AWS Identity and Access Management (IAM) Security Token Service (STS) is a foundational component of Amazon Web Services (AWS) that enables you to grant temporary, limited-privilege access to your AWS resources. In essence, it allows you to manage who can access what, for how long, and with what permissions, without the need for long-term credentials. This is particularly crucial in dynamic environments, microservices architectures, and for applications requiring fine-grained control over resource access. Understanding AWS STS is paramount for building secure, scalable, and robust cloud applications.
Understanding the Core Concepts of AWS STS
At its heart, AWS STS revolves around the concept of temporary security credentials. Unlike IAM users who have long-lived access keys and secret access keys, STS generates short-lived credentials that consist of an access key ID, a secret access key, and a session token. These credentials are valid for a limited duration, typically between 15 minutes and 36 hours, after which they expire. This temporal limitation significantly enhances security by reducing the window of opportunity for compromised credentials to be exploited.

The primary objective of AWS STS is to facilitate the principle of least privilege. By issuing temporary credentials with precisely defined permissions, you ensure that entities (users, applications, or services) only have the access necessary to perform their intended tasks. This minimizes the potential damage if a credential is leaked or misused.
Temporary Security Credentials
The output of an STS operation is a set of temporary security credentials. These credentials are not permanent and are tied to a specific session. When you call an STS API to assume a role or get federated user credentials, STS returns these temporary credentials along with their expiration time. Your application or service then uses these temporary credentials to make subsequent AWS API requests. This is a fundamental shift from managing long-lived access keys, which, if compromised, could grant attackers indefinite access to your AWS environment.
Role-Based Access Control (RBAC)
AWS STS heavily leverages role-based access control. Instead of directly assigning permissions to individual IAM users or applications, you define IAM roles. A role is a set of permissions that you can assign to an entity. This entity can then “assume” the role to gain temporary access with the permissions defined in that role. This approach simplifies permission management, especially in large organizations. Instead of managing hundreds or thousands of individual user policies, you manage a smaller set of role policies.
For example, an application running on an EC2 instance might not need its own long-term access keys. Instead, you can assign an IAM role to the EC2 instance. The EC2 instance can then use STS to obtain temporary credentials associated with that role, allowing it to interact with other AWS services like S3 or DynamoDB.
Federation and Identity Providers
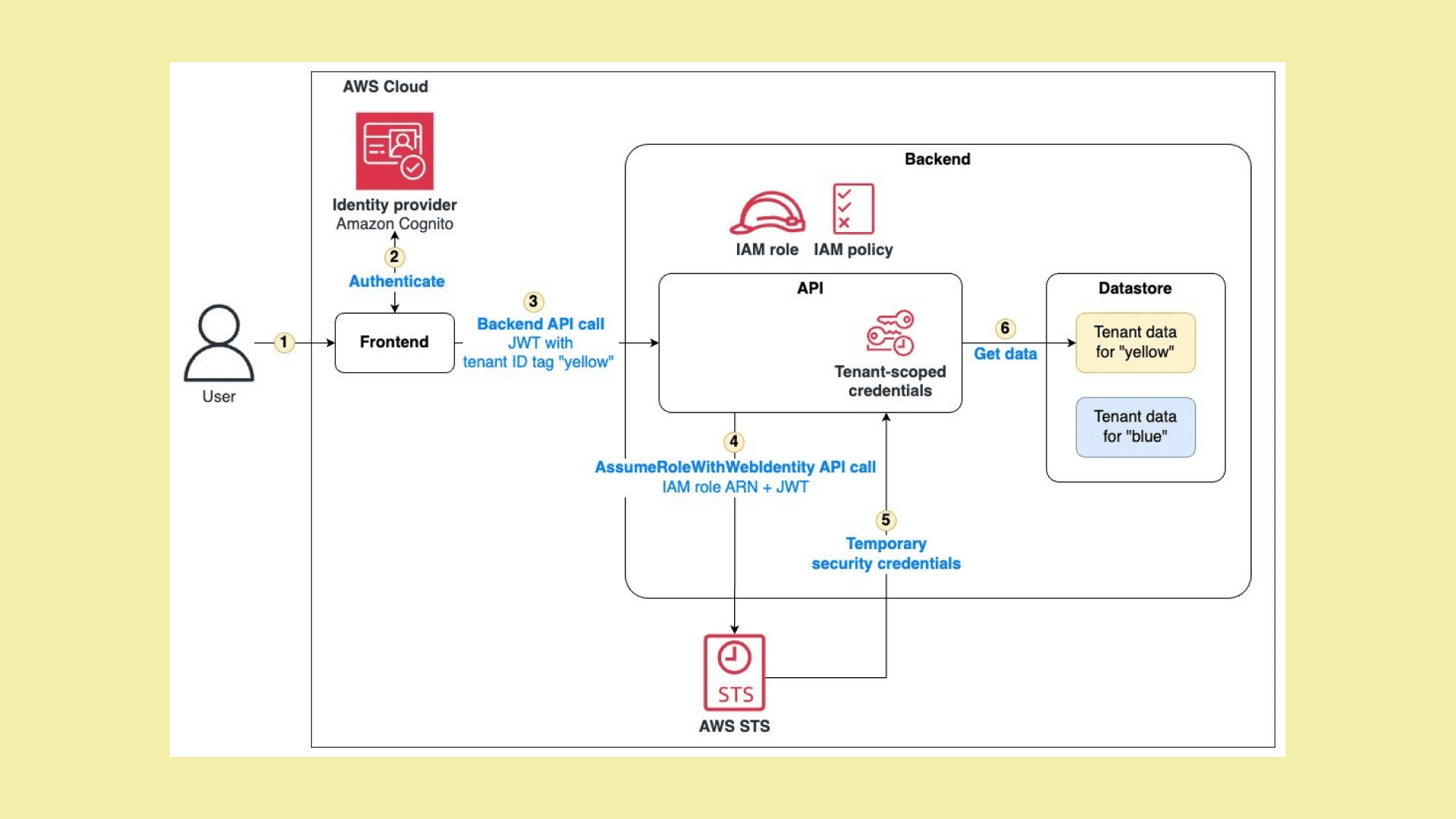
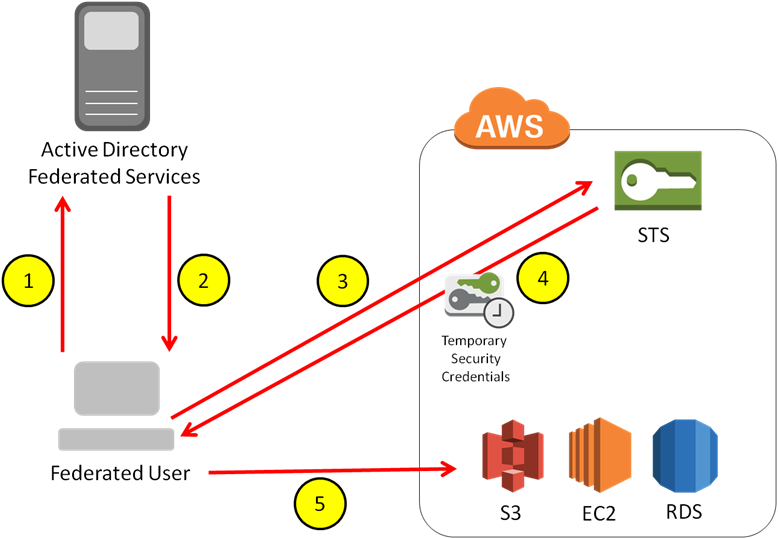
Another key use case for AWS STS is identity federation. This allows you to grant access to your AWS account to users who are managed by an external identity provider (IdP). Popular IdPs include Active Directory Federation Services (AD FS), Okta, Ping Identity, and even social identity providers like Google or Facebook.
