In the dynamic landscape of modern technology, where digital infrastructure forms the backbone of nearly every industry, computer security auditing stands as an indispensable discipline. Far from a mere bureaucratic exercise, it represents a proactive and systematic evaluation of an organization’s information systems, networks, applications, and processes to ensure their integrity, confidentiality, and availability. This intricate process is designed to identify vulnerabilities, assess compliance with established policies and regulations, and ultimately fortify an organization’s digital defenses against an ever-evolving array of threats. It is a critical component of risk management, offering a comprehensive snapshot of an organization’s security posture and guiding strategic improvements to protect sensitive data and critical operations.
The Fundamental Purpose of Security Auditing
The core objective of computer security auditing is multifaceted, extending beyond simple fault-finding to encompass strategic assurance and continuous improvement. It provides an independent and objective assessment, crucial for maintaining trust in digital systems, both internally and externally. In an era where data breaches can have catastrophic financial and reputational consequences, understanding and mitigating risks through robust auditing practices is paramount.
Ensuring Compliance and Governance
One of the primary drivers for security auditing is the imperative to meet regulatory and industry compliance standards. Organizations across sectors are subject to a complex web of regulations, such as GDPR, HIPAA, PCI DSS, and SOX, each imposing stringent requirements for data protection, privacy, and system security. Security audits verify adherence to these mandates, demonstrating due diligence and mitigating the risk of hefty fines, legal repercussions, and public distrust. Beyond external regulations, audits also confirm compliance with an organization’s internal security policies, governance frameworks, and best practices, ensuring that established controls are functioning as intended and that employees understand and follow security protocols. This aspect of auditing is not just about avoiding penalties; it’s about embedding a culture of security and accountability throughout the organizational structure.
Identifying Vulnerabilities Proactively
Perhaps the most tangible benefit of a security audit is its ability to uncover weaknesses before they can be exploited by malicious actors. Unlike reactive measures taken after an incident, auditing is a proactive strategy. It systematically probes systems, configurations, and processes for loopholes, misconfigurations, outdated software, weak access controls, and other potential entry points for attackers. By identifying these vulnerabilities, organizations can prioritize remediation efforts, allocating resources effectively to address the most critical risks. This foresight is invaluable, preventing potential data breaches, service disruptions, and financial losses that could arise from successful cyberattacks. A comprehensive audit examines not just technical flaws but also procedural gaps, such as inadequate patch management, weak password policies, or insufficient employee training, recognizing that human error remains a significant vector for compromise.
Methodologies and Technological Approaches to Auditing
The execution of a computer security audit employs a variety of methodologies, ranging from manual inspections to highly automated processes, often combining both for a comprehensive assessment. The technological advancements in recent years have profoundly influenced how audits are conducted, enhancing their depth, speed, and accuracy.
Automated vs. Manual Audits
Audits typically integrate both automated tools and manual expertise. Automated auditing tools are essential for efficiently scanning large infrastructures, detecting common vulnerabilities, misconfigurations, and non-compliance with predefined security policies. These tools can perform network scans, vulnerability assessments, penetration tests, and code reviews at scale, flagging potential issues for further investigation. They provide a rapid, consistent, and objective initial layer of analysis.
However, automated tools alone are insufficient. Manual audits, performed by experienced security professionals, offer the nuanced judgment and contextual understanding that machines cannot replicate. Human auditors can interpret complex findings, identify logical flaws in application design, social engineering vulnerabilities, and business process weaknesses that automated scanners might miss. They also perform interviews, review documentation, and conduct deeper forensic analysis where automated alerts indicate potential sophisticated threats. The synergy between automated efficiency and human insight creates a robust auditing framework.
Leveraging AI and Machine Learning in Auditing
The integration of Artificial Intelligence (AI) and Machine Learning (ML) is revolutionizing security auditing. AI-driven systems can analyze vast datasets of logs, network traffic, and system behaviors at speeds impossible for human auditors. They can identify anomalous patterns indicative of sophisticated threats, predict potential vulnerabilities based on historical data, and even suggest remediation strategies. ML algorithms continuously learn from new threats and attack vectors, refining their detection capabilities over time. For instance, AI can enhance security information and event management (SIEM) systems by improving the correlation of disparate security events, reducing false positives, and accelerating incident response. This innovative application allows for more intelligent threat hunting and a proactive stance against zero-day exploits and advanced persistent threats (APTs), transforming auditing from a periodic check-up into a continuous, intelligent monitoring process.
