone tech innovation.
Safeguarding Aerial Mapping and Remote Sensing Outputs
Aerial mapping and remote sensing are powerhouses of data generation, producing everything from intricate 3D models of construction sites to detailed multispectral imagery for crop health analysis. These outputs represent significant investments in time, resources, and specialized expertise. For instance, a drone company specializing in creating digital twins of infrastructure assets might store terabytes of highly detailed geometric data, critical for maintenance and planning. Similarly, an agricultural tech firm might house years of remote sensing data, revealing patterns and insights that drive precision farming decisions. A compromised Windows password could expose these proprietary maps, models, and data sets, allowing competitors to replicate your work, undermining your competitive edge. Furthermore, sensitive client data, such as property layouts or industrial espionage targets, could be leaked, leading to severe legal and financial repercussions.
Data Integrity for Autonomous Flight and AI Development
The development of autonomous flight capabilities and AI-driven drone functionalities relies heavily on vast quantities of accurate, untampered data. Training sophisticated AI models for object recognition, autonomous navigation, or predictive maintenance requires clean, validated data sets. If a ground station’s security is breached via a weak Windows password, the integrity of this data is at risk. Malicious actors could inject false data, subtly alter existing data points, or corrupt training sets, leading to flawed AI models that could cause catastrophic failures during autonomous operations. This not only jeopardizes the safety and reliability of your drones but also erodes trust in your technological advancements. Ensuring the absolute integrity of your data through robust access control is therefore a non-negotiable aspect of advancing AI and autonomous flight.
Compliance and Confidentiality in Commercial Drone Operations
Commercial drone operations often involve handling sensitive client information, adhering to strict regulatory compliance standards (e.g., GDPR, HIPAA if personal data is collected, or specific aviation authority regulations), and maintaining contractual confidentiality agreements. For example, a drone conducting inspections for a utility company might collect data about critical infrastructure vulnerabilities, which must remain confidential. Similarly, surveying a private property or a secure facility involves handling data that cannot be publicly disclosed. A weak Windows password on the ground station is a direct threat to these obligations. A data breach could result in hefty fines, legal action, loss of contracts, and irreparable damage to your professional reputation. Understanding that your Windows password is a key component in maintaining data confidentiality and regulatory compliance elevates its importance within the realm of professional drone tech.
Best Practices for Digital Security in Drone Tech
Given the critical role of the Windows ground station in drone operations and innovation, implementing robust digital security practices is non-negotiable. The answer to “what is my windows password” must always be a carefully constructed, securely managed credential. These best practices extend beyond simple password creation to encompass a holistic approach to securing your digital environment, ensuring the sustained reliability and integrity of your drone technology endeavors.
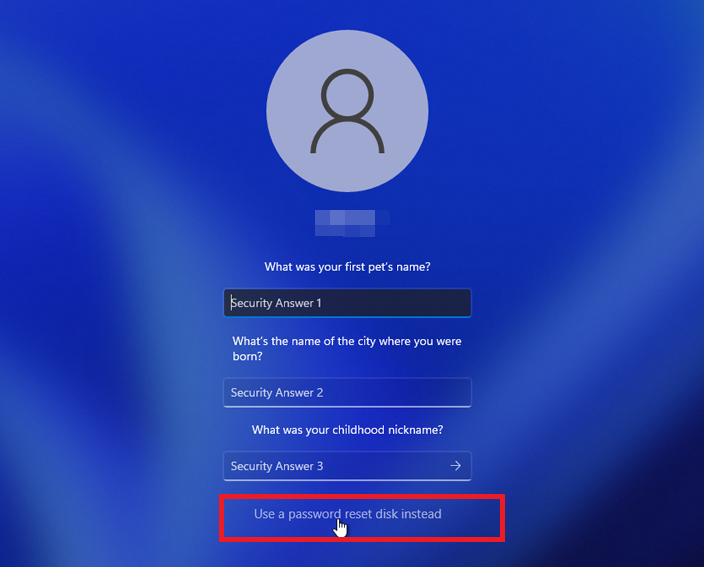
Strong Password Policies
The first line of defense is a strong password. A robust Windows password should be:
- Lengthy: Aim for at least 12-16 characters. Longer passwords are exponentially harder to crack.
- Complex: Incorporate a mix of uppercase and lowercase letters, numbers, and special characters. Avoid easily guessable information like birthdates, pet names, or sequential numbers.
- Unique: Never reuse passwords across different accounts or systems. If one service is breached, your other accounts remain secure.
- Random: Use a password manager to generate and store truly random, complex passwords. This eliminates the need to remember them, reducing the temptation to use simpler ones.
