The Crucial Role of Hardware Security Modules (HSMs) in Flight Technology
In the rapidly evolving landscape of Unmanned Aerial Vehicles (UAVs) and advanced flight systems, the acronym “HSM” holds significant weight, particularly in the realm of cybersecurity and system integrity. For those deeply entrenched in the intricacies of flight technology, HSM stands for Hardware Security Module. Far from a simple accessory, an HSM is a specialized, tamper-resistant physical device designed to protect cryptographic keys and perform cryptographic operations within a secure, isolated environment. Its integration into flight technology is becoming indispensable, addressing critical vulnerabilities ranging from data interception to malicious control takeover, thereby solidifying the reliability and trustworthiness of airborne operations.

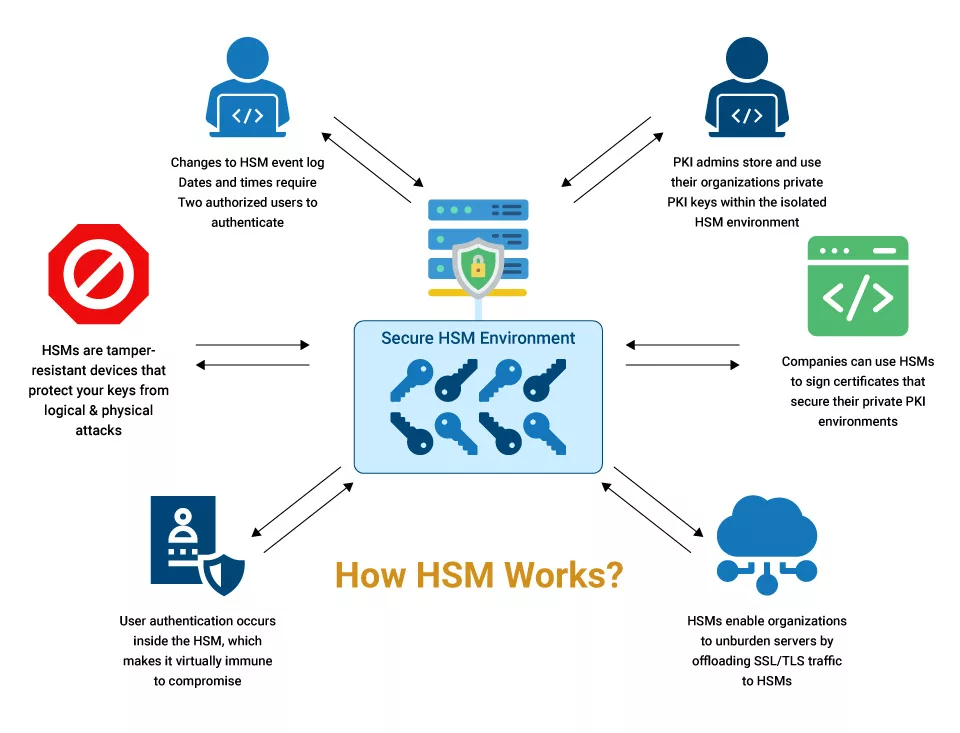
Defining the Hardware Security Module
At its core, a Hardware Security Module is a dedicated cryptographic processor that manages and protects digital keys for strong authentication and encryption. Unlike software-based encryption, which is vulnerable to software exploits, an HSM provides a robust hardware-backed foundation for cryptographic operations. It is engineered to be tamper-evident and often tamper-resistant, meaning any attempt to physically access or alter its internal components will either destroy the cryptographic material or render the device inoperable, thus preventing compromise. These modules are typically certified to international standards like FIPS 140-2, ensuring a high level of security assurance for the cryptographic processes they handle. For flight technology, where the stakes are incredibly high regarding safety, national security, and critical infrastructure protection, the assurance offered by HSMs is paramount.
Core Functions and Capabilities
The primary functions of an HSM revolve around key management and secure cryptographic processing. Key generation, storage, usage, and destruction are all performed within the secure confines of the HSM. This prevents sensitive keys from ever being exposed to less secure general-purpose computing environments. In the context of flight technology, this means that the private keys used for signing firmware updates, authenticating command signals, or encrypting sensitive sensor data are generated and kept within the HSM, drastically reducing the risk of their compromise.
Beyond key management, HSMs provide high-performance cryptographic operations, including encryption, decryption, digital signing, and hashing. These operations are executed much faster and more securely within the hardware than could be achieved through software alone. For flight systems, this translates to real-time secure communication, rapid authentication of critical systems, and the ability to process encrypted data streams without introducing significant latency, which is crucial for dynamic aerial operations. The integrity of these cryptographic processes, backed by a tamper-proof hardware module, forms the bedrock of trust for any sophisticated flight technology.
Enhancing Navigation and Data Integrity
The reliability of flight technology hinges on precise navigation and the unquestionable integrity of the data it collects and transmits. HSMs play a pivotal role in bolstering these fundamental aspects, creating a fortified barrier against sophisticated cyber threats.
Securing GPS and Navigation Systems
Modern flight technology, particularly UAVs, relies heavily on Global Positioning System (GPS) data for accurate navigation, waypoint following, and autonomous flight. However, GPS signals are susceptible to spoofing attacks, where malicious actors transmit fake GPS signals to deceive a drone into believing it is in a different location, potentially leading it off course or into restricted airspace. An HSM can significantly mitigate this risk by securing the integrity of GPS data processing. It can be used to authenticate the source of GPS correction data (e.g., RTK/PPK systems), ensuring that only trusted, signed correction messages are accepted and applied by the navigation system.
