In an era defined by rapid technological advancement and interconnected systems, securing our digital infrastructure has never been more critical. From autonomous robotics and AI-driven platforms to sophisticated remote sensing operations, the underlying network architecture plays a pivotal role in both functionality and security. One foundational concept in network design that remains highly relevant for professional tech deployments is the Demilitarized Zone, or DMZ. Often misunderstood or incorrectly implemented, a DMZ offers a strategic approach to isolating and protecting vulnerable services, striking a crucial balance between accessibility and security.

This exploration delves into the intricacies of a DMZ, explaining its purpose, functionality, and the strategic advantages it offers, particularly in the context of complex, innovation-driven environments where secure data transfer, remote access, and service exposure are paramount.
Unpacking the Demilitarized Zone: A Core Concept in Network Security
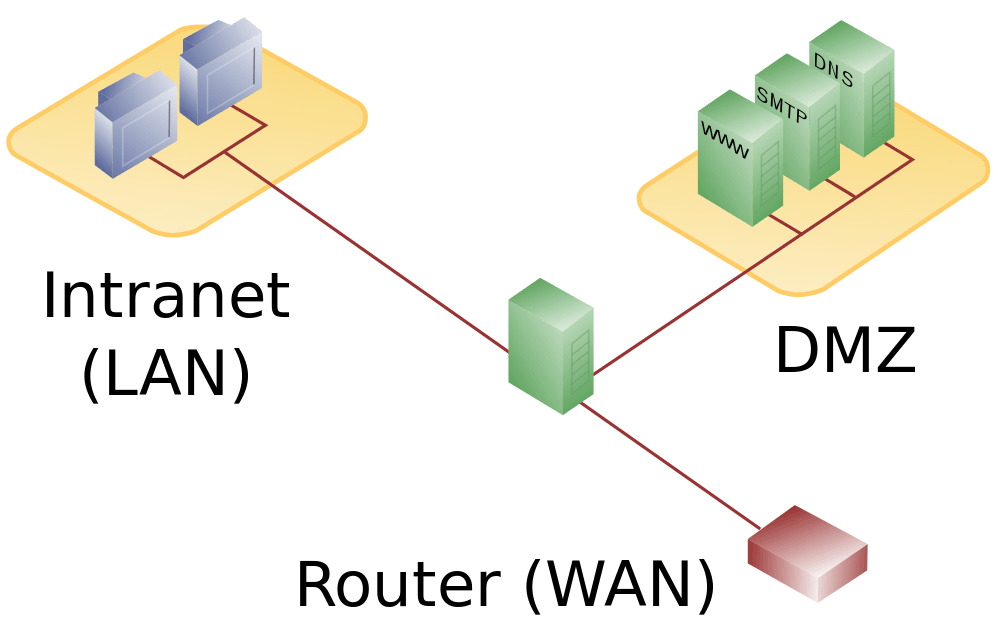
At its heart, a DMZ is a buffer network that sits between an organization’s secure internal network (LAN) and the untrusted external network (Internet). Its name is derived from the military concept of a “demilitarized zone”—an area where military forces are prohibited, serving as a neutral buffer between opposing factions. In networking, this translates to a segment designed to host services that need to be accessible from the internet while simultaneously protecting the private internal network from potential threats originating from the exposed services.
The Fundamental Problem: Balancing Access and Protection
Every advanced technological system, especially those involving remote operations, data aggregation, or cloud-based management, faces a fundamental paradox: certain services must be accessible from the internet for functionality, yet exposing them directly to the internet dramatically increases the risk of cyberattacks. Think of a web server hosting an application for managing remote sensing data, an email server, or a specialized server for an autonomous fleet’s command-and-control system. Without a DMZ, placing such services directly on the internal network makes the entire network vulnerable if the exposed service is compromised. Conversely, keeping them entirely isolated makes them unusable for their intended purpose. The DMZ provides an elegant solution to this dilemma.
How a DMZ Functions: The Buffer Zone Analogy
Imagine your network as a fortified castle. Your internal LAN is the inner keep, housing your most valuable assets and confidential data. The internet is the wild, untamed wilderness outside the castle walls, full of potential invaders. Your router, with its firewall, acts as the main gatekeeper.
A DMZ is like a moated courtyard or an outer defensive wall around the main keep. Any services that need to interact with the outside world (e.g., a public-facing web server for a drone mapping service, an FTP server for large data uploads, or a remote access portal for ground station operators) are placed within this courtyard. If an attacker breaches the outer wall (the DMZ), they gain access only to the courtyard and its contained services, not directly to the inner keep. The main firewall then prevents unauthorized access from the DMZ into the internal LAN. This multi-layered defense significantly reduces the attack surface on your most critical internal resources.
Key Components: Firewall Rules and Network Segmentation
The successful implementation of a DMZ relies heavily on precise firewall rules and effective network segmentation. Typically, a router or a pair of firewalls creates the DMZ:
- Outer Firewall (or Internet-facing interface of a router): This firewall sits between the internet and the DMZ. It allows specific, pre-defined traffic (e.g., HTTP/S, FTP, SSH) to reach the services within the DMZ. All other unsolicited traffic is blocked.
