The Imperative of Network Visibility
In an increasingly interconnected world, understanding the landscape of your local Wi-Fi network is no longer a mere convenience but a critical aspect of digital security and optimal performance. Every device, from smartphones and laptops to smart home appliances and IoT sensors, connects to your Wi-Fi, creating a dynamic digital ecosystem. Without clear visibility into this network, users risk unaddressed security vulnerabilities, bandwidth congestion, and potential data breaches. This proactive approach to network management embodies a core tenet of modern tech innovation: control through insight.
Understanding Your Digital Perimeter
Your Wi-Fi network serves as the primary gateway to the internet for most of your devices, establishing a digital perimeter around your home or office. Just as a physical perimeter needs to be monitored for unauthorized entry, your digital space demands constant vigilance. Each connected device represents an entry point, and knowing what these devices are allows you to assess their legitimacy and potential security posture. This understanding forms the bedrock of a robust cybersecurity strategy, moving beyond reactive fixes to proactive risk mitigation. The innovation here lies in the accessible tools and methodologies that empower even non-expert users to gain sophisticated insights into their network’s integrity.
Why Monitor Your Wi-Fi Network?
The reasons for regularly monitoring your Wi-Fi network are multifaceted, touching upon security, performance, and resource management. Firstly, unauthorized access poses a significant security risk. An unknown device on your network could belong to an intruder attempting to access your personal data, exploit vulnerabilities in your devices, or even launch attacks against other systems. Detecting such anomalies early is paramount. Secondly, network performance can suffer dramatically from an excessive number of connected devices, especially if some are consuming large amounts of bandwidth for streaming, gaming, or large downloads. Identifying these bandwidth hogs or inactive connections can help optimize your network’s speed and responsiveness. Thirdly, monitoring helps in managing your digital footprint and inventory. It allows you to confirm that all your intended devices are online and functioning correctly, while also identifying forgotten or legacy devices that might still be drawing power or posing a latent security risk. This iterative process of discovery and management is an ongoing innovation in personal and small-business network security.
Tools and Techniques for Network Discovery
Gaining insight into your Wi-Fi network’s connected devices doesn’t require specialized IT expertise. A range of accessible tools and techniques, from built-in router functionalities to advanced network scanning software, empowers users to effectively monitor their digital landscape. These innovations democratize network oversight, making it possible for anyone to adopt a more secure and efficient online environment.
Router Administration Interface
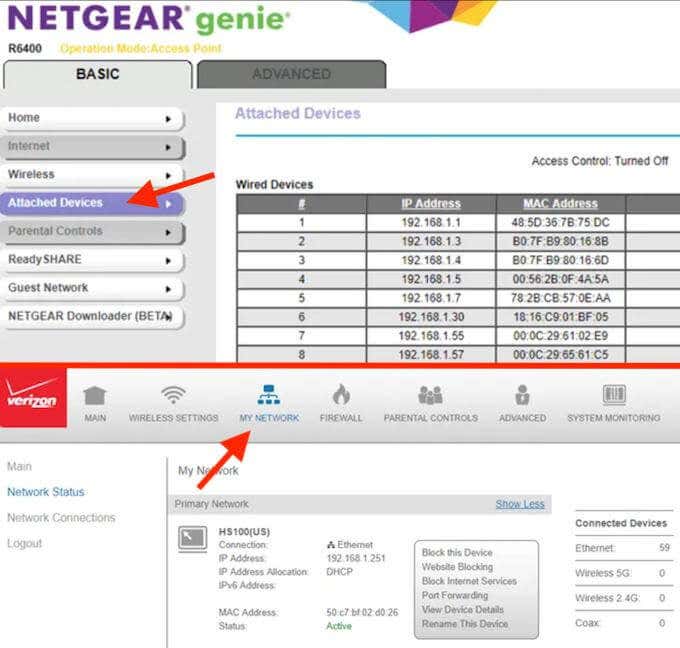
The most fundamental and often overlooked method for seeing what’s connected to your Wi-Fi is through your router’s administration interface. Every modern Wi-Fi router includes a web-based control panel accessible via a web browser. Typically, you can reach this interface by typing your router’s IP address (often 192.168.1.1, 192.168.0.1, or 192.168.100.1) into a browser’s address bar. After logging in with your administrator credentials (which should always be changed from the default for security reasons), you’ll find a section dedicated to “Connected Devices,” “DHCP Clients,” “Client List,” or similar.
