Data leakage prevention (DLP) stands as a critical cybersecurity discipline in an era defined by rapid technological advancement and an explosion of digital data. At its core, DLP refers to a set of strategies, technologies, and processes designed to ensure that sensitive data does not leave an organization’s control without authorization. In the dynamic landscape of modern tech and innovation, where proprietary algorithms, design specifications, customer data, and strategic insights are the lifeblood of progress, protecting this information from inadvertent or malicious disclosure is paramount. Data leakage can occur through various channels, including email, cloud storage, instant messaging, removable media, network shares, and even through the use of web applications. The consequences of such leaks range from significant financial losses and reputational damage to severe legal penalties and a loss of competitive advantage, making robust DLP an indispensable component of any forward-thinking enterprise’s security posture.
Understanding the Imperative: The Threat of Data Leakage in Modern Tech
The digital transformation sweeping across industries has amplified both the volume and sensitivity of data managed by organizations. From the vast datasets informing AI models and machine learning algorithms to the intricate telemetry streams guiding autonomous systems and the high-resolution imagery processed for advanced mapping and remote sensing, sensitive information is everywhere. This proliferation of data, coupled with a highly mobile and interconnected workforce, creates an expansive attack surface. Data leakage prevention addresses the inherent risks associated with data in motion and data at rest, aiming to prevent unauthorized access, use, or transfer.
In the context of cutting-edge technologies, the threat is particularly acute. Intellectual property related to new inventions, groundbreaking software code, or unique operational methodologies constitutes invaluable assets. A leak of such information could not only compromise a company’s market position but also fuel industrial espionage and undermine years of research and development. Furthermore, with increasingly stringent regulatory frameworks like GDPR, CCPA, and HIPAA, failing to prevent data leakage can result in astronomical fines and a significant erosion of trust from customers and partners. DLP is not merely a reactive measure but a proactive strategic investment in securing the future of innovation. It ensures the integrity and confidentiality of the data that drives progress, from the initial stages of conceptualization to the final deployment of advanced technological solutions.
The Pillars of Data Leakage Prevention (DLP): A Multi-Faceted Approach
Effective DLP is built upon several foundational components that work in concert to identify, monitor, and protect sensitive data across an organization’s entire digital ecosystem. This comprehensive strategy ensures that information assets are safeguarded regardless of where they reside or how they are accessed.
Content Discovery and Classification
The first step in any robust DLP strategy is understanding what data an organization possesses, where it is stored, and how sensitive it is. Content discovery involves scanning data repositories—including endpoints, servers, databases, cloud storage, and network shares—to locate sensitive information. Once discovered, this data must be accurately classified. Classification tags data based on its sensitivity (e.g., confidential, internal, public), type (e.g., personal identifiable information (PII), intellectual property, financial data), and regulatory requirements. This crucial step enables DLP systems to apply appropriate protection policies, ensuring that highly sensitive data receives the strictest controls while less critical information can be handled with more flexibility. Advanced classification often leverages machine learning to identify patterns, context, and semantic meaning, moving beyond simple keyword matching to accurately categorize complex data types, such as source code snippets or unique design schematics.
