The evolution of drone technology has ushered in an era of unprecedented innovation, transforming industries from logistics and agriculture to surveillance and entertainment. As unmanned aerial vehicles (UAVs) become more sophisticated, integrating advanced features like autonomous flight, AI-powered object recognition, and high-resolution remote sensing capabilities, the digital infrastructure supporting these operations grows in complexity. This expansion inevitably brings forth critical cybersecurity challenges. In this intricate landscape, understanding endpoint security solutions like FortiClient becomes paramount, not just for general IT environments, but specifically for safeguarding the ground control stations, data processing units, and communication links vital to modern drone operations. FortiClient, a comprehensive endpoint protection platform, represents a key piece of “Tech & Innovation” in securing the digital perimeter that underpins advanced aerial technologies.

FortiClient at its Core: A Comprehensive Endpoint Protection Platform
FortiClient is much more than a simple antivirus program; it is an integrated cybersecurity solution developed by Fortinet, a leader in network security. Designed to protect endpoints—any device connected to a network, from laptops and desktops to mobile devices and servers—FortiClient delivers a robust suite of security features. Its primary objective is to provide unified threat protection, secure remote access, and simplified management for organizations. In the context of drone operations, where sensitive data, critical control systems, and potentially vulnerable remote connections are commonplace, FortiClient’s capabilities become indispensable, offering an innovative layer of defense for the entire ecosystem.
Endpoint Security Fabric Integration
A cornerstone of FortiClient’s strength is its integration into the Fortinet Security Fabric. This architecture allows various Fortinet products to communicate and share threat intelligence seamlessly. For drone operators, this means that security policies applied to ground control stations can be consistent with network security at the operations center, creating a cohesive and adaptive defense system. This fabric integration allows for centralized visibility and control, simplifying the management of security across diverse devices and locations, which is critical when dealing with dispersed drone deployment teams or remote sensing operations.
Key Security Modules and Features
FortiClient bundles several powerful security modules into a single, lightweight client, ensuring comprehensive protection without significant performance overhead. These modules include:
- Next-Generation Antivirus (NGAV): Goes beyond signature-based detection to employ behavioral analysis, machine learning, and artificial intelligence to identify and neutralize both known and unknown threats, including zero-day exploits. For systems processing drone imagery or flight telemetry, this protection is crucial against malware that could corrupt data or compromise operational integrity.
- Web Filtering: Protects users from accessing malicious websites, phishing scams, and inappropriate content by blocking access based on categories or specific URLs. This is vital for maintaining the integrity of mission-critical systems and preventing accidental exposure to threats during research or data upload/download activities.
- Vulnerability Management: Scans endpoints for software vulnerabilities and missing patches, providing recommendations and facilitating remediation. In the rapidly evolving tech landscape of drone hardware and software, keeping all components patched and secure against known exploits is a continuous, critical task.
- Application Control: Allows administrators to manage and restrict applications that can run on an endpoint, reducing the attack surface by preventing unauthorized software from executing. This ensures that only approved drone-related applications and utilities are active on ground station computers, minimizing risks from rogue processes.
- Sandbox Integration: Leverages cloud-based or on-premise sandboxing for suspicious files, isolating them in a safe environment to observe their behavior before they can infect the endpoint. This advanced threat protection is particularly valuable when dealing with new or custom software components often found in specialized drone applications.
Secure Connectivity: VPN and Zero Trust Network Access (ZTNA) for Drone Operations
One of FortiClient’s most critical functions, particularly relevant for advanced drone operations, is its ability to establish secure, encrypted connections. As drone missions extend geographically, and teams operate remotely, the need for secure communication channels becomes non-negotiable.
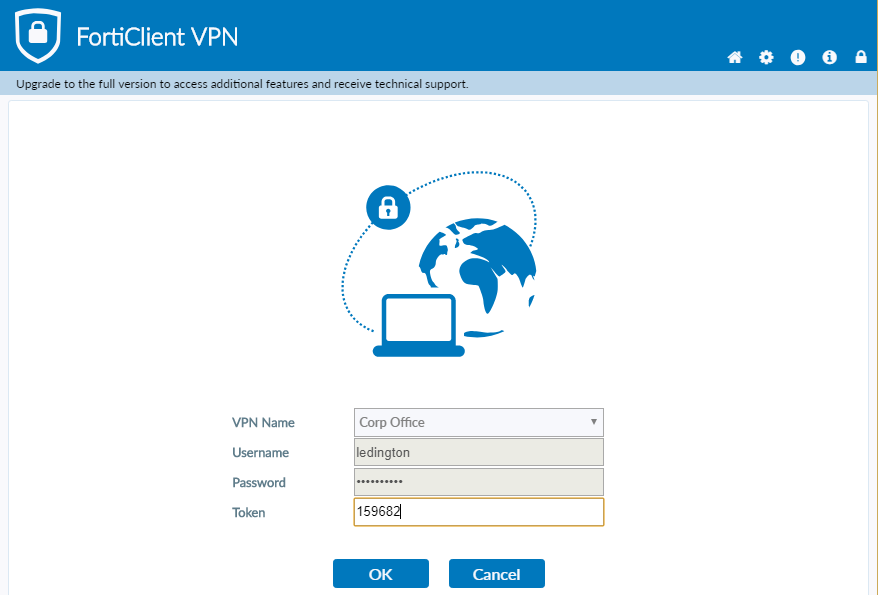
Virtual Private Network (VPN) for Remote Pilots and Data Transfer
FortiClient’s integrated VPN client enables remote users, such as drone pilots operating from home or field technicians transmitting data from a remote location, to securely connect to the corporate network. This establishes an encrypted tunnel, protecting sensitive operational data—like flight plans, sensor readings, and captured imagery—from interception or tampering during transit over public internet connections. For drone operations handling confidential information, such as critical infrastructure inspections or sensitive mapping projects, the integrity of data in transit is paramount. The VPN functionality ensures that commands sent to drones, and telemetry received from them, remain private and secure.
