The seemingly enigmatic title, “What is Ghost Weak To in Pokemon,” presents a unique challenge when transposed into the realm of advanced technology. While the original query pertains to the elemental weaknesses of a specific type within a popular game, we can draw a powerful analogy to explore a critical aspect of modern aerial innovation: the vulnerabilities inherent in “ghost” or stealth drone technology. In this context, “ghost” refers to unmanned aerial vehicles (UAVs) designed for low observability, minimal detectability, and clandestine operations. Just as every Pokémon type possesses distinct weaknesses, even the most advanced stealth drone, a marvel of Tech & Innovation, is susceptible to specific countermeasures and detection methods.

This article will delve into the technical “weaknesses” that advanced stealth drones face, exploring the principles of their low observability and the cutting-edge technologies being developed to counter them. We will stick strictly to the domain of Tech & Innovation, focusing on aspects like autonomous flight, remote sensing, AI-driven analysis, and advanced materials, using the “weakness” framework from the title to structure our understanding of drone vulnerabilities.
The Elusive Nature of “Ghost” Drones: Defining Stealth in UAVs
Before we can identify what “ghost” drones are weak to, it’s crucial to understand what makes them so elusive in the first place. “Ghost” drones, or stealth UAVs, represent the pinnacle of aeronautical engineering designed to operate with minimal detectability across various spectrums. Their primary objective is to penetrate contested airspace or conduct covert surveillance without being identified or intercepted.
Characteristics of Low-Observable Drones
The design philosophy behind stealth UAVs centers on reducing their signature across several domains:
- Radar Cross-Section (RCS) Reduction: This is perhaps the most well-known aspect of stealth. It involves shaping the drone to deflect radar waves away from the emitter, using radar-absorbent materials (RAM) that convert radar energy into heat, and minimizing external protrusions. The goal is to make the drone appear as small as possible, or even non-existent, on radar screens.
- Infrared (IR) Signature Management: Engines and exhaust plumes are significant sources of heat. Stealth drones incorporate advanced cooling systems, redesigned exhaust nozzles to mix hot gases with cooler ambient air, and coatings that reduce thermal emissivity to minimize their IR footprint, making them harder for thermal cameras and IR sensors to detect.
- Acoustic Signature Suppression: Even small drones can produce noticeable sound from propellers and motors. Stealth designs often feature slower-spinning, multi-bladed propellers, electric propulsion systems for quieter operation, and aerodynamic shapes that reduce airframe noise. Larger stealth UAVs might use advanced acoustic baffling.
- Visual Obscuration: While less effective at night or in adverse weather, visual stealth involves employing camouflage patterns, low-reflectivity coatings, and operating at high altitudes or within cloud cover to reduce optical detection. Some experimental designs even explore active camouflage.
- Electromagnetic Emissions Control: Drones communicate, navigate, and sense using various electromagnetic signals (radio, GPS, lidar, radar altimeters). Stealth UAVs meticulously manage these emissions, using directional antennas, burst transmissions, frequency hopping, and secure data links to minimize their electronic footprint and prevent interception or geo-location by adversaries.
Operational Challenges of Undetectable Flight
Achieving true undetectability is a monumental engineering feat, and it comes with its own set of trade-offs. Stealth designs often prioritize low observability over payload capacity, speed, or endurance. Complex materials and shaping add to manufacturing costs and maintenance requirements. Moreover, maintaining stealth in diverse operational environments – from dense urban areas to open skies – presents dynamic challenges that require sophisticated flight management and adaptive autonomy. Despite these advancements, no system is entirely impervious, leading us to examine their inherent vulnerabilities.
