The digital landscape, while offering unparalleled connectivity and convenience, also presents inherent risks. For drone enthusiasts and professionals alike, a compromised drone or associated account can be a deeply unsettling experience, leading to potential data breaches, loss of equipment, or even unauthorized operation. Understanding how to respond effectively when your drone or its ecosystem is hacked is paramount to mitigating damage and regaining control. This guide focuses on the critical steps to take when facing a drone-related cybersecurity incident, concentrating on the interconnected technologies that safeguard and control your aerial assets.
Understanding the Attack Vectors
Before delving into remediation, it’s crucial to grasp how drone systems can be compromised. While sophisticated nation-state attacks on drone control systems are rare for the average user, more common vulnerabilities lie within the broader digital ecosystem that surrounds them.
Compromised Control Applications
The primary interface for many drones is a dedicated mobile application or desktop software. These applications, designed for flight control, telemetry, and camera management, can themselves be targets. Malware disguised as legitimate updates, phishing attempts targeting login credentials, or vulnerabilities within the app itself can grant unauthorized access. If an attacker gains control of your account credentials for the drone’s control app, they could potentially access your flight logs, location data, and, in some cases, even attempt to issue flight commands if the drone is within range and connected.
Network Vulnerabilities
The communication link between your controller and the drone is a critical point of potential interception. While many modern drones employ encrypted communication protocols, older models or improperly configured systems might be susceptible to man-in-the-middle attacks. Furthermore, if your drone’s Wi-Fi network (used for initial setup or direct connection in some models) is not secured with a strong password, it becomes an easy entry point for unauthorized access. This could allow an attacker to join your network and potentially interact with the drone’s onboard systems.
Account Takeovers
Beyond the drone-specific apps, your general online accounts play a vital role. If the email address associated with your drone manufacturer’s account, your cloud storage for flight footage, or even your social media accounts (if linked for sharing) are compromised, an attacker could leverage these to gain access to your drone-related information or even reset passwords for your drone accounts. Weak passwords, reused credentials across multiple platforms, and a lack of multi-factor authentication are common culprits here.
GPS Spoofing and Interference
While less about “hacking” in the traditional sense and more about electronic warfare, deliberate GPS spoofing or jamming can disrupt navigation systems. This can cause a drone to lose its position hold, fly erratically, or even be guided off course to a location not intended by the pilot. Understanding the potential for such interference, especially in sensitive operational areas, is part of comprehensive drone security.
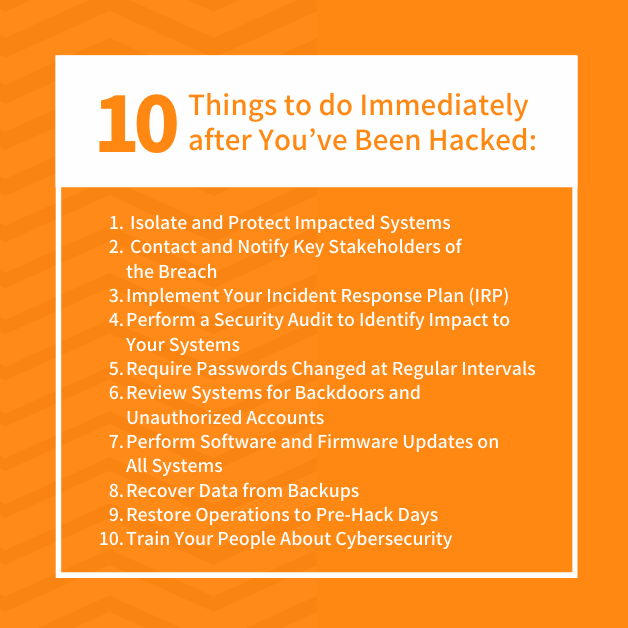
Immediate Actions Upon Suspected Compromise
The moment you suspect your drone system has been hacked, a swift and methodical response is essential. Delay can exacerbate the problem and make recovery more difficult.
Disconnect and Isolate
The first and most critical step is to immediately disconnect the drone from any network it might be connected to, including Wi-Fi and cellular data. If you suspect the controller app is compromised, close the application and, if possible, disconnect the mobile device from the internet entirely. For connected drones, this might involve powering them down if they are not in flight. The goal is to prevent further unauthorized access or data exfiltration.
