In an increasingly interconnected world driven by rapid technological advancements, the security and integrity of data are paramount. From autonomous vehicles navigating complex environments to sophisticated AI algorithms making critical decisions, and from drones meticulously mapping vast terrains to remote sensors collecting vital environmental data, the underlying trust in the information being processed and transmitted is non-negotiable. At the heart of ensuring this trust lies a cryptographic mechanism known as HMAC, or Hash-based Message Authentication Code. While not a household name, HMAC plays a silent yet crucial role in safeguarding the digital fabric of our innovative technologies, acting as a powerful guardian of data authenticity and integrity.
HMAC is a specific type of Message Authentication Code (MAC) that involves a cryptographic hash function and a secret cryptographic key. Its primary purpose is to verify both the data integrity and the authenticity of a message. In simpler terms, it allows a receiver to confirm that a message has not been altered in transit and that it genuinely originates from the expected sender who possesses the secret key. This dual assurance is vital for robust security in any modern tech ecosystem.
The Fundamental Role of HMAC in Digital Security
To truly appreciate HMAC, it’s essential to understand the problems it solves and why it stands as a cornerstone of digital security. In an era where data manipulation and impersonation are constant threats, mechanisms that can reliably detect tampering and verify origin are indispensable.
Beyond Simple Hashing: The Need for Message Authentication
Many are familiar with cryptographic hash functions like SHA-256, which take an input (message) and produce a fixed-size string of characters (hash value or digest). A key property of hash functions is that even a tiny change to the input message results in a drastically different hash value, making them excellent for detecting accidental data corruption. However, a simple hash alone does not provide authenticity. If an attacker intercepts a message and its hash, they can modify the message, compute a new hash for the modified message, and send both to the receiver. The receiver would then compute the hash of the tampered message, find it matches the attacker’s new hash, and unknowingly accept the forged data.
This is where message authentication becomes critical. Authentication ensures that the message originates from an authorized source. HMAC achieves this by incorporating a secret key known only to the sender and the legitimate receiver. Without this shared secret, an attacker cannot generate a valid HMAC for a modified message, thus preventing successful tampering and impersonation.
Core Principles of Operation: Keys, Hashes, and Integrity
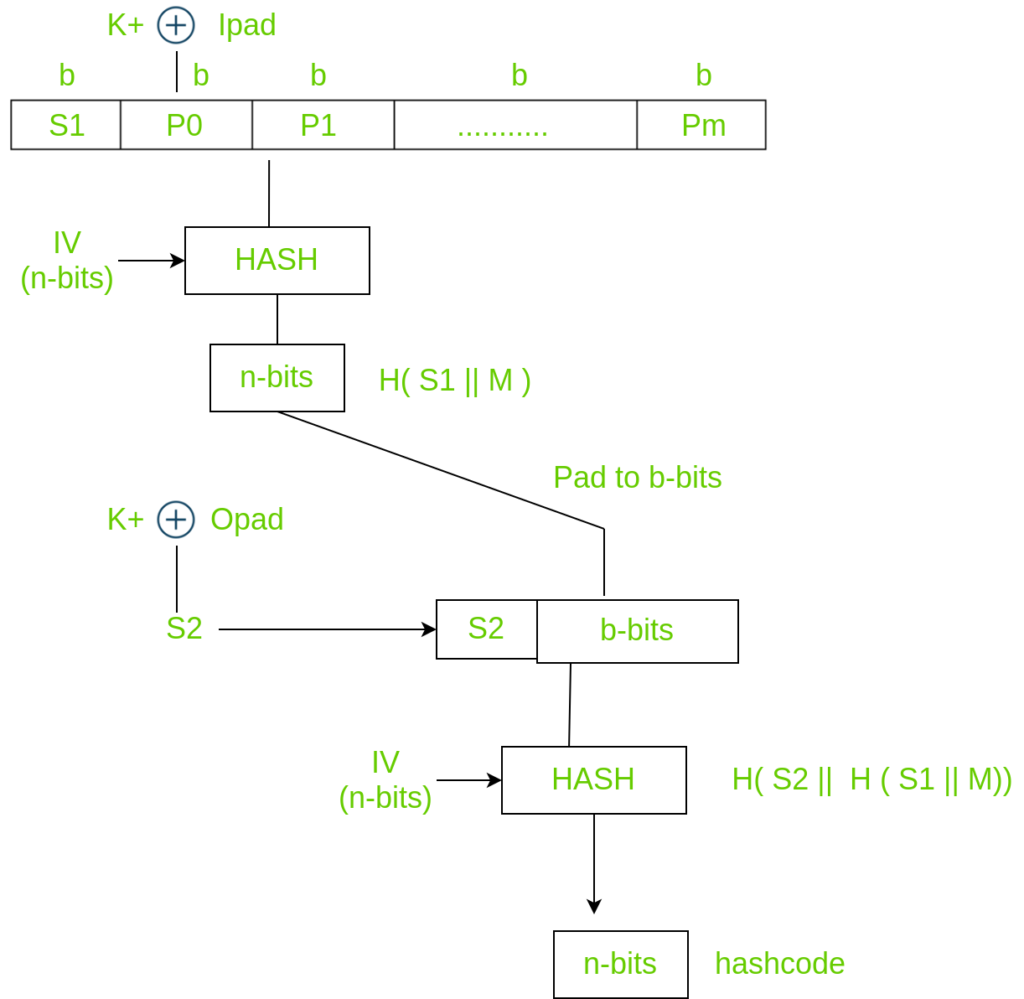
The operation of HMAC is elegantly simple yet cryptographically robust. It combines a secret key with the message data using a cryptographic hash function in a specific, well-defined manner. The process typically involves two nested hash operations:
- Inner Hash: The secret key is padded and XORed with an inner padding constant, then concatenated with the message and hashed.
