While the term “CSR SSL certificate” might sound technical and perhaps even a little intimidating, understanding its fundamental purpose is crucial for anyone involved in secure online operations. In the realm of cybersecurity and digital trust, a CSR SSL certificate, or more accurately, a Certificate Signing Request (CSR) used in conjunction with obtaining an SSL certificate, forms the bedrock of secure communication over the internet. It’s not a standalone item, but rather a vital step in a process that ensures the authenticity and encrypted integrity of websites and online services. To truly grasp what a CSR SSL certificate entails, we must delve into the intricacies of Public Key Infrastructure (PKI) and the role of SSL/TLS certificates in establishing trust in the digital landscape.
The Foundation: Understanding SSL/TLS Certificates
Before we can discuss the CSR, it’s essential to understand what an SSL/TLS certificate is and why it’s so important. SSL (Secure Sockets Layer) and its successor, TLS (Transport Layer Security), are cryptographic protocols designed to provide secure communication over a computer network. When you see “https://” at the beginning of a website’s URL and a padlock icon in your browser’s address bar, it signifies that your connection to that website is secured by an SSL/TLS certificate.
These certificates serve two primary purposes:
- Encryption: They encrypt the data transmitted between your browser and the website’s server. This means that any information you send, such as login credentials, credit card details, or personal information, is scrambled and unreadable to anyone who might intercept it. This is particularly vital for e-commerce sites, banking portals, and any platform handling sensitive user data.
- Authentication: They verify the identity of the website’s owner. When your browser connects to a website with an SSL/TLS certificate, it checks the certificate’s validity with a trusted Certificate Authority (CA). This process ensures that you are indeed communicating with the legitimate website and not a malicious imposter attempting to phish for your information.
Without SSL/TLS certificates, the internet would be a far more vulnerable place, with data easily intercepted and fake websites masquerading as legitimate ones. The widespread adoption of SSL/TLS has become a standard expectation for online security and a significant factor in building user trust.
The Crucial Step: The Certificate Signing Request (CSR)
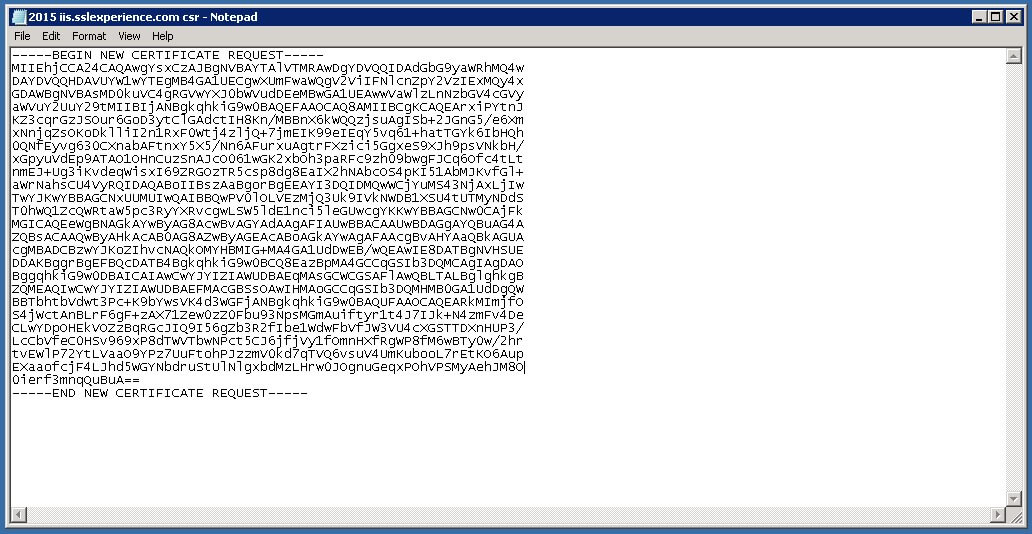
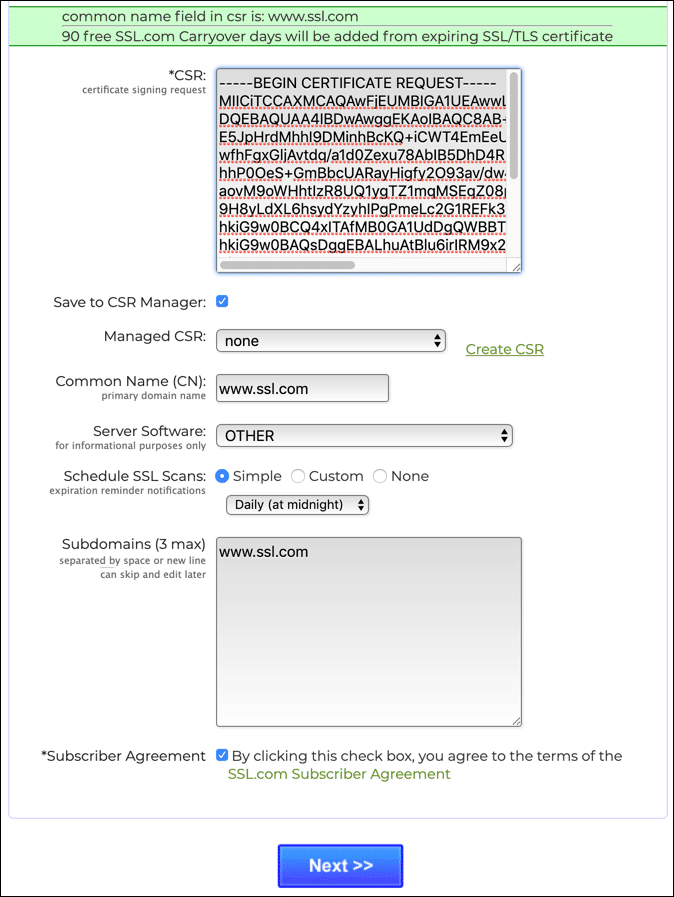
Now, let’s address the “CSR” part of the equation. A Certificate Signing Request (CSR) is essentially a block of encoded text that contains information about your organization and the public key you intend to use with your SSL/TLS certificate. Think of it as an application you submit to a Certificate Authority (CA) when you want to get an SSL/TLS certificate issued for your domain.
