Understanding network ports and how to check them is a fundamental skill for anyone involved in managing or securing any kind of networked technology, including advanced flight systems. While often discussed in the context of traditional computers, the principles and tools for port scanning are directly applicable to the complex communication networks that underpin modern unmanned aerial vehicles (UAVs), flight control systems, and their associated ground stations.
For drone operators and developers, particularly those working with custom firmware, integrated sensors, or complex mission planning software, knowing which ports are open is crucial for several reasons. It can help diagnose connectivity issues, ensure secure communication channels are established, and verify the functionality of specific onboard services. This article will delve into the methods and tools used to identify open ports, with a focus on their relevance within the realm of flight technology.
Understanding Network Ports in Flight Technology
Network ports are essentially virtual endpoints for network communications. When a device, such as a drone’s flight controller or a ground station’s processing unit, wants to send or receive data, it specifies both an IP address (to identify the destination device) and a port number (to identify the specific application or service on that device). This is analogous to a postal address for a building (IP address) and a specific apartment number within that building (port number).
In the context of flight technology, a wide array of devices and systems communicate over networks. This can include:
- Flight Controllers: These often host services for telemetry data streaming, command reception, diagnostic logging, and firmware updates.
- Gimbal Control Systems: Communicating with the flight controller or ground station to receive commands and send back status information.
- Onboard Sensors: Advanced sensors like LiDAR, thermal cameras, or specialized navigation sensors might expose data streams or configuration interfaces over a network.
- Ground Stations/Control Software: These devices receive telemetry, send commands, display video feeds, and manage mission planning. They often run multiple services that need to communicate with the drone and other ground-based components.
- Data Links: The communication hardware itself (e.g., Wi-Fi modules, cellular modems, proprietary radio links) relies on network protocols and port assignments to manage data flow.
- Autopilots and Navigation Systems: These complex systems may expose APIs or diagnostic interfaces for debugging and configuration.
Each of these components can potentially run services that listen on specific ports. For instance, a drone’s flight controller might have a port open for receiving commands from a companion computer running AI for obstacle avoidance, another for streaming telemetry to a ground station, and yet another for accepting a firmware update. Identifying which of these are active and accessible is the core of port scanning.
TCP vs. UDP Ports
It’s important to differentiate between two primary transport protocols that utilize ports: Transmission Control Protocol (TCP) and User Datagram Protocol (UDP).
- TCP: This is a connection-oriented protocol, meaning it establishes a reliable, ordered, and error-checked connection between two endpoints before data is exchanged. If you send data via TCP, you’re guaranteed that it will arrive in the correct order, and the sender will be notified if any data is lost. For critical flight commands or telemetry, TCP is often preferred. Examples include secure shell (SSH) on port 22 or hyper-text transfer protocol (HTTP) on port 80.
- UDP: This is a connectionless protocol. It sends data packets without establishing a prior connection and without guarantees of delivery, order, or error checking. While less reliable, UDP is faster and more efficient, making it suitable for applications where speed is paramount and minor data loss is acceptable, such as real-time video streaming or voice over IP. Many drone video feeds or sensor data streams might utilize UDP.
Port scanning tools can differentiate between these protocols, often by attempting to connect to a TCP port and sending a UDP packet to a UDP port. The response (or lack thereof) helps determine if the port is open, closed, or filtered.
Methods for Checking Open Ports
The primary method for checking open ports is through a process called port scanning. This involves sending specially crafted network packets to a target IP address on a range of port numbers and analyzing the responses received.