- Outer Hash: The secret key is padded and XORed with an outer padding constant, then concatenated with the result of the inner hash and hashed again.
The final output is the HMAC tag.
When a sender wants to transmit a message securely, they compute the HMAC for that message using their secret key. They then send the message along with the HMAC tag. Upon receiving both, the receiver uses the same secret key and the same HMAC algorithm to independently compute the HMAC for the received message. If the computed HMAC matches the received HMAC tag, the receiver can be confident that:
- The message has not been altered since it was sent (data integrity).
- The message originated from someone who possesses the correct secret key (data authenticity).
This mechanism effectively thwarts man-in-the-middle attacks where an adversary attempts to intercept and alter communications.
How HMAC Secures Modern Tech & Innovation
In the realm of Tech & Innovation, HMAC’s applications are pervasive, securing critical functions and data across diverse cutting-edge domains. Its ability to provide both integrity and authenticity is particularly vital where trust in data and commands is non-negotiable.
Protecting Data Integrity in Autonomous Systems
Autonomous systems, from self-driving vehicles to advanced drones performing automated tasks, rely heavily on the integrity of their sensor data, navigation instructions, and control commands. Imagine an autonomous drone performing critical infrastructure inspection:
- Navigation Commands: Commands sent to adjust flight paths, altitudes, or speeds must be authentic and untampered. An attacker altering a command could send the drone off course or into a collision. HMAC ensures that these commands originate from a trusted source and haven’t been maliciously modified.
- Sensor Data: Data streamed from LiDAR, radar, or ultrasonic sensors, crucial for obstacle avoidance and environmental mapping, must maintain integrity. Tampering with this data could lead the autonomous system to misinterpret its surroundings, causing accidents or faulty operation. HMAC can secure these data streams.
- System Updates: Software and firmware updates for autonomous systems are highly sensitive. HMAC can verify the authenticity and integrity of these updates, ensuring that only legitimate, untampered code is installed, protecting against malicious injections that could compromise the system.
Ensuring Authenticity in Remote Sensing and IoT
Remote sensing applications, often powered by drones or vast networks of IoT devices, generate enormous volumes of data that feed into mapping, environmental monitoring, agriculture, and urban planning.
- Data Provenance: When a remote sensor (e.g., a drone-mounted camera or an environmental IoT sensor) captures data, HMAC can be used to tag that data at the source. This ensures that when the data is later processed or analyzed, its origin can be authenticated, preventing the injection of fraudulent or misleading data into critical datasets. For instance, in precision agriculture, ensuring that crop health data genuinely comes from a specific field sensor is vital for accurate decision-making.
- Command and Control: IoT devices are often controlled remotely. Commands sent to these devices (e.g., adjust a smart city sensor’s parameters, trigger an action on a remote monitoring station) must be authenticated. HMAC ensures that only authorized entities can issue these commands, preventing unauthorized control or disruption of IoT networks.
- Edge Computing Security: As more processing moves to the edge, devices like AI-powered sensors generate insights locally. HMAC can protect the integrity of these derived insights before they are transmitted to central cloud systems, ensuring that local computations are not maliciously altered before aggregation.
