In the intricate landscape of modern web development and distributed systems, encountering a “CORS error” is a common rite of passage for developers. More than just an annoying roadblock, a CORS error signals a crucial security mechanism at play, designed to protect users and data across the internet. Understanding Cross-Origin Resource Sharing (CORS) is fundamental for anyone building sophisticated web applications, integrating APIs, or innovating with data-driven platforms, as it directly impacts how different parts of a complex system can securely communicate.
The Fundamental Principle of Web Security: The Same-Origin Policy
To fully grasp CORS, one must first understand the bedrock of web security it seeks to augment: the Same-Origin Policy (SOP). Introduced decades ago, the SOP is a critical security feature implemented by all modern web browsers. It dictates that a web page can only request resources (like images, stylesheets, scripts, or data via AJAX) from the same origin from which the page itself was loaded. This policy is paramount for preventing malicious scripts from one website (origin) from interacting with sensitive data on another website (different origin).
Understanding Origins
An “origin” is defined by a combination of three components: the protocol, the host (domain), and the port. For example:
https://www.example.com:443http://sub.anothersite.org:8080
Two URLs are considered to have the same origin if and only if all three components (protocol, host, port) are identical. If any one of these components differs, they are considered different origins or cross-origins.
The Policy’s Purpose and Limitations
The primary purpose of the Same-Origin Policy is to isolate potentially malicious documents. Without it, a rogue script embedded in one tab could, for instance, make requests to a banking site opened in another tab, read your private data, and send it to a third-party server. The SOP acts as a browser-enforced firewall, preventing such unauthorized interactions.
However, as web applications grew more complex, and architectures shifted towards microservices, APIs, and single-page applications (SPAs) that often need to fetch data from different domains (e.g., an application hosted on app.example.com needing data from an API on api.example.com or data.thirdparty.com), the SOP became a significant constraint. While essential for security, it restricted legitimate cross-origin communication, giving rise to the need for a controlled way to bypass it. This is precisely where CORS comes into play.
Introducing CORS: Bridging the Cross-Origin Divide
Cross-Origin Resource Sharing (CORS) is a W3C standard that provides a mechanism for web browsers to allow controlled access to resources from a different origin. Instead of completely blocking all cross-origin requests, CORS introduces a set of HTTP headers that enable servers to explicitly specify which origins are permitted to access their resources. This allows servers to grant specific permissions, mitigating the strictness of the SOP while maintaining a strong security posture.
When a browser makes a cross-origin HTTP request, it doesn’t just send the request; it first checks if the server allows cross-origin access from the requesting origin. If the server explicitly grants permission via CORS headers, the browser proceeds with the request. If not, the browser blocks the response and reports a CORS error in the console. It’s crucial to understand that the server does receive the request; the browser prevents the client-side JavaScript from accessing the response due to the security policy.
The CORS Mechanism: Preflight and Simple Requests
CORS operations typically fall into two categories:
Simple Requests
A request is considered “simple” if it meets certain criteria:
- Method is
GET,HEAD, orPOST. - Only certain “safe” headers are used (e.g.,
Accept,Accept-Language,Content-Language,Content-Typewith valuesapplication/x-www-form-urlencoded,multipart/form-data, ortext/plain). - No event listeners are registered on any
XMLHttpRequestUploadobject used in the request. - No
ReadableStreamobject is used in the request.
For simple requests, the browser sends the cross-origin request directly, including an Origin header indicating the domain of the requesting page. The server then responds with an Access-Control-Allow-Origin header (among others) to indicate whether the requesting origin is allowed. If the Origin matches an allowed origin (or is * for any origin), the browser permits the application to access the response.
Preflight Requests
Requests that do not meet the criteria for simple requests (e.g., using PUT or DELETE methods, or custom headers, or Content-Type: application/json) are considered “preflighted”. Before sending the actual request, the browser first sends an OPTIONS request to the server, known as a “preflight request.” This OPTIONS request includes headers like Access-Control-Request-Method and Access-Control-Request-Headers, informing the server about the intended method and headers of the actual request.
The server’s response to the preflight request must include CORS-specific headers, such as:
Access-Control-Allow-Origin: Specifies which origins are allowed to make requests.Access-Control-Allow-Methods: Lists the HTTP methods allowed for cross-origin requests.Access-Control-Allow-Headers: Lists the HTTP headers allowed in the actual request.Access-Control-Max-Age: Indicates how long the results of the preflight request can be cached, reducing subsequent preflight requests.
