In the rapidly evolving world of drone technology, innovation extends far beyond advancements in aerodynamics or camera resolution. It delves deep into the foundational mathematical and computational principles that ensure the reliability, security, and autonomy of unmanned aerial vehicles (UAVs). Among these critical underlying concepts lies the “primitive root,” a term originating from abstract algebra and number theory, which plays a surprisingly pivotal, albeit often unseen, role in securing drone operations and enabling advanced functionalities within the realm of Tech & Innovation.
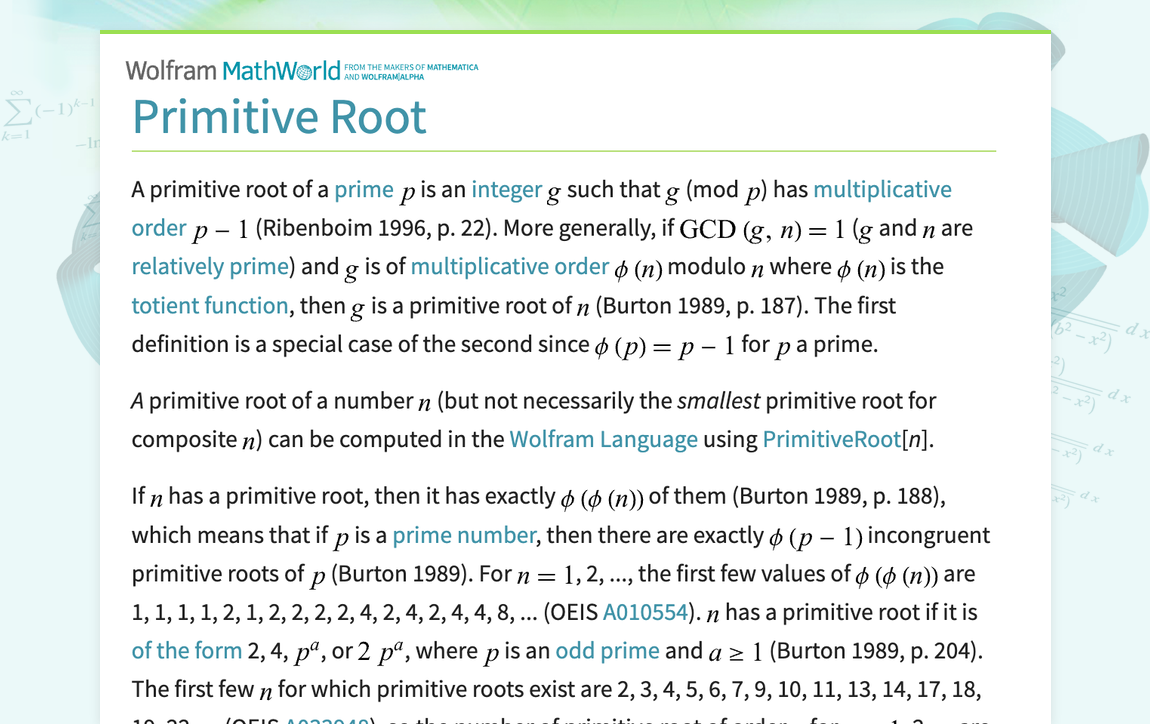
At its core, a primitive root is a specific type of integer within modular arithmetic, a system of arithmetic for integers, which considers the remainder. It’s about finding a generator for a set of numbers when performing operations modulo n. More formally, for a given modulus n, a primitive root g is an integer such that every number coprime to n (i.e., numbers that share no common factors with n other than 1) is congruent to a power of g modulo n. In simpler terms, if you take g and raise it to successive powers, then take the remainder when divided by n, you will generate all the numbers that are coprime to n before repeating. This cyclical property is what makes primitive roots so powerful in cryptographic applications, forming the bedrock of secure digital communication.
The Core of Secure Drone Communication
The modern drone ecosystem relies heavily on wireless communication—for control signals, telemetry data, live video feeds, and mission-critical data transmission. The integrity and confidentiality of these communications are paramount, not just for operational success but also for national security, privacy, and commercial interests. Here, the abstract concept of a primitive root transitions from theoretical mathematics into a practical tool for real-world security through its application in public-key cryptography.
Understanding Asymmetric Encryption
Most secure digital communications today utilize asymmetric encryption, also known as public-key cryptography. Unlike symmetric encryption, which uses a single secret key for both encryption and decryption, asymmetric encryption employs a pair of keys: a public key that can be shared openly, and a private key that must remain secret. Data encrypted with the public key can only be decrypted by the corresponding private key, and vice-versa for digital signatures. This ingenious system allows two parties, who have never met or shared a secret before, to establish a secure communication channel over an insecure medium.
The mathematical properties of primitive roots, particularly their ability to generate distinct sequences within a finite field, are fundamental to constructing these public-private key pairs. The difficulty of reversing these operations without the private key ensures the security of the system.
