The digital age has woven a complex tapestry of interconnected services, and at the heart of this intricate web lies the email account. It’s more than just a digital mailbox; it’s the primary key to unlocking countless online services, from social media platforms and online banking to cloud storage and even professional networking tools. For many, particularly those new to the digital landscape or those who manage multiple online presences, the question “What’s my email account?” can surface with surprising frequency. Understanding how to identify and manage your primary email accounts is not just a matter of convenience, but a critical aspect of digital security and efficient online navigation.
The Foundational Role of Email in the Digital Ecosystem
Email accounts have evolved far beyond their initial function of sending and receiving messages. They now serve as unique identifiers across the vast expanse of the internet. When you sign up for a new service, the email address you provide is almost universally used to:
Account Creation and Verification
This is the most fundamental use. Upon registration, a verification email is sent to your provided address to confirm its legitimacy. This step prevents the use of fake or disposable email addresses and ensures you are who you claim to be. Without this verification, many platforms would be susceptible to bot-driven spam and fraudulent account creation.
Password Recovery and Account Security
Perhaps the most crucial function of an email account in modern digital life is its role in password recovery. Forgetting a password is an almost universal experience. Your registered email account becomes the lifeline to regaining access to your locked-out services. A simple “Forgot Password” link typically triggers an email containing a reset link or a temporary code, allowing you to establish a new, secure password. This reliance underscores the paramount importance of keeping your primary email account secure and accessible.
Communication Hub for Services
Beyond initial verification and recovery, your email account acts as a central hub for communication from the services you use. This includes:
- Notifications: Alerts about account activity, security breaches, or important updates from the platform.
- Billing and Invoices: For subscription services, online purchases, or financial transactions, your email often receives receipts, invoices, and payment reminders.
- Promotional Content: While sometimes intrusive, marketing emails are a common form of communication from businesses about new products, services, or special offers.
- Important Announcements: Service changes, terms of service updates, or critical policy shifts are almost always communicated via email.
Digital Identity and Authentication
In many scenarios, your email address functions as your primary digital identifier. When logging into websites or applications, you are often prompted for your email address (or username, which is frequently an email address) and password. This process authenticates your identity and grants you access to your personalized account. This consistent use solidifies the email account’s status as a core component of your digital persona.
Strategies for Identifying Your Email Accounts
The proliferation of online services often leads to the creation of multiple email accounts, sometimes for different purposes or at different stages of one’s digital journey. Recalling all of them can be a challenge. Here are effective strategies to help you pinpoint your various email accounts:
Reviewing Browser Saved Credentials
Modern web browsers, such as Chrome, Firefox, and Edge, offer functionality to save login credentials for websites. If you have historically used your browser to log in to services, it likely stores your email address and password.
- Accessing Saved Passwords: Navigate to your browser’s settings and look for sections labeled “Passwords,” “Autofill,” or “Security.” Within these sections, you can typically view a list of websites for which you’ve saved credentials, along with the associated email addresses.
- Limitations: This method is effective only if you have consistently used the browser’s save feature and haven’t cleared your browser data. It also won’t help if you access services primarily through mobile apps without prior browser saving.
Searching Your Inbox for Verification and Welcome Emails
The initial email you receive when signing up for a service is often a “welcome” or “verification” email. These emails are invaluable for remembering which email address you used.
- Keyword Searches: Log into your known email accounts and perform targeted searches using keywords such as “welcome,” “verify your email,” “account created,” “signup confirmation,” or the names of popular services (e.g., “Facebook account,” “Amazon order,” “Google,” “Microsoft”).
- Sender Identification: Pay close attention to the sender’s email address. Many services send these initial emails from specific, easily recognizable domains (e.g.,
@google.com,@microsoft.com,@amazon.com). - Date Ranges: If you have an idea of when you might have created an account, filtering your search by date can narrow down the results considerably.
Leveraging Password Managers
If you use a dedicated password manager (e.g., LastPass, 1Password, Bitwarden), this is your most robust tool for tracking your email accounts. Password managers are designed to securely store all your login credentials.
- Comprehensive Database: Your password manager will contain a list of all the websites and applications you’ve logged into, along with the associated usernames (which are often your email addresses) and passwords.
- Cross-Platform Access: Most password managers offer browser extensions and mobile apps, ensuring you can access this information regardless of the device you’re using.
- Security Benefits: Beyond identification, password managers significantly enhance your online security by generating and storing strong, unique passwords for each service.
