The rapid evolution of drone technology has transformed various industries, from logistics and agriculture to surveillance and entertainment. As these unmanned aerial vehicles (UAVs) become more sophisticated, integrating advanced sensors, AI-driven autonomous capabilities, and complex operational procedures, the volume and sensitivity of the data they collect and transmit skyrocket. In this context, the concept of a “good VPN service,” traditionally associated with internet privacy and cybersecurity for personal computing, takes on a critical new dimension within the realm of drone technology and innovation. It’s not about accessing geo-restricted content; it’s about establishing virtual private networks and secure communication protocols that safeguard drone operations from ground control to cloud storage.
The Imperative for Secure Drone Communication and Data Privacy
Drones are no longer simple toys; they are sophisticated flying computers capable of gathering highly detailed information, executing precise commands, and operating in sensitive environments. This shift brings with it an unprecedented need for robust cybersecurity. Data streams from drones can include high-resolution imagery, thermal data, LiDAR scans, personal identifiable information, and critical infrastructure details. The commands sent to drones, particularly for autonomous missions or sensitive operations, also require impenetrable security to prevent unauthorized access or malicious interference.
A breach in drone security can have severe consequences:
- Data Compromise: Sensitive data collected by drones could be intercepted, leading to privacy violations, corporate espionage, or national security risks.
- Operational Interference: Unauthorized access to a drone’s control link could result in hijacking, diversion from its mission, or even weaponization.
- Reputational Damage: A security incident can severely erode public trust in drone technology and the organizations deploying them.
- Regulatory Penalties: With increasing regulations around data privacy (like GDPR) and aviation security, breaches can lead to significant fines and legal repercussions.
Therefore, for drone technology to truly innovate and integrate into critical sectors, the foundational principles of a “good VPN service”—encryption, authentication, and secure tunneling—must be intrinsically woven into the fabric of drone design and operation.
Applying Virtual Private Networking Principles to Drone Ecosystems
While a traditional VPN service creates a secure tunnel for internet traffic from a user’s device to a VPN server, the application of virtual private networking principles in the drone space involves securing the entire communication pipeline. This includes the command and control (C2) link, telemetry data, sensor feeds, and post-flight data transfer to storage or processing platforms.
Encrypted Command and Control (C2) Links
The C2 link is the lifeline between the drone and its operator or autonomous system. It carries critical instructions for flight path, altitude, payload deployment, and emergency maneuvers. An unencrypted or poorly secured C2 link is highly vulnerable to jamming, spoofing, or interception.
Implementing VPN-like encryption protocols for the C2 link ensures that:
- Confidentiality: Commands are private and cannot be read by unauthorized parties.
- Integrity: Commands cannot be altered during transmission, preventing malicious tampering with flight instructions.
- Authentication: Both the drone and the ground station verify each other’s identity, preventing rogue drones from receiving commands or legitimate drones from being hijacked.
Modern drone systems are increasingly integrating robust, hardware-level encryption and secure communication protocols that function as a dedicated, private network between the drone and its authorized controller, mirroring the security goals of a VPN.
Secure Telemetry and Sensor Data Transmission
Drones constantly transmit telemetry data (position, altitude, speed, battery status) and often stream high-bandwidth sensor data (video, thermal, LiDAR). This data is invaluable but also highly susceptible to interception. Establishing secure, encrypted channels for these data streams, analogous to a VPN tunnel, ensures that:
- Data Privacy: Sensitive visual or environmental data remains confidential.
- Operational Security: Real-time operational data cannot be exploited by adversaries to predict drone movements or mission objectives.
- Regulatory Compliance: Handling of personal or critical infrastructure data aligns with privacy regulations.
Innovations in this area focus on low-latency, high-throughput encryption standards optimized for the unique demands of aerial communication, ensuring data remains secure without compromising real-time performance.

Protecting the Identity and Privacy of Operations
Just as a VPN masks a user’s IP address to enhance online anonymity, secure drone networking solutions can protect the operational privacy of drone missions. This is particularly important for sensitive applications like law enforcement, military reconnaissance, or private industrial inspections where the identity of the operator or the specifics of the mission need to be concealed from potential observers or adversaries.
- Anonymity of Communication: Obfuscating metadata and communication patterns makes it harder to identify the source or destination of drone signals.
- Operational Secrecy: Preventing the association of specific drones with certain operators or mission objectives enhances overall security posture.
