The Social Security Number (SSN) is a cornerstone of American identity. For decades, this nine-digit identifier has been the key to unlocking a myriad of essential services, from employment and banking to healthcare and retirement benefits. Yet, in an era defined by ubiquitous digital connectivity and ever-evolving cyber threats, the very nature of our SSN’s role and its vulnerability has become a pressing concern. This article delves into what your Social Security Number truly represents today, the technological landscape that surrounds it, and the imperative for robust digital security practices to safeguard this invaluable piece of personal data.
The Enduring Significance of the Social Security Number
Originally conceived as a mechanism for tracking earnings for Social Security benefits, the SSN has transcended its initial purpose to become a de facto national identification number. Its ubiquity is undeniable, woven into the fabric of virtually every significant transaction and interaction within American society. Understanding its foundational role is crucial before examining its current implications.
From Social Security Administration to Universal Identifier
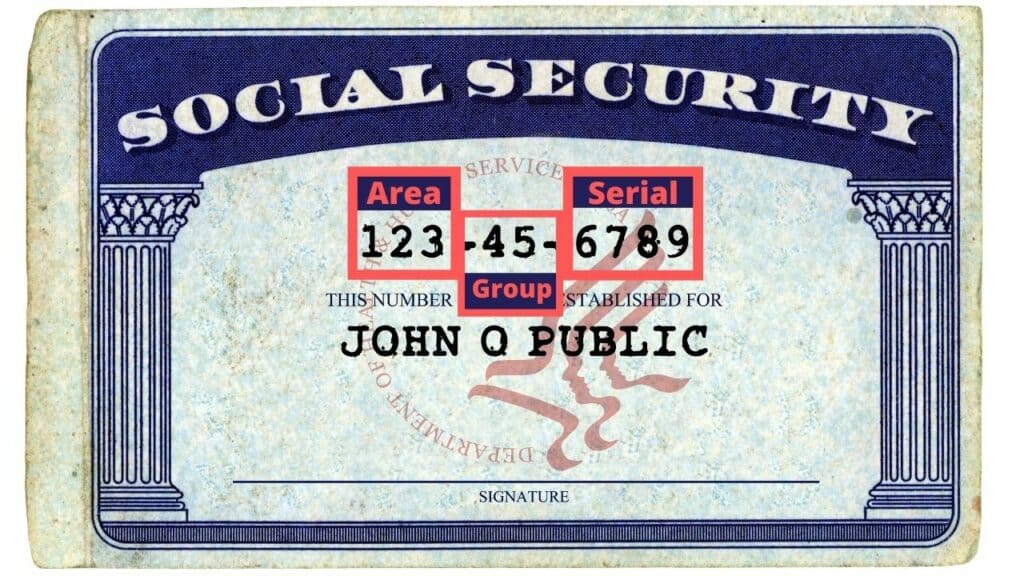
When President Franklin D. Roosevelt signed the Social Security Act into law in 1935, the primary objective was to establish a system for retirement pensions. The SSN was a vital tool for this purpose, ensuring accurate record-keeping of individual contributions and benefits. However, as the federal government expanded its reach and as other institutions sought reliable methods for identifying individuals, the SSN became an increasingly convenient and widely adopted identifier. This evolution was largely driven by the simplicity and uniqueness of the nine-digit structure, making it an efficient key for vast databases.
Key Functions and Reliance Across Sectors
The reliance on the SSN extends far beyond Social Security benefits. It is a prerequisite for:
- Employment: Employers require your SSN to report wages to the IRS and the Social Security Administration. Without it, you cannot legally be hired in most positions.
- Financial Services: Banks, credit card companies, and loan providers use your SSN to verify your identity, assess your creditworthiness, and comply with federal regulations.
- Healthcare: Healthcare providers often use your SSN to identify patients, process insurance claims, and manage medical records.
- Government Services: Obtaining a driver’s license, applying for government benefits (beyond Social Security), and filing taxes all necessitate the disclosure of your SSN.
- Background Checks: Many employers and landlords conduct background checks that rely on SSN verification to confirm identity and assess risk.
This pervasive integration means that the SSN is no longer just a number; it is intrinsically linked to an individual’s economic, social, and even personal life. The ease with which it can be used to establish identity has, unfortunately, also made it a prime target for those seeking to exploit or impersonate others.
The Digital Transformation and its Impact on SSN Security
The advent of the internet and the subsequent explosion of digital data have fundamentally altered how our SSNs are stored, transmitted, and accessed. This digital transformation, while bringing immense convenience, has also introduced unprecedented vulnerabilities.
Data Breaches: The Digital Achilles’ Heel
Perhaps the most significant threat to SSN security in the digital age stems from data breaches. As more organizations transition to digital record-keeping, the concentration of sensitive personal information, including SSNs, in centralized databases creates attractive targets for cybercriminals. These breaches can occur through various means, including:
- Hacking and Malware: Malicious actors exploit vulnerabilities in network security to gain unauthorized access to databases.
- Insider Threats: Disgruntled employees or individuals with legitimate access can misuse their privileges to steal data.
- Phishing and Social Engineering: Deceptive emails, websites, or phone calls designed to trick individuals into revealing their SSN and other personal details.
- Unsecured Data Transmission: Sending SSNs over unencrypted channels or through insecure networks can expose them to interception.
The consequences of such breaches are far-reaching. Stolen SSNs can be used to commit identity theft, open fraudulent credit accounts, file fake tax returns, and even access medical services, leaving victims with a tangled web of financial and legal problems that can take years to resolve.
The Rise of Identity Theft and Fraud
Identity theft is a direct byproduct of the digital vulnerability of SSNs. With access to a stolen SSN, along with other personally identifiable information (PII) often compromised in the same breaches, criminals can:
- Open new credit accounts: This can devastate a victim’s credit score.
