The world of drones has rapidly expanded beyond hobbyist recreation, transitioning into a crucial technological frontier driving innovation across countless industries. From precision agriculture and infrastructure inspection to remote sensing and autonomous delivery, Unmanned Aerial Vehicles (UAVs) are reshaping our operational landscapes. As these aerial platforms become more sophisticated, interconnected, and autonomous, a fundamental question emerges from the depths of their digital infrastructure: “what port is HTTPS?”
While seemingly a query rooted in traditional network protocols, when viewed through the lens of drone technology and innovation, this question transcends its literal interpretation. It compels us to consider not just a specific TCP/IP port number, but rather the critical communication channels, data gateways, and interfaces within the drone ecosystem that demand the highest levels of security—security akin to what HTTPS provides for web browsing. In essence, “what port is HTTPS” becomes a metaphor for identifying and fortifying every vulnerable conduit through which sensitive drone data and commands travel, ensuring the integrity, privacy, and reliability of our increasingly intelligent aerial assets. This article delves into the paramount importance of secure communication, drawing parallels with HTTPS, for the burgeoning field of drone tech and innovation.
The Evolving Landscape of Drone Connectivity and Data Exchange
The modern drone is far more than just a flying camera; it’s a sophisticated, connected computing platform generating and transmitting vast amounts of data. This evolution necessitates an intricate web of communication protocols and data exchange points, each presenting a potential “port” that requires robust security measures.
Beyond Line-of-Sight: The Need for Robust Remote Communication
Early drones primarily relied on direct radio frequency (RF) links for line-of-sight (LOS) control. However, the true promise of drone innovation lies in operations beyond visual line of sight (BVLOS) and in large-scale fleet management. This requires drones to communicate reliably over greater distances, often leveraging cellular networks (4G/5G), satellite links, and even mesh networks. These advanced communication methods transform the drone from a simple remote-controlled device into a node within a larger, often internet-connected, system. Real-time telemetry, high-definition video feeds, mission updates, and emergency commands must traverse these channels, making their security non-negotiable. Without secure “ports” for this data, BVLOS operations become inherently risky, susceptible to interference, interception, or malicious takeover.
The Interconnected Drone Ecosystem: Sensors, Ground Stations, and Cloud Platforms
The journey of data in a modern drone ecosystem is complex. It begins with an array of onboard sensors—cameras, LiDAR, GPS, IMUs, environmental sensors—collecting raw data. This data is processed by the drone’s flight controller and onboard computing units before being transmitted to various destinations:
- Drone to Controller: The traditional link for piloting commands and basic telemetry.
- Drone to Ground Station: More sophisticated ground control systems (GCS) might receive detailed mission data, high-resolution imagery, or even allow for real-time payload control.
- Drone to Cloud: Increasingly, drones are designed to upload data directly to cloud-based platforms for storage, advanced processing, AI analysis, and long-term management.
- Controller/Ground Station to Cloud/Internet: Operators often use web or mobile applications to manage missions, access processed data, or update drone firmware, connecting through the internet to cloud services.
- Drone to Drone (Swarm Operations): In future autonomous fleets, drones will communicate directly with each other to coordinate actions, share sensor data, and avoid collisions.
Each of these data exchange points represents a “port” or a communication gateway. Just as HTTPS secures web traffic between a browser and a server, these drone communication pathways require comparable end-to-end encryption, authentication, and integrity checks to safeguard the entire data lifecycle.
Why Security Matters: Protecting Drone Operations and Data Integrity
The integration of drones into critical infrastructure, sensitive operations, and data-intensive applications elevates security from a desirable feature to an absolute imperative. The consequences of insecure drone operations can range from financial losses and privacy breaches to catastrophic accidents and national security threats.
Preventing Unauthorized Access and Cyber Threats
An unsecured drone “port” is an open invitation for cyber adversaries. Malicious actors could exploit vulnerabilities to:
- Hijack Drone Control: Gaining unauthorized control of a drone during a mission could lead to theft of the drone itself, reconnaissance of restricted areas, or even using the drone as a weaponized platform.
- Spoofing and Jamming: Interfering with GPS signals (spoofing) or blocking communication channels (jamming) can disorient a drone, force it to land, or cause it to crash.