Monitoring and Analysis
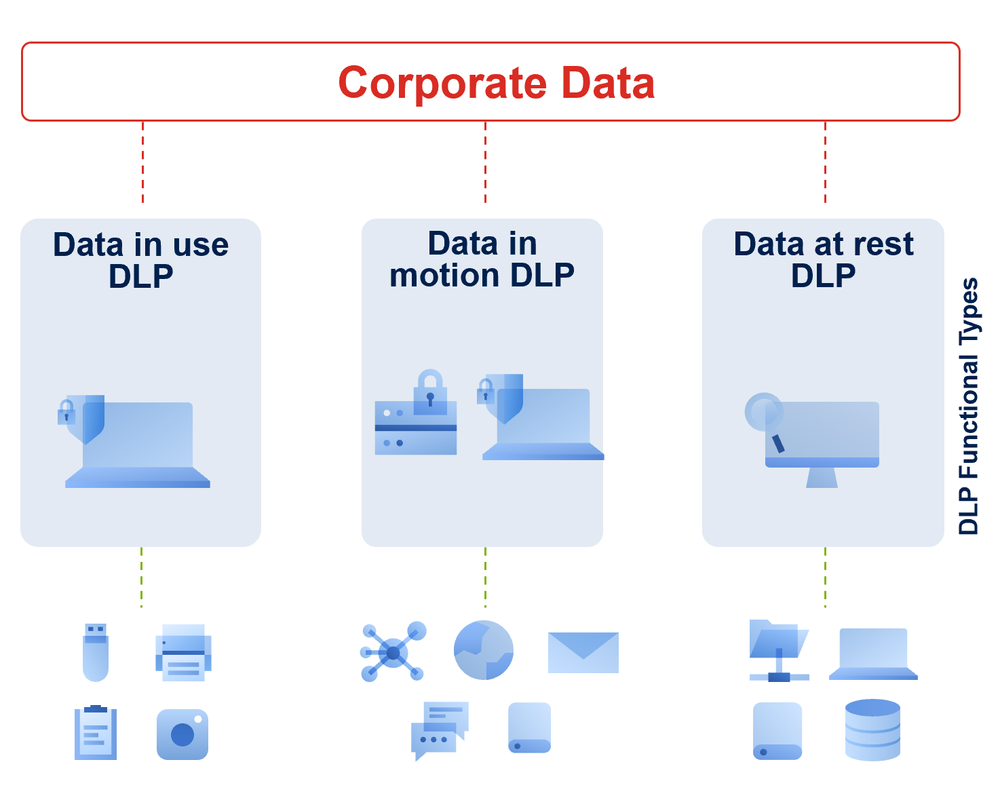
Once data is classified, DLP systems continuously monitor its movement and usage. This monitoring extends across various channels:
- Network DLP: Monitors data in transit over the network, including emails, web traffic, FTP transfers, and cloud sync operations. It can inspect content for sensitive information attempting to leave the network.
- Endpoint DLP: Monitors and controls data usage on employee workstations, laptops, and mobile devices. This includes preventing unauthorized copying to USB drives, printing, screen captures, or uploads to unapproved cloud services.
- Storage DLP: Scans data at rest in file shares, databases, and cloud storage to ensure sensitive information is not stored insecurely or without proper authorization.
- Cloud DLP: Specifically designed for cloud environments, it monitors data in SaaS applications, IaaS platforms, and PaaS services, ensuring compliance with data security policies as data flows into, within, and out of cloud infrastructures.
Monitoring also involves analyzing user behavior to detect anomalies that might indicate an attempted data breach or accidental leakage, leveraging behavioral analytics and threat intelligence to identify suspicious activities in real-time.
Policy Enforcement
The ultimate goal of DLP is to enforce security policies designed to prevent data leakage. Based on the classification of data and the context of its attempted use or transfer, DLP systems can take various automated actions:
- Blocking: Preventing the data transfer entirely (e.g., blocking an email containing PII from being sent outside the organization).
- Quarantining: Holding suspect data for review by security personnel before allowing or denying its movement.
- Encryption: Automatically encrypting sensitive data before it leaves a secure environment, ensuring it remains protected even if intercepted.
- Alerting: Notifying security teams or administrators of policy violations, often with detailed logs and forensic information.
- User Prompting: Warning users about potential policy violations and requiring justification or confirmation before proceeding.
These policies are granular and can be tailored to specific data types, user groups, destinations, and channels, allowing organizations to create a nuanced and adaptable security framework that aligns with their operational needs and risk appetite.
