Pioneering Secure Digital Asset Recovery
iPhone Lost Mode represents a significant innovation in personal device security and asset recovery, leveraging a sophisticated suite of integrated technologies to protect user data and facilitate the return of a lost or stolen device. It’s more than just a tracking feature; it’s a comprehensive digital safety net engineered into Apple’s ecosystem, designed to provide peace of mind in an increasingly interconnected world. At its core, Lost Mode exemplifies the critical role of thoughtful technological design in addressing real-world problems like device loss, offering a robust solution that blends cutting-edge location services with intelligent data management. This innovation transforms a potentially chaotic and stressful event into a manageable situation through a carefully orchestrated sequence of remote actions.

Leveraging Integrated Location and Communication Technologies
The efficacy of iPhone Lost Mode is rooted deeply in the seamless integration of various core technologies. Foremost among these are advanced Global Positioning System (GPS) capabilities, complemented by Wi-Fi triangulation and cellular network positioning. When a device is marked as lost, these systems work in concert to pinpoint its last known location with remarkable accuracy, often down to a few meters in urban environments. This sophisticated multi-modal location tracking ensures that even if a direct GPS signal is unavailable, alternative methods can still provide a strong directional indication.
Beyond mere location, Lost Mode leverages continuous, secure communication channels. The device, once marked as lost through iCloud, maintains an active connection to Apple’s servers. This persistent link allows for the remote transmission of commands and the receipt of location updates, even if the device is not actively being used. This constant “handshake” between the lost device and the user’s iCloud account is a testament to the innovation in network protocols and persistent connectivity that underpins modern mobile ecosystems. Furthermore, the feature is designed to conserve battery life while tracking, optimizing its power consumption so that location updates can continue for as long as possible, a crucial design consideration for effective asset recovery. This intelligent power management is a subtle yet vital aspect of its technological prowess, ensuring that the recovery window is maximized.
The Power of Cloud-Based Ecosystems
Central to Lost Mode’s functionality is its reliance on a robust cloud infrastructure—specifically, Apple’s iCloud. This cloud-based ecosystem serves as the central command and control hub for managing a lost device. When a user activates Lost Mode, they are not directly interacting with the physical device, but rather sending commands to their iCloud account, which then relays these instructions to the iPhone. This architecture offers several distinct advantages. Firstly, it allows for remote activation from any web-enabled device or another Apple product, providing flexibility and immediate response capabilities regardless of the user’s physical location.
Secondly, iCloud acts as a secure repository for device data, enabling functions like remote erase. This feature, while extreme, is an invaluable last resort for protecting sensitive personal information from falling into the wrong hands. The ability to wipe a device completely and unlink it from the user’s Apple ID ensures that even if the physical device is irrecoverable, the digital footprint remains secure. This cloud-centric approach also facilitates the “Find My network,” a groundbreaking innovation that allows millions of Apple devices worldwide to anonymously and securely help locate lost items, even when they are offline. This crowd-sourced tracking capability extends the reach of Lost Mode significantly, turning every participating Apple device into a potential beacon for a lost iPhone, iPad, or Mac. This demonstrates a powerful fusion of individual device security with a collective, anonymized network intelligence, setting a new benchmark for device recovery systems.
Innovation in User Control and Data Protection
Lost Mode isn’t just about passive tracking; it’s an active suite of tools that empower users with a remarkable degree of control over their lost device and its data, even from a distance. This proactive approach to security and recovery is a hallmark of intelligent technological design, placing the user firmly in command during a stressful situation. The innovation lies in making complex remote operations intuitive and accessible, transforming what could be a helpless scenario into one with actionable steps.
Remote Activation and Customization Features
The ability to remotely activate Lost Mode is a cornerstone of its innovative design. From any web browser or another Apple device, users can access their iCloud account and initiate Lost Mode with a few clicks. This immediacy is critical, as every moment counts when a device is lost. Upon activation, Lost Mode automatically performs several critical actions designed to secure the device and aid in its recovery. It immediately locks the iPhone with the user’s passcode, preventing unauthorized access to personal information. If no passcode was previously set, the user is prompted to create one remotely, adding an instantaneous layer of security.
