Blackmail is a serious criminal offense that can have devastating consequences for victims, both emotionally and financially. If you find yourself in this distressing situation, it’s crucial to act swiftly and strategically. This guide will walk you through the essential steps to take, focusing on preserving your digital security, gathering evidence, and seeking appropriate assistance. While the situation is undoubtedly stressful, a calm and methodical approach is your strongest defense.
Understanding the Threat and Securing Your Digital Footprint
The first and most critical step in dealing with blackmail is to understand the nature of the threat and immediately take steps to secure your digital life. Blackmailers often exploit information they’ve obtained illicitly, and their leverage is directly tied to your online presence and personal data.
Assess the Blackmailer’s Claims and Demands
Before reacting, take a moment to calmly assess what the blackmailer is claiming to possess and what they are demanding. Are they claiming to have compromising photos, private conversations, financial information, or something else entirely? What is their ultimate goal? Are they asking for money, favors, or to perform a specific action?
- Identify the Leverage: Pinpoint exactly what information or material the blackmailer believes they have that can harm you. Understanding their leverage is key to dismantling their strategy.
- Analyze the Demands: Be clear about the specific actions or payments they are requesting. Vague demands are often more dangerous as they allow the blackmailer to continually shift their goalposts.
- Resist Immediate Compliance: Your instinct might be to comply immediately to make the threat disappear. However, this rarely works. Giving in often emboldens the blackmailer and signals that you are a willing target. It’s essential to resist the urge to pay or concede without a clear plan.
Secure Your Digital Accounts and Devices
Blackmailers often gain access to sensitive information through compromised digital accounts. Therefore, securing your online presence is paramount.
- Change Passwords: Immediately change passwords for all your critical online accounts, including email, social media, banking, cloud storage, and any platform where you store personal or sensitive data. Use strong, unique passwords for each service. Consider using a password manager to help generate and store these complex passwords.
- Enable Two-Factor Authentication (2FA): Where available, enable 2FA on all your accounts. This adds an extra layer of security, requiring a code from your phone or a security key in addition to your password, making it significantly harder for unauthorized access.
- Review Privacy Settings: Go through the privacy settings on all your social media accounts and other online platforms. Limit who can see your posts, personal information, and connections. Restrict visibility of your friends lists, photos, and location data.
- Scan for Malware: Run comprehensive scans on all your devices (computers, smartphones, tablets) using reputable antivirus and anti-malware software. This can help identify if your devices have been compromised with spyware or other malicious software.
- Back Up Your Data: Before making any significant changes, consider backing up your important data to an external drive or a secure cloud service. This ensures that even if your devices are compromised, you won’t lose critical personal information.
Assess the Authenticity of the Threat
It’s also important to critically evaluate whether the blackmailer actually possesses the material they claim to have. Sometimes, blackmail attempts are based on bluffs or outdated information.
- Look for Proof: Has the blackmailer provided any proof of the compromising material? If they’ve sent a screenshot or a snippet, analyze it carefully. Does it seem authentic? Could it be fabricated or manipulated?
- Consider the Source: How did the blackmailer obtain this information? If it came from a source that is generally unreliable or known for scams, it might be a bluff.
- Don’t Panic Based on Accusations: While you should take the threat seriously, avoid succumbing to panic based solely on the blackmailer’s assertions. Your careful assessment will guide your next steps.
Documenting the Blackmail and Gathering Evidence
In any legal or investigative process, evidence is king. Documenting every interaction with the blackmailer and gathering any available proof is crucial for building a strong case and increasing your chances of a positive resolution.
Maintain a Detailed Record of All Communications
Every interaction with the blackmailer is potential evidence. It’s vital to keep meticulous records of every message, call, or contact.
- Save All Messages: Do not delete any emails, text messages, social media messages, or any other form of communication from the blackmailer. Take screenshots of these messages, ensuring the date and time are visible.
- Record Phone Calls (Where Legal): If the blackmailer communicates via phone, and it is legal to do so in your jurisdiction, consider recording the conversations. If not, take detailed notes immediately after each call, including the date, time, duration, what was said, and any specific threats or demands made.
- Log Dates and Times: Keep a running log of all communications, noting the date, time, and method of contact. This chronological record can be invaluable for law enforcement.
- Note Any Specifics: Pay attention to any details the blackmailer volunteers, such as their perceived knowledge of your personal life, their online handles, or any clues about their identity. Even seemingly insignificant details could become important later.
- Avoid Contacting the Blackmailer Unnecessarily: While you need to document, avoid engaging in lengthy or emotional conversations. Keep interactions brief and focused on gathering information, if you choose to respond at all. Ideally, all communication should be handled by authorities or legal counsel once you’ve decided to report.
Preserve Digital and Physical Evidence
Beyond direct communication, there might be other forms of evidence that can support your case.
- Screenshots of Compromised Accounts/Content: If the blackmailer claims to have access to specific accounts or content, take screenshots if you can verify their claims (e.g., a screenshot of a private message they sent you, or a photo of your account settings they might have accessed).