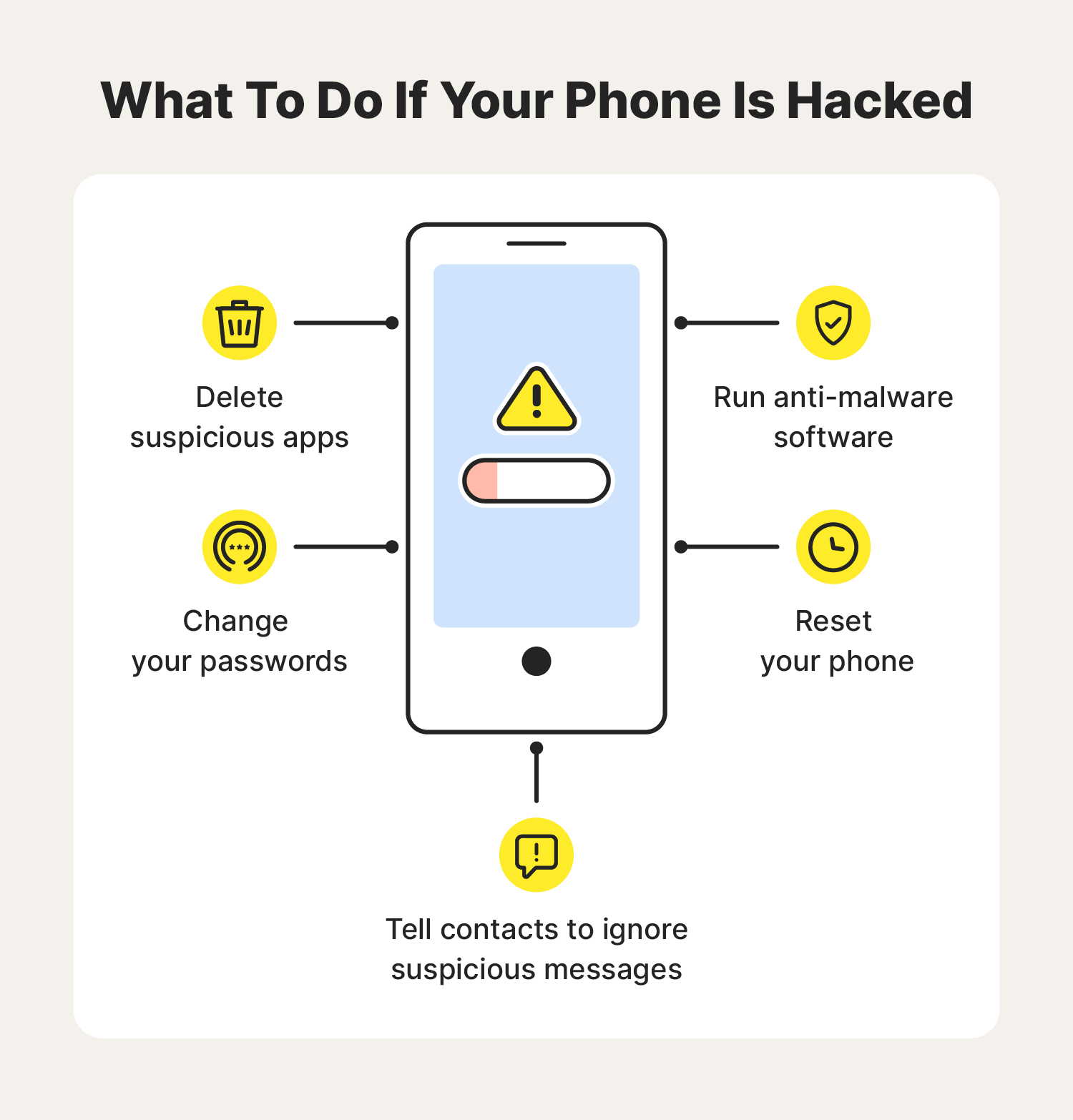
Secure Your Accounts
If you believe your drone-specific account or associated email has been compromised, change your password immediately. Use a strong, unique password that you do not use anywhere else. Enable multi-factor authentication (MFA) if it’s not already active. This adds a crucial layer of security, requiring more than just a password to log in. Review your account activity for any suspicious logins or changes.
