The intricate world of embedded systems, particularly those powered by OpenWrt, serves as a crucial backbone for many advanced technologies falling under the broad umbrella of Tech & Innovation. From securing IoT devices to optimizing communication for autonomous systems, understanding the nuances of network traffic is paramount. Packet capture, a fundamental diagnostic and analytical technique, allows developers and researchers to peer into the very data streams that define device interactions. Within the OpenWrt repository, the tools and libraries enabling this capability are carefully integrated, reflecting a modular and efficient design philosophy essential for resource-constrained environments.
The Foundation of Network Insight in OpenWrt
At its core, OpenWrt is a highly customizable Linux distribution tailored for embedded devices, primarily routers and gateways. Its architecture is designed for efficiency, offering a package management system (opkg) that allows users to install software components dynamically. When it comes to packet capture, the underlying mechanisms are deeply rooted in the Linux kernel and specific user-space utilities.
Decoding OpenWrt’s Architecture for Network Operations
OpenWrt’s structure, like many Linux systems, separates kernel-level functionalities from user-space applications. Packet capture begins at the kernel level, where network interfaces receive and transmit data. The kernel must be configured to allow “promiscuous mode” operation for an interface, meaning it captures all packets regardless of their destination MAC address. This capability is inherent in the network drivers themselves and controlled via ioctl system calls from user-space applications.
The netfilter framework, a highly modular packet filtering and manipulation system in the Linux kernel, is another critical component. While netfilter is primarily known for its firewall capabilities (e.g., iptables), it also provides hooks into various points of the network stack where packets can be inspected or redirected. Specialized modules can tap into these hooks to provide raw access to network data, which is then passed up to user-space libraries.
Within the OpenWrt source repository, the kernel configuration files (target/linux/*/config-*) specify which kernel modules and options are compiled into the firmware. For packet capture, ensuring that necessary network drivers are present and that core networking features are enabled is the first step. More specifically, the presence of modules related to network interface drivers (drivers/net) and the netfilter framework (net/netfilter) are foundational. These are not packet capture files themselves, but the essential prerequisites that enable the functionality.
The Role of Kernel Modules in Packet Interception
True packet interception, beyond the basic promiscuous mode, often relies on specific kernel modules. The most prominent example is the mechanism that libpcap (Packet CAPture library) uses. libpcap leverages a raw socket interface or, more commonly, a kernel-level packet filter to efficiently capture packets. This involves the Linux Packet Socket (PACKET) mechanism, which allows user-space programs to receive and send raw packets directly from and to the network device drivers.
When compiling OpenWrt, the configuration options within make menuconfig related to Kernel modules -> Network Support and Kernel modules -> Network Devices are crucial. While there isn’t a single “packet capture module” per se, the framework for it is baked into the kernel’s network stack. The CONFIG_PACKET option, for instance, enables the PF_PACKET family, which is essential for raw socket operations used by libpcap. The actual files residing in the kernel source (linux/net/packet/) define this crucial functionality.
Core Utilities and Their Repository Footprint
While the kernel provides the fundamental ability to access raw packets, user-space applications are needed to collect, filter, and present this data in an understandable format. In OpenWrt, as in most Linux environments, this is primarily handled by tcpdump and its underlying library, libpcap.
tcpdump: The De Facto Standard
tcpdump is the quintessential command-line packet analyzer. Its ubiquity makes it the first choice for network diagnostics on embedded systems. In the OpenWrt repository, tcpdump is found as a separate package. You’ll typically find its source code under package/network/utils/tcpdump. This directory contains the Makefile for compiling tcpdump, defining its dependencies, and specifying how it integrates into the OpenWrt build system.
The Makefile for tcpdump points to the upstream source code, often fetched from a designated URL. It also defines compilation flags specific to OpenWrt’s cross-compilation environment and ensures that tcpdump is built with appropriate features enabled for the target architecture. The tcpdump package might also include patches (patches/) to adapt the upstream code for OpenWrt’s specific kernel versions or to fix issues.