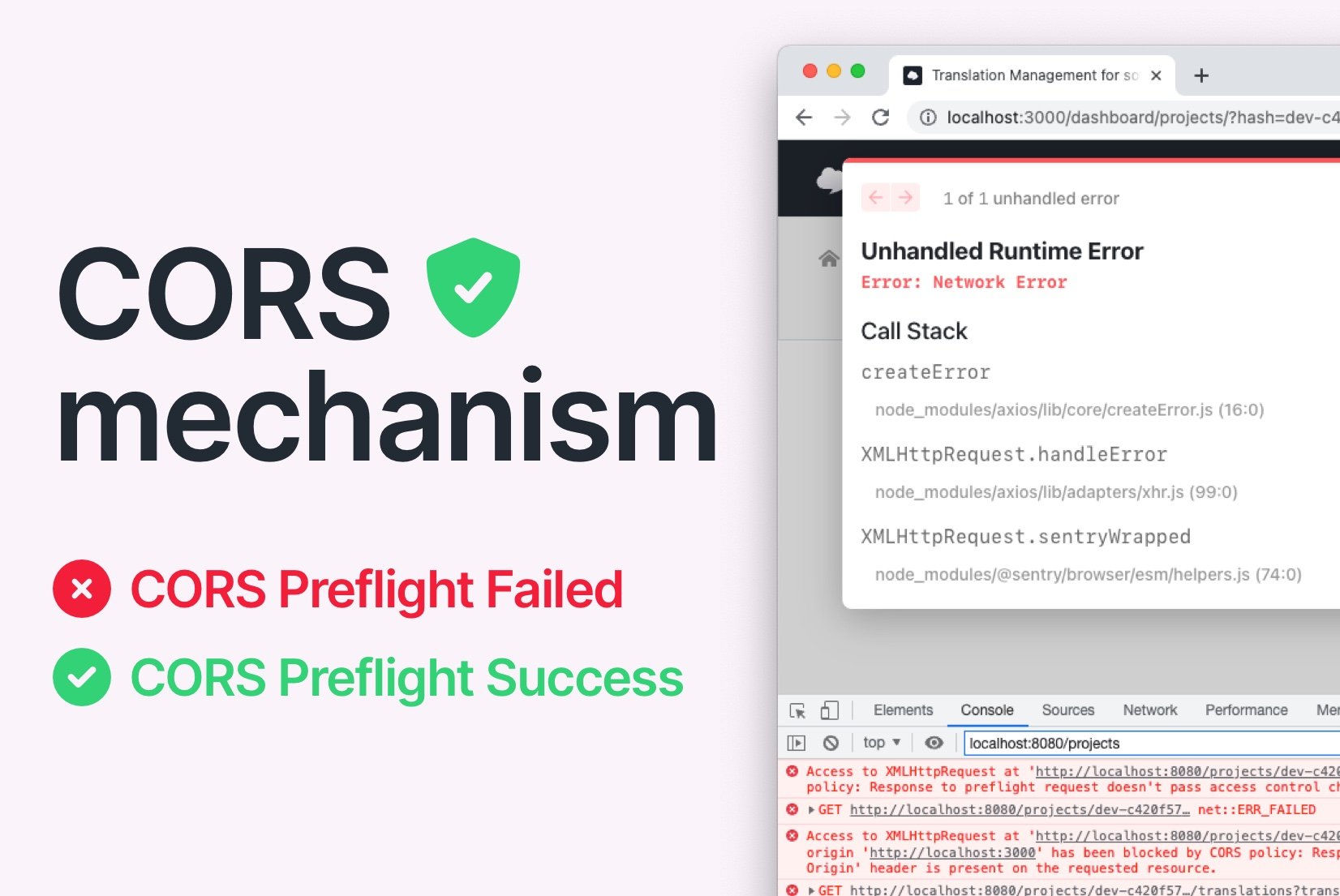
If the server’s response to the preflight request indicates that the actual request is permitted, the browser proceeds to send the actual request. If not, or if the server doesn’t respond with the necessary CORS headers, the browser blocks the request, resulting in a CORS error.
Key HTTP Headers in CORS
Several HTTP headers are central to the CORS mechanism:
- Request Headers (sent by browser):
Origin: Indicates the origin from which the cross-origin request was initiated.Access-Control-Request-Method: (Preflight only) Indicates the HTTP method that will be used in the actual request.Access-Control-Request-Headers: (Preflight only) Indicates the custom headers that will be sent in the actual request.
