As the drone industry shifts from manually piloted quadcopters to fully autonomous, remote-operated ecosystems, the underlying networking infrastructure has become as critical as the flight hardware itself. Central to this technical evolution is the ability to manage ground control stations, edge computing servers, and remote sensing workstations from anywhere in the world. This brings us to a fundamental question for drone system architects and innovators: What port is RDP, and how does it integrate into the modern drone technology stack?
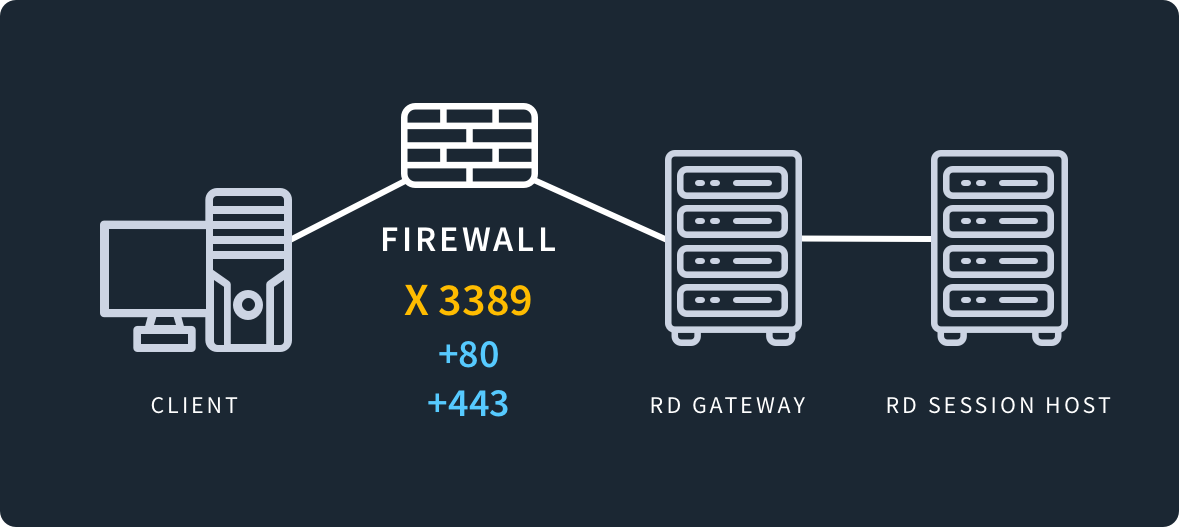
Remote Desktop Protocol (RDP) typically operates on Port 3389. While this might seem like a standard IT detail, in the context of high-tech drone operations—such as “Drone-in-a-Box” solutions, autonomous mapping, and remote sensing—understanding Port 3389 is essential for maintaining secure, low-latency control over the digital infrastructure that keeps UAVs in the air.
Understanding the Role of Port 3389 in Remote UAV Operations
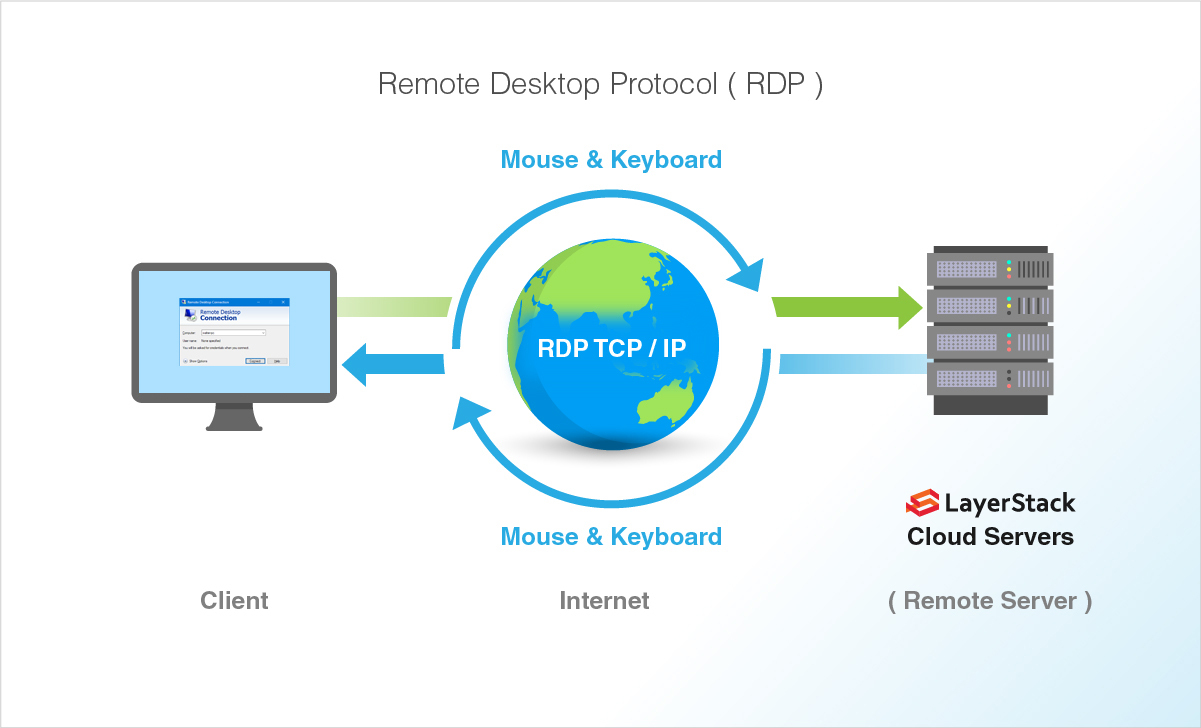
In the niche of drone tech and innovation, Remote Desktop Protocol (RDP) is a proprietary protocol developed by Microsoft that provides a user with a graphical interface to connect to another computer over a network connection. For drone professionals, that “other computer” is often a high-powered Ground Control Station (GCS) or a dedicated server located at a remote flight site.
What is RDP Port 3389?
Port 3389 is the default communication channel for RDP. It utilizes both TCP (Transmission Control Protocol) and UDP (User Datagram Protocol) to facilitate the transmission of display data, keyboard inputs, and mouse movements. In drone innovation, this port is the gateway used by engineers to remotely log into field-deployed computers to update flight software, monitor autonomous missions in real-time, or retrieve massive datasets from remote sensing equipment.
When a drone operator in a central office needs to check the health of a remote docking station located hundreds of miles away, they likely initiate a connection through Port 3389. This allows them to see the desktop of the remote machine as if they were sitting right in front of it, providing a level of control that standard command-line interfaces cannot match.
Why Remote Desktop Protocols Matter for Modern Drones