When tcpdump is installed, it resides in the filesystem of the OpenWrt device, typically in /usr/sbin/tcpdump. Running tcpdump from the command line on an OpenWrt device allows an administrator or developer to monitor network traffic in real-time, diagnose connectivity issues, or analyze protocol interactions, which is invaluable for debugging innovative prototypes, enhancing the security of IoT deployments, or optimizing data flow for autonomous drone systems.
libpcap and Its Dependencies
tcpdump does not directly interact with the kernel’s raw packet interface. Instead, it relies on libpcap, the Packet CAPture library. libpcap provides a high-level, platform-independent interface for capturing network packets. This abstraction is critical for maintaining compatibility across different operating systems and kernel versions.
In the OpenWrt repository, libpcap also exists as its own package, usually located at package/libs/libpcap. Similar to tcpdump, this directory contains the Makefile for libpcap, which specifies how to download, compile, and install the library. The libpcap Makefile ensures that the library is built against the OpenWrt toolchain and includes any necessary kernel headers. It also manages any specific patches (patches/) required for OpenWrt compatibility.
When libpcap is installed, its shared library files (e.g., lib/libpcap.so*) are placed on the OpenWrt device. Any application that wishes to perform packet capture, including tcpdump and potentially custom applications for specialized purposes (like a lightweight intrusion detection system for an edge device), links against libpcap. Its presence is fundamental for any advanced network analysis or diagnostic tool.
Alternative Tools and Specialized Packages
While tcpdump and libpcap are the primary players, OpenWrt’s modularity allows for other related packages:
ettercap: A comprehensive suite for man-in-the-middle attacks, which naturally involves advanced packet sniffing. ItsMakefileand source integration would be found underpackage/network/utils/ettercapor a similar path. While more focused on offensive security, its capabilities often draw uponlibpcap.ngrep: A networkgreptool that allows searching for patterns in network traffic. It also relies onlibpcapand would have its package definition in a similar structure totcpdump.- Custom Applications: Developers often write custom C/C++ applications that link directly against
libpcapfor highly specific packet processing tasks. For example, a specialized sensor gateway might need to capture specific types of packets to detect anomalies or trigger actions. These applications would be built as custom OpenWrt packages, with theirMakefileexplicitly declaringlibpcapas a dependency.
These additional tools expand the utility of packet capture within OpenWrt, enabling a broader range of applications in network security, performance monitoring, and advanced diagnostics crucial for emerging technologies.