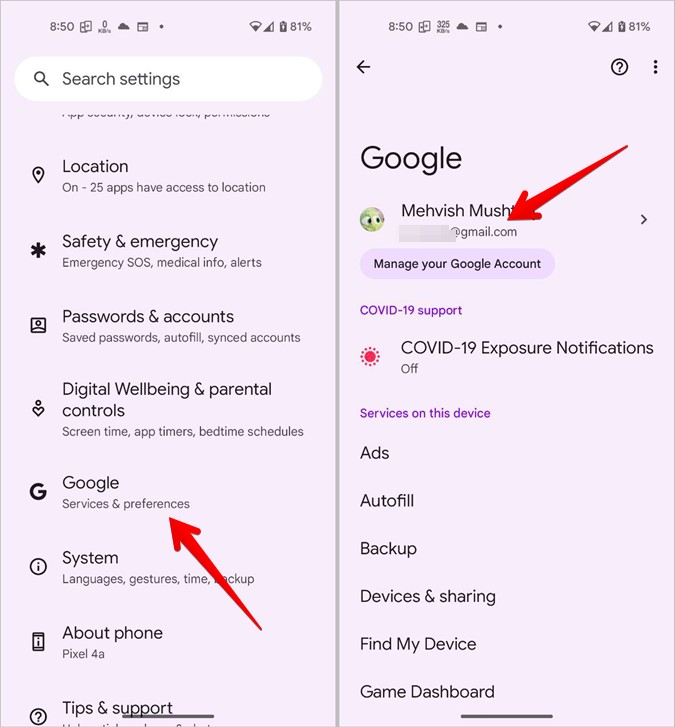
Checking Connected Accounts and Apps
Many online platforms allow you to link or connect them to other services. Your email account is frequently the common thread.
- Social Media Logins: If you’ve ever used “Login with Google,” “Login with Facebook,” or “Login with Apple,” these services link your social media account (and its associated email) to the new platform. Check the settings of your primary social media accounts for “Connected Apps” or “Linked Accounts.”
- Third-Party App Permissions: Review the settings within your email provider’s interface (e.g., Gmail’s “Security” settings, Outlook’s “Apps and Services”) to see which third-party applications have been granted access to your account. This can reveal other services you’ve authorized using that email.
Examining Financial Records and Subscriptions
For services that involve financial transactions, your email is often used for billing and receipts.
- Bank Statements and Credit Card Bills: Review your financial statements for recurring charges or online purchases. The vendor or service name might jog your memory, and you can then try logging into that service with your known email addresses.
- Subscription Management Services: Services like “Truebill” or “Rocket Money” can scan your financial accounts to identify recurring subscriptions, often providing the associated email used for signup.
The Significance of a Primary Email Account
While managing multiple email accounts might be necessary for organizational purposes, designating and consistently using one or two primary email accounts is highly recommended for several reasons:
Streamlined Management and Reduced Risk
Having a primary email account simplifies your digital life. You know where to look for important notifications, password resets, and service communications. This reduces the cognitive load and minimizes the risk of missing critical information due to it being scattered across numerous inboxes.
Enhanced Security Posture
The security of your primary email account is paramount. If it’s compromised, it can serve as a gateway for attackers to access many other services linked to it. By focusing your security efforts on one or two main accounts, you can implement stronger passwords, enable two-factor authentication (2FA), and diligently monitor for suspicious activity.
Professionalism and Credibility
For professional networking, job applications, and business communications, a consistent and professional-looking email address is crucial. Using a personal Gmail or Outlook account for professional purposes is generally acceptable, but a custom domain email (e.g., yourname@yourcompany.com) is ideal if you run a business. Avoid using very old, informal, or overly casual email addresses for professional interactions.
Ease of Use for Recovery
When you inevitably forget a password or need to recover an account, having a designated primary email makes this process straightforward. You know exactly which inbox to check for the reset link or verification code, saving time and reducing frustration.
Protecting Your Email Accounts: A Digital Imperative
Once you’ve identified and consolidated your important email accounts, the focus must shift to their protection. The security of your email is the cornerstone of your digital security.
Strong, Unique Passwords
This is the first line of defense. Avoid using easily guessable passwords, personal information, or common word combinations. Opt for long, complex passwords that include a mix of uppercase and lowercase letters, numbers, and symbols. Crucially, use a different password for each email account and for any other service linked to it. A password manager is an invaluable tool for generating and storing these complex credentials.
Enable Two-Factor Authentication (2FA)
Two-factor authentication adds an extra layer of security by requiring a second form of verification beyond just your password. This could be a code sent to your phone via SMS, generated by an authenticator app (like Google Authenticator or Authy), or a physical security key. Enabling 2FA on your primary email accounts is one of the most effective ways to prevent unauthorized access.
Be Wary of Phishing Attempts
Phishing emails are designed to trick you into revealing sensitive information, such as your password or financial details. They often mimic legitimate communications from well-known companies. Always scrutinize emails asking for personal information, look for unusual sender addresses, and avoid clicking on suspicious links or downloading unexpected attachments. When in doubt, go directly to the service’s official website instead of clicking a link in an email.
Regularly Review Account Activity
Most email providers offer logs or activity summaries that show when and from where your account has been accessed. Regularly reviewing this information can help you spot any unauthorized logins or suspicious activity, allowing you to take prompt action.

Secure Your Devices
The devices you use to access your email accounts are also potential vulnerabilities. Ensure your computers, smartphones, and tablets are protected with strong passcodes or biometric security (fingerprint, facial recognition). Keep your operating systems and applications updated, as these updates often include critical security patches.
The question “What’s my email account?” is more than a simple query; it’s an invitation to reflect on one’s digital footprint and the importance of organized, secure online management. By understanding the fundamental role of email, employing effective identification strategies, and prioritizing robust security measures, individuals can navigate the digital world with greater confidence and peace of mind.