The Role of Continuous Monitoring and Real-time Analytics
Traditional audits, often conducted annually or semi-annually, provide a snapshot in time. However, the nature of cyber threats demands a more dynamic approach. Continuous monitoring and real-time analytics are emerging as critical components of modern security auditing. This approach involves constantly collecting and analyzing security data from various sources—network devices, servers, applications, and user activity logs—to detect deviations from baselines or indicators of compromise as they occur. Technologies like Security Information and Event Management (SIEM) and Security Orchestration, Automation, and Response (SOAR) platforms are central to this. They aggregate data, apply analytics, and can even automate initial responses to detected threats. This real-time visibility allows organizations to identify and address security incidents almost instantly, drastically reducing the window of opportunity for attackers and moving beyond reactive incident response to proactive threat mitigation.

Key Areas of Focus in Modern Security Audits
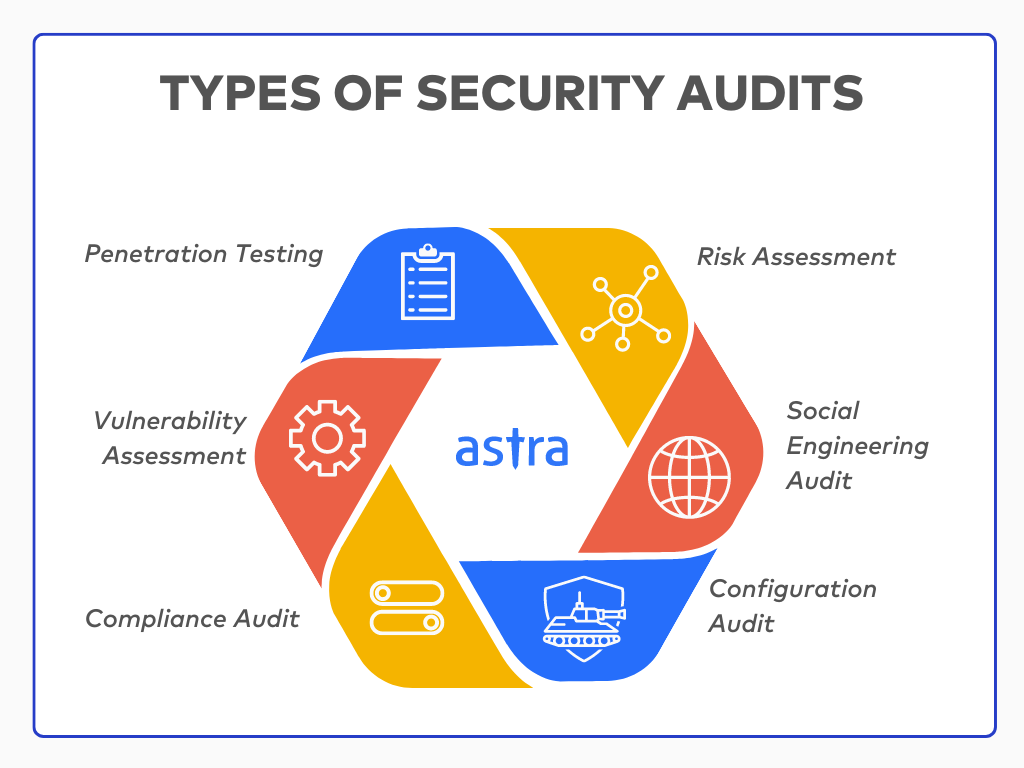
A comprehensive security audit typically scrutinizes multiple facets of an organization’s technology stack and operational procedures. Modern audits are holistic, recognizing that security is a chain, and its strength is determined by its weakest link.