- Response Headers (sent by server):
Access-Control-Allow-Origin: The most crucial header. Specifies which origin(s) are permitted to access the resource. Can be*for any origin, or a specific origin likehttps://client.example.com.Access-Control-Allow-Methods: Specifies the allowed HTTP methods for cross-origin requests.Access-Control-Allow-Headers: Specifies which custom headers are allowed in the actual request.Access-Control-Allow-Credentials: Indicates whether the browser should send cookies or HTTP authentication credentials with the request. If true,Access-Control-Allow-Origincannot be*.Access-Control-Expose-Headers: Specifies which non-simple response headers are safe to expose to the browser’s JavaScript.Access-Control-Max-Age: The maximum time (in seconds) for which the results of a preflight request can be cached by the browser.
Diagnosing and Debugging CORS Errors
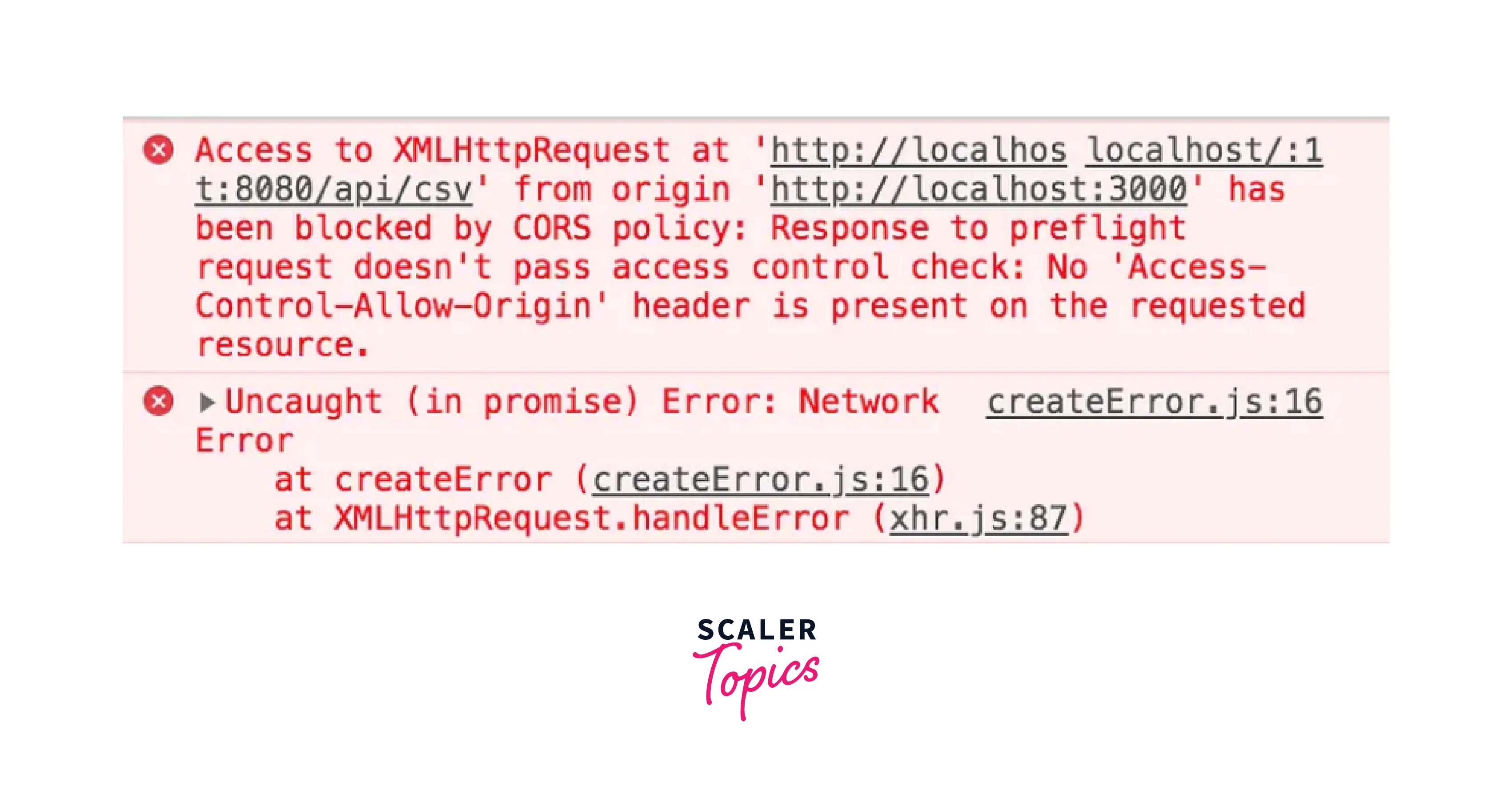
A CORS error manifests itself typically in the browser’s developer console. Common messages might include:
Cross-Origin Request Blocked: The Same Origin Policy disallows reading the remote resource... Reason: CORS header 'Access-Control-Allow-Origin' missing.Cross-Origin Request Blocked: The Same Origin Policy disallows reading the remote resource... Reason: CORS header 'Access-Control-Allow-Origin' does not match 'null'.Response to preflight request doesn't pass access control check: No 'Access-Control-Allow-Origin' header is present on the requested resource.The 'Access-Control-Allow-Origin' header has a value 'https://wrong-domain.com' that is not equal to the supplied origin.