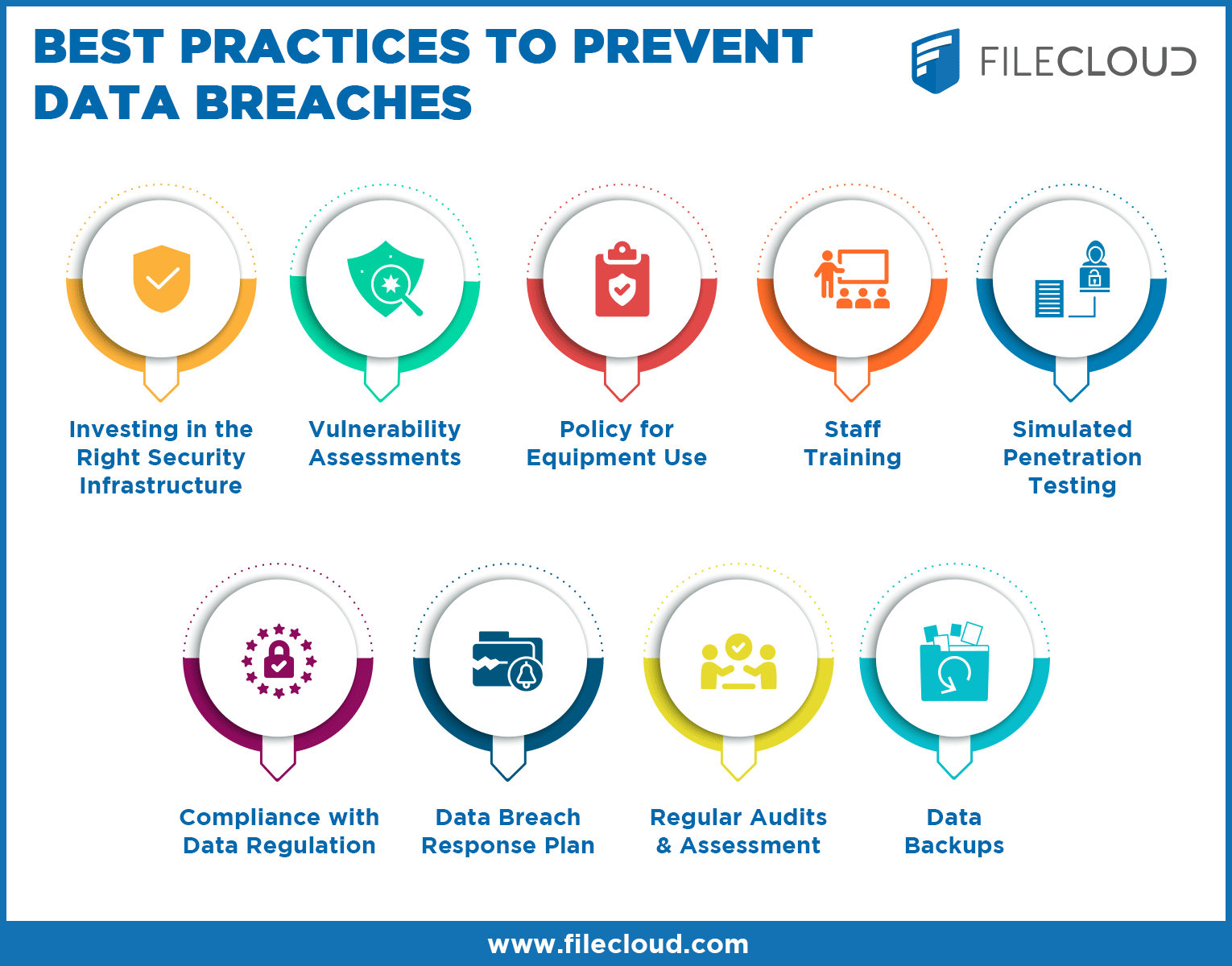
Implementing DLP: Strategies for Robust Data Security in Innovative Environments
Implementing an effective DLP program requires more than just deploying technology; it demands a strategic approach that integrates people, processes, and technology, particularly in environments focused on rapid innovation and emerging technologies.
Contextualizing DLP for Emerging Technologies
Innovative fields often involve unique data types and operational flows. For example, in AI development, safeguarding proprietary algorithms, training datasets, and model architectures is paramount. For autonomous systems, ensuring the integrity of operational code, sensor data, and decision-making logic is critical. Mapping and remote sensing initiatives involve vast amounts of geographic, environmental, and infrastructure data, which may be sensitive or proprietary. DLP solutions must be able to understand the context of these specialized data types, differentiating between legitimate data sharing for collaboration and unauthorized exfiltration. This often requires custom policies, integration with specialized development tools, and an understanding of the specific risks associated with each innovative application.