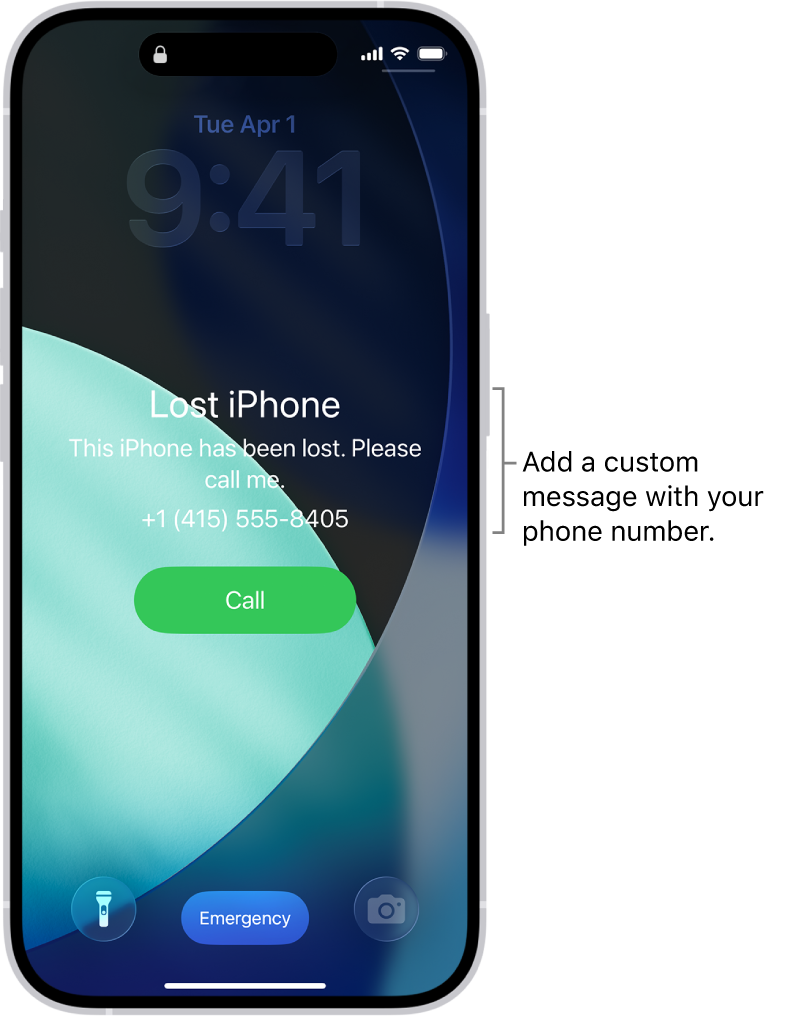
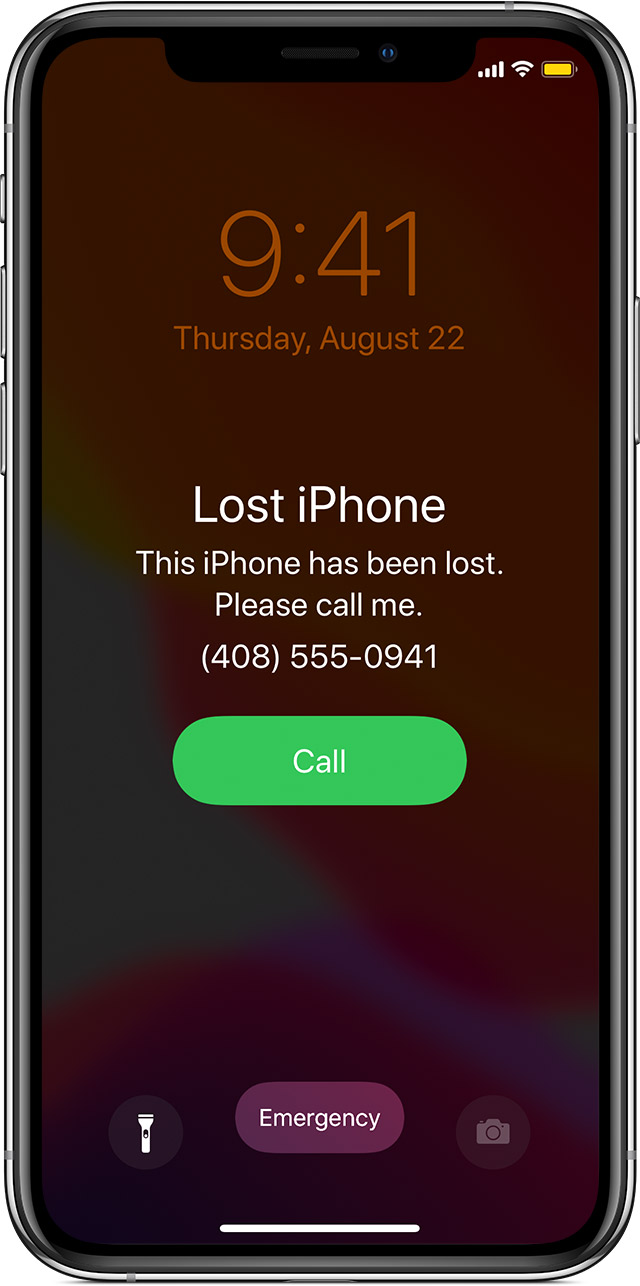
Furthermore, a truly innovative aspect is the customizable message feature. Users can display a custom message on the lock screen of the lost iPhone, along with a contact phone number. This personalized message can be a direct plea to the finder, offering a reward or simply providing instructions on how to return the device. This human element, facilitated by technology, significantly increases the chances of recovery by creating a direct line of communication between the finder and the owner, all without compromising the owner’s personal contact details directly on the device. The device’s functionality is also limited to essential communications, such as allowing incoming calls, while disabling Apple Pay to prevent unauthorized transactions, showcasing a balanced approach to utility and security.
Safeguarding Privacy Through Design
A critical consideration in any advanced tracking technology is privacy, and Lost Mode is meticulously designed to uphold user privacy even while facilitating recovery. The tracking is strictly opt-in and tied to the user’s Apple ID, meaning no one can track a device without the explicit authorization and credentials of the owner. When a device is located via the Find My network, the location data is end-to-end encrypted and anonymous, ensuring that only the owner can see the location of their lost item. Apple cannot see the location of the item, nor can any third-party devices relaying the location. This architectural choice underscores a profound commitment to user privacy, demonstrating how robust security features can coexist with strong privacy protections.
Moreover, the “Erase iPhone” feature, while a last resort, is another testament to this privacy-first approach. By remotely wiping all data and settings, users can prevent their personal information from being accessed if the device is deemed unrecoverable. This complete data sanitization ensures that even if the physical device is compromised, the digital integrity of the user’s identity and information remains intact. This layered approach to privacy, from encrypted location sharing to remote data destruction, positions Lost Mode as a leading example of responsible technology design in an era of increasing digital vulnerability.
Lost Mode’s Impact on the Broader Tech Landscape
iPhone Lost Mode is not merely a standalone feature; it represents a paradigm shift in how we conceive of device security and recovery within connected ecosystems. Its robust functionality and underlying technological architecture have set a high bar, influencing the development of similar features across the tech industry and highlighting the increasing importance of integrated services for smart device management.
A Model for Connected Device Security
The success and widespread adoption of Lost Mode have established it as a benchmark for connected device security. It demonstrates that effective asset recovery systems must be deeply integrated into the operating system and leverage a vast network of supporting infrastructure (cloud services, global location systems, peer-to-peer networks). This integrated approach moves beyond simplistic tracking apps, offering a holistic solution that encompasses location, locking, messaging, and data protection.
