In the rapidly evolving landscape of digital communication, the integrity and authenticity of emails are paramount. As businesses and individuals increasingly rely on email for critical information, marketing, and transactions, the potential for spoofing and phishing attacks grows proportionally. DomainKeys Identified Mail (DKIM) is a cornerstone of email authentication, providing a robust mechanism to verify that an email originated from the domain it claims to be from and that its content has not been tampered with in transit. Central to the implementation and functioning of DKIM is the concept of a “DKIM selector.”
Understanding DKIM Authentication
Before delving into the specifics of a DKIM selector, it’s essential to grasp the fundamental principles of DKIM. DKIM operates by attaching a digital signature to outgoing emails. This signature is generated using cryptographic methods and is linked to the sending domain. When an email arrives at its destination, the receiving mail server can retrieve the public key associated with the sending domain and use it to verify the signature. If the signature is valid, it confirms that the email was indeed sent by the claimed domain and has not been altered.

The process can be broken down into these key steps:
The Signing Process (Sender Side)
- Key Generation: The domain owner generates a pair of cryptographic keys: a private key and a public key. The private key is kept secret by the sender and is used to sign the outgoing emails. The public key is published in the Domain Name System (DNS) records for the domain.
- Signature Creation: When an email is sent, the sender’s mail server uses the private key to create a DKIM signature. This signature is typically appended to the email’s header. The signing process involves hashing the body of the email and specific headers, then encrypting this hash with the private key.
- Signature Encoding: The resulting encrypted hash, along with other information like the signing algorithm and the domain that generated the signature, is encoded into a DKIM-Signature header.
The Verification Process (Receiver Side)
- Signature Retrieval: Upon receiving an email, the recipient’s mail server locates the DKIM-Signature header. This header contains information about the signing domain and, crucially, the DKIM selector.
- Public Key Lookup: Using the selector and the signing domain from the DKIM-Signature header, the receiving server queries the sender’s DNS records. It looks for a specific TXT record that contains the corresponding public key.
- Signature Validation: The receiving server then uses the retrieved public key to decrypt the signature. It also independently hashes the email’s body and specified headers. If the decrypted hash matches the independently generated hash, the signature is considered valid.
This verification process ensures that the email has not been forged and that its content remains unaltered, significantly enhancing email security and deliverability.
The Role of the DKIM Selector
The DKIM selector, often referred to simply as a “selector,” is a critical component that allows for efficient and flexible management of DKIM. In essence, a selector is a unique identifier that differentiates between multiple DKIM signing keys that a domain might be using. Think of it as a specific label or pointer within the DNS records that tells the receiving server exactly which public key to use for verification.
Why Multiple Selectors?
There are several compelling reasons why a domain might employ multiple DKIM selectors:
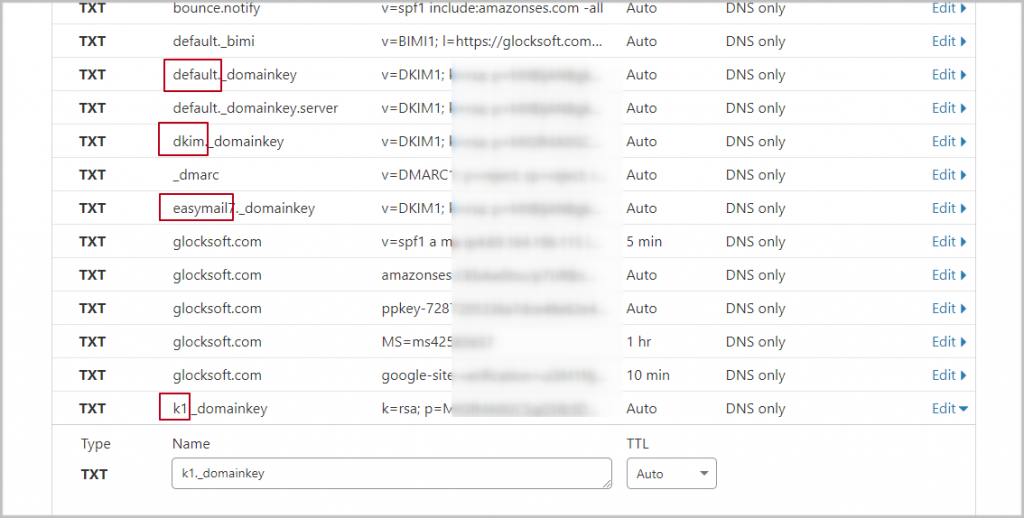
- Key Rotation: For security best practices, it is highly recommended to rotate cryptographic keys periodically. By using different selectors for different keys, a domain can rotate its private and public keys without disrupting the DKIM verification process for existing emails. When a new key pair is generated, a new selector is associated with it, and its corresponding public key is published in DNS. Older selectors and their associated keys can then be phased out over time.