When a user authenticates with an external IdP, the IdP can generate a SAML (Security Assertion Markup Language) assertion or an OpenID Connect (OIDC) token. This assertion/token can then be sent to AWS STS. STS validates the assertion/token and, if valid, issues temporary security credentials to the user. This enables single sign-on (SSO) capabilities, allowing users to access AWS resources using their existing corporate credentials.
Key AWS STS API Operations
AWS STS provides several API operations, each serving a distinct purpose in managing temporary credentials. Understanding these operations is crucial for effectively integrating STS into your applications and workflows.
AssumeRole
The AssumeRole API operation is one of the most frequently used STS operations. It allows an entity to assume an IAM role. When you call AssumeRole, you specify the ARN (Amazon Resource Name) of the role you want to assume, along with an optional session name. If the calling entity has the necessary permissions to assume the specified role, STS returns temporary security credentials associated with that role.
The AssumeRole operation is instrumental in scenarios like:
- Granting Cross-Account Access: A user or service in one AWS account can assume a role in another AWS account to access resources there. This is a secure way to share resources without creating duplicate IAM users or managing long-lived credentials across accounts.
- Application Access: Applications running on EC2 instances, Lambda functions, or other compute services can assume roles to obtain permissions to interact with other AWS services.
- Federated Access: As mentioned earlier, federated users can use
AssumeRole(often indirectly via thests:AssumeRoleWithSAMLorsts:AssumeRoleWithWebIdentitycalls) to gain temporary access to AWS resources.
The AssumeRole operation is a cornerstone of secure cross-account and application-level access management in AWS.
GetCallerIdentity
The GetCallerIdentity operation is a simple yet useful API call. It returns information about the IAM entity that is making the call. This includes the Account ID, User ID, and ARN of the caller. This is particularly helpful for debugging and understanding what identity is currently being used by an application or script. When using temporary credentials, GetCallerIdentity will reflect the identity derived from the assumed role.
GetFederationToken
The GetFederationToken API operation allows you to generate temporary security credentials for a user or application that is not directly managed by IAM. You can specify a duration for these credentials and a set of policies that will define the permissions granted. This operation is often used in conjunction with custom identity brokers or when you need to grant temporary access to a broad set of users from a non-AWS identity source.
The policies provided to GetFederationToken are applied as a “session policy.” This policy acts as a maximum boundary on the permissions that can be granted. Even if the underlying IAM user has broader permissions, the session policy will restrict what the temporary credentials can do.
DecodeAuthorizationMessage
The DecodeAuthorizationMessage API operation is used to decode authorization messages that are returned by AWS when an access denied error occurs. These messages can provide valuable insights into why a request was denied, helping developers to troubleshoot and correct their IAM policies.
Integrating AWS STS into Your Workflows
Implementing AWS STS effectively involves understanding how to integrate its capabilities into your existing and future workflows. This often involves programmatic interaction with STS APIs.
Programmatic Access with AWS SDKs
The most common way to interact with AWS STS is through the AWS Software Development Kits (SDKs). These SDKs are available for a wide range of programming languages, including Python (Boto3), Java, Node.js, Go, .NET, and more.
Using an SDK, you can write code that calls AssumeRole, GetFederationToken, or other STS operations. For instance, in a Python application using Boto3, you might write code like this:
import boto3
sts_client = boto3.client('sts')
response = sts_client.assume_role(
RoleArn='arn:aws:iam::123456789012:role/MyApplicationRole',
RoleSessionName='MyApplicationSession'
)
credentials = response['Credentials']
access_key_id = credentials['AccessKeyId']
secret_access_key = credentials['SecretAccessKey']
session_token = credentials['SessionToken']
# Now use these temporary credentials to make calls to other AWS services
This programmatic approach is essential for building dynamic and secure cloud applications.
Leveraging IAM Roles for EC2 and Lambda
As mentioned earlier, IAM roles are a cornerstone of secure application access. For services like EC2 and Lambda, AWS provides simplified mechanisms for assuming roles.