Safeguarding Software Updates and AI Model Integrity
The continuous development and deployment cycles of AI models and software applications demand robust update mechanisms.
- Secure Software Distribution: Software updates, whether for an operating system, an application, or an AI model, are prime targets for attackers who aim to inject malware or backdoors. When a software vendor releases an update, they can compute an HMAC over the entire update package using a secret key. Users can then verify this HMAC upon download, ensuring that the update is genuine and hasn’t been tampered with by an adversary. This is a standard practice for secure software delivery pipelines.
- AI Model Integrity: AI models, especially those used in critical applications like medical diagnostics or financial fraud detection, represent significant intellectual property and are sensitive to subtle alterations. If an AI model or its parameters are tampered with, it could lead to incorrect predictions, biased outcomes, or even malicious behavior. HMAC can be used to verify the integrity of stored AI models, model updates, and data used for training, providing assurance that the AI system is operating on untainted information. This is crucial for maintaining trust and reliability in AI-driven decision-making processes.
Diving Deeper: The Cryptographic Mechanics of HMAC
Understanding the underlying cryptographic principles of HMAC reveals its strength and why it’s so widely adopted across various security standards.
The Algorithm Behind the Assurance: A Step-by-Step Overview
HMAC is formally defined in RFC 2104 and commonly used with various hash functions. The general construction involves:
- Key Preparation: The secret key (
K) is adapted to the block size of the hash function. IfKis longer than the hash function’s block size, it’s hashed. If it’s shorter, it’s padded with zeros. - Inner Padding: The prepared key is XORed with a specific padding constant (
ipad). - Inner Hash: The result from step 2 is concatenated with the message (
M) and then hashed using the chosen cryptographic hash function (H). This producesH(K ⊕ ipad || M). - Outer Padding: The prepared key is XORed with a different padding constant (
opad). - Outer Hash: The result from step 4 is concatenated with the output of the inner hash (from step 3) and then hashed again. This produces
H(K ⊕ opad
H(K ⊕ ipad The final output of this process is the HMAC tag. This double-hashing approach, combined with the use of a secret key in both stages, provides strong resistance against various cryptographic attacks.
Why Secret Keys are Paramount
The security of HMAC rests entirely on the secrecy of the shared key. If an attacker gains knowledge of the secret key, they can generate valid HMACs for any message, completely undermining the authentication and integrity guarantees. Therefore, robust key management practices are paramount for any system employing HMAC:
- Secure Generation: Keys must be generated using cryptographically secure random number generators.
- Secure Storage: Keys should be stored in secure modules (e.g., Hardware Security Modules - HSMs) and never exposed in plain text.
- Secure Exchange: Keys must be exchanged between legitimate parties using secure out-of-band methods or established key agreement protocols (like Diffie-Hellman) that protect against eavesdropping.
- Key Rotation: Keys should be regularly rotated to limit the impact of a potential key compromise.
Choosing the Right Hash Function: SHA-256 and Beyond
HMAC can be used with any iterative cryptographic hash function. Common choices include:
- HMAC-MD5: Based on the MD5 hash function. While HMAC-MD5 is considered cryptographically stronger than MD5 alone due to the secret key, MD5 itself is broken for collision resistance. Thus, HMAC-MD5 is generally discouraged for new applications where strong security is required.
- HMAC-SHA1: Based on SHA-1. Similar to MD5, SHA-1 has known weaknesses (collision attacks are theoretically feasible), making HMAC-SHA1 also deprecated for most new deployments, especially in high-security contexts.
- HMAC-SHA256/HMAC-SHA384/HMAC-SHA512: These use the SHA-2 family of hash functions and are currently considered cryptographically secure and are widely recommended. HMAC-SHA256 is particularly prevalent.
- HMAC-SHA3 (Keccak): Based on the SHA-3 (Keccak) hash function, which is a newer standard and also considered very secure.
The choice of hash function directly impacts the security strength of the HMAC. For critical tech innovations, sticking to modern, unbroken hash functions like SHA-256 or SHA-3 is imperative.
Practical Applications and Implementation in Innovative Systems
HMAC's versatility makes it a go-to tool for securing various components of the modern digital landscape, from web services to decentralized technologies.
Securing APIs and Web Communications
Many innovative applications, including those involving AI services, remote sensing data processing, and drone fleet management, communicate via Application Programming Interfaces (APIs). HMAC is frequently used to secure these API calls:
- API Authentication: When an client application makes a request to an API, it can include an HMAC of the request parameters (e.g., URL, timestamp, payload) using a shared secret key. The API server then independently computes the HMAC and verifies it against the received one. This ensures that the API request is legitimate and hasn't been tampered with, protecting against unauthorized access and data manipulation.
