In the intricate world of computer networking, the term “node” serves as a fundamental building block. It’s a concept that underpins the very fabric of how devices communicate and share information. While seemingly simple, understanding the role and diversity of nodes is crucial for anyone delving into the complexities of network architecture, performance, and security. At its core, a network node is any active electronic device that is connected to a network and is capable of sending, receiving, or forwarding information. This definition is broad, encompassing a vast array of hardware that participates in the dynamic exchange of data.
The significance of nodes lies in their ability to contribute to the network’s functionality. Each node plays a part, whether it’s the origin of a data packet, a transit point, or the final destination. Without these individual components, the flow of information that we rely on daily – from browsing the web to sending emails and streaming videos – would be impossible. Moreover, the characteristics and configuration of each node directly influence the overall performance, reliability, and security of the network. Therefore, a comprehensive grasp of what constitutes a node, and the different types that exist, is paramount for effective network design and management.
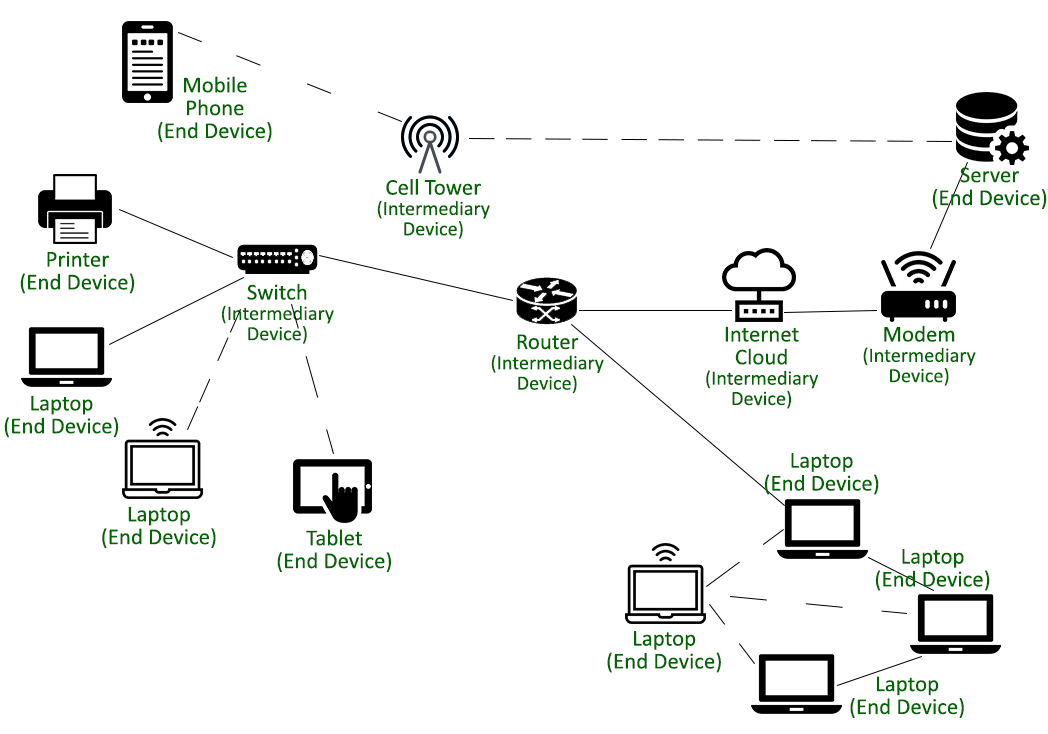
The Fundamental Role of Nodes in Network Communication
At the most basic level, a node is a point of connection within a network. Imagine a spiderweb; each intersection where a strand connects is analogous to a node. These connections facilitate the transmission of data between various points. A node isn’t just a passive endpoint; it actively participates in the network’s operations. This active participation can manifest in several ways, depending on the type of node and its function.
Data Transmission and Reception
The primary function of most nodes is to transmit and receive data. When you send an email, your computer (a node) creates a data packet containing your message and the recipient’s address. This packet travels through the network, potentially passing through multiple other nodes, until it reaches the destination computer, which then receives and displays the email. Similarly, when you request a webpage, your browser sends a request (a data packet) to a web server (another node), which then sends the webpage data back to your browser.