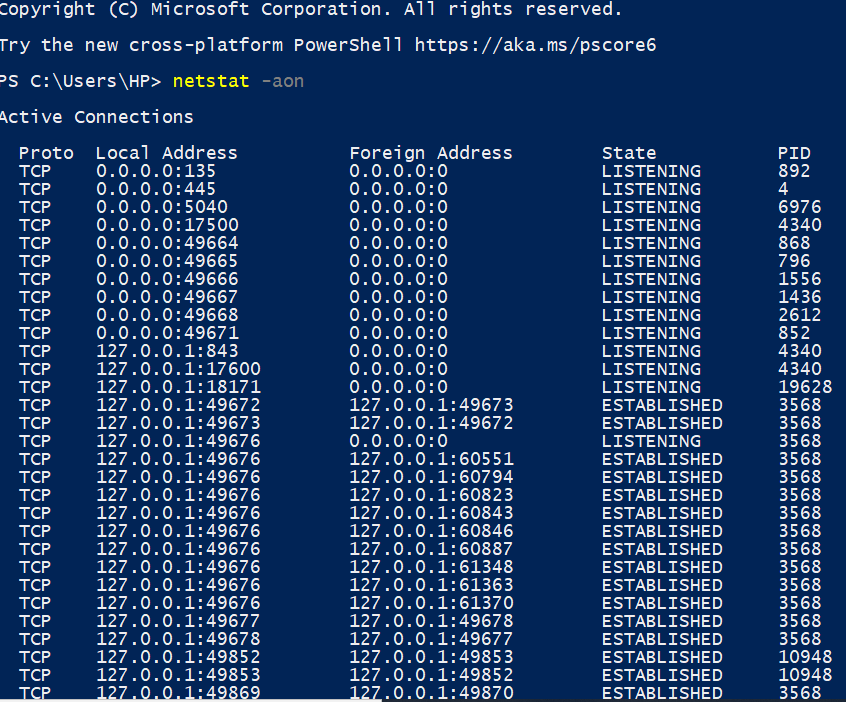
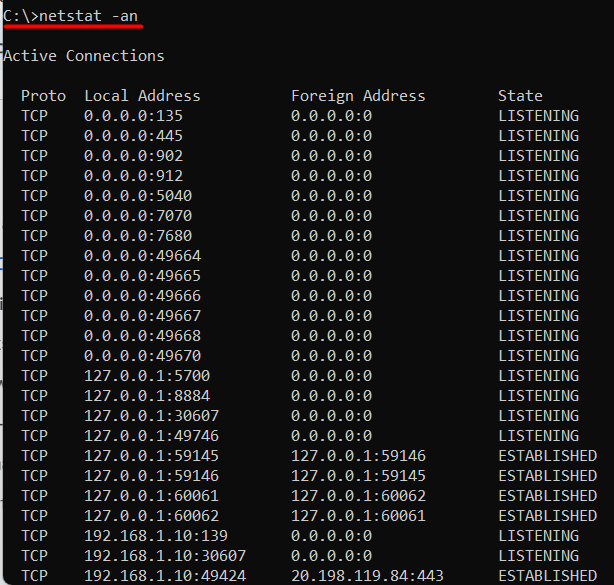
Using Command-Line Tools
For those comfortable with the command line, several powerful and versatile tools are available. These are often the go-to for system administrators and developers for their speed and scripting capabilities.
Nmap (Network Mapper)
Nmap is arguably the most popular and feature-rich network scanning tool. It’s cross-platform and can perform a wide array of scans, from simple port enumeration to advanced OS detection and vulnerability analysis.
Basic TCP Scan:
To check for open TCP ports on a specific IP address (e.g., a drone’s IP, 192.168.1.100), you can use the following command:
nmap 192.168.1.100
By default, Nmap scans the 1000 most common TCP ports. To scan all 65,535 TCP ports, use the -p- option:
nmap -p- 192.168.1.100
Basic UDP Scan:
UDP scanning is generally slower and less reliable than TCP scanning because UDP is connectionless. Nmap uses different techniques for UDP scanning. A common approach is:
nmap -sU 192.168.1.100
Again, to scan all UDP ports:
nmap -sU -p- 192.168.1.100
Service and Version Detection:
Once you’ve identified open ports, Nmap can often determine which services are running on them and their versions. This is invaluable for understanding what functionality is exposed.
nmap -sV 192.168.1.100
Combining this with a full port scan:
nmap -sV -p- 192.168.1.100
Host Discovery:
Before scanning ports, it’s often useful to discover which hosts are active on a network.
nmap -sn 192.168.1.0/24 # Scans the entire subnet for active hosts
Output Interpretation:
Nmap’s output will list ports and their states:
- open: The port is actively accepting connections. This is what you’re looking for.
