The digital landscape is a complex ecosystem, teeming with threats that can compromise our systems and data. Among the most persistent and well-known are computer viruses and worms. While often used interchangeably in casual conversation, these two types of malware are distinct in their functionality, propagation methods, and impact. Understanding these differences is crucial for effective cybersecurity and for appreciating the nuances of how malicious code operates within our connected world.
The Nature of Malware: A Fundamental Distinction
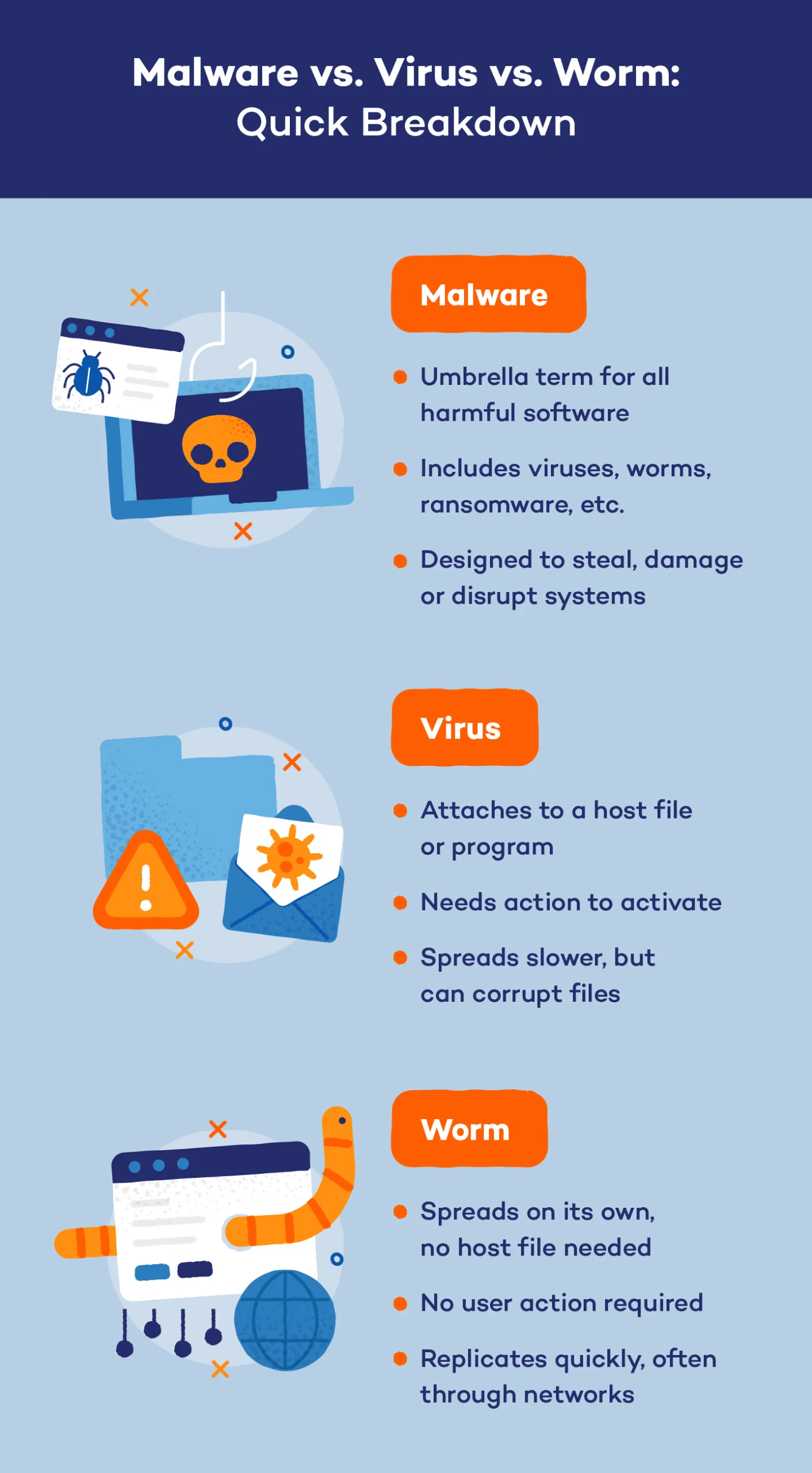
At their core, both viruses and worms are types of malicious software designed to infiltrate computer systems without the user’s consent. Their ultimate goals can vary, from disrupting operations and stealing sensitive information to holding systems hostage for ransom. However, the fundamental difference lies in their ability to replicate and spread.