Common Scenarios Leading to CORS Issues
- Missing or Incorrect
Access-Control-Allow-OriginHeader: This is the most frequent cause. The server is not sending this header, or its value does not include the origin of the requesting client. - Incorrect
Access-Control-Allow-MethodsorAccess-Control-Allow-Headers: For preflighted requests, if the server doesn’t explicitly allow the requested method (e.g.,DELETE) or custom headers, the preflight will fail. - Credentialed Requests with
*Origin: IfAccess-Control-Allow-Credentialsistrue,Access-Control-Allow-Origincannot be*. It must specify a particular origin. - Misconfigured Reverse Proxies or CDNs: Sometimes, a proxy or CDN in front of the actual server might strip or alter CORS headers, leading to errors.
- Local Development vs. Production: Developers often encounter CORS errors during local development (
http://localhost:port) when interacting with an API hosted on a different domain. Production environments also face issues when client and API domains diverge.
Strategies for Resolving CORS Errors
Resolving CORS errors primarily involves configuring the server that hosts the requested resource. The browser is merely enforcing a security policy; it cannot be configured to bypass CORS for specific requests.
Server-Side Configuration: The Primary Solution
The most robust and secure way to resolve CORS errors is to correctly configure the server-side application or web server (e.g., Nginx, Apache, Node.js Express, Python Flask, Java Spring Boot) to include the necessary CORS headers in its responses.
-
Allow Specific Origins: The safest approach is to explicitly list the domains that are allowed to make cross-origin requests.
Access-Control-Allow-Origin: https://yourclientapp.comFor multiple allowed origins, the server must dynamically set the header based on the incoming
Originheader.// Example logic (Node.js Express) app.use((req, res, next) => { const allowedOrigins = ['https://client1.com', 'https://client2.com']; const origin = req.headers.origin; if (allowedOrigins.includes(origin)) { res.setHeader('Access-Control-Allow-Origin', origin); } res.setHeader('Access-Control-Allow-Methods', 'GET, POST, PUT, DELETE, OPTIONS'); res.setHeader('Access-Control-Allow-Headers', 'Content-Type, Authorization'); res.setHeader('Access-Control-Max-Age', '86400'); // Cache preflight for 24 hours if (req.method === 'OPTIONS') { return res.sendStatus(200); } next(); }); -
Allow All Origins (Less Secure): For public APIs or during development, allowing all origins (
*) might seem convenient, but it reduces security.Access-Control-Allow-Origin: *Caution: Do not use
*withAccess-Control-Allow-Credentials: true. -
Allow Specific Methods and Headers: Ensure that all HTTP methods (GET, POST, PUT, DELETE, PATCH, OPTIONS) and custom headers (e.g.,
Authorization,X-Custom-Header) that your client application intends to use are explicitly allowed by the server.
Development-Time Proxies and Alternatives
During local development, setting up a full CORS configuration on the backend might be cumbersome.
- Development Proxy: Many frontend development tools (like Webpack Dev Server, Create React App) offer proxy configurations. The frontend development server acts as an intermediary, making requests to the backend API on the same origin, thus bypassing browser CORS restrictions. The proxy then forwards these requests to the actual cross-origin API.
- Browser Extensions (for local testing only): Some browser extensions can temporarily disable or manipulate CORS headers. These are never for production use and should only be used for quick local debugging.

Security Considerations and Best Practices
While CORS enables valuable cross-origin communication, it must be implemented carefully.
- Be Specific with Origins: Always prefer specifying exact origins in
Access-Control-Allow-Originrather than using*, especially for sensitive data. - Limit Allowed Methods and Headers: Only permit the HTTP methods and headers that your client applications genuinely need.
- Understand
Access-Control-Allow-Credentials: Whentrue, it allows cookies and HTTP authentication to be sent with cross-origin requests, but it mandates a specific origin (not*). - Regular Audits: As your application evolves, periodically review your CORS configurations to ensure they remain secure and only allow necessary access.
In the realm of Tech & Innovation, where distributed systems, microservices, and sophisticated frontends are the norm, a robust understanding and correct implementation of CORS are not just about fixing errors but about designing secure, interoperable, and scalable applications. It’s a critical enabler for modern web architecture, ensuring that innovation can thrive without compromising user security.