Building and Integrating Packet Capture Capabilities
Integrating packet capture tools into an OpenWrt firmware image requires navigating the OpenWrt build system, a powerful set of Makefiles and scripts that orchestrate the cross-compilation process.
Navigating the OpenWrt Build System
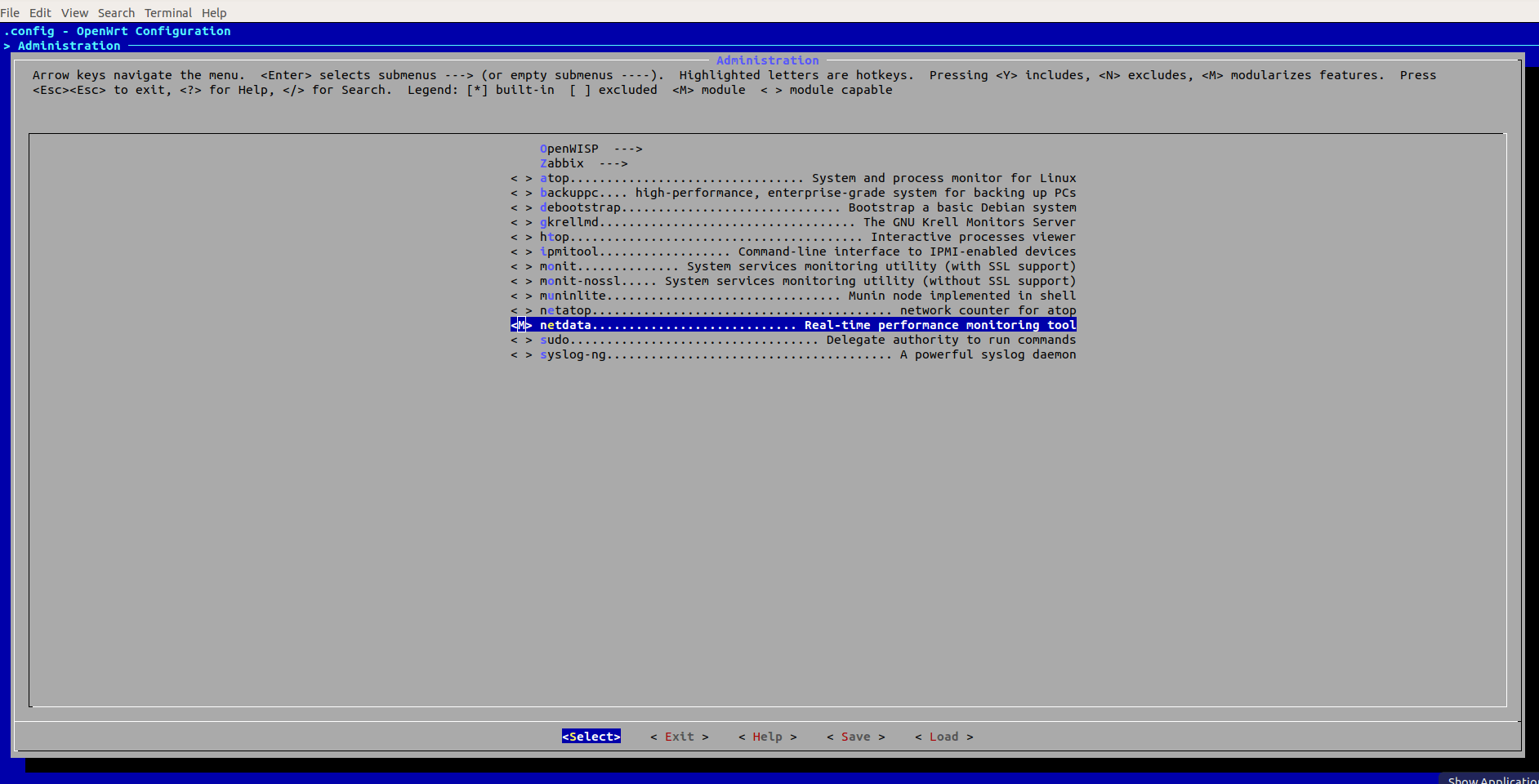
The OpenWrt build system is located at the root of the OpenWrt source tree. To enable packet capture, one typically executes make menuconfig and selects the tcpdump and libpcap packages under Network -> Utilities and Libraries respectively. This action modifies the .config file at the root of the build directory, instructing the build system to compile these packages.
When make is run, the build system traverses the package/ directories. For tcpdump and libpcap, it executes the Makefile within their respective package directories. These Makefiles handle:
- Downloading Source: Fetching the upstream tarball for the software.
- Patching: Applying any OpenWrt-specific patches.
- Configuration: Running
configurescripts (if applicable) with appropriate cross-compilation flags and OpenWrt-specific paths. - Compilation: Compiling the source code using the OpenWrt toolchain.
- Installation: Staging the compiled binaries and libraries into the
staging_dirand finally into the target firmware image.
Understanding this flow is crucial for developers who need to customize packet capture tools, perhaps by enabling specific features or adding custom filters directly into the firmware.
Configuration and Target-Specific Considerations
OpenWrt supports a vast array of hardware targets, from low-power MIPS-based routers to more powerful ARM-based single-board computers. The specific capabilities and performance of packet capture can vary significantly between these targets.
- Kernel Configuration: As mentioned, the kernel configuration (
target/linux/*/config-*) is vital. Some low-resource devices might have minimal kernel features enabled by default, potentially requiring manual intervention to enableCONFIG_PACKETor ensure proper network driver support for promiscuous mode. - Resource Constraints: Packet capture, especially heavy traffic capture, can be resource-intensive, consuming CPU cycles and memory. Developers must consider the target device’s RAM and flash storage limitations. For instance, capturing to disk (
-woption intcpdump) might be limited by the available flash write endurance or storage space. - Performance Optimization: For high-throughput applications, selecting an OpenWrt target with a capable CPU and sufficient RAM is paramount. Compiling
tcpdumpwith specific optimizations or using custom-built capture applications that are highly optimized for a particular data stream can improve performance.
