The landscape of wireless security is constantly evolving, and at the forefront of this evolution is Wi-Fi Protected Access 3 (WPA3). For those managing networks, particularly in environments where the seamless integration of new devices with existing infrastructure is paramount, understanding “WPA3 Personal Transition” is crucial. This mode represents a critical bridge, allowing devices that support the newer, more robust WPA3 standard to coexist with older devices still relying on WPA2. This coexistence is not merely a convenience; it’s a strategic necessity for network administrators aiming to enhance security without immediately forcing a complete overhaul of their client devices.
The transition period, facilitated by WPA3 Personal Transition mode, is designed to ease the adoption of WPA3. It acknowledges the reality that not all devices will be upgraded simultaneously. This interim phase allows for a gradual migration, mitigating potential disruptions and ensuring that older, yet still functional, equipment can maintain network access while the network itself benefits from the enhanced security features of WPA3. Without such a transitional approach, a mandatory switch to WPA3 could leave a significant portion of a user base unable to connect, leading to frustration and a potential security vacuum as users seek less secure workarounds. Therefore, understanding the nuances of WPA3 Personal Transition is key to navigating this important upgrade path effectively.
The Evolution of Wi-Fi Security: From WPA2 to WPA3
Wi-Fi security has come a long way since its inception. Early Wi-Fi standards relied on wired equivalent privacy (WEP), a protocol that was quickly found to be riddled with vulnerabilities, making it trivial for attackers to decrypt network traffic. This led to the development of Wi-Fi Protected Access (WPA), which offered improvements but was still susceptible to certain attacks. WPA2, introduced in 2004, significantly bolstered security with stronger encryption protocols like AES-CCMP, becoming the de facto standard for personal and enterprise networks for nearly two decades. However, as technology advanced and new attack vectors emerged, WPA2 also began to show its limitations.
Limitations of WPA2 and the Need for WPA3
Despite its long tenure and widespread adoption, WPA2 is not without its weaknesses. One of the most significant vulnerabilities is the Pre-Shared Key (PSK) authentication method, commonly used in WPA2 Personal networks. In this method, all devices on the network share a single password. While convenient, thisPSK can be susceptible to offline dictionary attacks. Attackers can capture the handshake packets exchanged between a device and the access point during authentication and then attempt to crack the password offline using vast lists of potential passwords. If the password is weak, it can be compromised relatively easily.
Furthermore, WPA2 lacks protection against deauthentication attacks, where an attacker can disrupt network connectivity for legitimate users, forcing them to reauthenticate and potentially exposing their handshake data. Another critical area where WPA2 falls short is in its handling of individual device security. All devices on a WPA2 Personal network share the same authentication credentials and encryption keys, meaning a compromise of one device could potentially expose the entire network to significant risks. This is particularly concerning with the proliferation of IoT devices, many of which have weaker security postures.
Introducing WPA3: A New Era of Security
WPA3 was developed by the Wi-Fi Alliance to address the shortcomings of WPA2 and provide a more robust and future-proof security solution. It introduces several key enhancements designed to improve both the confidentiality and integrity of Wi-Fi communications. WPA3 offers stronger encryption, better protection against brute-force attacks, and enhanced privacy features, particularly for public Wi-Fi networks. The overarching goal of WPA3 is to provide a more secure and resilient wireless experience for all users, from home networks to enterprise environments. This includes a suite of protocols, each designed for specific use cases and levels of security.
