In the rapidly evolving world of unmanned aerial vehicles (UAVs), commonly known as drones, technological sophistication underpins every flight, every data capture, and every autonomous operation. While discussions often center on visible advancements like high-resolution cameras, GPS precision, or AI-powered flight modes, a foundational element of their digital infrastructure operates silently in the background: the Media Access Control (MAC) address. Often overlooked by casual users, a MAC ID is a critical identifier, a digital fingerprint for virtually every network-enabled component within a drone’s intricate ecosystem. Understanding what a MAC ID is and its role offers profound insights into how drones communicate, integrate, and operate securely, placing it squarely within the domain of essential “Tech & Innovation.”
The Digital Fingerprint: Understanding MAC Addresses
At its core, a MAC address is a unique identifier assigned to a network interface controller (NIC) for use as a network address in communications within a network segment. It operates at the data link layer of the OSI model, making it fundamental to local network communication. Think of it as a device’s permanent physical address on a local network, analogous to a street address for a house, whereas an IP address is more like a temporary mailing address that can change depending on where the house is connected to the postal service.
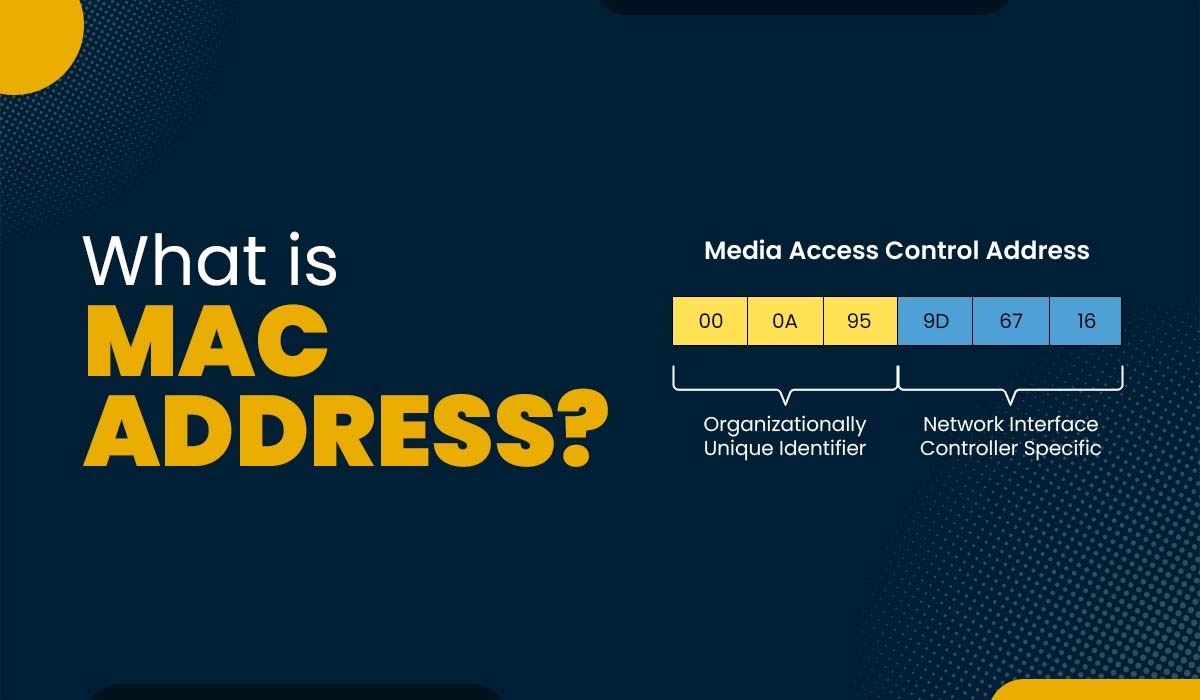
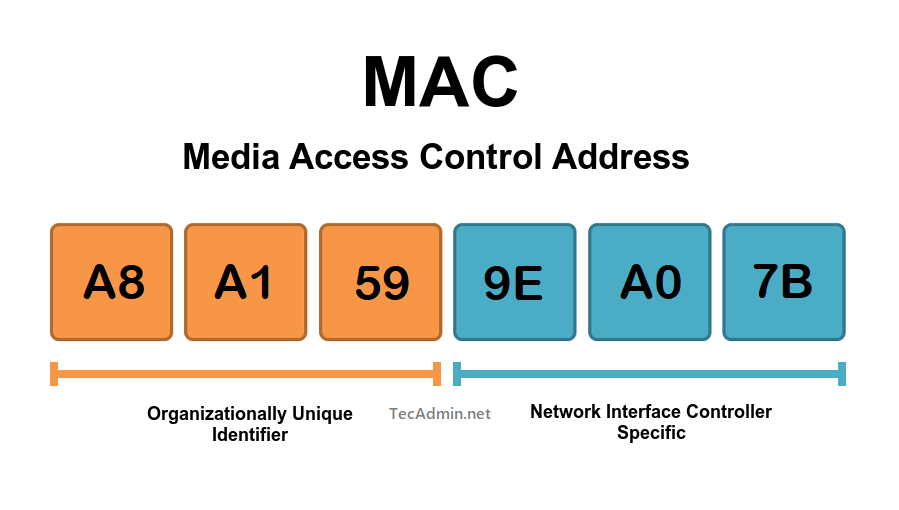
Anatomy of a MAC Address
A MAC address is typically a 48-bit number, usually displayed as six groups of two hexadecimal digits separated by hyphens, colons, or periods (e.g., 00-1A-2B-3C-4D-5E). The first half of the address (the first three octets, or 24 bits) is known as the Organizationally Unique Identifier (OUI). This OUI is assigned by the IEEE (Institute of Electrical and Electronics Engineers) to the manufacturer of the network device. For example, a particular OUI might signify that the device was manufactured by DJI, Parrot, or a specific Wi-Fi module supplier. The second half of the address (the last three octets) is assigned by the manufacturer itself and is unique to that specific device. This two-part structure ensures global uniqueness across all manufactured network interfaces.