Zero Trust Network Access (ZTNA) for Enhanced Security
Beyond traditional VPNs, FortiClient also facilitates Zero Trust Network Access (ZTNA). ZTNA operates on the principle of “never trust, always verify,” meaning no user or device is inherently trusted, regardless of their location inside or outside the network perimeter. For drone-related “Tech & Innovation,” ZTNA represents a significant leap forward in security:
- Granular Access Control: ZTNA allows administrators to define highly specific access policies based on user identity, device posture (e.g., patched, no malware), and context. This means a drone pilot might only be granted access to the flight planning application and specific data repositories, not the entire corporate network.
- Reduced Attack Surface: By granting access only to the specific applications or resources required, ZTNA significantly reduces the network’s attack surface, limiting lateral movement for potential attackers who might gain a foothold on one endpoint.
- Dynamic Policy Enforcement: Policies can adapt in real-time based on changes in device posture or user behavior, enhancing security against evolving threats. This is critical in dynamic field environments where device security status might fluctuate.
Implementing ZTNA via FortiClient means that every connection from a ground control station, a data analysis laptop, or a remote pilot’s device is verified and authenticated before access is granted to drone management systems or sensitive data servers. This proactive approach significantly mitigates risks associated with compromised credentials or devices, bolstering the overall security posture of innovative drone ecosystems.
FortiClient and the Future of Secure Drone Ecosystems
The integration of drones into various sectors signals a future where these aerial platforms are not merely tools but critical components of infrastructure and data acquisition strategies. With this advancement comes an increased responsibility to ensure the security and integrity of all associated digital assets. FortiClient, as a robust endpoint protection solution, is a vital “Tech & Innovation” enabler in this context.
Protecting Ground Control Stations and Field Devices
Ground control stations (GCS) and field-deployed devices (laptops, tablets) are the nerve centers of drone operations. They house flight planning software, mission-critical data, and provide the interface for commanding UAVs. These endpoints are often exposed to varying environmental conditions and network access points, making them prime targets for cyber threats. FortiClient ensures these devices are protected against malware, ransomware, and unauthorized access, maintaining the operational integrity and reliability of drone missions. By safeguarding these points of control, FortiClient helps prevent scenarios where a compromised GCS could lead to mission failure, data loss, or even unauthorized drone takeovers.
Securing Data Flow and Remote Sensing Outputs
Modern drones generate vast amounts of data—high-resolution imagery, LiDAR scans, thermal maps, and more. This data is often sensitive, containing proprietary information, critical infrastructure details, or personal data. The journey of this data, from capture on the drone’s sensors to storage, processing, and analysis, involves multiple digital touchpoints. FortiClient, through its endpoint protection and secure connectivity features, helps secure the endpoints responsible for handling this data, from initial transfer to local processing. Its ability to secure remote access points ensures that sensitive remote sensing outputs can be accessed and manipulated securely by authorized personnel, regardless of their physical location. This is particularly relevant for applications like precision agriculture, environmental monitoring, or geological surveying, where data accuracy and confidentiality are paramount.

Compliance and Regulatory Adherence
As drones become more regulated, especially in sectors like defense, public safety, and critical infrastructure, adherence to cybersecurity standards and data protection regulations (e.g., GDPR, HIPAA, NIST) is becoming mandatory. FortiClient’s comprehensive logging capabilities, centralized management, and strong security posture assist organizations in meeting these stringent compliance requirements. By providing a verifiable layer of security at the endpoint, it helps create an auditable trail of security events and ensures that devices handling sensitive drone data operate within established security frameworks.
In conclusion, “what is FortiClient” in the landscape of drone technology is best understood as a critical piece of the cybersecurity puzzle. It is an innovative solution that extends advanced protection to the digital boundaries of drone operations, securing everything from ground control stations and remote access points to sensitive data flows. As drone technology continues its rapid advancement, the sophisticated, integrated endpoint security offered by FortiClient will remain indispensable for ensuring reliable, secure, and compliant aerial operations in an increasingly connected and vulnerable world.