Addressing Insider Threats and Human Error
While external cyberattacks dominate headlines, a significant portion of data breaches originates from within the organization, often due to human error or malicious insider activity. Employees may inadvertently send sensitive information to the wrong recipient, store it on unsecured personal devices, or upload it to unauthorized cloud services. Malicious insiders, motivated by financial gain, revenge, or corporate espionage, can deliberately exfiltrate data. DLP plays a crucial role in mitigating these risks by monitoring internal data movements, enforcing access controls, and identifying anomalous user behavior. Coupled with comprehensive employee training on data handling best practices and a strong security-aware culture, DLP can significantly reduce the likelihood of both accidental and intentional data leakage.
Balancing Security and Innovation
A common challenge in implementing DLP in innovative environments is striking the right balance between robust security and enabling rapid development and collaboration. Overly restrictive DLP policies can impede productivity, stifle innovation, and frustrate users, leading to workarounds that ironically create new security gaps. The key is to design DLP policies that are intelligent and adaptive, allowing legitimate data flows for collaboration and development while strictly controlling unauthorized egress. This involves continuous fine-tuning, stakeholder engagement, and leveraging advanced DLP features like content-aware detection and user-behavior analytics to distinguish between legitimate and risky activities. The goal is to make security a seamless enabler of innovation, not a barrier.
DLP in Action: Protecting Sensitive Information in Advanced Systems
The practical applications of DLP are far-reaching, particularly in safeguarding the complex data ecosystems inherent in advanced technological ventures.
Safeguarding Intellectual Property
For organizations at the forefront of AI, robotics, and advanced software development, intellectual property (IP) is their most valuable asset. DLP systems are critical for preventing the leakage of source code, design specifications, proprietary algorithms, research data, and trade secrets. By scanning code repositories, development environments, and communication channels, DLP ensures that these critical assets do not fall into the wrong hands, preserving competitive advantage and investment in innovation.
Ensuring Regulatory Compliance
Compliance with a myriad of data protection regulations (e.g., GDPR, HIPAA, PCI DSS) is a non-negotiable requirement for many industries, especially those dealing with personal or financial data collected through advanced systems like remote sensing platforms or smart analytics. DLP solutions help organizations meet these obligations by preventing the unauthorized disclosure of regulated data, providing audit trails of data access and movement, and demonstrating a proactive commitment to data privacy. This is particularly vital when handling vast amounts of data that might contain PII or other sensitive information, ensuring that data is handled responsibly throughout its lifecycle.
Securing Data in AI and Autonomous Systems
The integrity of AI models and autonomous systems relies heavily on the security of their data pipelines. Training data, model parameters, and operational logs can be highly sensitive. DLP helps prevent the leakage of these critical components, protecting against model poisoning, intellectual property theft, and ensuring the continued reliable operation of AI-driven and autonomous technologies. By monitoring data flows within these complex systems, DLP safeguards against both internal vulnerabilities and external threats to data integrity.

The Evolving Landscape of Data Security and DLP’s Future Role
As technology continues to evolve, so too will the challenges and solutions in data leakage prevention. The rise of new data storage paradigms, the increasing sophistication of cyber threats, and the ever-expanding global regulatory landscape will demand continuous adaptation from DLP strategies. Future DLP solutions will likely leverage more advanced artificial intelligence and machine learning to predict potential leakage points, identify zero-day threats, and offer more dynamic, context-aware policy enforcement. Integration with other security tools, such as Security Information and Event Management (SIEM) and User and Entity Behavior Analytics (UEBA), will become more seamless, creating a unified and intelligent security fabric. Ultimately, as innovation accelerates, DLP will remain an indispensable tool, serving as the bedrock of data trust and security for organizations pushing the boundaries of what’s possible.