For drone operators, especially those managing multiple systems or teams, implementing a strict password policy across all Windows ground stations and associated accounts is vital. This policy should be regularly reviewed and enforced.
Multi-Factor Authentication (MFA) for Enhanced Protection
Even the strongest password can theoretically be compromised. Multi-Factor Authentication (MFA) adds a crucial second (or third) layer of security. MFA requires users to provide two or more verification factors to gain access, typically something they know (password), something they have (a phone, a hardware token), or something they are (biometrics like a fingerprint). Many Windows systems support MFA, including Windows Hello for biometrics and integration with authenticator apps. Implementing MFA on your Windows ground station means that even if a malicious actor somehow obtains your password, they cannot access your system without the second factor, significantly bolstering security for your drone data and control systems.
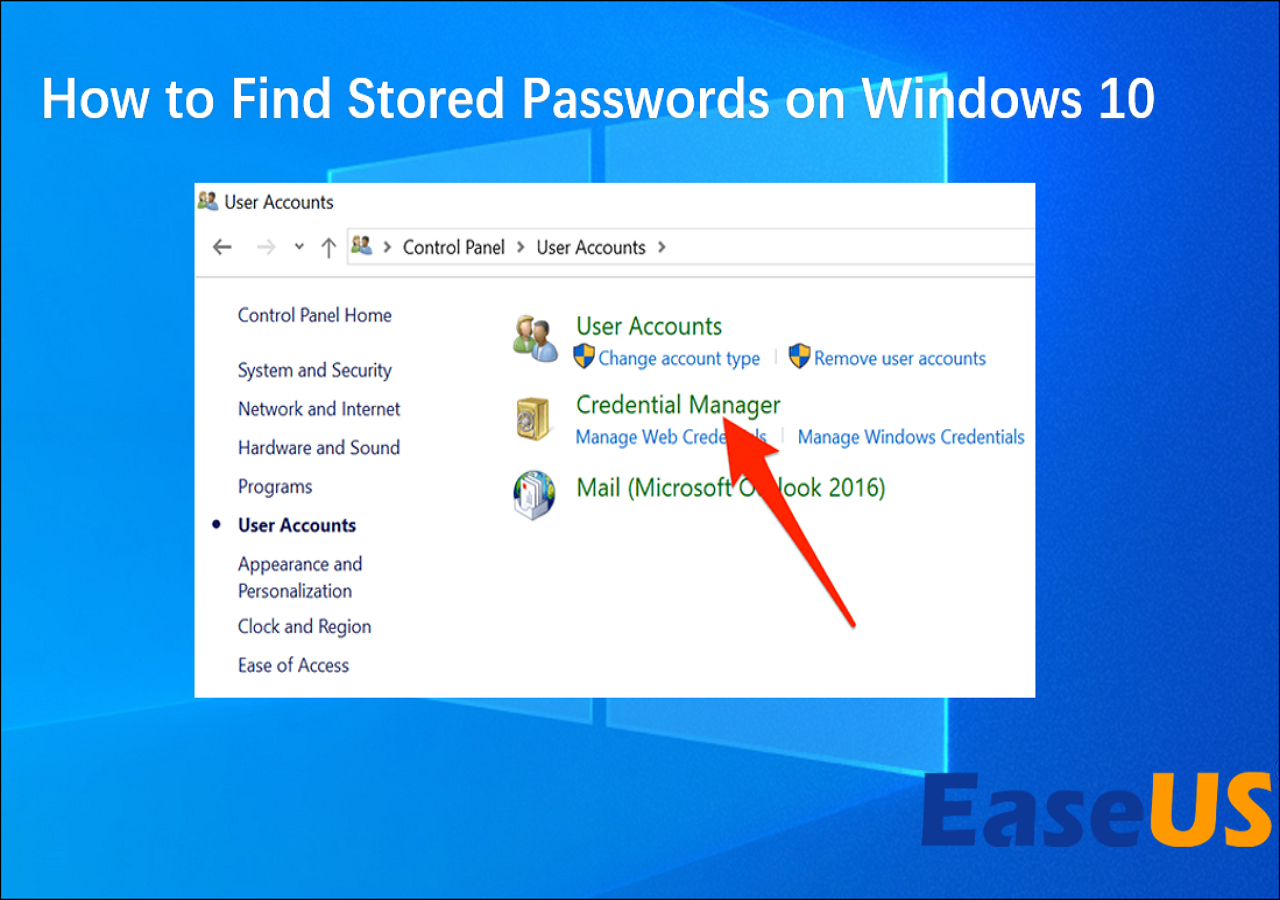
Regular Security Audits and Software Updates
The digital threat landscape is constantly evolving. Operating systems and software applications regularly discover vulnerabilities that attackers can exploit. Therefore, keeping your Windows operating system and all drone-related software (GCS applications, firmware update tools, data processing suites) consistently updated is paramount. Enable automatic updates for Windows whenever possible, and diligently apply patches for all third-party drone software. Beyond updates, conduct regular security audits of your ground station. This includes scanning for malware, checking firewall settings, and reviewing user access logs. Proactive maintenance is key to mitigating emerging threats and ensuring that your innovative drone tech remains secure.
