In the realm of digital security and data integrity, the concept of hashing is fundamental. Among the various hashing algorithms, MD5 (Message-Digest Algorithm 5) has historically played a significant role, particularly in applications where verifying the integrity of data is paramount. While its use in security-critical scenarios has diminished due to discovered vulnerabilities, understanding MD5 remains valuable for appreciating the evolution of cryptographic hashing and its continued application in non-security-sensitive contexts. This article delves into what MD5 hashes are, how they work, their historical significance, and their current relevance, particularly within the broader landscape of tech and innovation.
The Fundamentals of Cryptographic Hashing
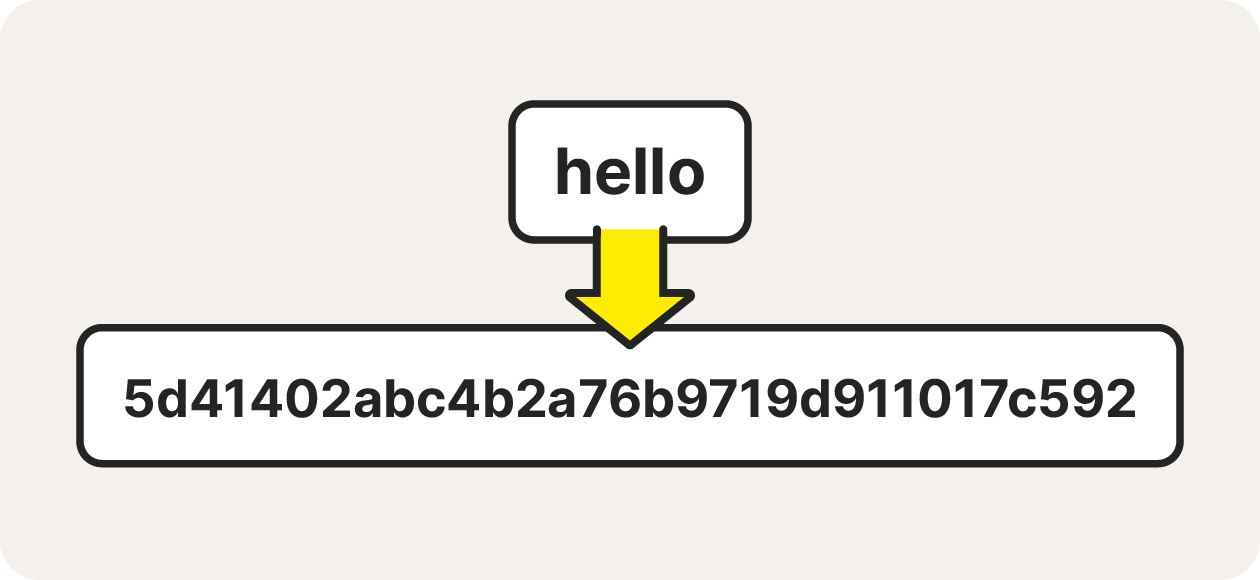
At its core, a cryptographic hash function is a mathematical algorithm that takes an input of any size and produces a fixed-size output, known as a hash value, digest, or simply, a hash. This output is typically a string of characters, often represented in hexadecimal format. The key properties that define a good cryptographic hash function are:
- Deterministic: The same input will always produce the same output. This means if you hash a file today and again tomorrow, you’ll get the identical hash value, provided the file hasn’t changed.
- Fast Computation: It should be computationally efficient to generate a hash for any given input. This is crucial for practical applications where hashing is performed frequently.
- Pre-image Resistance (One-Way Function): It should be computationally infeasible to determine the original input data from its hash value alone. This is why hashing is considered a one-way process; you can easily generate a hash from data, but it’s extremely difficult to reverse the process.
- Second Pre-image Resistance: Given an input and its hash, it should be computationally infeasible to find a different input that produces the same hash. This prevents an attacker from substituting a malicious file for a legitimate one with the same hash.