The Virus: The Parasitic Invader
A computer virus, much like its biological counterpart, requires a host to survive and propagate. It is a piece of code that attaches itself to an existing, legitimate program or file. When the host program is executed, the virus code is also executed, allowing it to perform its malicious actions. More importantly, it can then replicate by inserting its own code into other programs or files on the infected system.
The key characteristic of a virus is its dependence on human action to spread. A user must typically open an infected email attachment, download and run an infected file, or execute an infected program for the virus to spread to a new host. Without this active intervention, a virus remains dormant, attached to its original host.
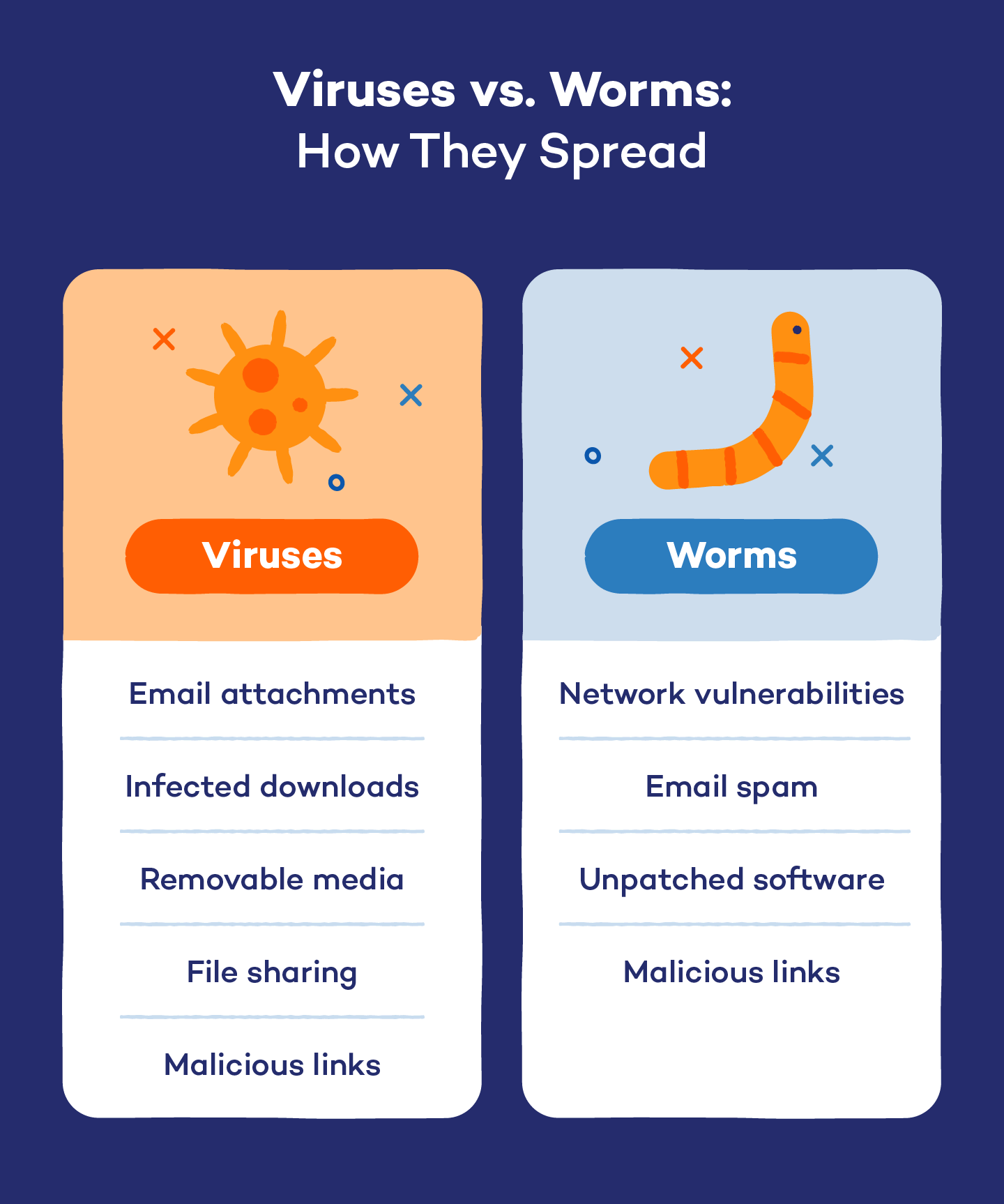
How Viruses Infect
The infection process typically involves several stages:
- Attachment: The virus code embeds itself within a legitimate file or program, such as an executable (.exe), document (.doc), or script (.vbs).