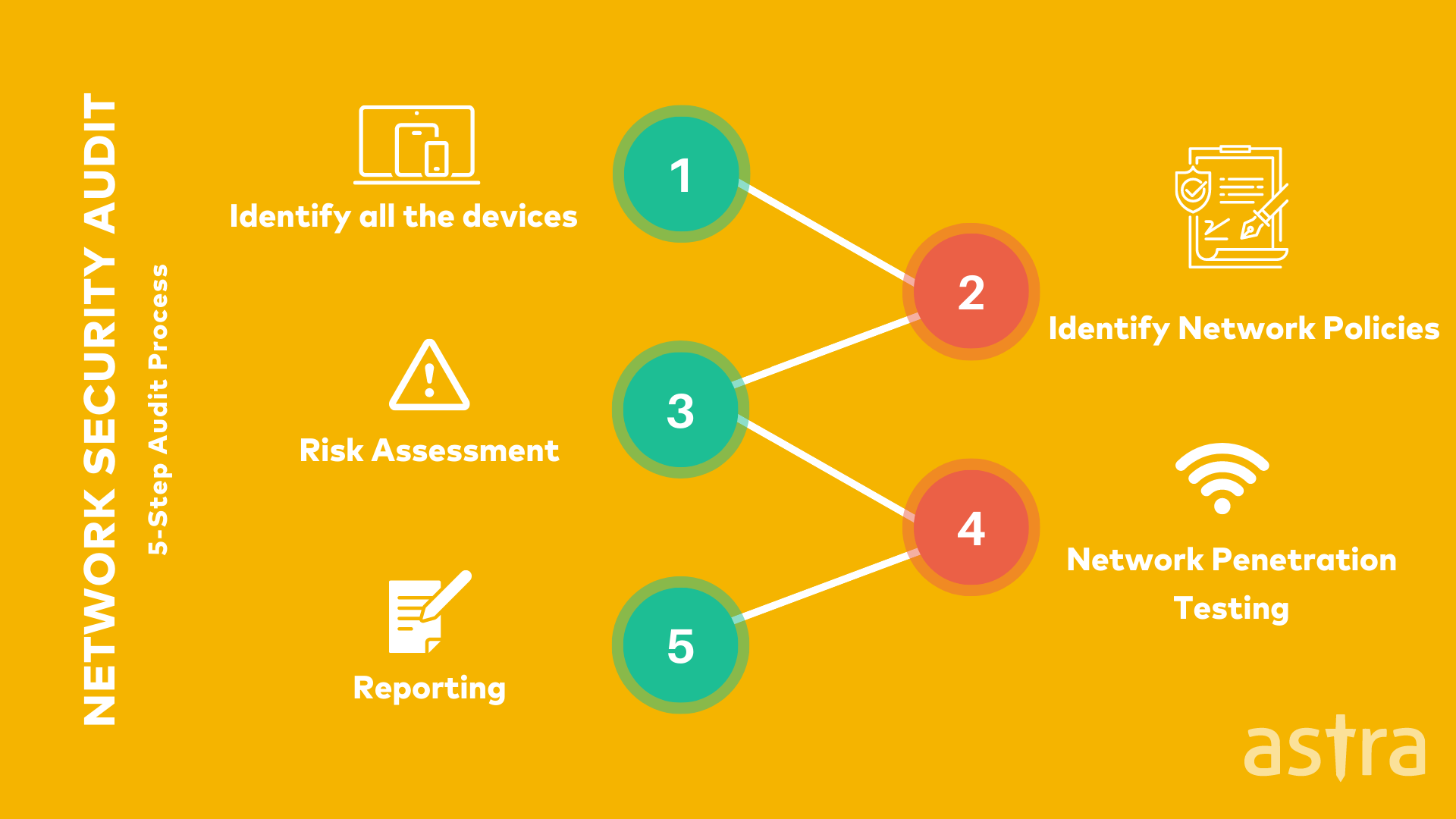
Network and Infrastructure Audits
This area focuses on the security posture of an organization’s network devices, servers, firewalls, routers, switches, and other critical infrastructure components. Audits review network architecture, firewall rules, intrusion detection/prevention systems (IDS/IPS), patch management, system hardening, and configuration settings. They assess network segmentation, wireless security, and remote access controls to ensure that only authorized traffic and users can access sensitive resources. The goal is to identify open ports, misconfigured devices, outdated firmware, and other weaknesses that could be exploited to gain unauthorized network access or disrupt services.