Identifying Key Vulnerabilities: The “Elemental” Weaknesses of Stealth Tech
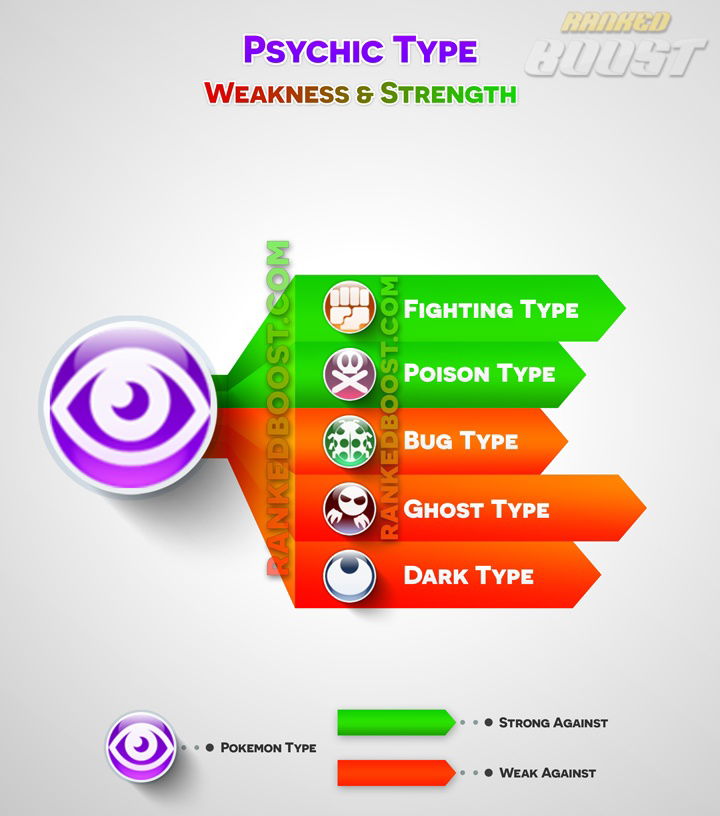
Just as a Ghost-type Pokémon has specific types it’s weak to, stealth drones possess intrinsic vulnerabilities that, when exploited, can compromise their low-observable characteristics. These “weaknesses” often correspond to the very physical principles they attempt to circumvent.
Acoustic Signatures: The Sound Barrier
While efforts are made to silence drones, particularly smaller ones, the fundamental physics of propulsion often creates an acoustic signature. Large, heavy stealth UAVs, though potentially equipped with advanced noise reduction, still displace significant air. Smaller drones, while generally quieter, are still audible at closer ranges.
- Passive Acoustic Detection: Arrays of sensitive microphones, often combined with AI-driven sound analysis, can detect, classify, and even triangulate the position of drones based on their unique acoustic profiles. Machine learning models trained on vast libraries of drone sounds can distinguish them from ambient noise, even at significant distances. This approach is passive, meaning it doesn’t emit any signals, making it difficult for the drone to detect its own detection.
Radio Frequency Emissions: Digital Footprints
Even the most advanced stealth drone needs to communicate with its ground control, transmit sensor data, or utilize navigation signals like GPS. These electromagnetic interactions represent a significant vulnerability.
- Electronic Support Measures (ESM): Sophisticated ESM systems can passively intercept and analyze radio frequency (RF) emissions. By detecting command and control links, data downlinks, or active sensor emissions, these systems can identify a drone’s presence, type, and even its mission profile. Direction-finding techniques can pinpoint its location.
- GPS Spoofing and Jamming: Drones heavily rely on Global Positioning System (GPS) for navigation. GPS jamming floods the environment with noise, preventing the drone from receiving legitimate signals. More advanced GPS spoofing sends false signals, tricking the drone into believing it’s in a different location or on an incorrect trajectory, potentially leading it off course or even crashing. This vulnerability extends to other satellite navigation systems (GNSS) as well.
Visual and Thermal Signatures: Infrared and Optics
Despite efforts to reduce visual and thermal signatures, environmental factors and advanced sensors can still expose “ghost” drones.
- Advanced Optical Tracking: High-resolution cameras, especially those with powerful optical zoom and low-light capabilities, can detect drones that are visually camouflaged or operating at altitude. Multi-spectral imaging can differentiate drone materials from background clutter. AI-powered computer vision systems can identify drone shapes and movement patterns, even against complex backgrounds.
- Thermal Imaging and Hyperspectral Sensors: Even with IR signature management, engines generate heat. Advanced thermal cameras can pick up subtle temperature differences, especially after sustained flight. Hyperspectral imaging, which captures data across a wide range of the electromagnetic spectrum, can identify specific material compositions or residual heat plumes that might be invisible to conventional sensors. Atmospheric conditions, such as humidity or fog, can also interact with residual heat, making thermal signatures more prominent.
Cyber Vulnerabilities: The Digital Underbelly
Modern drones are complex computing platforms, and like any networked system, they are susceptible to cyberattacks. This represents a non-physical “weakness” that can be exploited remotely.
- Software Exploits and Hacking: Vulnerabilities in a drone’s operating system, flight control software, or communication protocols can be exploited. This could allow an adversary to take control of the drone, corrupt its data, disable its systems, or even force it to land.
- Supply Chain Attacks: Malicious code or hardware modifications could be introduced during the manufacturing process, creating backdoors or weaknesses that can be exploited later.