- File fraudulent tax returns: To claim refunds.
- Obtain loans or mortgages: Leaving the victim responsible for repayment.
- Access existing accounts: Such as bank accounts or investment portfolios.
- Apply for government benefits: Including unemployment or stimulus payments.
The sophistication of these schemes continues to grow, with criminals leveraging advanced technological tools and techniques to evade detection. This underscores the critical need for individuals to be vigilant and proactive in protecting their SSN.
Technological Innovations in SSN Protection and Verification
In response to the escalating threats, technological advancements are playing a crucial role in both safeguarding SSNs and verifying their authenticity. While no system is entirely foolproof, these innovations offer enhanced layers of security and more sophisticated methods of authentication.

Advanced Encryption and Secure Data Storage
The fundamental principle of protecting sensitive data digitally is robust encryption. Technologies like:
- End-to-End Encryption: Ensures that data is encrypted at the point of origin and can only be decrypted by the intended recipient, making it unreadable to anyone in between.
- Tokenization: Replaces sensitive data with a unique identifier (a token) that has no exploitable meaning or value if breached. The actual SSN is stored securely elsewhere and only retrieved when absolutely necessary through a controlled process.
- Homomorphic Encryption: A groundbreaking technology that allows computations to be performed on encrypted data without decrypting it first. This has immense potential for processing sensitive information, like SSNs, without ever exposing the raw data.
These advanced encryption techniques are increasingly being adopted by financial institutions, healthcare providers, and government agencies to protect the SSNs entrusted to them.
Multi-Factor Authentication (MFA) and Biometric Verification
Beyond traditional password-based authentication, Multi-Factor Authentication (MFA) adds critical layers of security. This involves requiring users to provide two or more verification factors to gain access to an account or system. Common factors include:
- Something you know: Passwords, PINs.
- Something you have: A physical security key, a smartphone receiving a one-time code.
- Something you are: Biometrics like fingerprints, facial recognition, or iris scans.
The integration of biometrics with SSN verification is a growing trend. For example, when accessing sensitive online accounts that require SSN verification, a user might be prompted to provide a fingerprint scan in addition to their password. This significantly reduces the risk of unauthorized access even if an attacker has obtained the SSN itself.
The Role of AI and Machine Learning in Fraud Detection
Artificial intelligence (AI) and machine learning (ML) are proving to be invaluable allies in the fight against SSN-related fraud. These technologies excel at analyzing vast datasets and identifying patterns that would be impossible for humans to detect.
- Anomaly Detection: AI algorithms can monitor transaction patterns and identify deviations from a user’s typical behavior. For instance, if a sudden flurry of activity occurs on an account using a compromised SSN, the AI can flag it as suspicious.
- Predictive Analytics: ML models can learn from historical fraud data to predict the likelihood of fraudulent activity occurring. This allows organizations to proactively implement preventative measures.
- Behavioral Analysis: AI can analyze user interactions with digital platforms to detect subtle behavioral anomalies that might indicate an imposter.
By continuously learning and adapting, AI and ML are providing a dynamic defense against the ever-evolving tactics of cybercriminals.
Safeguarding Your Social Security Number in the Digital Realm
Given the inherent risks, individuals must take proactive steps to protect their SSN. The responsibility for safeguarding this critical identifier now rests on a shared foundation of robust organizational security and vigilant personal practices.
Personal Vigilance and Best Practices
While institutions are implementing advanced security measures, personal vigilance remains paramount. Key best practices include:
- Protecting Your Physical Documents: Treat your Social Security card and any other documents containing your SSN with extreme care. Do not carry your Social Security card in your wallet, and store documents containing your SSN in a secure location at home.
- Limiting Disclosure: Only provide your SSN when absolutely necessary and when you are confident about the legitimacy of the request. Ask why it is needed and how it will be protected.
- Monitoring Your Credit Reports: Regularly review your credit reports from Equifax, Experian, and TransUnion for any suspicious activity. You are entitled to a free credit report annually from each bureau.
- Using Strong, Unique Passwords and MFA: For all online accounts, especially those linked to financial or personal information, use strong, unique passwords and enable Multi-Factor Authentication whenever possible.
- Being Wary of Unsolicited Communications: Be suspicious of emails, phone calls, or texts asking for your SSN or other personal information. Government agencies and reputable organizations will rarely ask for this information unsolicited.
- Securing Your Home Network: Ensure your home Wi-Fi network is secured with a strong password and up-to-date encryption.
Understanding Your Rights and Reporting Suspicious Activity
Familiarizing yourself with your rights as a consumer regarding data privacy is crucial. In cases of suspected identity theft or data breaches, prompt action is essential.
- Reporting Identity Theft: If you believe your SSN has been compromised or used for fraudulent purposes, report it immediately to the Federal Trade Commission (FTC) at IdentityTheft.gov. The FTC provides a personalized recovery plan to help you resolve issues.
- Contacting Law Enforcement: In addition to the FTC, you may need to file a report with your local law enforcement agency.
- Notifying Affected Institutions: Contact the banks, credit card companies, or other institutions that may have been affected by the identity theft.
The Future of SSN Security: A Continuous Evolution
The role of the SSN, and the technologies used to protect it, will undoubtedly continue to evolve. As digital threats become more sophisticated, so too will the defensive measures. The ongoing development of privacy-enhancing technologies, decentralized identity solutions, and stronger regulatory frameworks will all contribute to a more secure digital future. However, the fundamental principles of vigilance, education, and proactive safeguarding of personal information will remain the bedrock of individual security in the digital age. Understanding “what my Social Security number” means in this context is the first, crucial step towards ensuring its protection.