How MAC Addresses are Assigned
MAC addresses are hard-coded into the hardware of a network interface card (NIC) at the time of manufacturing. This is why they are often referred to as “burned-in addresses” (BIA). While it’s technically possible to spoof or change a MAC address on a software level for specific purposes (like privacy or bypassing network restrictions), the original, physical MAC address remains embedded in the hardware. For drone components, this means that every Wi-Fi module, Bluetooth chip, or wired Ethernet port on a drone, its controller, or connected peripherals will possess a distinct, factory-assigned MAC address.
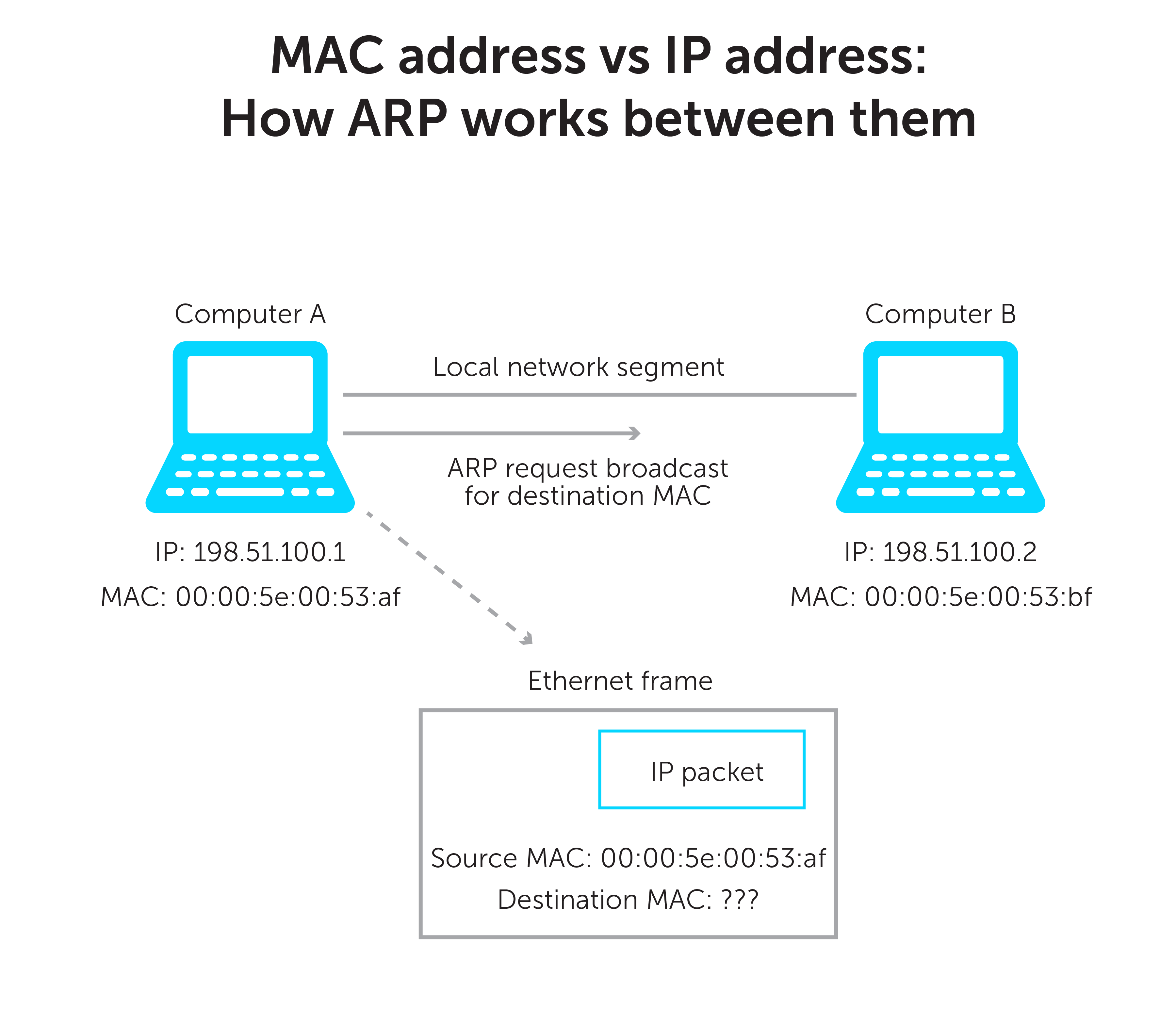
MAC vs. IP Addresses: A Crucial Distinction
It’s vital to differentiate MAC addresses from IP (Internet Protocol) addresses, as both are used for network identification but serve different functions.