Preserve Evidence
If you suspect unauthorized flight activity or data tampering, try to preserve any available logs. This includes flight logs stored on the drone itself, within the control application, or in any cloud storage services you use. Screenshots of unusual activity or error messages can also be valuable. Avoid deleting anything, as it might be needed for investigation or reporting.
Notify Relevant Parties

If you are using the drone for professional purposes, notify your organization’s IT security team or management immediately. If the incident involves potential misuse of your drone or its data, consider reporting it to law enforcement or relevant aviation authorities. For manufacturer-specific issues, contacting their customer support with details of the suspected hack can be crucial for them to investigate and potentially issue patches or advisories.
Recovery and Prevention Strategies
Once the immediate crisis is managed, the focus shifts to recovery and implementing robust preventative measures to avoid future incidents.
Comprehensive System Reset
In cases of suspected deep compromise, a full factory reset of your drone might be necessary. Consult your drone’s manual for the specific procedure, as it can vary between models. This will erase all custom settings, including any potentially malicious configurations. Similarly, uninstall and reinstall the control application on your mobile device or computer to ensure you have a clean, uncorrupted version.
Secure Network Practices
- Strong Wi-Fi Passwords: If your drone connects to a local Wi-Fi network for setup or control, ensure this network is protected by a strong, unique password using WPA2 or WPA3 encryption.
- Guest Networks: Consider using a separate guest network for your drone’s initial setup or any IoT devices that don’t require direct access to your primary network.
- Regular Updates: Keep your router firmware updated, as older versions can have known security vulnerabilities.
Enhanced Account Security
- Unique Passwords: Implement a password manager to create and store strong, unique passwords for every online account, especially those related to your drone.
- Multi-Factor Authentication (MFA): Activate MFA on all your critical accounts (email, drone manufacturer accounts, cloud storage, etc.). This is one of the most effective defenses against account takeovers.
- Phishing Awareness: Be vigilant about phishing attempts. Never click on suspicious links or download attachments from unknown senders. Verify the legitimacy of any communication requesting your credentials or personal information.
Drone-Specific Security Measures
- Firmware Updates: Regularly check for and install firmware updates for your drone and controller. Manufacturers often release updates that patch security vulnerabilities.
- Secure Communication: Understand the encryption protocols used by your drone’s communication system. Modern drones generally use robust encryption, but it’s good to be aware.
- Physical Security: When not in use, store your drone and its accessories securely to prevent unauthorized physical access.
Data Management and Privacy
- Review Permissions: Carefully review the permissions requested by your drone’s control app. Understand what data it’s accessing and why.
- Cloud Storage Security: If you store your flight footage or telemetry data in the cloud, ensure that service is also secured with strong passwords and MFA.
- Data Minimization: Only collect and store data that is necessary for your operations. Be mindful of privacy regulations if you are capturing footage of people or private property.
When to Seek Professional Help
While many hacking incidents can be managed with the steps outlined above, certain situations may warrant professional assistance.
Persistent Issues and Advanced Threats
If you’ve followed all the standard recovery steps and still experience unexplained behavior, or if you suspect a more sophisticated attack targeting your drone’s core systems, it’s time to seek expert help. Cybersecurity professionals specializing in IoT or aviation security can provide advanced diagnostic and remediation services.
Legal and Forensic Investigations
In cases where your drone has been used for illicit purposes, data has been stolen, or significant financial or operational damage has occurred, a digital forensics expert can help gather evidence for legal proceedings. They can analyze system logs, network traffic, and device states to reconstruct events and identify perpetrators.
Manufacturer Support Escalation
For critical security flaws or if you suspect a vulnerability in the drone’s hardware or software itself, escalating the issue with the manufacturer’s technical support or security team is essential. They have the deepest understanding of their product’s architecture and can investigate at a fundamental level.
The landscape of drone technology is rapidly evolving, and with it, the potential for cybersecurity threats. By remaining informed, vigilant, and prepared with a clear response plan, you can significantly mitigate the risks associated with drone hacking and protect your valuable aerial assets and the data they capture. Proactive security measures are not merely an afterthought but an integral part of responsible drone operation in today’s interconnected world.