- Collision Resistance: It should be computationally infeasible to find two different inputs that produce the same hash output. A collision means
hash(input1) == hash(input2)whereinput1 != input2. This is the property that MD5 is most famously known for lacking in modern contexts.
How MD5 Generates a Hash
MD5 operates on an input message of arbitrary length and produces a 128-bit (16-byte) hash value. This is typically represented as a 32-character hexadecimal number. The algorithm involves a series of complex operations, including bitwise operations (AND, OR, XOR, NOT), modular addition, and bitwise rotations, applied in stages. The process can be broadly broken down into several steps:
-
Padding: The input message is padded to ensure its length is a multiple of 512 bits. This padding involves appending a ‘1’ bit, followed by as many ‘0’ bits as necessary, and finally, a 64-bit representation of the original message length. This step is crucial for standardizing the input block size for subsequent processing.
-
Initialization: The algorithm initializes four 32-bit “chaining variables” (often denoted as A, B, C, and D) with specific, fixed magic constants. These values are the starting point for the hashing process.
-
Processing in 512-bit Blocks: The padded message is divided into 512-bit blocks. Each block is then processed sequentially through a series of operations. The current state of the four chaining variables is updated based on the contents of the current block.
-
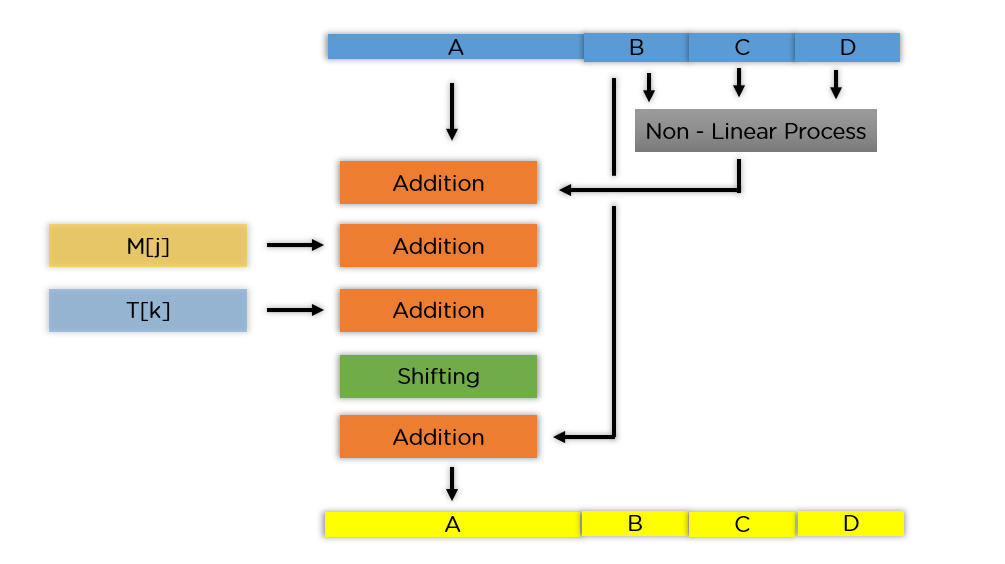
The Core Rounds: Within the processing of each 512-bit block, MD5 employs a series of 64 rounds. These rounds are divided into four stages, with 16 rounds in each stage. Each round involves:
- A non-linear function (F, G, H, or I) that depends on the current values of the chaining variables.
- Addition of a specific “t-constant” (derived from the sine function, a common practice in cryptographic algorithms).
- Addition of a word from the current 512-bit message block.
- A left bitwise rotation of the result by a variable amount.
- Finally, the result is added to one of the chaining variables, and the variables are cyclically shifted.
-
Final Hash Value: After all 512-bit blocks have been processed, the final values of the four chaining variables (A, B, C, and D) are concatenated. These 128 bits form the MD5 hash value.