- MAC Addresses (Physical Address): Operate at Layer 2 (Data Link Layer) of the OSI model. They identify devices within a local network segment. They are permanent and unique to the hardware.
- IP Addresses (Logical Address): Operate at Layer 3 (Network Layer). They identify devices across different networks and enable routing of data packets over the internet. They can be dynamically assigned (DHCP) or statically configured, and are not tied to the hardware in the same permanent way as a MAC address.
In a drone’s communication, a MAC address ensures that data packets reach the correct hardware interface on the local wireless link between, say, the drone and its controller, or between internal drone modules. An IP address, if used (e.g., for internet connectivity or complex network setups), would then handle routing those packets to their final destination across potentially larger networks.
MAC IDs in Drone Ecosystems: More Than Just Identification
The role of MAC IDs extends far beyond simple identification within the drone landscape. They are integral to communication, security, and the reliable operation of these sophisticated flying machines.
Device Communication and Connectivity
Every modern drone is a network of interconnected components. The flight controller communicates with ESCs (Electronic Speed Controllers), GPS modules, camera systems, and various sensors. Many of these communications, especially those involving wireless interfaces like Wi-Fi or Bluetooth (for telemetry, camera feeds, or controller connections), inherently rely on MAC addresses.
- Drone-to-Controller Link: When a drone establishes a wireless link with its remote controller, MAC addresses play a role in identifying the specific devices on both ends of the connection, ensuring that control commands and telemetry data are directed correctly.
- Payload Integration: Advanced drones often carry specialized payloads like thermal cameras, LiDAR scanners, or agricultural sprayers. If these payloads have their own network interfaces (e.g., to transmit data independently or to receive commands), their MAC addresses enable their seamless integration and distinct identification within the drone’s internal network or when connecting to external ground stations.
- Internal Module Communication: Even within the drone’s internal architecture, certain modules might use network protocols (e.g., Ethernet-over-IP or specific wireless links) where MAC addresses are used to identify and address individual components.
Network Security and Access Control
MAC addresses offer a basic, though not foolproof, layer of network security and access control, particularly useful in managing fleets of drones or restricting access in controlled environments.
- MAC Filtering: In scenarios where multiple drones might operate in proximity, or where specific ground control stations need to connect only to authorized drones, MAC address filtering can be implemented. A Wi-Fi access point or a network router can be configured to only allow devices with specific MAC addresses to connect, effectively creating a whitelist for authorized drones or controllers.
- Preventing Unauthorized Access: While MAC address spoofing is possible, for many common drone operational environments, MAC filtering can deter casual or opportunistic unauthorized connections to a drone’s local network or control link. This is particularly relevant in sensitive operations or where data integrity is paramount.
Firmware Updates and System Diagnostics
Maintaining drone software and hardware is crucial for safety and performance. MAC IDs indirectly support these processes:
- Targeted Updates: Manufacturers or fleet managers might use MAC addresses to track specific drones or batches of drones that require particular firmware updates or diagnostics. While updates are typically managed through higher-level protocols (like IP addresses or unique serial numbers), the underlying network communication for delivering these updates often relies on MAC addresses for local delivery.
- Troubleshooting: During diagnostics, network administrators or drone technicians might use MAC addresses to identify specific network interfaces that are experiencing connectivity issues, helping to pinpoint hardware failures or configuration errors within the drone’s networked components.
Payload Integration and Sensor Networks
Many modern drone applications involve complex sensor suites and sophisticated payloads. These often form their own mini-networks onboard the drone, transmitting vast amounts of data.
- Distributed Sensor Systems: Imagine a drone equipped with multiple environmental sensors, each with its own tiny network interface. MAC addresses would uniquely identify each sensor, allowing the flight controller or an onboard computer to precisely address and collect data from each specific unit.