Furthermore, HSMs can protect the cryptographic keys used for secure boot processes and firmware authenticity of the navigation module itself. By digitally signing the navigation software and configuration files, the HSM ensures that only verified and unaltered code can execute, preventing the injection of malicious navigation instructions or the compromise of positioning algorithms. This hardware-backed security extends to the inertial measurement units (IMUs) and other critical navigation sensors, ensuring that their data streams are protected from tampering before being fed into the flight controller, thus guaranteeing that the flight system acts upon authentic positional and orientation information.
Protecting Sensor Data and Telemetry
Drones are increasingly employed for critical missions involving the collection of highly sensitive data, from high-resolution imagery for mapping and surveillance to environmental sensor readings for scientific research. The integrity and confidentiality of this data are paramount. An HSM provides the perfect mechanism to protect sensor data from the moment of collection through transmission and storage.
Upon collection, sensor data can be immediately encrypted using keys securely managed by an HSM. This “encryption at the edge” ensures that even if a drone is intercepted or its communication link compromised, the data remains unreadable to unauthorized parties. Similarly, telemetry data, which includes vital flight parameters such as altitude, speed, battery status, and system diagnostics, can be digitally signed by the HSM before transmission. This digital signature acts as a tamper-evident seal, allowing the ground station to verify that the telemetry data has not been altered in transit. Any discrepancy in the signature would alert operators to potential interference or data manipulation. By securing both the confidentiality (encryption) and integrity (digital signatures) of sensor and telemetry data, HSMs ensure that mission-critical information remains accurate, trustworthy, and protected from prying eyes.
Safeguarding Communication and System Autonomy
The ability for flight technology to operate securely and autonomously hinges on infallible communication and robust protection against unauthorized interference. HSMs are instrumental in building these layers of security, enabling reliable command and control while safeguarding the very core of the flight system.
Secure Command and Control Links
The remote operation of UAVs relies on secure command and control (C2) links between the ground station and the airborne platform. Compromising these links can lead to devastating consequences, including loss of control, mission failure, or even the weaponization of the drone. HSMs provide a critical layer of defense by securing the cryptographic keys used for authenticating command signals and encrypting communication channels.
When a command is issued from the ground station, it can be digitally signed using a private key stored within a ground-side HSM. Upon reception by the drone, an on-board HSM can then verify this signature using the corresponding public key. This process ensures that only commands originating from an authenticated and trusted source are accepted and executed by the flight controller. Simultaneously, all communication between the drone and the ground station, including real-time video feeds, telemetry, and critical commands, can be encrypted using session keys established and managed by the HSMs at both ends. This end-to-end encryption prevents eavesdropping and ensures the confidentiality of sensitive operational data. By hardware-securing the cryptographic foundation of C2 links, HSMs render drones highly resistant to spoofing, jamming, and unauthorized takeover attempts, guaranteeing that operators maintain full, trusted control.
Ensuring Firmware Authenticity and Anti-Tampering
The integrity of a drone’s firmware is paramount. Malicious firmware updates can introduce backdoors, disable safety features, or completely hijack the drone’s functionality. HSMs provide a robust mechanism for ensuring firmware authenticity and preventing tampering throughout the lifecycle of the flight system. Before any firmware is loaded or executed on a drone, its digital signature, created by the manufacturer using a private key secured in an HSM, is verified by an on-board HSM. If the signature is valid, indicating that the firmware has not been altered since it left the manufacturer and originated from a trusted source, the drone proceeds with the boot process or update. If the signature is invalid, the drone will refuse to load the compromised firmware, thereby preventing the execution of malicious code.
This hardware-backed secure boot process is a fundamental defense against supply chain attacks, ensuring that only authentic and approved software runs on the flight platform. Furthermore, HSMs can be integrated into hardware root of trust mechanisms, extending anti-tampering capabilities beyond just firmware. They can protect critical configuration settings, ensure the integrity of the operating system, and even monitor other hardware components for signs of compromise. This comprehensive approach to system integrity, anchored by the HSM, ensures that the drone operates precisely as intended by its designers, maintaining its intended level of safety and reliability, even in hostile cyber environments.

The Future of Secure Flight Operations
As flight technology continues its trajectory towards greater autonomy, swarm intelligence, and integration into critical infrastructure, the role of Hardware Security Modules will only become more pronounced. The increasing complexity of aerial systems necessitates more sophisticated security measures to counteract the evolving threat landscape. Future advancements in HSM technology for flight applications will likely focus on even greater integration into System-on-Chip (SoC) designs for smaller form factors and reduced power consumption, making them ubiquitous across all classes of drones.
Furthermore, HSMs will be crucial in enabling secure interoperability between different drone platforms and ground control systems, especially in scenarios involving multi-drone operations or shared airspace management. Their ability to securely manage identities and cryptographic keys will facilitate trusted data exchange and collaborative missions. With the advent of quantum computing, the need for quantum-resistant cryptographic algorithms will push HSM development towards supporting these new standards, ensuring long-term security against future decryption capabilities. Ultimately, HSMs are not merely a component; they are a foundational pillar for establishing trust, ensuring safety, and enabling the secure and ethical expansion of flight technology into every facet of our lives.