The CSR is generated on your web server. It contains vital information that the CA will use to verify your identity and create the corresponding digital certificate. This information typically includes:
- Common Name (CN): This is the fully qualified domain name (FQDN) for which you are requesting the certificate. For example,
www.example.comormail.example.com. For wildcard certificates, it would be*.example.com. - Organization Name (O): The legal name of your organization.
- Organizational Unit (OU): A department or unit within your organization (e.g., “IT Department,” “Web Services”).
- City or Locality (L): The city where your organization is located.
- State or Province (ST): The state or province where your organization is located.
- Country (C): The two-letter ISO code for your country (e.g., “US” for United States, “GB” for United Kingdom).
- Public Key: This is the public component of a public-key cryptography pair. The private key, which must be kept secret, is generated alongside the public key and remains on your server. The CSR includes the public key that will be embedded in the final SSL/TLS certificate.
The process of generating a CSR involves creating a pair of cryptographic keys: a private key and a public key. The private key is securely stored on your server and should never be shared. The public key, along with the organizational information, is what you include in the CSR. This public key is what the CA will use to issue the certificate, and it works in tandem with your private key to establish the secure, encrypted connection.
Why is the CSR so important?

The CSR is the gateway to obtaining a trusted SSL/TLS certificate. Without a valid CSR, a CA cannot issue a certificate because they lack the necessary information to verify your identity and create the digital signature that binds the certificate to your domain and organization. It’s the formal request that initiates the validation process by the CA.
The Certificate Authority (CA) and the Issuance Process
Once you’ve generated your CSR, you submit it to a Certificate Authority (CA). CAs are trusted third-party organizations that are responsible for issuing and managing digital certificates. Some of the most well-known CAs include DigiCert, Sectigo (formerly Comodo CA), GlobalSign, and Let’s Encrypt.
The CA will then undertake a validation process, which varies depending on the type of SSL/TLS certificate you are requesting:
- Domain Validated (DV): The CA verifies that you own or control the domain for which you are requesting the certificate. This is the most basic and fastest validation method, often involving an email verification or a DNS record check.
- Organization Validated (OV): In addition to domain ownership, the CA verifies the legal existence and identity of your organization. This usually involves checking business registration documents and other official records.
- Extended Validation (EV): This is the most rigorous validation process. The CA conducts a thorough investigation into the legal, physical, and operational existence of your organization, adhering to strict industry guidelines. EV certificates typically display the organization’s name prominently in the browser’s address bar, providing a higher level of user trust.
After the CA has successfully validated your information, they will use the public key and organizational data from your CSR to generate and digitally sign your SSL/TLS certificate. This signed certificate is then sent back to you, along with any intermediate certificates required for proper chain of trust.
Installing and Utilizing the SSL/TLS Certificate
The final step in the “CSR SSL certificate” lifecycle is installing the issued certificate on your web server. This process differs depending on your server software (e.g., Apache, Nginx, IIS) and hosting environment. Generally, it involves uploading the certificate file, the private key (which you generated alongside the CSR and must have kept secure), and any intermediate certificates to your server and configuring your web server to use them for HTTPS connections.
Once installed, your server will use the private key to decrypt information sent by clients (browsers) and the public key embedded in the certificate to encrypt information sent back to clients. This handshake process, enabled by the SSL/TLS certificate, ensures that all communication between your website and its visitors is secure and authenticated.
Common Misconceptions and Clarifications
It’s important to clarify that “CSR SSL certificate” is not a specific type of certificate. Instead, it refers to the process of obtaining an SSL/TLS certificate, where the CSR is a critical component. You don’t “buy” a CSR; you generate one to request an SSL/TLS certificate.
Another point of clarification is the relationship between the CSR and the private key. The CSR contains the public key, while the private key is generated at the same time and must be kept securely on your server. If you lose your private key, you will not be able to use your SSL/TLS certificate, and you will need to generate a new CSR and obtain a new certificate.
In summary, a CSR SSL certificate is fundamentally about securing online communications. The CSR is the essential application submitted to a Certificate Authority, containing your domain and organizational details along with your public key, which allows the CA to issue a trusted SSL/TLS certificate. This certificate then enables encryption and authentication, safeguarding sensitive data and building confidence for users interacting with your website or online service. In the modern digital ecosystem, understanding and correctly implementing this process is paramount for any entity operating online.