- closed: The port is accessible, but no application is listening on it.
- filtered: A firewall or other network device is blocking the port, and Nmap cannot determine if it’s open or closed.
For flight technology, an open TCP port might indicate a control interface, while an open UDP port could be for telemetry or video streaming. A filtered port might suggest a security policy in place, or simply that the service is not meant to be externally accessible.
Netcat (nc)
Netcat is a versatile networking utility often referred to as the “TCP/IP swiss army knife.” It can be used for port scanning, though it’s more basic than Nmap.
Checking a single TCP port:
To check if TCP port 23 (Telnet, often used for basic terminal access) is open on 192.168.1.100:
nc -zv 192.168.1.100 23
The -z flag tells netcat to scan for listening daemons, and -v provides verbose output.
- If the port is open, you’ll see a message like
Connection to 192.168.1.100 23 port [tcp/telnet] succeeded!. - If it’s closed or filtered, you’ll get a connection refused or timeout message.
Checking a range of TCP ports:
nc -zv 192.168.1.100 1-100 # Checks ports 1 through 100
Checking a single UDP port:
UDP scanning with netcat is less reliable as it relies on ICMP “port unreachable” messages. If no such message is received, it’s assumed to be open.
nc -zvu 192.168.1.100 53 # Checks UDP port 53 (DNS)
Using Netcat for Scripting:
Netcat is excellent for scripting simple checks within custom diagnostic tools for drones. You can pipe lists of ports into it to automate checks.
Graphical User Interface (GUI) Tools
For users who prefer a visual interface, several GUI tools offer port scanning capabilities, often wrapping Nmap or providing their own scanning engines. These can be more intuitive for less experienced users or for quick visual checks.
Angry IP Scanner
Angry IP Scanner is a popular, open-source, and cross-platform IP address and port scanner. It’s known for its speed and simplicity. It allows you to define IP address ranges and port ranges to scan and displays results in an easy-to-read table.
When scanning a drone’s IP address with Angry IP Scanner, you can specify common ports or a custom range. The results will indicate which ports are open, closed, or possibly filtered, often with additional information like hostnames or MAC addresses. This can be helpful for quickly verifying network services on an onboard computer or flight controller that supports network access.
Advanced Port Scanner
This is a free, Windows-based port scanner that is also highly regarded for its speed and ease of use. It can scan entire networks or specific IP addresses. Similar to Angry IP Scanner, it provides a clear overview of open ports and associated services. For developers working with drone ground station software on Windows, it offers a straightforward way to check network configurations and potential vulnerabilities.
Online Port Scanners
There are also numerous online port scanning services. These are useful if you need to check the external-facing ports of a device that is accessible from the internet. However, for internal drone networks, such as those connecting a ground station to a drone in the field, internal scanning tools are essential. Using an online scanner for a private drone network is generally not feasible or advisable.