- Managed Mail Infrastructure: Organizations often have complex mail infrastructures. They might use different mail servers, third-party email sending services (like marketing platforms or transactional email providers), or handle inbound and outbound mail differently. Each of these sending entities might need its own DKIM signing key. Using unique selectors for each service or server allows for granular control and simplifies the management of these diverse signing configurations. For example, one selector might be for the primary mail server, another for a dedicated marketing platform, and yet another for a customer support ticketing system.
- Testing and Experimentation: A domain might use a separate selector for testing new DKIM configurations or algorithms before rolling them out to their primary signing keys. This allows for a controlled environment to ensure that the new settings function as expected without impacting the overall email authentication status.
- Delegation of Signing Authority: In larger organizations, different departments or teams might be responsible for sending emails. Each team could be assigned its own DKIM selector and manage its own signing keys, with the DKIM records published under the main domain. This promotes autonomy and efficient management.
How Selectors Work in DNS
When a DKIM signature is generated, it includes a s= tag in the DKIM-Signature header. This tag contains the value of the selector. For example, a signature might look like this:
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/simple; d=example.com; s=mail202308; bh=...
In this example, s=mail202308 indicates that the selector used for this signature is mail202308.
When the receiving mail server encounters this signature, it constructs a DNS query to find the public key. The query will look for a TXT record in the following format:
[selector]._domainkey.example.com
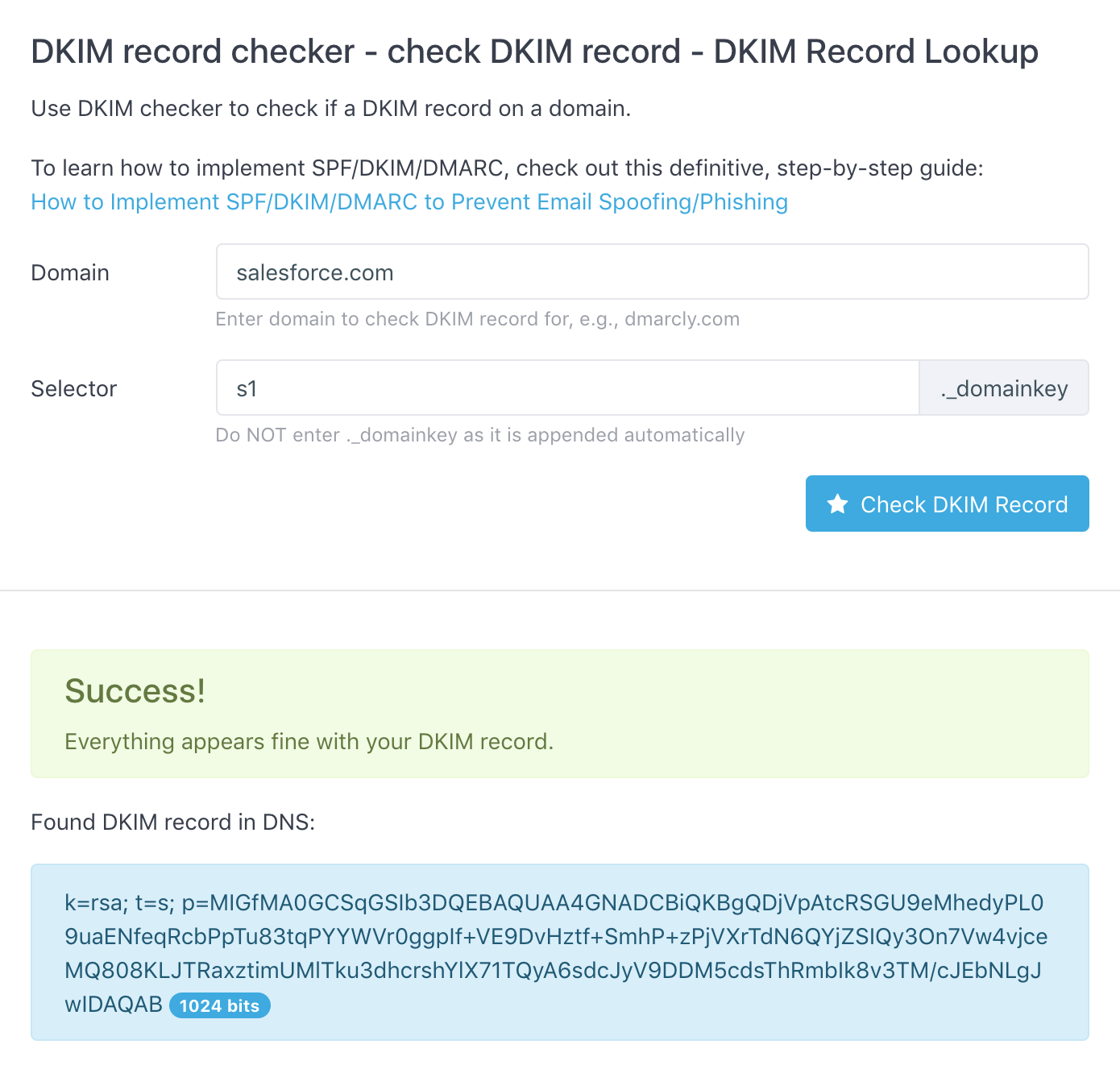
So, in our example, the receiving server would query for:
mail202308._domainkey.example.com
The DNS TXT record at this address would contain the public key necessary to verify the signature. This mechanism provides a clear and structured way to associate specific signing keys with specific sending contexts.