- Data Link Interception and Manipulation: Despite encryption, sophisticated cyber tools can potentially intercept, decrypt, or even inject false commands into a drone’s data link, turning the drone against its operator.
Countering the Ghost: Advanced Detection and Interception Strategies
Recognizing these vulnerabilities, militaries and security agencies are investing heavily in counter-drone technologies that leverage cutting-edge Tech & Innovation to detect, track, and neutralize stealth UAVs.
Multi-Sensor Fusion for Enhanced Tracking
No single sensor system is foolproof against a sophisticated stealth drone. The most effective counter-drone systems employ sensor fusion, combining data from multiple sources to create a comprehensive picture.
- Integrated Detection Grids: Combining radar, acoustic arrays, optical and thermal cameras, and RF interceptors into a single, networked system dramatically increases the probability of detection. AI algorithms process and correlate data from all sensors, filtering out false positives and accurately tracking targets. For example, a faint acoustic signature might be correlated with an intermittent radar blip and a fleeting thermal signature to confirm a drone’s presence.
- AI-Driven Anomaly Detection: Machine learning and deep learning models are crucial for sifting through vast amounts of sensor data. They can identify subtle anomalies or patterns indicative of a stealth drone that would be missed by human operators or traditional rule-based systems. This includes detecting unusual RF signatures, faint acoustic profiles, or minute changes in thermal backgrounds.
AI-Driven Anomaly Detection
AI plays a pivotal role not just in processing sensor data but in predicting drone behavior and adapting countermeasures.
- Predictive Analytics: AI can analyze drone flight patterns, operational parameters, and environmental data to predict potential trajectories, loitering areas, or target approaches. This allows for proactive deployment of countermeasures.
- Adaptive Countermeasures: Instead of static jamming, AI-driven electronic warfare systems can analyze a drone’s communication frequency and protocol in real-time and adaptively jam specific channels or spoof signals with greater precision, minimizing collateral interference.
- Swarm Defense: Future counter-drone systems might employ autonomous counter-drone swarms that, guided by AI, can effectively pursue, track, and neutralize stealthy individual or swarming threats.
Directed Energy and Electronic Warfare Countermeasures
Beyond detection, effective neutralization of stealth drones requires advanced intervention capabilities.
- High-Power Microwave (HPM) and Laser Systems: Directed energy weapons represent a promising countermeasure. HPM systems can disrupt or damage a drone’s electronics from a distance, while high-energy lasers can physically disable or destroy drones by burning through their airframes or critical components. These offer precision and a low cost per engagement compared to kinetic interceptors.
- Advanced Electronic Warfare (EW) Suites: Modern EW systems can do more than just jam. They can perform sophisticated cyber-attacks through the air, exploiting vulnerabilities in a drone’s operating system or communication protocols to disable it, force it to land, or even hijack it. This could involve manipulating sensor data, overwhelming processing units, or injecting malicious code.
The Future Landscape: Adapting to Evolving Stealth and Counter-Stealth
The race between stealth drone development and counter-drone technologies is an ongoing one, a continuous cycle of innovation and adaptation within the Tech & Innovation landscape. As drone technology advances, so too will the methods to detect and neutralize them.
Miniaturization vs. Detection Thresholds
One of the significant trends in drone technology is miniaturization. Smaller drones are inherently harder to detect visually, acoustically, and often by radar due to their reduced physical footprint. However, the same principles of physics still apply: they still need power, generate some heat, and communicate. The challenge for counter-drone tech will be to develop ever more sensitive and intelligent sensors capable of detecting these increasingly minute signatures across diverse environments. This will drive further advancements in quantum sensors, passive coherent location (PCL) radar, and neuromorphic computing for ultra-fast, low-power data processing.
Regulatory and Ethical Considerations
As drone technology becomes more sophisticated and stealth capabilities improve, the regulatory and ethical landscape becomes increasingly complex. The ability to conduct highly covert surveillance or kinetic operations raises profound questions about privacy, accountability, and international law. The development and deployment of counter-stealth technologies also carry significant implications, particularly concerning the use of directed energy weapons and autonomous interception systems. Future innovation in this field will not only be about technological prowess but also about establishing robust frameworks for responsible development and deployment.
In conclusion, while “ghost” drones embody the cutting edge of low-observable technology, they are far from invincible. Their very design principles create specific “weaknesses” that can be exploited through a combination of multi-spectral sensing, AI-driven analysis, cyber warfare, and directed energy countermeasures. The ongoing evolution of Tech & Innovation ensures that the tactical dance between stealth and detection will continue to define the future of aerial autonomy and remote sensing.