These considerations are not merely technical details but strategic decisions in designing innovative solutions where embedded systems play a critical role, from high-speed data acquisition for remote sensing to real-time analysis for autonomous vehicle communication.
Applications in Modern Tech & Innovation
The ability to perform packet capture within OpenWrt extends far beyond simple network debugging. It forms a cornerstone for various advanced applications in Tech & Innovation, providing invaluable insights into device behavior, security posture, and communication efficiency.
Securing IoT and Edge Devices
OpenWrt-powered devices often serve as critical nodes in IoT ecosystems or as edge computing gateways. Packet capture is an indispensable tool for their security.
- Vulnerability Assessment: By capturing traffic, security researchers can identify unencrypted communications, weak authentication protocols, or unusual outbound connections that signal potential malware or data exfiltration.
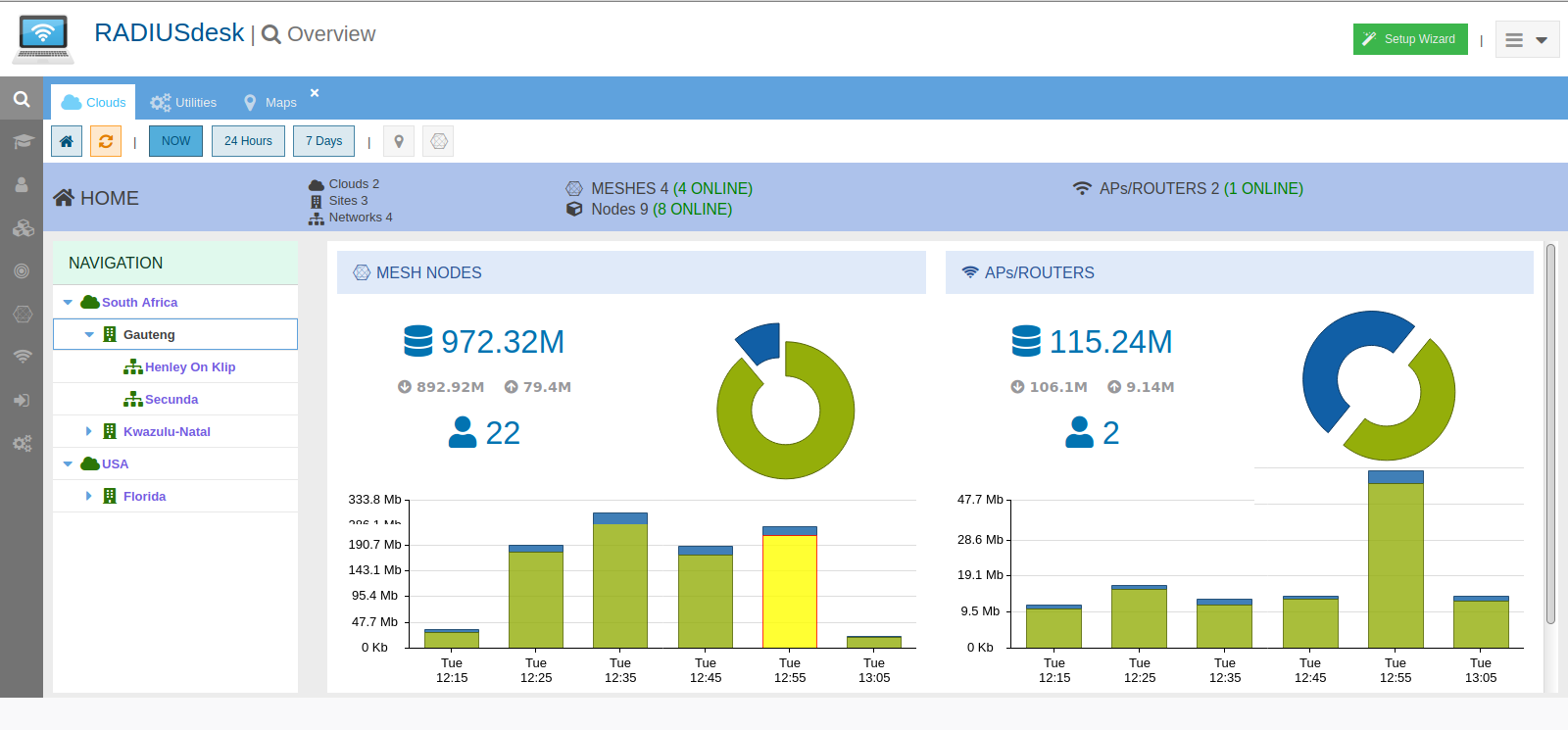
- Intrusion Detection: Custom scripts or lightweight intrusion detection systems (IDS) can be developed to analyze captured packets for known attack signatures or anomalous behavior, such as a device attempting to communicate with an unauthorized server.