Implementing and Managing DKIM Selectors
Proper implementation and management of DKIM selectors are crucial for maintaining effective email authentication. A misconfigured selector or an incorrectly published public key can lead to legitimate emails being marked as spam or rejected altogether.
Key Management Practices
- Naming Conventions: Establish a clear and consistent naming convention for your selectors. This could include dates (as in
mail202308), service identifiers (e.g.,googlemail,sendgrid), or version numbers. This makes it easier to identify which key is associated with which service or purpose. - Regular Audits: Periodically audit your DKIM records and ensure that all active selectors point to the correct, up-to-date public keys. Remove any old or unused selectors to minimize the attack surface.
- Secure Private Key Storage: The private key is the most sensitive part of the DKIM setup. It must be stored securely, ideally on a dedicated, hardened server or hardware security module (HSM), and access should be strictly controlled.
- DNS Propagation Time: Be aware that changes to DNS records can take time to propagate across the internet. When updating or adding DKIM records, allow sufficient time for these changes to become effective before expecting them to be used for verification.
Common Pitfalls to Avoid
- Typos in Selectors: Even a single typo in the selector name in either the DKIM-Signature header or the DNS record can cause verification to fail.
- Incorrect Public Key: Publishing the wrong public key in the DNS record is a common mistake. Always double-check that the public key corresponding to the private key used for signing is accurately published.
- Missing or Expired Records: If the DNS record for a selector is missing or has expired (though DNS records themselves don’t typically expire in this context unless manually removed), verification will fail.
- Overlapping Selectors: While not technically an error, using too many overlapping or confusing selectors can make management difficult and increase the risk of misconfiguration.
DKIM Selectors in Relation to Other Email Authentication Protocols
DKIM selectors play a vital role within the broader ecosystem of email authentication, working in conjunction with other protocols like SPF (Sender Policy Framework) and DMARC (Domain-based Message Authentication, Reporting & Conformance).
SPF and its Synergy with DKIM
SPF identifies the mail servers authorized to send email on behalf of a domain. It achieves this by publishing a TXT record in the domain’s DNS that lists the IP addresses of authorized sending servers. While SPF authenticates the sending IP address, DKIM authenticates the sender’s domain identity through cryptographic signing.
The combination of SPF and DKIM provides a more robust authentication mechanism. A receiving server can check both:
- SPF: Is this email coming from an IP address authorized to send for this domain?
- DKIM: Was this email signed by the domain it claims to be from, and has its content been altered?
A DKIM selector allows for flexible SPF configurations, especially when using third-party email services. If a service signs emails with its own domain using a specific selector, the domain owner doesn’t need to list the service’s IP addresses directly in their SPF record (though it’s often recommended for a complete SPF implementation).
DMARC and the Power of DKIM Selectors
DMARC builds upon SPF and DKIM, providing a policy framework that tells receiving servers what to do with emails that fail SPF or DKIM checks (e.g., quarantine, reject). DMARC also mandates that the domain identifier used in the “From” header must align with the domain identifier validated by SPF or DKIM.
Crucially, DMARC requires that at least one of the authentication mechanisms (SPF or DKIM) must pass and align for the email to be considered authenticated. A robust DKIM implementation, facilitated by well-managed selectors, is therefore a prerequisite for effective DMARC deployment. DMARC reports also provide valuable insights into DKIM validation results, helping administrators identify issues with their selectors or signing configurations.
When using third-party services that sign with their own domain (and thus require a DKIM selector), ensuring proper DKIM setup is essential for DMARC alignment. A properly configured DKIM selector pointing to the correct public key ensures that the DKIM check passes and aligns with the sending domain, contributing to a strong DMARC posture.
In conclusion, the DKIM selector is not merely a technical detail but a fundamental element that underpins the flexibility, security, and manageability of DKIM. By enabling multiple signing keys and providing a clear mechanism for referencing them in DNS, selectors allow organizations to maintain robust email authentication in complex and dynamic communication environments. Understanding and properly managing DKIM selectors is a critical step for any entity seeking to protect its domain’s reputation and ensure the trustworthiness of its email communications.
