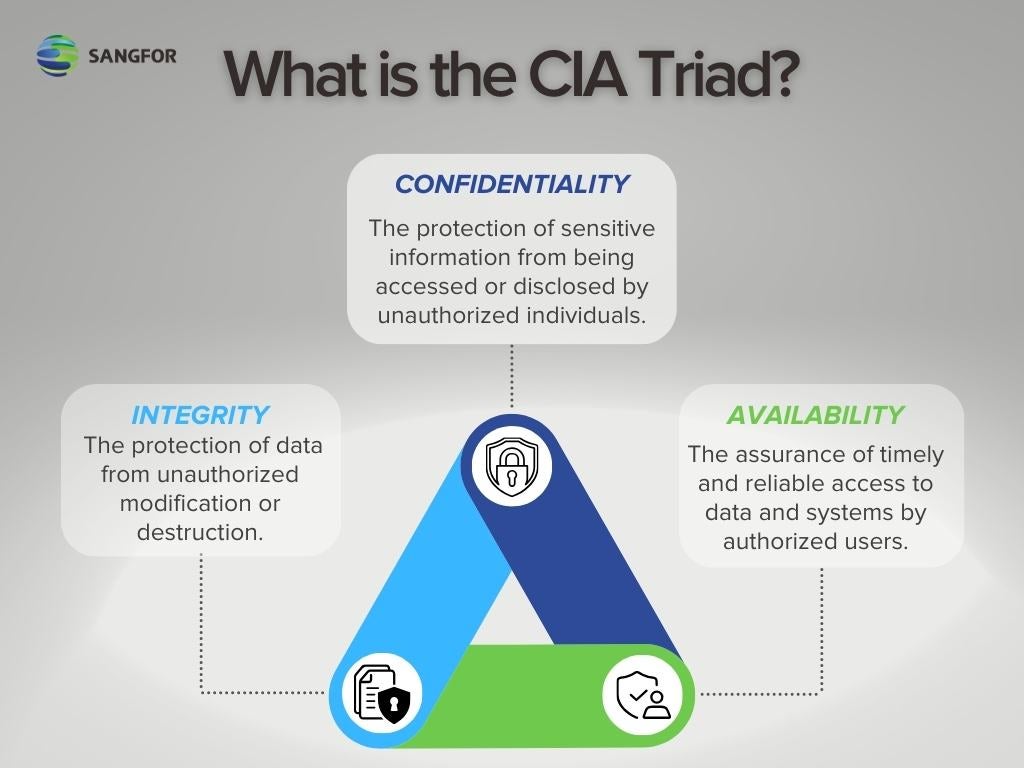
The realm of cybersecurity is a constantly evolving battleground, and understanding its fundamental principles is crucial for effective defense. Among the core tenets of this field, the “CIA Triad” stands out as a foundational model. CIA, in this context, is not an acronym for the Central Intelligence Agency, but rather for Confidentiality, Integrity, and Availability. These three principles represent the essential goals of any robust cybersecurity strategy, forming the bedrock upon which protective measures are built. Ignoring any one of these pillars can leave systems and data vulnerable to a wide array of threats, from unauthorized access and data breaches to system failures and operational disruptions.
Confidentiality: Keeping Secrets Safe
Confidentiality, the first component of the CIA Triad, is concerned with protecting sensitive information from unauthorized disclosure. In essence, it’s about ensuring that only authorized individuals or systems can access specific data. This principle is paramount in environments where personal identifiable information (PII), financial records, intellectual property, or classified government data are handled.
Access Control and Authentication
At the heart of maintaining confidentiality lies robust access control. This involves implementing mechanisms that verify the identity of users or systems attempting to access resources and then granting them appropriate permissions based on their role and necessity.
User Authentication
Authentication is the process of verifying who a user claims to be. This can be achieved through various methods, each with its own strengths and weaknesses:
- Something You Know: This typically involves passwords or personal identification numbers (PINs). While widely used, they are susceptible to brute-force attacks, phishing, and credential stuffing if not managed properly.
- Something You Have: This refers to physical tokens, smart cards, or security keys that a user possesses. These are generally more secure than passwords alone but can be lost, stolen, or compromised.
- Something You Are: This category encompasses biometrics, such as fingerprints, facial recognition, or iris scans. Biometric authentication offers a high level of security as it’s unique to the individual, but concerns about privacy, data storage, and potential spoofing exist.
Multi-factor authentication (MFA), which combines two or more of these methods, significantly enhances security by requiring multiple forms of verification before granting access, making it much harder for unauthorized individuals to gain entry.
Authorization and Permissions
Once a user or system is authenticated, authorization dictates what they are allowed to do. This involves assigning specific permissions or privileges that define the scope of their access to data, applications, and system resources. The principle of least privilege is a critical best practice here, meaning users should only be granted the minimum level of access necessary to perform their job functions. This minimizes the potential damage if an account is compromised.
Encryption and Data Protection
Encryption plays a vital role in ensuring confidentiality, especially when data is in transit or at rest.
Data in Transit Encryption
When data travels across networks, such as the internet, it is vulnerable to interception. Encryption protocols like TLS/SSL (Transport Layer Security/Secure Sockets Layer) are used to scramble data, making it unreadable to anyone who might intercept it. This is why secure websites use HTTPS, indicated by a padlock icon in the browser’s address bar. VPNs (Virtual Private Networks) also use encryption to create secure tunnels for network traffic.