This model is particularly relevant as the Internet of Things (IoT) expands, with an ever-growing number of smart devices entering our daily lives. From smartwatches and headphones to vehicles and even industrial equipment, the principles pioneered by Lost Mode—remote management, secure communication, privacy-centric tracking, and data security—are becoming essential blueprints for ensuring the integrity and recoverability of these diverse assets. The ability to manage and secure a fleet of connected devices, whether personal or enterprise-level, increasingly relies on the kind of sophisticated, ecosystem-wide approach exemplified by iPhone Lost Mode. It underscores a fundamental shift from securing individual devices in isolation to securing an entire digital persona across multiple interconnected touchpoints.
Trends in Intelligent Asset Tracking
Lost Mode also serves as a leading indicator for broader trends in intelligent asset tracking. The evolution from basic GPS tracking to the nuanced “Find My network” showcases a move towards more pervasive and energy-efficient location technologies. The innovation of leveraging anonymous, encrypted Bluetooth signals from nearby devices to locate offline items is a game-changer, demonstrating how collective intelligence can overcome traditional limitations of direct network connectivity. This approach has implications for various sectors, from logistics and supply chain management to personal item tracking (e.g., smart tags for keys or wallets).
Furthermore, the sophisticated power management employed by Lost Mode to maximize tracking duration highlights an ongoing trend towards optimizing device longevity for critical functions. As devices become smaller and more power-constrained, intelligent software solutions that balance functionality with energy efficiency will become paramount. These advancements contribute to a future where virtually any valuable asset, regardless of its size or power source, could be intelligently tracked and recovered, all while maintaining stringent privacy and security protocols. This continuous push for more intelligent, efficient, and secure tracking solutions is a testament to the enduring impact of innovations like iPhone Lost Mode.
Ethical Frameworks and Future Trajectories in Tech Innovation
The capabilities of iPhone Lost Mode, while immensely beneficial, also naturally raise important ethical considerations, particularly concerning privacy and data integrity. Addressing these concerns through thoughtful design is crucial for the responsible evolution of technology, and Lost Mode provides a valuable case study in navigating these complexities.
Navigating Privacy and Data Integrity
At the heart of any location-based and remote-control technology lies the delicate balance between utility and privacy. iPhone Lost Mode exemplifies how this balance can be achieved through deliberate architectural choices. The emphasis on end-to-end encryption for location data within the Find My network ensures that only the device owner has access to their device’s whereabouts, even preventing Apple itself from viewing this sensitive information. This design choice sets a high standard for privacy, distinguishing it from systems where data might be accessible to service providers.
The ethical framework surrounding Lost Mode also extends to informed consent. Users explicitly opt-in to these services and are provided with clear explanations of how their data is used and protected. This transparency builds trust, which is fundamental for the widespread adoption of powerful technologies. As tech innovation continues to push boundaries, the lessons from Lost Mode—particularly regarding anonymous data handling, encryption, and user-centric privacy controls—will remain vital in shaping ethical guidelines for future developments in surveillance, tracking, and remote management across all connected devices.
The Horizon of Autonomous Device Management
Looking forward, the principles underlying Lost Mode point towards a future of increasingly autonomous device management and proactive security. Imagine scenarios where devices, equipped with advanced AI, can not only report their location but also intelligently respond to potential threats or abnormal situations. This could involve self-diagnosing issues, autonomously seeking secure environments, or even activating enhanced security protocols based on learned patterns of behavior and environmental context.
The “Find My network” is already a step towards collective intelligence in device recovery. Future innovations might leverage even more sophisticated machine learning algorithms to predict theft patterns, analyze common loss locations, or even coordinate with local authorities more seamlessly and securely. As our physical and digital worlds converge, the need for intelligent systems that can protect our assets and our data will only grow. iPhone Lost Mode, with its pioneering blend of location technology, cloud integration, and user-centric security, serves as a compelling harbinger of this future, continually evolving to meet the complex demands of a hyper-connected world. It’s a testament to how focused innovation can create not just a product feature, but an entire paradigm for secure digital existence.