Secure Data Storage and Backup Strategies
Your drone’s collected data – whether it’s mapping coordinates, thermal imagery, or remote sensing outputs – is an invaluable asset. Implement secure data storage solutions for both active and archived data. For Windows systems, BitLocker drive encryption can protect data at rest, making it unreadable without the correct key, even if the physical drive is stolen. When using cloud storage for backups, choose reputable providers that offer strong encryption and security protocols, and ensure your data is encrypted both in transit and at rest. Additionally, maintain robust offline backup strategies for critical data, storing backups in secure, geographically separate locations to protect against localized disasters or cyber-attacks that might impact your primary systems.
Beyond the Basics: Advanced Safeguards for Innovation
As drone technology advances into more complex realms like fully autonomous fleets, sophisticated AI analytics, and remote sensing for critical infrastructure, the security measures protecting these innovations must also evolve. Moving beyond basic password hygiene, adopting advanced safeguards is crucial for maintaining a competitive edge and ensuring the resilience of your operations in the face of increasingly sophisticated cyber threats.
Network Security for Ground Control Stations
The ground control station isn’t an island; it’s connected to various networks for internet access, data transfer, and communication with drones. Robust network security is essential. This includes:
- Secure Wi-Fi: Always use strong encryption protocols (WPA3 or WPA2-Enterprise) for Wi-Fi networks connected to your ground station. Avoid public or unsecured Wi-Fi networks when handling sensitive drone data.
- Virtual Private Networks (VPNs): When accessing remote servers or transferring data over public internet, use a reputable VPN to encrypt your traffic and protect against eavesdropping.
- Firewall Configuration: Properly configure your Windows firewall to restrict incoming and outgoing connections to only those necessary for drone operations, blocking malicious traffic.
- Network Segmentation: For larger operations, segmenting your network can isolate drone-related systems from general office networks, limiting the spread of potential breaches.
These measures collectively create a more secure perimeter around your ground station, protecting data as it moves to and from your innovative drone platforms.
Device Management and Remote Wipe Capabilities
For organizations operating multiple drones or managing a fleet of ground stations and associated devices, centralized device management is critical. Solutions that allow for remote monitoring, configuration, and security policy enforcement are invaluable. Furthermore, in the unfortunate event of a ground station laptop or tablet being lost or stolen, the ability to remotely wipe its data becomes an indispensable feature. This capability prevents sensitive flight plans, proprietary mapping data, or AI development secrets from falling into the wrong hands, thus mitigating severe intellectual property loss and operational disruption. Implementing such controls ensures that the physical security of your devices is backed by powerful digital safeguards.
User Permissions and Role-Based Access Control (RBAC)
In team-based drone operations, not all users require the same level of access to all data or software functions. Implementing Role-Based Access Control (RBAC) on your Windows ground station and associated drone applications is a best practice. RBAC ensures that each team member only has access to the resources and functionalities necessary for their specific role. For example, a pilot might have access to flight planning software but not to advanced AI model training data, while a data analyst would have the inverse. This principle of “least privilege” significantly reduces the attack surface, minimizing the potential impact of an insider threat or if a single user account is compromised. It protects sensitive components of your innovation pipeline from unnecessary exposure.
Proactive Threat Intelligence and Incident Response
Staying ahead of cybersecurity threats requires more than just reactive measures. Integrating proactive threat intelligence into your security strategy means actively monitoring for new vulnerabilities, understanding emerging attack vectors relevant to drone technology, and subscribing to industry-specific security advisories. Furthermore, having a clearly defined incident response plan is crucial. This plan outlines the steps to take in the event of a security breach, from detection and containment to eradication and recovery. For companies pioneering in AI-driven autonomous flight or highly sensitive remote sensing, a well-rehearsed incident response plan can significantly reduce the damage from a cyberattack, ensuring continuity and protecting the fruits of their technological innovation. The question “what is my windows password” must evolve into a comprehensive strategy for safeguarding your entire drone tech ecosystem.