Application Security Audits
Applications, especially web-facing and custom-developed software, often present significant attack surfaces. Application security audits involve assessing the security of software throughout its lifecycle, from design and development to deployment and maintenance. This includes source code reviews, penetration testing of live applications, and vulnerability scanning for common flaws such as SQL injection, cross-site scripting (XSS), insecure authentication, and broken access control. Audits also examine API security, third-party library dependencies, and the secure configuration of application servers, ensuring that applications are built and operated with security in mind.
Cloud Security Audits
As more organizations migrate to cloud environments (IaaS, PaaS, SaaS), cloud security auditing has become a specialized and critical domain. These audits evaluate the security configurations of cloud services, adherence to shared responsibility models, identity and access management (IAM) policies, data encryption practices, and compliance with cloud-specific regulations. They assess the security of virtual machines, container orchestration platforms (like Kubernetes), serverless functions, and cloud storage solutions. Cloud audits often involve reviewing cloud service provider (CSP) certifications, configurations of cloud security posture management (CSPM) tools, and the implementation of robust network security groups and virtual private clouds (VPCs).
Data Integrity and Privacy Audits
With increasing data volumes and stringent privacy regulations, audits specifically address data integrity, confidentiality, and privacy. These audits examine how sensitive data is collected, stored, processed, transmitted, and ultimately disposed of. They verify the implementation of data encryption at rest and in transit, data access controls, data loss prevention (DLP) measures, and data retention policies. Compliance with privacy regulations like GDPR, CCPA, and similar frameworks is a central focus, ensuring that personal identifiable information (PII) and other sensitive data are handled in accordance with legal and ethical requirements, minimizing the risk of privacy breaches and regulatory non-compliance.
The Evolving Landscape: Challenges and Future Trends
The field of computer security auditing is in a perpetual state of evolution, driven by the rapid pace of technological change and the increasing sophistication of cyber threats. Auditors face ongoing challenges but also stand on the cusp of significant innovation.
Adapting to Emerging Threats
The emergence of new technologies like quantum computing, advanced AI in attack tools, and the pervasive Internet of Things (IoT) continually introduces novel attack vectors and vulnerabilities. Auditors must continuously update their knowledge and tools to keep pace with these developments. Auditing IoT devices, for instance, requires specialized expertise in embedded systems, real-time operating systems, and unique connectivity protocols. Similarly, securing AI/ML systems demands audits that assess not only the underlying infrastructure but also the integrity of algorithms, training data, and potential for adversarial AI attacks. The challenge lies in developing audit methodologies and tools that can effectively scrutinize these complex and rapidly changing technological frontiers.
The Human Element and Skill Gaps
Despite advances in automation, the human element remains critical in security auditing. There is a persistent global shortage of skilled cybersecurity professionals, including auditors with the expertise to navigate complex IT environments and understand intricate threat landscapes. The demand for auditors with specialized knowledge in areas like cloud security, industrial control systems (ICS), application security, and AI security far outstrips supply. Addressing this skill gap through education, training, and continuous professional development is vital to ensure that organizations can effectively assess and fortify their defenses. Moreover, audits must also address human factors within an organization, such as employee awareness, adherence to policies, and susceptibility to social engineering, as these remain significant attack vectors.
Future Innovations in Audit Automation
Looking ahead, the future of computer security auditing will likely see even greater integration of automation, AI, and predictive analytics. Continuous auditing, powered by AI and machine learning, will become the norm, moving beyond periodic assessments to provide real-time assurance. Blockchain technology might also play a role in creating immutable audit trails and verifiable integrity checks for critical systems. Furthermore, the development of intelligent compliance engines that can dynamically interpret regulatory changes and automatically assess an organization’s adherence will significantly streamline the audit process. These innovations promise to make auditing more efficient, more comprehensive, and more capable of protecting an organization’s digital assets against the sophisticated threats of tomorrow.