The advancement of autonomous flight and “beyond visual line of sight” (BVLOS) operations has necessitated a move toward centralized management. We are no longer looking at a single pilot with a handheld controller; we are looking at fleets of drones managed via cloud-based platforms.
RDP serves as the bridge between the physical drone hardware and the human supervisor. By utilizing Port 3389, innovators can deploy complex AI algorithms and heavy processing tasks to localized edge computers at the drone’s launch site, while still maintaining full administrative access from a centralized hub. This separation of hardware and human presence is the cornerstone of scalable drone technology.
RDP in the Ecosystem of Autonomous Flight and Mapping
The intersection of RDP and drone innovation is most visible in the realms of autonomous flight systems and advanced mapping. These sectors require immense computational power and high-speed data transfer, often necessitating remote access to specialized hardware.
Remote Ground Control Stations (GCS)
Modern autonomous drones often rely on a Ground Control Station that acts as the “brain” on the ground. This station processes telemetry, manages obstacle avoidance data, and communicates with the drone via radio links. However, for a truly autonomous “Drone-in-a-Box” system to work, there must be a way for a remote technician to intervene if the software hangs or if a configuration change is needed.
Using Port 3389, a technician can remotely access the GCS to calibrate sensors, adjust flight paths, or troubleshoot AI follow-mode parameters. Without this remote access, every minor software glitch would require a physical site visit, which is economically unfeasible for large-scale deployments in sectors like agriculture, mining, or offshore wind farm inspection.
Data Processing and Remote Sensing Workflows
Mapping and remote sensing are perhaps the most data-intensive applications in the drone industry. A single flight using LiDAR (Light Detection and Ranging) or multispectral sensors can generate gigabytes of raw data. Transferring this data to the cloud for processing is often slow and costly.
Instead, many innovators use powerful on-site servers to process the data immediately after the drone lands. By opening Port 3389 (ideally through a secure tunnel), data scientists can remotely access these processing units to run complex photogrammetry software or AI-driven analysis. This allows for “edge-to-cloud” innovation, where the heavy lifting is done locally, but the insights are managed remotely via RDP.

