The digital landscape, while offering unprecedented connectivity and access to information, is also a fertile ground for unwanted intrusions. Among the most pervasive and often annoying of these are “spam” messages. The term itself has become a ubiquitous descriptor for unsolicited electronic communications, primarily in the form of email, but its reach extends to other platforms as well. Understanding what constitutes spam, why it proliferates, and how it impacts individuals and organizations is crucial for navigating the modern digital world effectively and securely.
Defining Spam: Beyond the Unsolicited Email
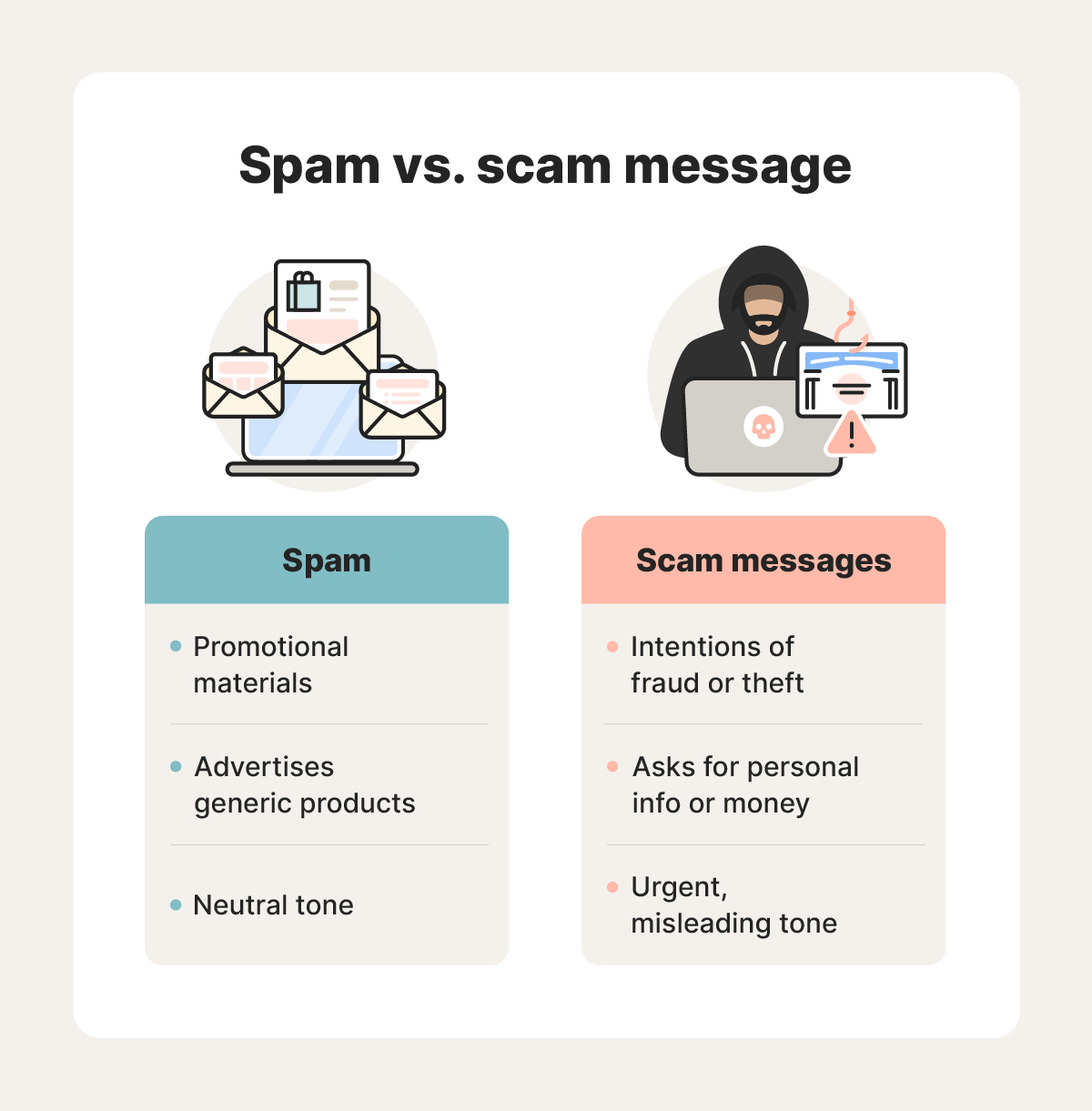
At its core, spam refers to any mass unsolicited message, typically sent for commercial purposes, that aims to advertise, scam, or distribute malware. While email remains the most common vector for spam, the definition has broadened to encompass:

Email Spam
This is the classic and most widely recognized form of spam. It includes marketing emails for products or services you haven’t subscribed to, phishing attempts designed to steal personal information, and chain letters or hoaxes. These emails are sent in bulk, often to millions of recipients, with the hope that a small percentage will engage, leading to profit for the sender. The volume of email spam is staggering, with estimates suggesting that a significant portion of all email traffic is unsolicited.
Instant Messaging Spam
Similar to email, instant messaging platforms can be flooded with unsolicited messages. These can range from advertisements for dubious products to attempts to engage users in fraudulent schemes. The immediacy of instant messaging can make these spam messages particularly intrusive.
Social Media Spam
Platforms like Facebook, Twitter, Instagram, and LinkedIn are also targets for spammers. This can include fake profiles promoting scams, repetitive comments or messages intended to spread misinformation or advertisements, and phishing links disguised as legitimate posts.