- EC2 Instances: When you launch an EC2 instance, you can associate an IAM role with it. The instance automatically retrieves temporary credentials from STS and makes them available on a local metadata endpoint (
http://169.254.169.254/latest/meta-data/iam/security-credentials/ROLE_NAME). Applications running on the instance can then query this endpoint to obtain the credentials. - AWS Lambda Functions: Similarly, you can assign an IAM role to a Lambda function. The Lambda execution environment automatically provides the temporary credentials to the function’s runtime, allowing it to interact with other AWS services.
This eliminates the need to manage access keys directly within your application code or configuration files.
Identity Federation with SAML and OIDC
Integrating with external identity providers for federated access requires a few key steps:
- Configure the Identity Provider: Set up your IdP to trust your AWS account and configure it to generate SAML assertions or OIDC tokens.
- Create IAM Roles: Define IAM roles in your AWS account that specify the permissions federated users will have. These roles need a trust relationship configured to allow the IdP to assume them.
- Implement a Relying Party Application: This application (e.g., a web application) handles the user authentication with the IdP. Once authenticated, it exchanges the SAML assertion or OIDC token with AWS STS (
AssumeRoleWithSAMLorAssumeRoleWithWebIdentity) to obtain temporary AWS credentials. - Use Temporary Credentials: The relying party application then uses these temporary credentials to access AWS resources on behalf of the federated user, or it can pass them back to the user’s browser (e.g., via JavaScript) to allow direct access to AWS services from the client-side.
This enables seamless and secure access for your users from their existing authentication systems.
Advanced Use Cases and Security Considerations
Beyond basic role assumption and federation, AWS STS supports more advanced scenarios and necessitates careful security considerations.
Cross-Account Access Best Practices
When granting cross-account access using AssumeRole, follow these best practices:
- Principle of Least Privilege: Define granular IAM policies for the roles in the resource account. Grant only the necessary permissions for the cross-account entity to perform its tasks.
- Restrict Principals: In the trust policy of the role in the resource account, explicitly list the ARNs of the principals (users, roles, or accounts) that are allowed to assume this role. Avoid overly permissive trust policies.
- Session Policies: Use session policies when calling
AssumeRoleto further restrict the permissions of the assumed role session. This provides an additional layer of control. - Session Names: Use descriptive and unique session names to easily identify assumed role sessions in CloudTrail logs.
Security of Temporary Credentials
While temporary credentials offer enhanced security, their management is still critical:
- Short Lifetimes: Always use the shortest possible duration for temporary credentials. Regularly rotate credentials by re-issuing them.
- Secure Storage: If your application needs to store temporary credentials (though this should be avoided where possible), ensure they are stored securely, for instance, using AWS Secrets Manager or Parameter Store.
- Credential Hoarding: Implement mechanisms to prevent credential hoarding. Applications should not store credentials longer than absolutely necessary.
Auditing and Monitoring with CloudTrail
AWS CloudTrail is indispensable for monitoring STS activity. Every call to an STS API operation is logged in CloudTrail, providing an audit trail of who assumed which role, from where, and when.
- Monitor
AssumeRoleCalls: Regularly review CloudTrail logs forAssumeRoleevents. Look for unusual or unauthorized role assumptions. - Investigate Access Denied Events: Correlate
Access Deniederrors with STS logs to understand policy misconfigurations or potential security breaches. - Set Up Alarms: Configure CloudWatch alarms based on CloudTrail events to alert you to suspicious STS activity, such as frequent failed
AssumeRoleattempts or assumptions from unexpected IP addresses.
Conclusion
AWS STS is a powerful and essential service for managing access to your AWS resources securely and efficiently. By understanding and utilizing temporary security credentials, role-based access control, and identity federation, you can significantly enhance your cloud security posture. Whether you’re building microservices, enabling cross-account collaboration, or integrating with external identity providers, AWS STS provides the flexible and robust tools necessary to implement the principle of least privilege and safeguard your cloud environment. Its programmatic nature and integration with AWS SDKs make it a core component for any modern cloud architecture.