- Financial Records (If Demands Involve Money): If the blackmailer demands money, do not pay, but be prepared to show financial records if you are asked to provide evidence of attempted transactions or any communication related to payments.
- Witnesses: If anyone else is aware of the blackmail attempt or has witnessed any suspicious activity related to it, their testimony could be important.
- Your Own Devices: Ensure your devices are handled carefully. Avoid deleting files or performing actions that could inadvertently destroy evidence.
Seek Digital Forensics Assistance (If Necessary)
In complex cases, especially those involving sophisticated hacking or the creation of fabricated evidence, you might consider seeking the help of digital forensics experts.

- Identify Compromises: Forensics can help determine how your accounts or devices were compromised, which can be crucial for law enforcement.
- Verify or Disprove Evidence: Experts can analyze alleged evidence to determine its authenticity and identify any signs of manipulation.
- Assist Law Enforcement: This specialized assistance can provide law enforcement with a more thorough understanding of the technical aspects of the blackmail.
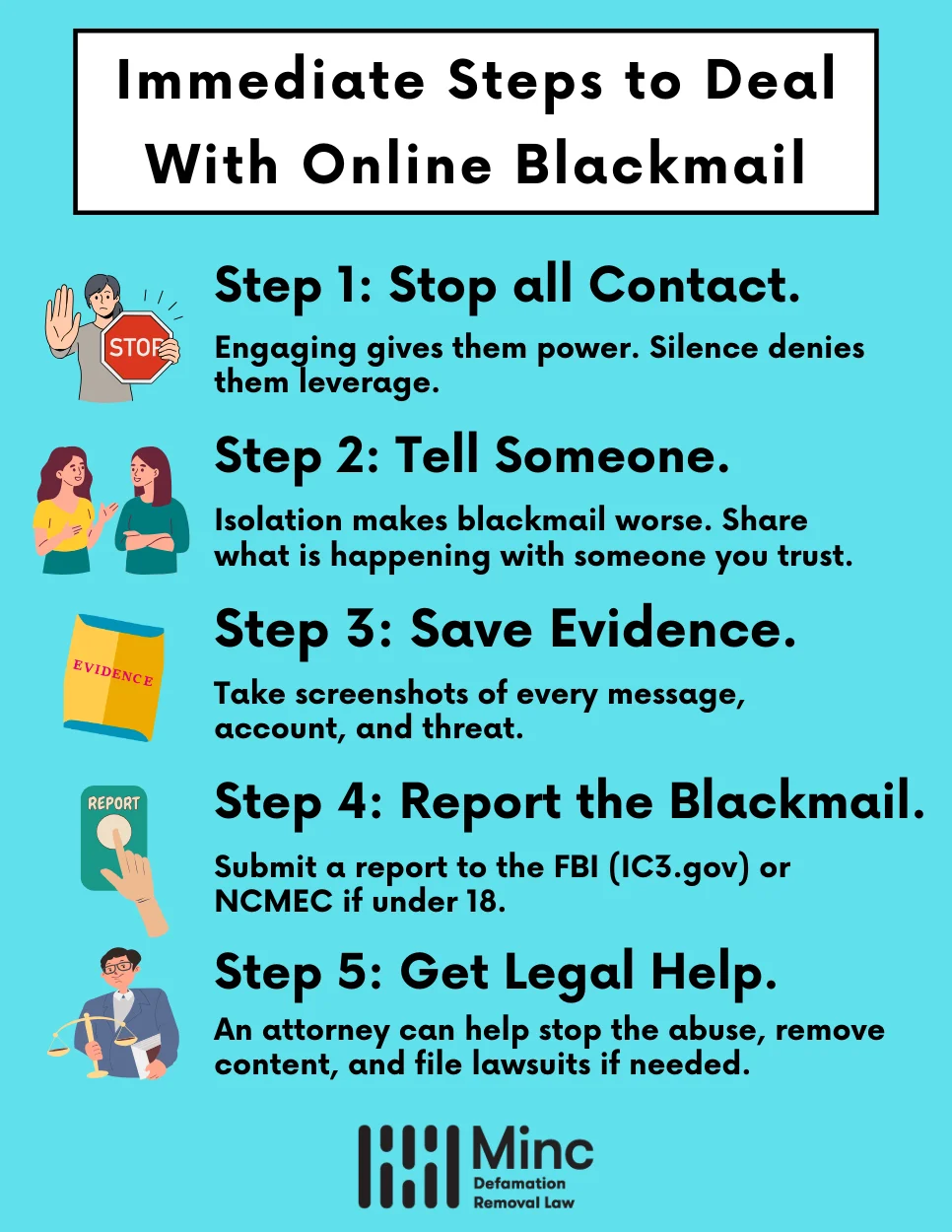
Reporting the Blackmail and Seeking Support
Once you have begun to secure your digital footprint and gather evidence, the next critical step is to report the blackmail to the appropriate authorities and seek both legal and emotional support.
Contact Law Enforcement
Blackmail is a criminal offense, and reporting it to the police is essential. They have the resources and legal authority to investigate and prosecute the perpetrator.