- Execution: When the infected file or program is run by the user, the virus’s code is activated.
- Replication: The virus then makes copies of itself and inserts them into other accessible files or programs on the system.
- Payload Delivery: Once replicated, the virus may activate its “payload” – the intended malicious action. This could range from displaying annoying pop-ups to deleting files, corrupting data, or providing unauthorized access to the system.
Viruses can be categorized further based on their behavior and infection methods, such as:
- Boot Sector Viruses: These infect the boot sector of a hard drive or removable media, executing when the system starts up.
- File Infector Viruses: These attach themselves to executable files.
- Macro Viruses: These are written in macro languages embedded within software applications like Microsoft Word or Excel and are triggered when the document is opened and macros are enabled.
- Polymorphic Viruses: These constantly change their code to evade detection by antivirus software.
The Worm: The Autonomous Spreader
In contrast to viruses, computer worms are designed to be self-replicating and self-propagating. They do not need to attach themselves to an existing program or file to spread. Instead, worms exploit vulnerabilities in operating systems or network protocols to travel from one computer to another across networks, often without any user intervention.
The primary characteristic of a worm is its independence. Once it is present on a system, it can actively seek out other vulnerable systems and spread itself. This autonomous nature makes worms particularly dangerous and capable of causing widespread damage very rapidly.
How Worms Spread
Worms leverage various methods to propagate:
- Network Vulnerabilities: Worms often scan networks for systems with unpatched security holes or weak configurations. They then exploit these vulnerabilities to gain access and install themselves on the new system.
- Email Attachments (with a twist): While viruses can spread via email attachments, worms often use email differently. They might send copies of themselves to all the contacts in an infected user’s address book, or even disguise themselves as legitimate emails to trick users into opening them.
- Instant Messaging and File Sharing: Worms can also spread through instant messaging programs or peer-to-peer file-sharing networks.
- Removable Media: Similar to viruses, worms can also reside on and spread through USB drives and other portable storage devices.
Once a worm infects a system, it will typically replicate itself and then actively search for new targets to infect. This can lead to a rapid exponential growth of the infection across a network.
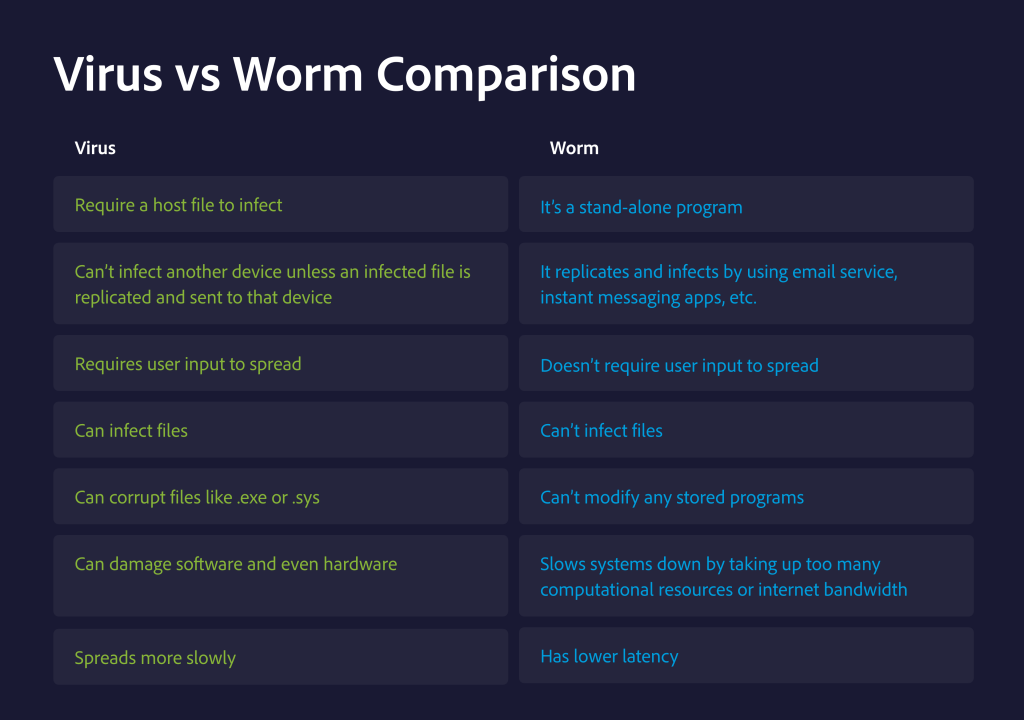
Key Differences in a Nutshell
To summarize the core distinctions:
| Feature | Virus | Worm |
|---|---|---|
| Replication | Attaches to a host file/program; requires host execution to replicate. | Self-replicating; creates independent copies of itself. |
| Propagation | Requires human intervention (e.g., opening an infected file). | Spreads autonomously across networks by exploiting vulnerabilities. |
| Host Dependence | Highly dependent on a host program or file. | Independent; does not require a host program to spread. |
| Impact | Can corrupt files, delete data, display messages, or steal info. | Consumes network bandwidth, can overload servers, and deliver payloads. |
| Speed of Spread | Generally slower, as it relies on user actions. | Can spread extremely rapidly, potentially globally, within hours. |
The Impact and Consequences
The consequences of a virus or worm infection can be severe, affecting individuals, businesses, and even critical infrastructure.
For Individuals