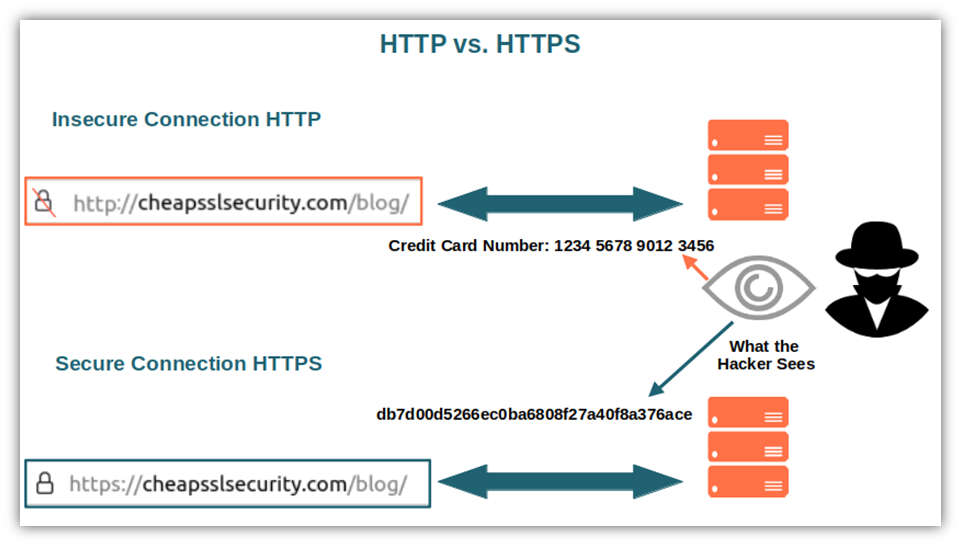
- Data Interception: Capturing sensitive data streams, such as high-resolution imagery of industrial facilities, thermal signatures, or personal identifiable information, constitutes a significant risk.
- Malware Injection: Compromising the drone’s operating system or firmware can lead to persistent backdoors, data manipulation, or denial-of-service attacks.
The concept of “what port is HTTPS” becomes vital here: it highlights the need for every communication interface to be rigorously authenticated and encrypted, ensuring that only authorized entities can interact with the drone and that its commands and data cannot be tampered with.
Ensuring Data Confidentiality and Privacy
Drones collect a treasure trove of data—from detailed topographical maps and crop health metrics to thermal images revealing energy inefficiencies and video footage for surveillance. Much of this data is confidential, proprietary, or subject to strict privacy regulations (e.g., GDPR, CCPA).
- Proprietary Business Data: For commercial entities, aerial data might reveal trade secrets, operational weaknesses, or competitive intelligence.
- Personal Privacy: When drones collect visual or other sensory data in public or private spaces, robust security is essential to protect individual privacy and prevent unauthorized access or misuse of that data.
- Regulatory Compliance: Industries like energy, utilities, and public safety are subject to stringent regulations regarding data handling. Secure drone communication ensures compliance and mitigates legal risks.
The secure “ports” are thus crucial for maintaining the confidentiality of this data during transit and storage, preventing unauthorized viewing or exfiltration.
Maintaining Command and Control Integrity
For autonomous drones, the integrity of command and control (C2) links is paramount. A drone executing an autonomous mission, such as inspecting a power line or delivering medical supplies, relies entirely on the accuracy and security of its programming and real-time instructions. If these C2 “ports” are compromised, the drone could deviate from its mission, endanger property or lives, or fail to respond to emergency overrides. Secure communication ensures that every command received by the drone is authentic, untampered, and originates from an authorized source, mirroring the trust model that HTTPS establishes for web applications.
HTTPS and its Parallels: Architecting Secure Communication Channels
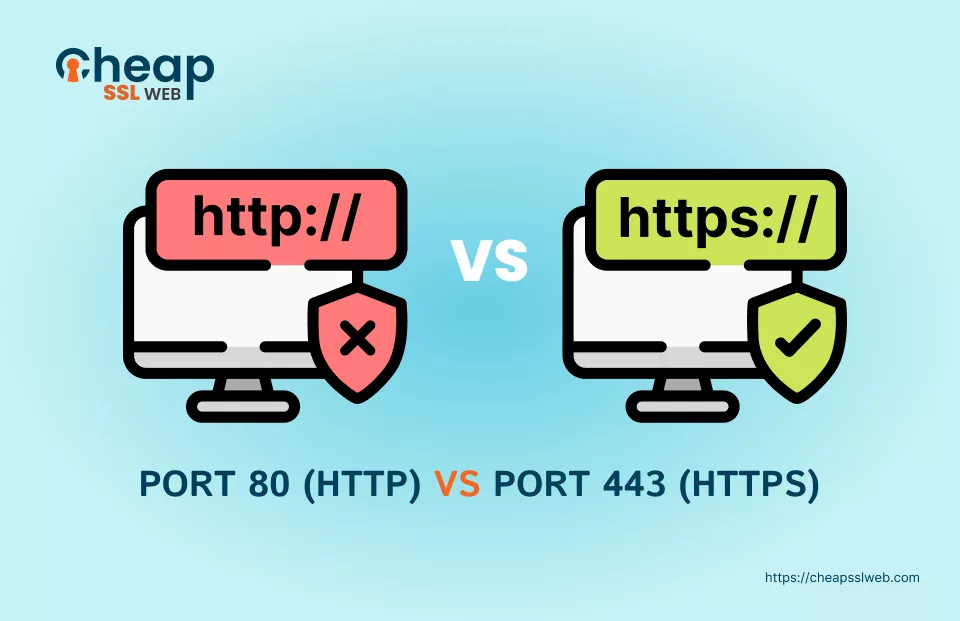
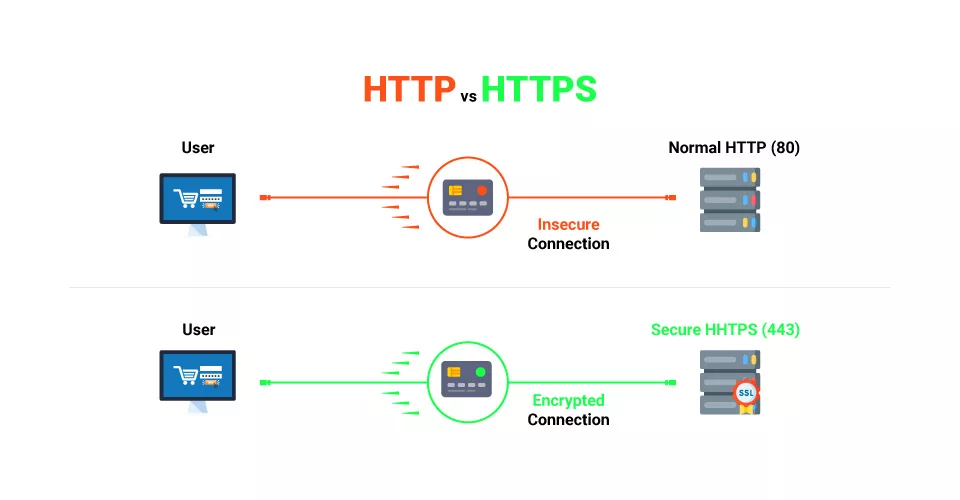