Data Forwarding
Many nodes within a network act as intermediaries, forwarding data from one point to another. Routers and switches are prime examples of such nodes. They don’t necessarily originate or terminate the data themselves but play a critical role in directing traffic along the most efficient path. Without these forwarding nodes, data packets would be lost or would take circuitous and slow routes, severely degrading network performance.
Network Services and Management
Beyond simple data transfer, some nodes are dedicated to providing and managing network services. Servers, for instance, are nodes that provide resources and services to other nodes on the network. This can include file storage, application hosting, email services, or website hosting. Domain Name System (DNS) servers are another crucial type of node, responsible for translating human-readable domain names (like google.com) into machine-readable IP addresses. Network management nodes monitor the health and performance of the network, identifying and resolving issues.
The Interconnected Ecosystem
The collective interaction of these diverse nodes forms a complex and dynamic ecosystem. The way these nodes are interconnected, their individual capabilities, and the protocols they employ all contribute to the overall network’s robustness and efficiency. A failure in one node can have ripple effects, potentially disrupting communication for other connected devices. Conversely, the addition of new, powerful nodes can enhance the network’s capacity and introduce new functionalities.
Diverse Types of Network Nodes
The term “node” is a generic descriptor, and the specific type of node can vary significantly based on its role and function within the network. Understanding these different categories helps in appreciating the layered complexity of modern networking.
End Devices
These are the devices that users directly interact with and that initiate or terminate network communication.
Computers and Mobile Devices
Your personal computer, laptop, smartphone, and tablet are all common examples of end-device nodes. They connect to the network (either wired or wirelessly) to access resources, send and receive data, and run applications. Their processing power, memory, and network interface cards (NICs) determine their capabilities as network participants.
Peripherals and IoT Devices
Beyond personal computing devices, a growing array of peripherals and Internet of Things (IoT) devices also function as nodes. Network printers, smart TVs, gaming consoles, security cameras, and smart home devices (like thermostats and smart speakers) all connect to the network to perform their specific functions. The proliferation of IoT devices has significantly expanded the number and variety of nodes within contemporary networks.
Network Infrastructure Devices
These are the devices that form the backbone of the network, enabling connectivity and managing data flow between end devices and other network segments.
Routers
Routers are perhaps the most recognizable network infrastructure nodes. Their primary function is to connect different networks together (e.g., your home network to the internet) and to direct data packets between these networks based on IP addresses. Routers use routing tables to determine the best path for data to travel, ensuring efficient and timely delivery.
Switches
Switches operate at a lower level than routers, primarily connecting multiple devices within a single network (e.g., all the computers in an office on the same Local Area Network or LAN). They use MAC addresses to forward data frames directly to the intended recipient device, rather than broadcasting them to all devices on the network, which makes them more efficient than older hubs.
Hubs
While largely superseded by switches, hubs were an earlier form of network device that connected multiple devices in a network. Unlike switches, hubs simply broadcast incoming data to all connected devices, regardless of the intended recipient. This broadcast nature made them inefficient and prone to collisions, which can slow down network performance.
Modems
Modems are essential for connecting a local network to the broader internet. They modulate digital signals from your network into analog signals that can be transmitted over telephone lines or cable infrastructure, and demodulate incoming analog signals back into digital data.
Servers
Servers are powerful computers that provide resources, data, services, or programs to other computers, known as clients, over a network.
File Servers

These nodes store and manage files, allowing multiple users to access and share documents, spreadsheets, and other data centrally.
Web Servers
Web servers host website content and respond to requests from web browsers, delivering webpages and associated media to users.
Application Servers
These servers run specific applications that can be accessed by multiple clients, such as enterprise resource planning (ERP) systems or customer relationship management (CRM) software.
Database Servers
Dedicated nodes for storing and managing large volumes of structured data, enabling efficient querying and retrieval by client applications.
Wireless Access Points (WAPs)
WAPs act as bridges between a wireless network and a wired network. They allow wireless devices to connect to the network by broadcasting a Wi-Fi signal.