Historical Significance and Evolution

MD5 was developed by Ronald Rivest in 1991 and published in 1992 as a successor to the MD4 algorithm. At the time of its creation, MD5 was considered a robust and secure hashing algorithm. It quickly found widespread adoption across various computing domains for a multitude of purposes, including:
- Data Integrity Verification: Users would often download files and compare their MD5 checksums (generated by the MD5 algorithm) with those provided by the source. A matching checksum indicated that the file had not been corrupted during download. This was particularly common for software distribution.
- Password Storage: Many systems historically stored user passwords as MD5 hashes rather than plain text. While this was an improvement over storing passwords in cleartext, it became a significant security risk as brute-force and rainbow table attacks became feasible against MD5.
- Digital Signatures: While not the primary algorithm for digital signatures, MD5 was sometimes used in conjunction with public-key cryptography to ensure the integrity of the message being signed.
However, as computational power increased and cryptographic analysis advanced, weaknesses in MD5 began to emerge.
The Vulnerability of Collisions
The most critical vulnerability discovered in MD5 is its susceptibility to collision attacks. In 2004, researchers independently demonstrated that it was possible to find two different inputs that produce the same MD5 hash. This means an attacker could, for instance, create a legitimate-looking document and a malicious one that have identical MD5 hashes. If a system relied solely on MD5 for integrity checks, it would be fooled into accepting the malicious document as authentic.
This weakness significantly undermined MD5’s suitability for security-sensitive applications where collision resistance is paramount, such as digital signatures, SSL certificates, and password security. Consequently, security bodies and software developers began migrating to stronger hashing algorithms like SHA-256 (Secure Hash Algorithm 256-bit) and SHA-3.
Current Relevance and Use Cases
Despite its cryptographic weaknesses, MD5 has not entirely disappeared. Its widespread historical use means that legacy systems and applications might still employ it. Moreover, in specific non-security-critical contexts, its speed and simplicity can still make it a viable option.
Non-Security Sensitive Applications
- Data Deduplication: In storage systems or databases, MD5 can be used to identify duplicate files or blocks of data. By hashing chunks of data, systems can quickly compare hashes to detect identical content, saving storage space. The risk of a malicious collision causing an incorrect deduplication is generally negligible in these scenarios.
- Checksums for File Verification (Non-critical): For users simply wanting to ensure a file hasn’t been accidentally corrupted during a transfer (e.g., copying files between personal devices), MD5 checksums can still be a quick and easy way to check for basic integrity. The emphasis here is on accidental corruption, not malicious tampering.
- Integrity Checks in Specific Software: Some older software or internal tools might continue to use MD5 for basic file integrity checks where the threat model does not involve sophisticated attackers.
Understanding the Shift to Stronger Algorithms
The decline of MD5 in security-critical roles highlights the dynamic nature of cryptography. What is considered secure today may not be tomorrow. This understanding is vital for anyone involved in technology development, cybersecurity, or data management. The industry constantly evolves, pushing for algorithms that offer stronger guarantees against increasingly sophisticated threats. Algorithms like SHA-256 and SHA-3 provide much larger hash outputs (256 bits and variable, respectively) and are based on more complex mathematical principles that make finding collisions astronomically more difficult, if not practically impossible with current computational capabilities.
Conclusion
MD5 is a cryptographic hash function that generates a 128-bit output. Historically, it was widely used for verifying data integrity and in other applications. While it possesses the deterministic and fast computation properties, its susceptibility to collision attacks has rendered it insecure for most security-sensitive purposes. Understanding what MD5 hashes are is essential for appreciating the evolution of cryptographic hashing techniques, the importance of choosing appropriate algorithms for specific use cases, and the ongoing pursuit of stronger, more secure digital technologies. As the tech landscape continues to advance, the lessons learned from algorithms like MD5 underscore the critical need for continuous innovation and vigilance in safeguarding digital information.