- Token-based Authentication (e.g., JWTs): JSON Web Tokens (JWTs) are commonly used for stateless authentication in web applications. While JWTs can be signed using public-key cryptography (RSA, ECDSA), they can also be signed using HMAC (e.g., HS256, HS384, HS512). The server signs the token with a secret key, and the client (or another server) can verify the token's integrity using the same secret, ensuring the token hasn't been tampered with after issuance. This is critical for microservices architectures and distributed systems.
Authenticating Distributed Ledger Technologies and Blockchain
While blockchain itself employs robust cryptographic hashing and public-key cryptography, HMAC can play a role in securing certain aspects or peripheral systems:
- Off-chain Data Integrity: For applications that bridge off-chain data with smart contracts (oracles), HMAC could be used to ensure the integrity and authenticity of the data feed before it's submitted to the blockchain. An oracle provider could sign the data using HMAC, allowing the consuming entity to verify its origin and untampered state before using it in a smart contract.
- Secure API Access to Blockchain Nodes: For applications interacting with blockchain nodes via APIs, HMAC can provide an additional layer of security for API requests, similar to general API security, ensuring that interactions with the blockchain are authorized and untampered.
Best Practices for Robust HMAC Deployment
Implementing HMAC effectively requires adherence to best practices:
- Use Strong, Random Keys: Never hardcode keys or use predictable keys. Generate keys using cryptographically secure random number generators and ensure sufficient length (e.g., 256 bits for HMAC-SHA256).
- Protect the Secret Key: The security of HMAC is entirely dependent on the secrecy of the key. Keys must be stored securely (e.g., in HSMs, secure enclaves, or protected configuration files) and never transmitted in plain text.
- Choose a Cryptographically Secure Hash Function: Use current, recommended hash functions like SHA-256 or SHA-3 variants. Avoid deprecated algorithms like MD5 or SHA-1.
- Time-Varying Inputs: To protect against replay attacks (where an attacker simply re-sends a legitimate message and its HMAC), include a timestamp or a nonce (a number used once) in the message that is part of the HMAC calculation. The receiver can then check if the timestamp is fresh or if the nonce has been seen before.
- Implement Correctly: Ensure the HMAC algorithm is implemented strictly according to the standard (e.g., RFC 2104) to avoid subtle vulnerabilities. Use established cryptographic libraries rather than attempting to implement from scratch.
The Future of Trust: HMAC's Enduring Relevance in an Evolving Landscape
As technology continues to accelerate, with AI becoming more sophisticated, autonomous systems more prevalent, and data flowing at unprecedented rates, the need for foundational security mechanisms like HMAC will only grow.
Countering Emerging Cyber Threats
The sophistication of cyber threats is constantly evolving. While HMAC isn't a silver bullet for all security challenges (it doesn't provide confidentiality, for instance, which requires encryption), its role in providing integrity and authenticity remains critical. As attackers develop new methods to tamper with data and impersonate legitimate entities, robust authentication mechanisms like HMAC serve as a fundamental defense layer, preventing adversaries from manipulating critical operational data or injecting false commands into advanced systems.
Adapting to Quantum Computing Challenges
The advent of quantum computing poses a potential threat to many current cryptographic algorithms, particularly those based on factoring large numbers or discrete logarithms (e.g., RSA, ECC for digital signatures). While quantum computers might eventually break certain hash functions by reducing their effective security strength, the core construction of HMAC, which relies on the "random oracle" model of hash functions, is believed to be more resistant to quantum attacks than public-key cryptography. Post-quantum cryptographic research includes developing quantum-resistant hash functions. Should such functions become necessary, HMAC can simply be re-instantiated with these new, quantum-safe hash algorithms (e.g., HMAC-SHA3-512 with a quantum-resistant permutation), preserving its fundamental security guarantees. This adaptability ensures HMAC’s continued relevance in a future defined by quantum technologies.
In conclusion, HMAC is far more than just a cryptographic algorithm; it is a critical enabler of trust in the digital age. By providing an unforgeable assurance of data integrity and authenticity, it underpins the secure operation of everything from complex AI systems and autonomous vehicles to the vast networks of IoT devices and secure web communications. As we push the boundaries of innovation, HMAC will continue to serve as a silent, yet powerful, guardian of the veracity of our digital world, ensuring that the technologies of tomorrow can operate with the confidence and reliability that society demands.