- Compliance Monitoring: For industrial IoT (IIoT) or sensitive data environments, packet capture provides a verifiable log of network interactions, crucial for regulatory compliance and forensic analysis after a security incident. This proactive and reactive security capability is vital for trust in smart homes, smart cities, and critical infrastructure.
Optimizing Communication for Autonomous Systems
Autonomous systems, whether drones, robots, or self-driving vehicles, rely heavily on robust and efficient wireless communication. OpenWrt devices, acting as communication relays or onboard controllers, can leverage packet capture to fine-tune these systems.
- Latency Analysis: By capturing packets at various points in the communication chain (e.g., between drone and ground station, or between internal drone components), developers can precisely measure latency and identify bottlenecks that could impact real-time control or mission-critical data transfer for AI follow mode or autonomous flight.
- Protocol Validation: Ensuring that custom or standard communication protocols are operating as expected, with correct packet sequencing and error handling, is critical. Packet capture allows for deep inspection of these exchanges.
- Bandwidth Utilization: Monitoring packet sizes and frequencies helps optimize bandwidth usage, especially in contested spectrum environments or when dealing with limited wireless data links, directly impacting the efficiency of data streaming for remote sensing or mapping applications.
Enhancing Remote Sensing Data Pipelines
Remote sensing, often performed by drones or fixed sensor platforms, generates vast amounts of data. OpenWrt devices in the data pipeline can use packet capture to ensure data integrity and efficient flow.
- Data Integrity Verification: By capturing packets containing sensor data, developers can verify that data is transmitted without corruption or loss, crucial for accurate mapping and environmental monitoring.
- Throughput Monitoring: Packet capture helps monitor the actual data throughput from sensors to storage or processing units, identifying any slowdowns that could affect the timely availability of remote sensing data.
- Troubleshooting Data Link Issues: For high-resolution imaging or complex sensor arrays, dropped packets or intermittent connectivity can severely impact data quality. Packet capture provides the granular detail needed to diagnose and resolve these elusive network issues.
Diagnostics for Next-Generation Network Architectures
As network architectures evolve towards 5G, software-defined networking (SDN), and edge computing, OpenWrt devices often play a role as micro-gateways, access points, or specialized controllers. Packet capture remains a fundamental diagnostic tool in these complex environments.
- SDN Flow Verification: In SDN deployments, where network behavior is programmed, packet capture helps verify that traffic flows are correctly established and routed according to the defined policies.
- Edge Computing Performance: Analyzing traffic at the edge helps understand the load on edge devices and optimize data processing and offloading strategies.
- Wireless Mesh Network Analysis: For innovative mesh networks, packet capture on individual OpenWrt nodes can reveal routing inefficiencies, interference issues, or client connectivity problems, contributing to more robust and reliable network solutions.
The files and configurations within the OpenWrt repository that enable packet capture are not just technical components; they are empowering tools that allow engineers and innovators to understand, secure, and optimize the underlying communication fabric of the most cutting-edge technologies. From the kernel drivers that provide raw access to network data to the user-space utilities that process and present it, these elements are essential for fostering continued progress in the realm of Tech & Innovation.