Node Connectivity and Network Topologies
The way nodes are interconnected is defined by the network topology, which dictates the physical or logical layout of the network. The choice of topology significantly impacts network performance, scalability, and fault tolerance.
Bus Topology
In a bus topology, all nodes are connected to a single, central cable or backbone. Data is transmitted along this bus, and all nodes receive the data, but only the intended recipient processes it. This topology is simple and inexpensive but has limitations in terms of scalability and fault tolerance; a break in the backbone can render the entire network inoperable.
Star Topology
In a star topology, all nodes are connected individually to a central hub or switch. This is one of the most common topologies in modern networks, especially in LANs. If one connection fails, only that specific node is affected, and the rest of the network continues to function. The central device is a single point of failure, but redundancy can be built into the central device.
Ring Topology
In a ring topology, each node is connected to exactly two other nodes, forming a closed loop or ring. Data travels in one direction around the ring, passing through each node until it reaches its destination. While it can offer good performance, a single node failure or cable break can disrupt the entire network.
Mesh Topology
A mesh topology involves multiple interconnections between nodes. In a full mesh, every node is directly connected to every other node. This provides a high degree of redundancy and fault tolerance, as data can take multiple paths to reach its destination. However, it is complex and expensive to implement due to the sheer number of connections required.
Hybrid Topology
Many real-world networks employ a hybrid topology, combining elements of two or more basic topologies to leverage their respective strengths and mitigate their weaknesses. For example, a network might use a star topology for individual office floors and connect these stars together using a bus or ring backbone.
The Importance of Nodes in Network Performance and Security
The performance and security of any computer network are intrinsically linked to the characteristics and behavior of its constituent nodes. Understanding these relationships is vital for optimizing network operations.
Network Performance
The speed and efficiency of data transfer are heavily influenced by the capabilities of the nodes involved. High-performance end devices with fast processors and ample memory can generate and process data more quickly. Similarly, robust infrastructure nodes like high-speed routers and switches can handle larger volumes of traffic with minimal latency. The presence of bottlenecks – nodes that cannot keep up with the data flow – can severely degrade overall network performance, leading to slow loading times and dropped connections. Network monitoring tools often focus on node performance metrics like CPU utilization, memory usage, and network interface throughput to identify and address such issues.
Network Security
Nodes are both the targets and the potential points of entry for cyber threats. Malicious actors often attempt to compromise nodes to gain access to sensitive data, disrupt network operations, or use them as launchpads for further attacks.
Vulnerabilities in Nodes
Each node, especially end devices running various operating systems and applications, can have vulnerabilities that attackers can exploit. Outdated software, weak passwords, and misconfigurations are common entry points. For instance, an unpatched server node could be exploited by malware to install backdoors, allowing attackers persistent access.
Security Measures at the Node Level
Implementing robust security measures at the node level is crucial. This includes:
- Strong Authentication: Using complex passwords, multi-factor authentication (MFA), and role-based access control to ensure only authorized users and devices can access network resources.
- Software Updates and Patching: Regularly updating operating systems and applications on all nodes to fix known vulnerabilities.
- Firewalls: Configuring firewalls on individual nodes or at network perimeters to block unauthorized incoming and outgoing traffic.
- Antivirus and Anti-malware Software: Installing and maintaining up-to-date security software on end devices to detect and remove malicious programs.
- Network Segmentation: Dividing the network into smaller, isolated segments to limit the lateral movement of threats if one segment is compromised.
The Role of Network Devices in Security
Infrastructure nodes like routers and firewalls play a critical role in enforcing security policies, filtering malicious traffic, and preventing unauthorized access. Intrusion detection and prevention systems (IDPS) often monitor traffic flowing through these nodes to identify and block suspicious activity.
In conclusion, the concept of a node is central to understanding computer networking. From the simplest end devices to the most complex servers and routers, each node is a vital component that contributes to the network’s functionality, performance, and security. As networks continue to evolve and become more complex, a solid understanding of nodes and their diverse roles will remain an indispensable asset for navigating the digital landscape.