- Local Police Department: Your first point of contact should be your local police department. Provide them with all the documented evidence you have collected.
- Cybercrime Units: Many police forces have specialized cybercrime units that are equipped to handle digital extortion cases. Inquire if such a unit is available in your area.
- National Agencies: Depending on the severity and nature of the blackmail, national law enforcement agencies (e.g., FBI in the US, NCA in the UK) might also be relevant. Your local police can advise you on when to involve these agencies.
- Be Prepared to Cooperate: Law enforcement will likely ask for detailed information and your full cooperation throughout the investigation. Be honest and forthcoming.
Consult with Legal Counsel
A lawyer specializing in cybercrime, privacy law, or criminal defense can provide invaluable guidance.
- Understand Your Rights: A legal professional can explain your rights and the legal ramifications of the blackmail attempt.
- Navigate Legal Processes: They can help you understand the legal process and represent your interests if the case goes to court.
- Advise on Communication: They can advise you on how to communicate with the blackmailer, or if it’s best to cease all communication and let them handle it.
- Pursue Civil Remedies: Beyond criminal prosecution, a lawyer can explore options for civil remedies, such as seeking damages if you have suffered financial loss due to the blackmail.
Seek Emotional and Psychological Support
Being a victim of blackmail can be incredibly traumatizing. It’s vital to address the emotional toll this experience takes.
- Therapy and Counseling: Consider seeking professional help from a therapist or counselor. They can provide a safe space to process your emotions, develop coping mechanisms, and work through the trauma.
- Support Groups: Connecting with others who have experienced similar situations can be incredibly validating. Look for online or in-person support groups focused on victims of cybercrime or extortion.
- Trusted Friends and Family: While it can be difficult to share such a personal ordeal, confiding in a few trusted individuals can provide comfort and a sense of not being alone. Choose wisely who you share this with, as discretion is important.
- Self-Care: During this stressful period, prioritize self-care. Ensure you are getting enough sleep, eating well, and engaging in activities that help you relax and de-stress. This might seem difficult, but it’s crucial for your resilience.
Long-Term Strategies for Prevention and Recovery
Once the immediate crisis of blackmail has been addressed, it’s important to focus on long-term strategies for preventing future incidents and aiding in your recovery. This involves a continued commitment to digital security and learning from the experience.
Strengthen Your Online Defenses Continuously
The digital landscape is constantly evolving, and so are the methods used by cybercriminals. Proactive and ongoing security measures are your best defense.
- Regularly Update Software: Keep all your operating systems, applications, and antivirus software up to date. Updates often contain critical security patches that protect against newly discovered vulnerabilities.
- Be Wary of Phishing and Scams: Educate yourself and your family about common phishing tactics. Be suspicious of unsolicited emails, messages, or phone calls asking for personal information or financial details. Never click on suspicious links or download attachments from unknown sources.
- Practice Secure Browsing Habits: Use secure, encrypted connections (look for HTTPS in the URL) when browsing the internet, especially when entering sensitive information. Consider using a Virtual Private Network (VPN) for added security, especially on public Wi-Fi.
- Limit Information Sharing: Be mindful of the personal information you share online. The less information available publicly, the harder it is for malicious actors to exploit.
- Regularly Review Account Activity: Periodically check your bank statements, credit reports, and online account login histories for any unusual activity. Report any discrepancies immediately.
Learn from the Experience and Build Resilience
Every challenging experience, while painful, offers an opportunity for growth and increased resilience.
- Understand Your Vulnerabilities: Reflect on how the blackmail occurred. Were there specific vulnerabilities in your digital security, or information you shared that was later exploited? Understanding these points can help you plug those gaps.
- Develop a Crisis Plan: For future reference, consider developing a personal crisis plan for digital security incidents. This could include pre-identified contacts for law enforcement, legal counsel, and trusted IT professionals.
- Educate Others: Share your learnings with friends and family to help them avoid similar predicaments. Awareness is a powerful tool against digital threats.
- Reclaim Your Narrative: Blackmail seeks to control you through fear. As you recover, focus on reclaiming your narrative and not letting the experience define you. Your ability to overcome this challenge is a testament to your strength.

Maintain Vigilance and Seek Ongoing Support
Recovery is not always a linear process. Maintaining vigilance and continuing to seek support when needed is crucial for long-term well-being.
- Stay Informed: Keep abreast of current cyber threats and security best practices through reputable technology news sources and cybersecurity advisories.
- Don’t Hesitate to Seek Help: If you experience lingering anxiety, fear, or any other emotional distress, do not hesitate to reach out to your therapist, counselor, or support network.
- Celebrate Progress: Acknowledge and celebrate the steps you’ve taken towards recovery and rebuilding your sense of security. This journey is a marathon, not a sprint.
Being subjected to blackmail is a violation of your privacy and security. By taking a proactive, informed, and strategic approach, you can effectively counter the threat, protect yourself, and begin the process of healing and recovery. Remember, you are not alone, and help is available.