- Inner Firewall (or LAN-facing interface of a router): This crucial firewall sits between the DMZ and the internal LAN. It is configured to explicitly prevent traffic from the DMZ from entering the LAN, except for very specific, tightly controlled exceptions (e.g., a DMZ-based web server needing to query a database on the internal LAN). This strict separation ensures that even if a server in the DMZ is compromised, the attacker cannot easily pivot into the internal network.
Network segmentation is the act of dividing a computer network into multiple smaller network segments or subnets. The DMZ is a prime example of this, creating a logical or physical separation that enhances security, performance, and manageability.
Why DMZ Matters in Advanced Tech Deployments
In the realm of modern tech and innovation, where systems are increasingly distributed, remotely managed, and reliant on external connectivity, the strategic application of a DMZ offers tangible benefits for security and operational continuity.
Securing Internet-Facing Services: Beyond Simple Port Forwarding
Many small operations might resort to simple port forwarding to expose a service to the internet. While easy to configure, port forwarding directly maps an external port to an internal device, essentially poking a hole directly into your private network. If that device is compromised, an attacker has a direct foothold inside your LAN.
For critical applications like remote ground control stations for drone fleets, servers processing sensitive mapping data, or platforms managing AI models for real-time analysis, such a direct exposure is an unacceptable risk. A DMZ provides a controlled environment, isolating these services so that even if they are exploited, the attack is contained, preventing lateral movement into the core network infrastructure where valuable intellectual property or operational control systems reside.
Isolation and Containment: Limiting Breach Impact
The principle of least privilege extends beyond user access to network architecture. By isolating internet-facing services within a DMZ, you limit the blast radius of a potential security breach. If an external attacker successfully compromises a public-facing server in the DMZ (e.g., by exploiting a software vulnerability in a drone data portal), their access is largely confined to that segment. They would then need to breach a second, more robust firewall to gain entry to the internal network, significantly increasing the difficulty and detection chances of an attack. This containment strategy is vital for maintaining operational integrity and protecting proprietary algorithms, flight plans, or sensitive data sets.
Practical Applications for Remote Access and Data Management
Consider a company developing autonomous systems or managing a fleet of drones for industrial inspection. They might require:
- Remote Access for Operators: Field operators or engineers might need secure VPN or SSH access to a central ground station server to monitor missions, update parameters, or troubleshoot issues. Placing the VPN/SSH gateway in the DMZ allows secure external access without exposing the entire internal network.
- Data Ingestion and Processing Servers: Drones generate vast amounts of data (imagery, LiDAR, telemetry). This data often needs to be uploaded to dedicated servers for processing, analysis, and storage. A server in the DMZ can act as an initial staging point for incoming data, scanning it for malware or anomalies before it’s moved to more secure internal storage or processing clusters.
- Public APIs or Web Services: If the company offers public APIs for third-party integration or a web portal for clients to access processed data, these services should ideally reside in a DMZ to handle external requests without risking the internal network.
Implementing a DMZ: Configuration and Best Practices
Implementing a DMZ effectively requires careful planning and a thorough understanding of network security principles. While the concept is straightforward, misconfigurations can negate its benefits or even introduce new vulnerabilities.
Router-Based DMZ vs. Dedicated DMZ Architectures
Most consumer-grade and many prosumer routers offer a “DMZ Host” feature. This is the simplest form of a DMZ, where you designate a single internal IP address as the DMZ host. The router then forwards all unsolicited incoming traffic (that isn’t port-forwarded elsewhere) to this specific host. While easy to set up, this is often a poor security choice as it effectively places the DMZ host outside the firewall’s protection for inbound traffic, making it highly vulnerable. It lacks the critical inner firewall protection and the ability to host multiple services securely.
For serious tech deployments, a true DMZ architecture involves either:
- Three-Legged DMZ: Using a single firewall with three network interfaces (one for LAN, one for WAN/Internet, one for DMZ).
- Back-to-Back DMZ (or Dual Firewall DMZ): Using two firewalls. The first firewall connects the WAN to the DMZ, and the second firewall connects the DMZ to the LAN. This offers the highest level of security and redundancy.
These more robust architectures allow for granular control over traffic flow between all three zones (WAN, DMZ, LAN) using sophisticated firewall rules.
Steps to Configure a DMZ on a Standard Router (High-Level, conceptual)
For a basic “DMZ Host” on a standard router (caution advised for production environments):
- Assign a Static IP: Ensure the device you want to place in the DMZ has a static IP address on your internal network.
- Access Router Settings: Log into your router’s administration interface.
- Locate DMZ Settings: Find the DMZ section, usually under advanced settings, WAN setup, or security.
- Enable DMZ and Specify IP: Enable the DMZ feature and enter the static IP address of your chosen DMZ host.
- Review Firewall Rules: Understand that this configuration often bypasses the firewall for inbound traffic to the DMZ host.
For a true multi-zone DMZ with a dedicated firewall, the process involves configuring VLANs, interface assignments, and detailed ingress/egress firewall rules for each zone.