- High-Bandwidth Data Transmission: For applications requiring high-bandwidth data transfer, such as uncompressed video feeds from a cinema camera or raw data from a LiDAR scanner, dedicated network interfaces on the payload often communicate with a central data logger or a ground station using protocols that rely on MAC addresses for local data link integrity.
Practical Implications and Advanced Applications for Drones
Leveraging MAC IDs extends to practical operational aspects and paves the way for advanced drone applications.
Fleet Management and Asset Tracking
For organizations operating large fleets of drones, managing and tracking individual assets can be complex. While serial numbers and dedicated fleet management software are primary tools, MAC addresses provide an additional layer of hardware-level identification.
- Unique Device Identification: Each drone, and potentially each key network-enabled component within it, carries a unique MAC ID. This can be logged and correlated with other asset information, providing a reliable hardware identifier for inventory management, maintenance scheduling, and tracking specific drone units within a deployment.
- Network Auditing: In networked drone operations (e.g., drones communicating within a hangar or a specific test range), MAC addresses can be used to audit network activity, identifying which specific devices were active and when, aiding in incident investigation or performance analysis.
Regulatory Compliance and Drone Identification
As drone regulations become more sophisticated, the need for unique and reliable drone identification grows. While remote ID systems typically rely on broadcasting unique serial numbers or cryptographically signed identifiers, the underlying network interfaces that facilitate these broadcasts still possess MAC addresses. In some future scenarios, MAC addresses might be integrated into local identification schemes or used by law enforcement or air traffic control to identify specific drone hardware connected to a local network. They could serve as a secondary or confirmatory identifier in highly localized identification requirements.
Enhancing Data Link Reliability
In environments with high electromagnetic interference or numerous wireless devices, ensuring a stable and reliable control link is paramount for drone safety. MAC addresses, by uniquely identifying source and destination hardware, contribute to the foundational reliability of these links. While higher-level protocols manage error correction and retransmission, the initial ability to address the correct physical interface on the network is enabled by MAC IDs. This becomes particularly critical for FPV (First Person View) racing drones or critical infrastructure inspection drones where even momentary communication loss can have severe consequences.
Challenges and Future Trends
While indispensable, the use and implications of MAC IDs are not without their challenges and are subject to evolving trends in networking and privacy.
MAC Address Randomization and Privacy Concerns
In the broader context of consumer electronics (smartphones, laptops), MAC address randomization has become a prevalent feature. This means that a device might present a different MAC address each time it connects to a new Wi-Fi network or at random intervals, making it harder to track a device’s movements or profile a user based on their network presence. For consumer-grade drones that connect to public Wi-Fi networks for updates or data offloading, this privacy feature might be implemented. However, for professional drones or those operating in controlled fleets, a stable and known MAC address is generally preferred for management and security. This creates a dichotomy where privacy interests for consumers clash with the need for reliable identification in professional/industrial applications.
Securing MAC-Based Communication
While MAC filtering provides a basic layer of security, it’s not robust enough against determined attackers who can spoof MAC addresses. Therefore, drone communication security relies heavily on higher-level encryption and authentication protocols (e.g., WPA2/WPA3 for Wi-Fi, TLS for data transmission). MAC IDs serve as the foundational layer, but subsequent layers of security are essential to protect sensitive drone operations and data. The “Tech & Innovation” space continues to develop more robust secure boot processes and hardware-level security measures that tie cryptographic identities to immutable hardware identifiers, of which the MAC ID is a part.
The Role of MAC IDs in Future Drone Swarms
The future of drone technology points towards autonomous swarms and highly coordinated multi-drone operations. In such scenarios, ultra-reliable and efficient inter-drone communication will be critical. While high-level mesh networking protocols and AI will orchestrate swarm behavior, the underlying network identification and addressing for each drone in the swarm will still rely on MAC addresses. They will be crucial for establishing ad-hoc networks, identifying individual nodes, and managing the flow of localized data between drones within the swarm, contributing to the overall intelligence and resilience of the collective.
Conclusion: The Unseen Foundation of Drone Connectivity
The MAC ID, or Media Access Control address, often goes unnoticed amidst the dazzling array of features and capabilities that modern drones offer. Yet, it stands as an unsung hero, a fundamental building block of their digital existence. From enabling basic device-to-controller communication to facilitating complex payload integrations, fleet management, and laying the groundwork for future drone swarms, MAC addresses are intrinsic to the operational reliability and networked intelligence of UAVs.
As drones continue to push the boundaries of technology and innovation, becoming more autonomous, interconnected, and integrated into our daily lives, understanding the foundational technologies like MAC IDs becomes increasingly important. They are the unseen fingerprints that ensure every packet of data, every command, and every piece of telemetry finds its rightful home in the intricate, high-flying world of drones, solidifying their place as a critical piece of “Tech & Innovation.”