HTTPS, or Hypertext Transfer Protocol Secure, is the standard for secure communication over a computer network, widely used for internet security. It achieves this through encryption and authentication, primarily via TLS (Transport Layer Security) or its predecessor SSL (Secure Sockets Layer). While drones don’t necessarily use “HTTPS” directly for all internal communications, the principles it embodies are universally applicable and serve as a blueprint for securing drone “ports.”
The Role of Encryption in Drone Data Streams
At its core, HTTPS uses encryption to scramble data, making it unreadable to anyone who intercepts it without the correct decryption key. In drone technology, this principle is applied to:
- Telemetry Data: Encrypting flight parameters (altitude, speed, GPS coordinates) ensures that unauthorized parties cannot track a drone’s precise movements or infer its mission.
- Video and Sensor Feeds: Real-time video streams, thermal imagery, or LiDAR data often contain sensitive information. Encrypting these feeds prevents eavesdropping and protects the confidentiality of the observations.
- Firmware Updates: Over-the-air (OTA) firmware updates are convenient but can be a major vulnerability. Encrypting the update package and verifying its authenticity prevents malicious firmware injection.
- Command Payloads: Critical commands sent to the drone (e.g., “return to home,” “deploy payload”) must be encrypted to prevent unauthorized command injection or modification in transit.
Implementing strong, industry-standard encryption protocols across all these “ports” ensures that even if data is intercepted, it remains unintelligible and useless to attackers.
Secure APIs and Cloud Integration for Drone Platforms
Modern drone operations often rely on sophisticated software platforms for mission planning, data analysis, and fleet management. These platforms frequently integrate with cloud services and third-party applications via Application Programming Interfaces (APIs). These APIs are critical “ports” for data exchange, and their security is paramount.
- Authenticated Access: Just as HTTPS requires certificates to verify server identity, secure drone APIs demand robust authentication mechanisms (e.g., OAuth 2.0, API keys) to ensure only authorized applications or users can access drone data or issue commands.
- Encrypted Endpoints: All communication between drone software, ground stations, and cloud services through APIs must be encrypted using TLS/SSL, mirroring the HTTPS standard. This protects data as it flows between different components of the ecosystem.
- Access Control: Granular access controls dictate what data a specific user or application can access and what actions they can perform. This limits the blast radius in case a “port” is compromised.
By securing these API “ports” with HTTPS-like principles, drone innovation can leverage the power of cloud computing and diverse applications without sacrificing security.