Diffie-Hellman and Key Exchange
One of the most prominent examples of primitive roots in action is the Diffie-Hellman key exchange protocol. This protocol, pioneered in the 1970s, allows two parties to securely establish a shared secret key over an insecure communication channel, without ever transmitting the secret itself. This shared secret can then be used to encrypt subsequent communications using a symmetric cipher, which is generally faster for bulk data.
The Diffie-Hellman protocol heavily relies on the properties of modular exponentiation and the discrete logarithm problem. A large prime number p and a primitive root g modulo p are chosen and made public. Each party then independently generates a secret random number (their private key), performs a modular exponentiation using the public g and p with their private key, and sends the result (their public key) to the other party. By combining the received public key with their own private key through another modular exponentiation, both parties arrive at the same shared secret key. The security of this method stems from the computational difficulty of calculating the private keys from the public values and the public g and p (the discrete logarithm problem), especially with very large numbers. Primitive roots ensure that the exponents generate a sufficiently diverse and unpredictable set of numbers within the modular group, making brute-force attacks infeasible for appropriately sized keys.
Primitive Roots in Action: Securing Drone Data
The application of primitive roots through cryptographic protocols like Diffie-Hellman is indispensable for the secure operation and data handling of modern drones.
Protecting Telemetry and Control

Every drone flight involves a constant exchange of data between the ground control station (GCS) and the UAV. This includes critical control commands (take-off, navigation, landing), real-time telemetry (altitude, speed, battery status, GPS coordinates), and sensor data. Unauthorized interception or manipulation of these signals could lead to catastrophic outcomes, ranging from loss of control and crashes to malicious hijacking or surveillance.
By implementing cryptographic key exchange mechanisms built on primitive roots, drone manufacturers and operators can establish robust, encrypted communication links. This ensures that:
- Confidentiality: Only the intended drone and GCS can understand the commands and telemetry.
- Integrity: Any attempt to alter commands or data during transmission will be detected.
- Authentication: Both the drone and the GCS can verify each other’s identity, preventing rogue drones or spoofed GCS signals.
This layer of security is vital for commercial drone operations, military applications, and even recreational flying in increasingly regulated airspace. It underpins the trust required for autonomous operations and beyond visual line of sight (BVLOS) flights.
Safeguarding Sensitive Imaging and Mapping Data
Drones equipped with advanced cameras and sensors are powerful tools for aerial imaging, surveying, mapping, inspection, and surveillance. The data collected—high-resolution photos, 4K video, thermal imagery, LiDAR scans, and multi-spectral data—often contains sensitive information. This could include proprietary commercial data, critical infrastructure details, or personal identifiable information.
Transmitting this vast amount of data from the drone to the ground, or storing it on onboard systems, requires stringent security measures. Primitive root-based cryptographic systems secure these data streams and storage. As live video feeds are streamed, they are often encrypted using keys derived through protocols that leverage primitive roots. When data is stored onboard, encryption keys for the storage device itself may be managed through similar secure key management practices. This ensures that even if a drone is lost, captured, or its data link is compromised, the sensitive information it carries remains protected from unauthorized access.
Beyond Security: Foundational Math in Drone AI and Autonomy
While the most direct application of primitive roots in drone tech innovation is undeniably in cryptography, their underlying mathematical principles reflect a broader reliance on foundational mathematics for advanced drone capabilities. The ability to model complex systems, ensure data integrity, and develop robust algorithms for artificial intelligence and autonomous decision-making all stem from deep mathematical understanding.
Algorithmic Efficiency and Integrity
The principles of modular arithmetic, which give rise to primitive roots, are also foundational to various algorithms that ensure efficiency and integrity in drone systems. From error correction codes that allow drones to recover from data packet loss in noisy environments, to hash functions used for data verification and blockchain-like distributed ledger technologies in drone swarm management, these mathematical constructs are pervasive. The properties that make primitive roots valuable for cryptography – their predictability within a defined cycle, yet unpredictability without knowing the key – are analogous to properties sought in other robust algorithms.
For instance, in autonomous flight, path planning algorithms, sensor fusion, and real-time decision-making systems rely on sophisticated mathematical models. While not directly employing primitive roots, the same rigorous approach to number theory and discrete mathematics informs the design of these algorithms to ensure they are computationally efficient, resistant to error, and perform predictably under varying conditions.

The Future of Trustworthy Drone Operations
As drones become more integrated into critical infrastructure, logistics, and public safety, the need for infallible security and robust autonomous capabilities will only grow. Innovations like AI follow mode, autonomous delivery, and large-scale drone swarms require not only advanced hardware but also highly secure and reliable software frameworks.
The continued research and application of mathematical concepts, including those related to primitive roots, will be crucial. This involves developing quantum-resistant cryptographic algorithms (as classical primitive root-based cryptography could be vulnerable to future quantum computers), enhancing the security of drone-to-drone communication in swarms, and creating verifiable autonomous decision-making processes. Understanding and leveraging these “primitive roots” of mathematical innovation allows engineers and researchers to build a future where drones operate with unparalleled security, reliability, and autonomy, pushing the boundaries of what’s possible in the skies.