Data at Rest Encryption
Data stored on hard drives, servers, or cloud storage can also be compromised if the physical storage medium is stolen or accessed without authorization. Encryption at rest involves encoding data stored on these devices, so even if unauthorized physical access is gained, the data remains unintelligible without the correct decryption key.
Data Masking and Anonymization
In certain scenarios, such as testing or development environments, it may be necessary to use sensitive data without exposing the actual sensitive information. Data masking and anonymization techniques create fictionalized versions of sensitive data that retain the structural characteristics and statistical properties of the original data, thereby protecting the confidentiality of the real information.
Integrity: Ensuring Data Accuracy and Trustworthiness
Integrity, the second pillar of the CIA Triad, focuses on maintaining the accuracy, completeness, and consistency of data throughout its lifecycle. It’s about ensuring that data has not been altered or corrupted in an unauthorized or accidental manner. Compromised data integrity can lead to flawed decision-making, incorrect operations, and a loss of trust in the information.
Hashing and Digital Signatures
Technological solutions are essential for verifying data integrity. Hashing algorithms and digital signatures are two powerful tools in this regard.
Hashing
A hash function takes an input (of any size) and produces a fixed-size string of characters, known as a hash value or digest. Even a small change in the input data will result in a completely different hash value. By comparing the hash of a piece of data with a known, trusted hash, one can quickly detect if the data has been altered. This is commonly used to verify the integrity of downloaded files or to store password representations securely.
Digital Signatures
Digital signatures combine hashing with public-key cryptography. A sender hashes a message and then encrypts that hash with their private key. The recipient can then decrypt the hash using the sender’s public key and re-hash the received message. If the decrypted hash matches the re-calculated hash, it confirms both the integrity of the message (it hasn’t been tampered with) and the authenticity of the sender (only the holder of the private key could have created that signature).
Version Control and Audit Trails
Maintaining the integrity of systems and data also relies on processes that track changes and provide accountability.
Version Control Systems
For software development and document management, version control systems (VCS) are indispensable. They track every change made to files, allowing developers to revert to previous versions, compare different revisions, and understand the history of modifications. This ensures that the current state of a project or document is a known and traceable evolution, rather than an uncontrolled alteration.
Audit Trails and Logging
Comprehensive audit trails and logging mechanisms are crucial for monitoring system activity and detecting unauthorized modifications. These systems record who did what, when, and on which resource. By reviewing these logs, security professionals can identify suspicious activities, investigate security incidents, and reconstruct events to understand how data integrity might have been compromised.
Data Validation and Error Detection
Implementing robust data validation and error detection mechanisms at various points in data processing can prevent corrupted or inaccurate data from entering or propagating through a system. This includes input validation to ensure data conforms to expected formats and constraints, as well as checksums and parity bits to detect transmission errors.
Availability: Ensuring Access When Needed
Availability, the third and final component of the CIA Triad, guarantees that authorized users can access information and systems when they need them. This principle is about ensuring continuous operation and preventing disruptions that could hinder productivity or critical functions. Outages, denial-of-service attacks, or hardware failures can all compromise availability.
Redundancy and Failover
To ensure systems remain operational even in the face of component failures, redundancy and failover mechanisms are employed.
Hardware Redundancy
This involves having duplicate hardware components, such as power supplies, network interfaces, or even entire servers. If one component fails, a backup component can immediately take over its function, often without any noticeable interruption to users.
Data Redundancy and Backups
Regular backups of data are essential for recovery in case of data loss or corruption. However, availability goes beyond just backups. It involves strategies like RAID (Redundant Array of Independent Disks) for disk storage, which distributes data across multiple drives to provide fault tolerance. Furthermore, geographically dispersed data centers and replication can ensure that data is accessible even if an entire facility is affected by a disaster.
Disaster Recovery and Business Continuity Planning
Beyond immediate hardware and data redundancy, comprehensive disaster recovery (DR) and business continuity (BC) plans are critical for long-term availability.
Disaster Recovery Plans
DR plans outline the procedures and resources needed to restore IT operations after a catastrophic event, such as a natural disaster or a major cyberattack. This includes steps for data restoration, system recovery, and network re-establishment.
Business Continuity Plans
BC plans are broader, focusing on maintaining essential business functions during and after a disruption. They encompass not only IT systems but also personnel, processes, and facilities, ensuring that the organization can continue to operate at an acceptable level, even under adverse conditions.
Network and System Resilience
Designing networks and systems with resilience in mind is fundamental to availability.
Load Balancing
Load balancers distribute incoming network traffic across multiple servers. This prevents any single server from becoming overwhelmed, which can lead to performance degradation or complete failure. It also allows for seamless addition or removal of servers without service interruption.
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Mitigation
DoS and DDoS attacks aim to overwhelm a system with traffic, making it unavailable to legitimate users. Robust security measures, including traffic filtering, rate limiting, and specialized DDoS mitigation services, are crucial to protecting against these threats and ensuring continuous availability.

Regular Maintenance and Patching
Proactive maintenance and timely patching of systems and software are vital for preventing vulnerabilities that could be exploited to cause downtime. Regularly updating operating systems, applications, and security software helps to fix bugs, close security holes, and improve system stability, thereby contributing to overall availability.
In conclusion, the CIA Triad – Confidentiality, Integrity, and Availability – provides a vital framework for understanding and implementing effective cybersecurity strategies. By focusing on these three interconnected goals, organizations can build more resilient, trustworthy, and secure digital environments, safeguarding their valuable assets and ensuring uninterrupted operations in an increasingly complex threat landscape.