Firmware Over-the-Air (FOTA) Updates and Secure Boot
The ability to update drone firmware remotely (FOTA) is essential for deploying new features, patching vulnerabilities, and improving performance. However, this convenience introduces a significant security risk if not handled meticulously. Secure FOTA leverages principles similar to HTTPS for secure software distribution:
- Digital Signatures: Firmware updates are digitally signed by the drone manufacturer. The drone verifies this signature before applying the update, ensuring that the firmware package is authentic and hasn’t been tampered with. This is analogous to a web browser verifying an HTTPS certificate.
- Encrypted Transmission: The firmware package itself is transmitted over an encrypted channel, preventing interception and modification during download.
- Secure Boot: Many advanced drones implement a “secure boot” process, where the drone’s processor only loads firmware that has been cryptographically signed by a trusted authority. This prevents the drone from booting with unauthorized or malicious software, protecting the lowest “port” of the drone’s operating system.
These mechanisms ensure that the foundational software running the drone is trustworthy, protecting it from attacks aimed at its very core.
Implementing Secure “Ports” in Next-Gen Drone Innovations
As drones become more autonomous and integrate into critical infrastructure, the drive for innovative security solutions intensifies. The question “what port is HTTPS” will continue to evolve, pushing the boundaries of what secure communication entails.
Edge Computing and Secure Onboard Processing
To minimize latency and reduce reliance on constant cloud connectivity, next-gen drones are increasingly incorporating powerful edge computing capabilities. This means more data processing happens directly on the drone itself. Securing these onboard “ports” is crucial:
- Hardware Security Modules (HSMs): Dedicated hardware components can be integrated into drones to securely store cryptographic keys, perform encryption/decryption, and protect sensitive data at rest and during processing on the edge.
- Secure Enclaves: Within the drone’s processor, secure enclaves can create isolated environments where critical data and algorithms (e.g., AI models for object recognition) can operate without being exposed to the rest of the system, even if other parts are compromised.
- Data Minimization: Processing data at the edge allows drones to extract only relevant information and transmit aggregated, anonymized, or encrypted summaries, reducing the amount of sensitive raw data flowing through external “ports.”
Blockchain and Decentralized Security Concepts
Blockchain technology, with its immutable ledger and decentralized nature, offers intriguing possibilities for enhancing drone security, especially for autonomous fleets and data integrity.
- Tamper-Proof Logging: Mission logs, flight data, and maintenance records could be stored on a blockchain, creating an unalterable audit trail that verifies drone operations and data provenance.
- Secure Drone Identity: Each drone could have a unique, cryptographically secured identity on a blockchain, enabling secure authentication and authorization within a decentralized network of drones and ground stations.
- Smart Contracts for Autonomous Operations: Blockchain-based smart contracts could automate secure payments for drone services, define flight permissions, or trigger actions based on verified sensor data, ensuring integrity across complex, multi-party operations.
These innovations explore new dimensions of securing “ports” by distributing trust and creating verifiable, transparent records of drone interactions.
AI-Driven Threat Detection and Adaptive Security Measures
Artificial intelligence (AI) is not only enabling autonomous flight but also enhancing drone security. AI algorithms can analyze vast amounts of data from drone operations, communication patterns, and environmental factors to detect anomalies indicative of cyber threats.
- Behavioral Analysis: AI can learn normal drone behavior and communication patterns, flagging deviations that might suggest a hijacking attempt, data exfiltration, or jamming.
- Real-time Anomaly Detection: By continuously monitoring communication “ports” and data streams, AI can identify unusual data volumes, unexpected command sequences, or unauthorized network connections in real-time.
- Adaptive Response: In response to detected threats, AI systems could trigger autonomous security measures, such as switching communication channels, initiating emergency landing protocols, or alerting operators, creating an adaptive and resilient security posture for drone “ports.”
Conclusion
The question “what port is HTTPS” serves as a powerful metaphor for the pervasive need for robust security across the entire drone technology and innovation landscape. It transcends the specificity of a single network port, instead highlighting the critical importance of secure communication channels, authenticated data gateways, and integrity-protected interfaces throughout the drone ecosystem. From the secure transmission of flight commands and sensitive sensor data to the integrity of firmware updates and cloud integrations, every “port” must be fortified with the same rigorous principles that make HTTPS the bedrock of internet security.
As drones continue to push the boundaries of autonomy, connectivity, and data collection, the commitment to end-to-end security will not just be a feature, but a foundational requirement. Investing in encryption, authentication, secure boot mechanisms, and innovative approaches like edge computing and AI-driven threat detection will be crucial. By meticulously securing every “port” within the drone’s digital architecture, we can ensure that these remarkable flying machines fulfill their transformative potential, operating safely, reliably, and with the unwavering trust of industries and the public alike, ushering in a truly secure era of aerial innovation.