This section provides a real-time list of all devices currently connected to your network, both wired and wireless. For each device, you’ll typically see its IP address, MAC address (a unique hardware identifier), and sometimes a hostname (a user-friendly name if the device provides one). This method is direct, requires no additional software, and offers a foundational understanding of your network’s composition. Many modern routers integrate sophisticated dashboards here, representing a significant innovation in user-friendly network management.
Network Scanning Software
For a more comprehensive and often more user-friendly view, dedicated network scanning software offers enhanced capabilities. These applications actively scan your local network to discover all active devices, often providing more detailed information than what a basic router interface might offer.
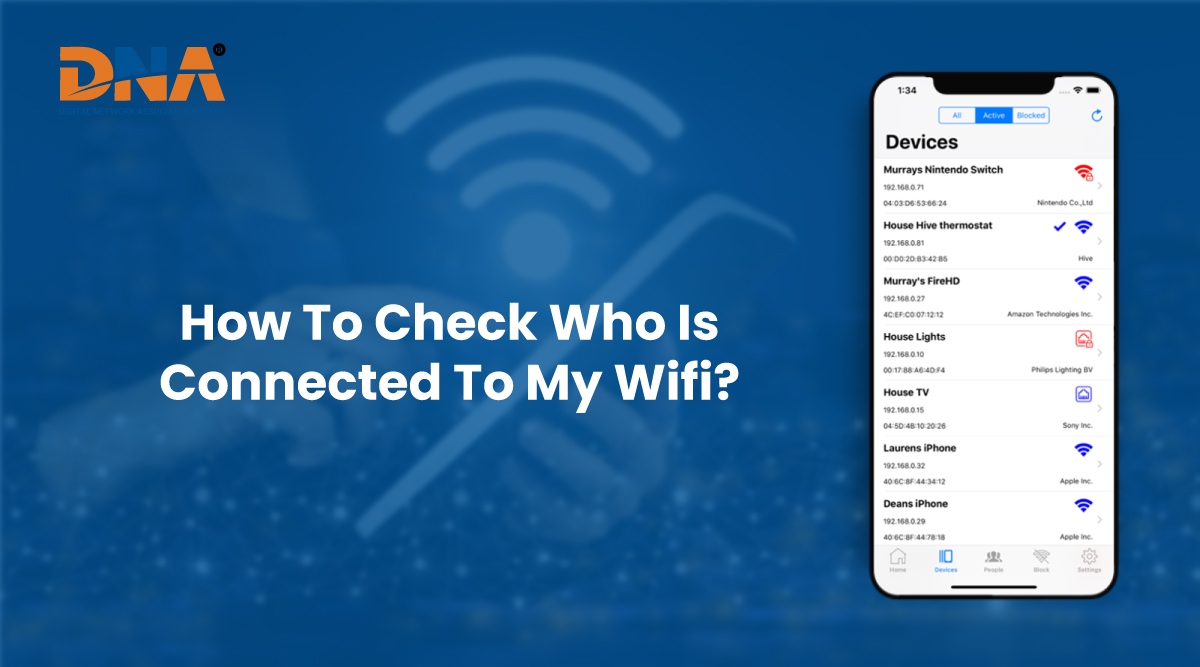
- Fing (Mobile & Desktop): Fing is a popular and highly intuitive network scanner available for both Android, iOS, and desktop operating systems. It quickly discovers all devices on your Wi-Fi, identifies their IP and MAC addresses, and often attempts to determine the device type, manufacturer, and even the operating system. Fing also offers tools for port scanning, network latency checks, and Wi-Fi analysis. Its ease of use combined with powerful features makes it an excellent example of accessible network innovation.