Personal computers can become unusable, data can be lost or stolen, and online accounts can be compromised. Phishing attacks, identity theft, and financial fraud are common outcomes of malware infections. The emotional toll of dealing with such breaches can also be significant.
For Businesses
The impact on businesses can be catastrophic. Data breaches can lead to massive financial losses due to recovery costs, legal liabilities, and reputational damage. Operational downtime can halt production, disrupt services, and lead to significant revenue loss. Sensitive intellectual property or customer data falling into the wrong hands can have long-term detrimental effects.
For Critical Infrastructure
Infections targeting government agencies, utilities, or healthcare systems can have far-reaching and potentially life-threatening consequences. Disruptions to power grids, water treatment facilities, or emergency services can have devastating societal impacts.
Protection and Prevention Strategies
Understanding the differences between viruses and worms informs the most effective strategies for protection and prevention.
Antivirus and Anti-Malware Software
This is the first line of defense. Antivirus software is designed to detect, prevent, and remove known viruses, worms, and other malware. It works by scanning files and programs for signatures of malicious code. Keeping this software up-to-date with the latest virus definitions is paramount.
Patching and Updates
Both viruses and worms often exploit known vulnerabilities in software and operating systems. Regularly updating your operating system and all installed applications with the latest security patches is crucial. This closes the loopholes that malware uses to gain entry.
User Education and Awareness
Many infections, especially those involving viruses, still rely on social engineering tactics to trick users into taking harmful actions. Educating users about the dangers of opening suspicious email attachments, clicking on unsolicited links, or downloading software from untrusted sources is a critical component of a robust security strategy.
Network Security Measures
For preventing worm propagation, strong network security is vital. This includes:
- Firewalls: Act as a barrier between internal networks and the external internet, blocking unauthorized access.
- Intrusion Detection and Prevention Systems (IDPS): Monitor network traffic for malicious activity and can block or alert on suspicious patterns.
- Network Segmentation: Dividing a network into smaller, isolated segments can limit the spread of malware if one segment is compromised.
Strong Passwords and Authentication
While not directly preventing the initial infection, using strong, unique passwords for all accounts and enabling multi-factor authentication can prevent malware from easily spreading to other accounts or systems if credentials are compromised.
The Evolving Threat Landscape
The lines between different types of malware can sometimes blur. For instance, some modern malware might exhibit characteristics of both viruses and worms, or employ advanced techniques to evade detection and spread. For example, a piece of malware might initially spread like a worm by exploiting a network vulnerability, but then attach itself to files on the infected system like a virus.
Moreover, the motivations behind malware attacks are constantly evolving, ranging from state-sponsored cyber warfare and organized cybercrime to hacktivism and individual malicious intent. This dynamic landscape necessitates continuous vigilance, adaptation of security measures, and a deep understanding of the threats we face. By understanding the fundamental differences between entities like viruses and worms, we build a stronger foundation for navigating the complexities of cybersecurity and protecting our digital lives.