Key Attributes of a “Good VPN Service” (Secure Drone Network)
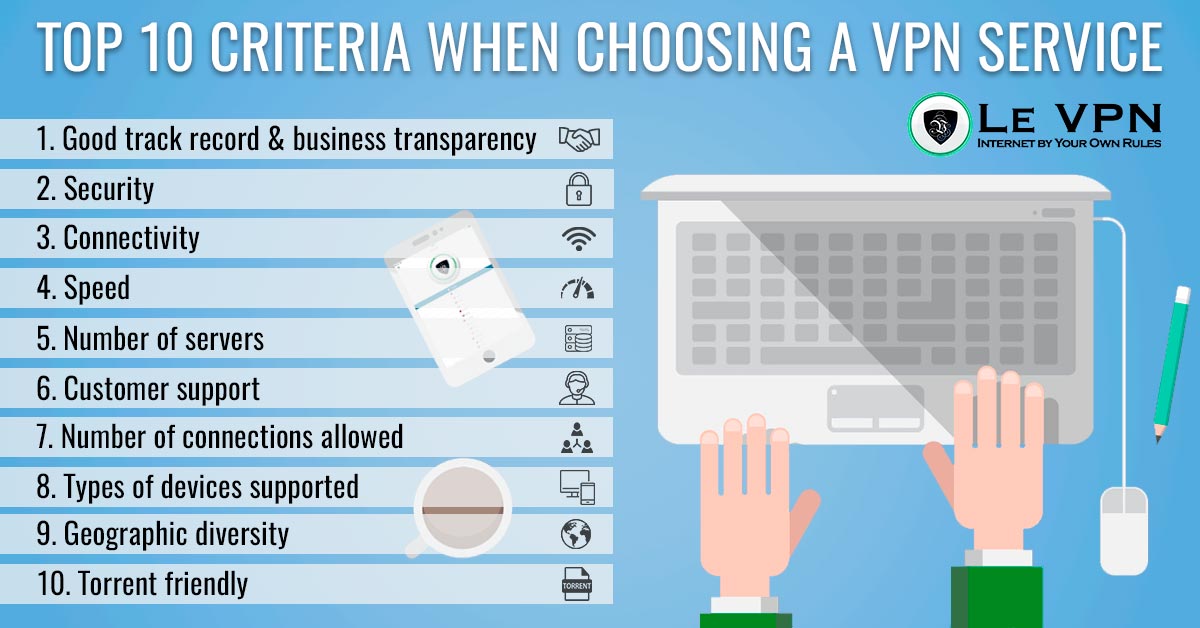
When evaluating what constitutes a “good VPN service” in the context of advanced drone tech and innovation, we must shift our focus from commercial VPN providers to the inherent security architecture of the drone ecosystem itself. The key attributes align with the core principles of robust cybersecurity.
Robust Encryption Standards
At the heart of any secure network is strong encryption. For drones, this means employing industry-standard algorithms like AES-256 for all data in transit. This applies to control commands, telemetry, and payload data. Future innovations might include post-quantum cryptography to future-proof drone communications against emerging threats.
Secure Protocols and Authentication
Beyond encryption, the underlying communication protocols must be inherently secure. This involves:
- Mutual Authentication: Ensuring both the drone and the ground control system cryptographically verify each other’s identity before establishing communication. This prevents unauthorized devices from joining the network.
- Secure Handshake Mechanisms: Robust key exchange protocols that resist eavesdropping and replay attacks.
- Tamper Detection: Mechanisms to detect if data packets have been altered during transmission.
Technologies like Hardware Security Modules (HSMs) on drones and ground stations can further strengthen these protocols by securely storing cryptographic keys.
Low Latency and High Throughput
Unlike general internet browsing, drone operations often require real-time control and high-bandwidth data streaming. A “good VPN service” for drones must therefore minimize latency introduced by encryption/decryption and support the necessary throughput for high-resolution video feeds and complex sensor data without compromising performance. This often necessitates hardware-accelerated encryption and efficient protocol implementations.
Scalability and Centralized Management
For fleet operators, a good secure networking solution must be scalable. It should allow for the centralized management of security policies, cryptographic keys, and access controls for multiple drones. This ensures consistent security posture across an entire fleet and simplifies administration.
Compliance and Regulatory Readiness
As drone regulations evolve, incorporating secure communication standards becomes critical for compliance. A “good VPN service” in this domain anticipates and integrates features that help operators meet upcoming data privacy, aviation security, and critical infrastructure protection regulations. This includes audit trails, secure logging, and incident response capabilities.

The Future of Secure Drone Ecosystems
The integration of “VPN-like” security is not an optional add-on but a fundamental requirement for the future of drone innovation. As drones become more autonomous, operate in swarms, and integrate into smart city infrastructures, their security perimeters will expand and become more complex.
Future innovations will likely include:
- AI-driven Threat Detection: Machine learning algorithms continuously monitoring drone network traffic for anomalies that indicate potential cyber threats or attacks.
- Blockchain for Data Integrity: Utilizing distributed ledger technology to create immutable records of drone data, ensuring its integrity from collection to analysis.
- Quantum-Resistant Cryptography: Proactive adoption of cryptographic algorithms resilient to attacks from quantum computers, safeguarding long-term data security.
- Dynamic Trust Environments: Systems that can adaptively adjust security levels based on the drone’s mission, location, and perceived threat level.
Ultimately, a “good VPN service” in the drone world translates to a comprehensive, multi-layered security architecture that ensures the confidentiality, integrity, and availability of drone operations and the sensitive data they handle. It’s about building trust in the air, securing the invisible links that make drone innovation possible and safe.