Essential Security Considerations and Limitations
- No Panacea: A DMZ is a security enhancement, not a complete solution. Services within the DMZ still need to be robustly secured (patched, strong passwords, least privilege access).
- Proper Rule Sets: The effectiveness of a DMZ hinges entirely on correctly configured firewall rules. Misconfigured rules, especially between the DMZ and LAN, can undermine its purpose.
- Data Flow: Carefully consider what data needs to flow from the DMZ to the LAN. Minimize these connections and secure them with encryption.
- Monitoring: Implement robust logging and monitoring for all traffic to and from the DMZ to detect and respond to potential intrusions promptly.
The DMZ in the Context of Evolving Tech & Innovation
As “Tech & Innovation” pushes boundaries, the underlying network infrastructure must evolve to meet new demands for connectivity, security, and scalability. The DMZ, while an older concept, remains highly relevant in shaping robust solutions.
Addressing IoT Security Challenges (Ground Control Stations, Sensors)
The proliferation of IoT devices, including autonomous drone ground control units, environmental sensors for remote monitoring, and edge computing devices, presents significant security challenges. Many IoT devices have limited security features and can be vulnerable. Placing critical, internet-exposed IoT gateways or aggregators within a DMZ can isolate them from the core network. This strategy protects the internal network if an IoT device or its gateway is compromised, allowing for secure aggregation and forwarding of data while minimizing risk.
Facilitating Secure Remote Operations and Data Pipelines
Innovation often thrives on collaboration and distributed teams. Remote operations, such as piloting drones beyond visual line of sight (BVLOS) or managing remote sensing campaigns, rely on stable and secure network connections. A DMZ can house servers that facilitate these connections, like dedicated VPN endpoints, telemetry relays, or secure file transfer protocols (SFTP) for massive data pipelines, ensuring that the critical internal operational network remains insulated from the public internet. This enables global teams to securely interact with the system without compromising the entire infrastructure.
Future Trends: Zero Trust and Micro-segmentation Beyond DMZ
While the DMZ offers a strong perimeter defense, the future of network security is moving towards more granular approaches like “Zero Trust” architecture and micro-segmentation. Zero Trust dictates “never trust, always verify,” meaning every connection, whether internal or external, is authenticated and authorized. Micro-segmentation takes this a step further by creating even smaller, isolated network segments, often down to individual workloads or applications, each with its own firewall rules.
These advanced concepts don’t render the DMZ obsolete but rather complement it. A DMZ can be seen as an initial, broad segment within a larger Zero Trust strategy. As tech ecosystems grow more complex, with numerous autonomous agents, cloud services, and edge devices, a multi-layered approach that integrates DMZ principles with newer paradigms will be essential for maintaining a strong security posture.
Weighing the Advantages and Risks
The decision to implement a DMZ should be part of a comprehensive network security strategy, carefully weighing its benefits against potential risks and complexities.
Benefits: Enhanced Security, Dedicated Service Exposure, Control
- Enhanced Security: Provides a vital layer of defense, isolating internet-facing services from internal networks.
- Dedicated Service Exposure: Allows specific services to be publicly accessible without exposing the entire network.
- Improved Control: Granular control over traffic flow between the internet, DMZ, and internal network.
- Containment: Limits the impact of a breach to the DMZ segment, protecting critical internal assets.
- Compliance: Helps meet regulatory and compliance requirements for data protection.
Risks: Misconfiguration Vulnerabilities, Single Point of Failure
- Misconfiguration: Improperly configured firewall rules are the leading cause of DMZ security failures, potentially opening direct paths to the internal network.
- Single Point of Failure (for simple DMZ Host): A basic DMZ host setup can create a single, highly vulnerable target.
- Complexity: Designing and maintaining a robust DMZ, especially with multiple firewalls, requires significant expertise.
- Performance Overhead: Additional firewalls and network segmentation can introduce slight latency, though typically negligible for most applications.

When to Use (and When to Avoid) a DMZ
A DMZ is highly recommended for:
- Any organization exposing public-facing services (web servers, mail servers, FTP, VPN gateways, remote ground station access points, data ingestion servers) in a professional context.
- Companies dealing with sensitive data or critical operational systems (e.g., in drone operations, autonomous systems, AI data processing).
- Environments requiring strong regulatory compliance.
A DMZ might be overkill or less effective for:
- Simple home networks with minimal or no exposed services.
- Situations where the “DMZ Host” feature on a consumer router is the only option, without proper internal firewalling.
In conclusion, the DMZ remains a cornerstone of network security in modern tech ecosystems. For innovators pushing the boundaries of autonomous flight, AI, remote sensing, and interconnected IoT, understanding and correctly implementing a DMZ is not merely a technical detail but a strategic imperative. It provides the secure foundation upon which complex, internet-facing operations can confidently operate, protecting invaluable assets while facilitating essential external connectivity. As technology evolves, so too will the methods of securing it, but the fundamental principles embodied by the DMZ will undoubtedly continue to play a crucial role.