Security Implications: Protecting Drone Infrastructure from Unauthorized Access
While Port 3389 is incredibly useful, it is also one of the most targeted ports by malicious actors. In the world of drone technology, a compromised RDP port isn’t just a data risk—it is a physical safety risk. If an unauthorized user gains access to a Ground Control Station via an exposed Port 3389, they could potentially hijack a drone, steal sensitive mapping data, or disable critical infrastructure.
Vulnerabilities of Port 3389
The primary danger with Port 3389 is that it is often left “open” to the public internet. Automated bots constantly scan the web for open RDP ports to launch brute-force attacks or exploit known vulnerabilities in the protocol. For a drone operator, an open port is a neon sign inviting intrusion.
Because RDP provides high-level administrative access, a successful breach gives the attacker the keys to the kingdom. They could alter flight logs, change “no-fly zone” parameters, or even brick the drone’s firmware. As drone technology becomes more integrated into national infrastructure (such as power line inspections), the security of the ports used for remote management becomes a matter of national security.
Best Practices for Secure Drone Networking
To leverage the power of RDP without falling victim to cyberattacks, drone innovators must implement rigorous security protocols.
- Non-Standard Ports: One of the simplest “security by obscurity” measures is to change the default RDP port from 3389 to a random high-numbered port. While this won’t stop a determined hacker, it prevents basic automated scans from finding the entry point.
- VPN and SSH Tunneling: Professional drone operations should never expose Port 3389 directly to the internet. Instead, operators should use a Virtual Private Network (VPN) or an SSH tunnel. This requires the user to authenticate with a secure network before they can even see that the RDP port exists.
- Network Level Authentication (NLA): Enabling NLA ensures that the user must authenticate with the network before a full RDP session is established. This significantly reduces the risk of denial-of-service (DoS) attacks and certain exploits.
- IP Whitelisting: Since drone base stations are usually in fixed locations, or connected via specific cellular gateways, innovators can whitelist only specific IP addresses to access Port 3389. This ensures that only the headquarters or specific authorized tablets can initiate a remote session.
Advanced Alternatives and the Future of Remote Connectivity in UAV Tech
As we look toward the future of drone innovation, the reliance on Port 3389 and RDP is evolving. While RDP is excellent for administrative tasks, it was not originally designed for the high-latency, low-bandwidth environments sometimes found in remote field operations (such as drones operating on 4G/5G links in rural areas).
The Shift Toward Web-Based Interfaces and API Control
Many of the newest innovations in the drone space are moving away from traditional desktop-based control in favor of web-enabled dashboards. By using protocols like WebRTC for low-latency video and HTTPS for control commands, developers can bypass Port 3389 entirely for day-to-day operations. These web interfaces are often easier to secure and provide a more responsive experience for the operator.
However, even in these systems, RDP remains the “fail-safe” or “deep-maintenance” tool. When the web dashboard fails, the ability to drop into the OS level via Port 3389 is invaluable for recovery.
Cloud-Native Solutions and Edge Computing
The next frontier of drone tech involves “Cloud-Native” drones. In this model, the drone is essentially an IoT (Internet of Things) device that communicates directly with cloud servers. In this architecture, Port 3389 is less about controlling the drone and more about managing the cloud instances that process the drone’s telemetry and AI vision data.
As AI follow-modes and autonomous obstacle avoidance become more sophisticated, the processing is increasingly split between the drone’s onboard computer and a remote “digital twin” running on a server. Managing these digital twins requires robust remote access, ensuring that the innovation cycle—from flight data collection to AI model retraining—remains seamless.
Conclusion
Understanding “what port RDP” is is more than just an IT trivia point; it is a fundamental requirement for anyone building the future of autonomous drone systems. Port 3389 is the silent workhorse of remote UAV management, enabling the remote ground stations, data processing units, and autonomous hives that define modern aerial innovation.
By mastering the technical nuances of RDP, drone innovators can ensure that their systems are not only highly functional and remotely accessible but also resilient against the growing threats of the digital landscape. As we move closer to a world of fully autonomous, “set-and-forget” drone fleets, the secure and efficient use of remote protocols like RDP will be the differentiator between successful scaling and technical failure. Whether it is updating a mapping algorithm from halfway across the globe or troubleshooting a sensor in the middle of a forest, Port 3389 remains a vital link in the chain of drone technology.