- Advanced IP Scanner (Windows): For Windows users, Advanced IP Scanner is a robust and free utility that provides fast and reliable network scanning. It lists all network devices, their IP addresses, MAC addresses, and often their names, allowing for quick identification. It also offers features to access shared folders or remote control computers directly from the scan results, adding a layer of functionality beyond simple discovery.
- Nmap (Network Mapper – Advanced Users): Nmap is an open-source tool renowned for network discovery and security auditing. While it has a steeper learning curve, Nmap offers unparalleled flexibility and depth. It can perform various types of scans to identify active hosts, open ports, operating systems, and service versions running on networked devices. Nmap is a staple in cybersecurity and network administration for its powerful scripting capabilities and detailed output, representing the cutting edge of network analysis tools.
These tools represent significant innovations in network diagnostics, providing granular detail and actionable insights into the state of your connected environment.
Operating System Utilities
For users comfortable with command-line interfaces, several built-in operating system utilities can reveal connected devices, offering a quick diagnostic without installing additional software.
- ARP (Address Resolution Protocol) Command: The
arp -acommand in Windows Command Prompt or macOS/Linux Terminal displays the ARP cache, which maps IP addresses to MAC addresses of devices that your computer has recently communicated with on the local network. While it doesn’t show all active devices, it’s a useful quick check for immediate neighbors on the network. netstatCommand: Thenetstatcommand (e.g.,netstat -anin Windows/Linux) displays active network connections and listening ports on your own machine. While primarily focused on your device’s connections, it can indirectly help identify suspicious outgoing connections that might indicate compromise, often a secondary step in assessing overall network security.
These utilities, while more technical, underscore the inherent capabilities within operating systems to monitor network interactions, providing a foundational layer of tech insight that advanced tools build upon.
Interpreting the Data and Enhancing Security
Merely listing connected devices is only the first step; the true value lies in interpreting this data and acting upon it to enhance your network’s security posture and performance. This analytical phase represents a significant area of innovation, as tools become smarter at flagging anomalies and suggesting remedies.
Identifying Known vs. Unknown Devices
Upon gathering a list of devices, the critical task is to differentiate between known, legitimate devices and unknown, potentially unauthorized ones.
- MAC Address Lookup: Every network-enabled device has a unique MAC address. By comparing the MAC addresses in your scan results with a list of your personal devices, you can quickly identify unknowns. Most network scanning tools will also attempt to resolve the manufacturer from the MAC address’s Organizationally Unique Identifier (OUI) prefix, which can provide helpful clues (e.g., “Apple, Inc.,” “Samsung Electronics”).
- Hostnames and IP Addresses: Familiar hostnames (e.g., “Johns-iPhone,” “LivingRoom-TV”) and static IP assignments you’ve made can help in identification. For unknown devices, their IP addresses will typically fall within your network’s DHCP range.
- Device Type Inference: Modern network scanners use various techniques, including examining open ports and network traffic patterns, to infer the device type (e.g., “smart speaker,” “printer,” “security camera”). This inference is a powerful innovation in making raw network data more actionable for the average user.
Maintain a spreadsheet or a simple list of your legitimate devices, including their MAC addresses, to streamline this identification process.
Addressing Unauthorized Access
If you discover an unknown device, it’s crucial to act swiftly:
- Change Wi-Fi Password: This is the immediate first step. A strong, unique password for your Wi-Fi network (WPA2 or WPA3 security protocol) will disconnect all current users, including any unauthorized ones. This provides a clean slate.
- Enable MAC Filtering (with caution): Some routers allow you to create a “whitelist” of authorized MAC addresses, blocking any device not on the list. While it adds a layer of security, MAC filtering is not foolproof (MAC addresses can be spoofed) and can be cumbersome to manage as you add new devices. It’s often better used as a secondary defense layer rather than a primary one.
- Update Firmware: Ensure your router’s firmware is up to date. Manufacturers frequently release updates to patch security vulnerabilities, an essential aspect of maintaining network integrity.
- Review Router Security Settings: Disable WPS (Wi-Fi Protected Setup) if not in use, as it can be vulnerable. Ensure your administrative password is strong and unique. Consider enabling a guest network for visitors to keep your primary network isolated.