Search Engine Spam (Spamdexing)
This refers to the practice of manipulating search engine rankings to promote unwanted websites. Spammers might create content that is keyword-stuffed or uses other deceptive techniques to appear higher in search results, often leading users to sites filled with intrusive ads or malware.
Forum and Comment Spam
Many online forums and blog comment sections are targeted by spammers who post irrelevant or promotional messages to drive traffic to their own sites. This degrades the user experience and makes it difficult to find genuine discussions.
SMS Spam
Unsolicited text messages, often promoting deals, services, or even phishing attempts, are a common nuisance on mobile devices. These can be particularly alarming due to their direct and immediate nature.
The Motivations Behind Spam
The continued prevalence of spam, despite numerous efforts to combat it, stems from a variety of motivations, primarily driven by profit and malicious intent.
Commercial Advertising and Marketing
For legitimate businesses, spam can be a cost-effective, albeit often unethical, way to reach a large audience. By sending out mass emails or messages, they hope to attract new customers without the expense of targeted advertising campaigns or building opt-in subscriber lists. However, this approach often backfires, damaging brand reputation and leading to increased spam filtering.
Fraudulent Schemes and Phishing
A significant portion of spam is designed to deceive recipients into revealing sensitive personal or financial information. Phishing emails, for instance, often mimic legitimate communications from banks, online retailers, or government agencies, tricking users into clicking malicious links or providing login credentials. These scams can lead to identity theft, financial loss, and other serious consequences.
Malware Distribution
Spam is also a primary vehicle for distributing malicious software. Emails can contain infected attachments or links that, when clicked, download viruses, ransomware, spyware, or other harmful programs onto the victim’s device. This can compromise data security, disrupt operations, and lead to significant financial damage.
Hoaxes and Misinformation
Not all spam is purely commercial or fraudulent. Some spam campaigns aim to spread misinformation, urban legends, or chain letters. While these may seem less harmful, they can contribute to a general sense of digital clutter and can sometimes be used as a precursor to more malicious activities.
Political or Ideological Agitation
In some cases, spam can be used to spread political propaganda or to disrupt online discourse by flooding platforms with specific messages or opinions.
The Impact of Spam
The consequences of spam extend far beyond mere annoyance. It poses significant challenges for individuals, businesses, and the internet infrastructure itself.
For Individuals
Spam consumes valuable time and mental energy as users sift through unwanted messages. It increases the risk of falling victim to phishing scams or malware infections, leading to financial loss, identity theft, and compromised personal data. The constant barrage of spam can also lead to “email fatigue,” where users become desensitized to important communications.
For Businesses
Spam significantly impacts productivity. Employees waste time managing and deleting spam, and IT departments bear the burden of implementing and maintaining spam filters. Furthermore, successful spam attacks can lead to data breaches, reputational damage, and significant financial costs associated with recovery and remediation. For e-commerce businesses, spam can also dilute marketing efforts and erode customer trust.
For Internet Infrastructure
The sheer volume of spam traffic places a considerable strain on internet service providers (ISPs) and email servers. This increased traffic requires more bandwidth, processing power, and storage, leading to higher operational costs. Moreover, the constant battle against spam necessitates continuous development and refinement of anti-spam technologies, diverting resources from other important areas of network management.
Combating Spam: A Multi-faceted Approach
The fight against spam is an ongoing one, requiring a layered and collaborative approach involving individuals, technology providers, and regulatory bodies.
Individual Vigilance and Best Practices
The first line of defense often lies with the individual user. Being cautious about sharing email addresses, scrutinizing suspicious emails for red flags (e.g., poor grammar, generic greetings, urgent requests for personal information), avoiding clicking on unsolicited links or opening attachments from unknown senders, and regularly updating anti-virus software are crucial steps.
Technological Solutions
A range of technological solutions are employed to filter and block spam. These include:
- Spam Filters: Sophisticated algorithms used by email providers and security software analyze emails for spam-like characteristics, such as suspicious sender addresses, keywords, and patterns, and divert them to a junk or spam folder.
- Blacklists and Whitelists: These are lists of known spam senders (blacklists) or trusted senders (whitelists) that help in filtering messages.
- Bayesian Filtering: This statistical method learns from user feedback to identify and classify spam with increasing accuracy over time.
- CAPTCHAs (Completely Automated Public Turing test to tell Computers and Humans Apart): These are often used on web forms to distinguish human users from automated bots that send spam.
- Sender Policy Framework (SPF), DomainKeys Identified Mail (DKIM), and Domain-based Message Authentication, Reporting & Conformance (DMARC): These email authentication protocols help to verify the legitimacy of email senders and reduce spoofing.
Regulatory and Legal Measures
Governments worldwide have enacted legislation to combat spam, such as the CAN-SPAM Act in the United States and the GDPR (General Data Protection Regulation) in Europe, which impose penalties for sending unsolicited commercial emails and require consent for marketing communications. These regulations aim to hold spammers accountable and provide legal recourse for victims.

Industry Collaboration
Internet service providers, email providers, security companies, and technology developers collaborate to share information about spam trends, new spamming techniques, and best practices for mitigation. This collective effort is essential for staying ahead of evolving spam threats.
In conclusion, spam represents a persistent challenge in our increasingly digital world. By understanding its nature, motivations, and impacts, and by employing a combination of individual vigilance, advanced technological solutions, and supportive regulatory frameworks, we can collectively work towards a cleaner, safer, and more productive online environment.