Practical Applications in Flight Technology
The ability to check open ports is not just an academic exercise for drone enthusiasts and professionals. It has direct, practical applications:
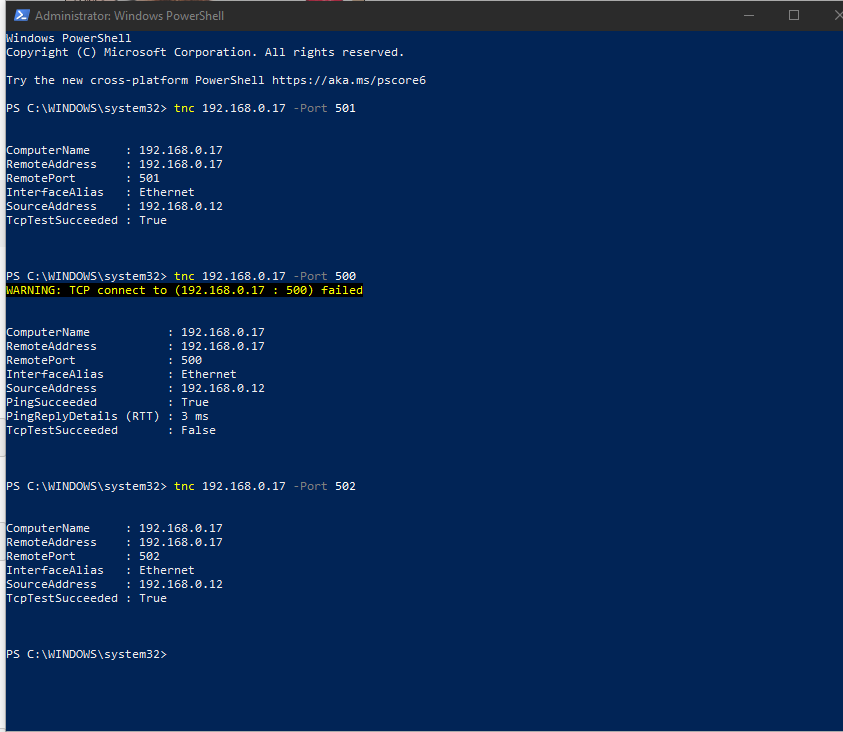
Troubleshooting Connectivity Issues
- Ground Station to Drone: If your ground station software isn’t receiving telemetry or can’t send commands, checking the relevant ports on both the drone and the ground station can help pinpoint the issue. For example, if the telemetry port (e.g., UDP 14550 for MAVLink) is closed or filtered on the drone, that’s a clear indication of where the problem lies.
- Companion Computer Communication: Drones increasingly use companion computers for advanced tasks like computer vision or AI. If these are not communicating correctly with the flight controller, verifying open ports for their inter-process communication (IPC) is a crucial first step.
Security Assessment and Hardening
- Minimizing Attack Surface: For any networked device, especially those that might operate in potentially unsecured environments, it’s vital to ensure only necessary ports are open. Unnecessary open ports represent potential entry points for malicious actors. Regular port scans can reveal services running on unexpected ports, which can then be disabled or secured.
- Verifying Firewall Rules: If you’ve implemented firewall rules on a drone’s onboard computer or ground station to restrict access, port scanning is the way to verify that those rules are effective and that only the intended ports are accessible.
Development and Debugging
- API Verification: Developers building custom software for drones often expose APIs or diagnostic interfaces over the network. Port scanning confirms that these services are running and accessible as expected during the development and testing phases.
- Firmware Updates: Some firmware update mechanisms might rely on specific network protocols and ports. Ensuring these ports are open and correctly configured is essential for successful updates.
Understanding Network Architectures
- Mapping Network Services: For complex drone systems with multiple interconnected components, port scanning can help create a map of available network services, aiding in understanding the overall communication architecture. This is especially useful when integrating third-party hardware or software.
Considerations and Best Practices
When performing port scans, especially on operational drone systems, it’s important to proceed with caution and follow best practices:
- Obtain Permission: Always ensure you have authorization before scanning any network or device that you do not own or manage.
- Scan Responsibly: Avoid overly aggressive scans that could overload a device’s network stack or processing capabilities, potentially disrupting flight operations. Start with less intrusive scans.
- Understand Your Network: Know the IP address range of your drone network and the typical ports used by your flight control software (e.g., MAVLink, PX4, ArduPilot configurations).
- Context is Key: The meaning of an open port depends heavily on the device. An open port on a flight controller is different from one on a ground station or a companion computer.
- Secure Default Passwords: If a scan reveals services like Telnet or FTP are open, always ensure they are secured with strong, unique passwords. Ideally, these services should be disabled or replaced with more secure alternatives like SSH.
- Regular Audits: For mission-critical systems, perform regular port scans as part of your security and maintenance routine.
By mastering the techniques for checking open ports, you gain a powerful toolset for understanding, troubleshooting, and securing the complex networked systems that enable the advanced capabilities of modern flight technology. This knowledge empowers operators to maintain reliable communication, ensure system integrity, and confidently deploy sophisticated drone applications.