These steps leverage fundamental network security practices, continually evolving with the latest threats and technological innovations to protect against them.
Proactive Network Hygiene and Innovation
Beyond reactive measures, maintaining “network hygiene” involves continuous monitoring and adaptation. Innovative approaches include:
- Regular Scans: Make network scanning a routine. Monthly or bi-weekly checks can quickly identify new, potentially unauthorized devices.
- IoT Device Isolation: For smart home devices (IoT), consider isolating them on a separate guest network or a dedicated VLAN (Virtual Local Area Network) if your router supports it. This limits their access to your main network, containing potential security risks if an IoT device is compromised. This is a critical innovation in securing the sprawling IoT landscape.
- Strong Passwords for All Devices: Ensure all network-connected devices, not just your Wi-Fi, have strong, unique passwords. Default credentials are a common entry point for attackers.
Advanced Strategies for Network Management
As our digital lives become more integrated and the number of connected devices grows, simple network monitoring evolves into more sophisticated management strategies. These advanced approaches exemplify the ongoing innovation in maintaining secure, efficient, and resilient digital environments.
Implementing Network Segmentation
For users with more complex network requirements or a desire for enhanced security, network segmentation offers a powerful solution. This involves dividing a single physical network into multiple, smaller logical networks (VLANs). Each segment can have its own security policies and access controls, effectively isolating different categories of devices.
For instance, you might create:
- A primary trusted network for your personal computers, sensitive data, and critical devices.
- A guest network for visitors, completely isolated from your main resources.
- An IoT network for smart home devices, limiting their ability to communicate with your primary devices even if compromised.
This strategic partitioning significantly reduces the “blast radius” of a security breach. If one segment is compromised, the attacker’s access is contained, preventing them from easily moving to other, more sensitive parts of your network. Implementing VLANs typically requires a router with advanced features or managed network switches, representing a higher tier of network management innovation.
Leveraging IoT Security Practices
The proliferation of Internet of Things (IoT) devices introduces unique challenges and opportunities for network innovation. From smart thermostats to networked security cameras, these devices often have less robust security features than traditional computers, making them attractive targets for attackers. Advanced practices include:
- Dedicated IoT Gateways: Some solutions offer specialized IoT gateways that funnel all IoT traffic through a secured, managed pipeline, adding layers of encryption and intrusion detection.
- Behavioral Anomaly Detection: Innovative security platforms can monitor the typical network behavior of IoT devices and flag any deviations. For example, if a smart light bulb suddenly attempts to access a foreign server, it could indicate a compromise. This AI-driven monitoring is at the forefront of network security innovation.
- Regular Firmware Updates: Beyond your router, ensure all IoT devices receive regular firmware updates. Manufacturers are continually patching vulnerabilities, and keeping devices current is essential.

Future Trends in Smart Network Monitoring
The landscape of network monitoring is continuously evolving, driven by advancements in artificial intelligence, machine learning, and cloud computing. Future trends promise even more intelligent and automated solutions:
- AI-Powered Anomaly Detection: AI algorithms will become even more sophisticated at identifying unusual network behavior that might indicate an intrusion or malware, without relying on predefined rules. This proactive threat detection will significantly enhance security.
- Self-Healing Networks: Networks of the future may incorporate self-healing capabilities, automatically isolating compromised devices, reconfiguring settings, or deploying countermeasures in response to detected threats, minimizing human intervention.
- Ubiquitous Network Visibility: Integrated cloud-based platforms will offer comprehensive views of entire network ecosystems, from individual devices to broad traffic patterns, accessible from anywhere. This convergence of data and accessibility will provide unprecedented control and insight.
- Zero-Trust Architectures for Homes: Extending enterprise-level “zero-trust” security models (where no device or user is inherently trusted, regardless of their location or prior authentication) to home networks will ensure every connection and access request is rigorously verified, significantly elevating residential cybersecurity.
Understanding and leveraging the tools available today for Wi-Fi network visibility is a crucial step towards embracing these future innovations, ensuring your digital environment remains secure, efficient, and future-ready.