Understanding WPA3 Personal Transition Mode
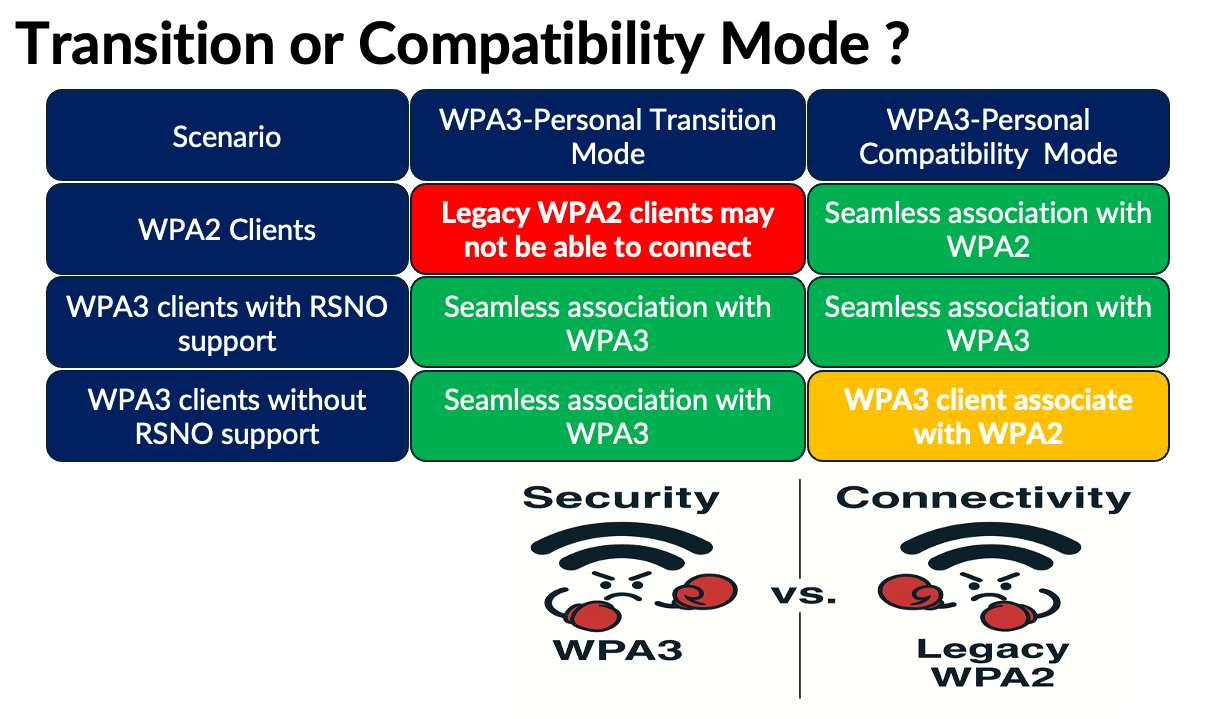
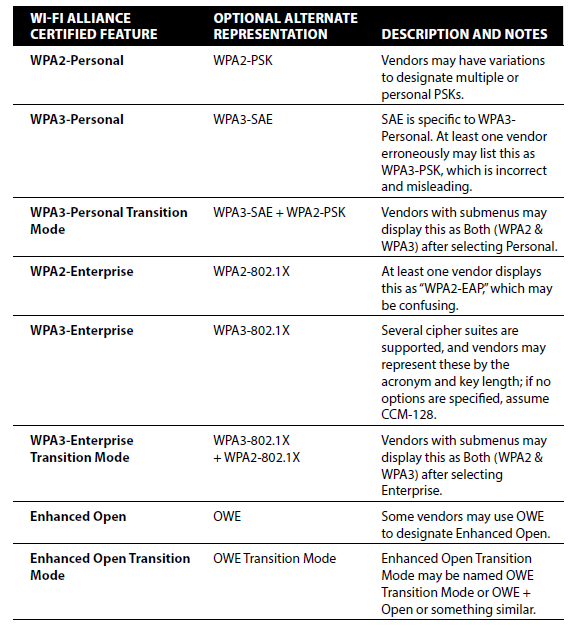
WPA3 Personal Transition mode is a crucial feature designed to facilitate the migration from WPA2 to WPA3. It allows for a mixed network environment where both WPA2 and WPA3-compatible devices can connect to the same access point. This mode is specifically intended to ease the transition process for users and organizations that cannot immediately upgrade all their wireless devices to support WPA3. It’s a practical solution that acknowledges the reality of device lifecycles and the cost and complexity associated with wholesale hardware replacements.
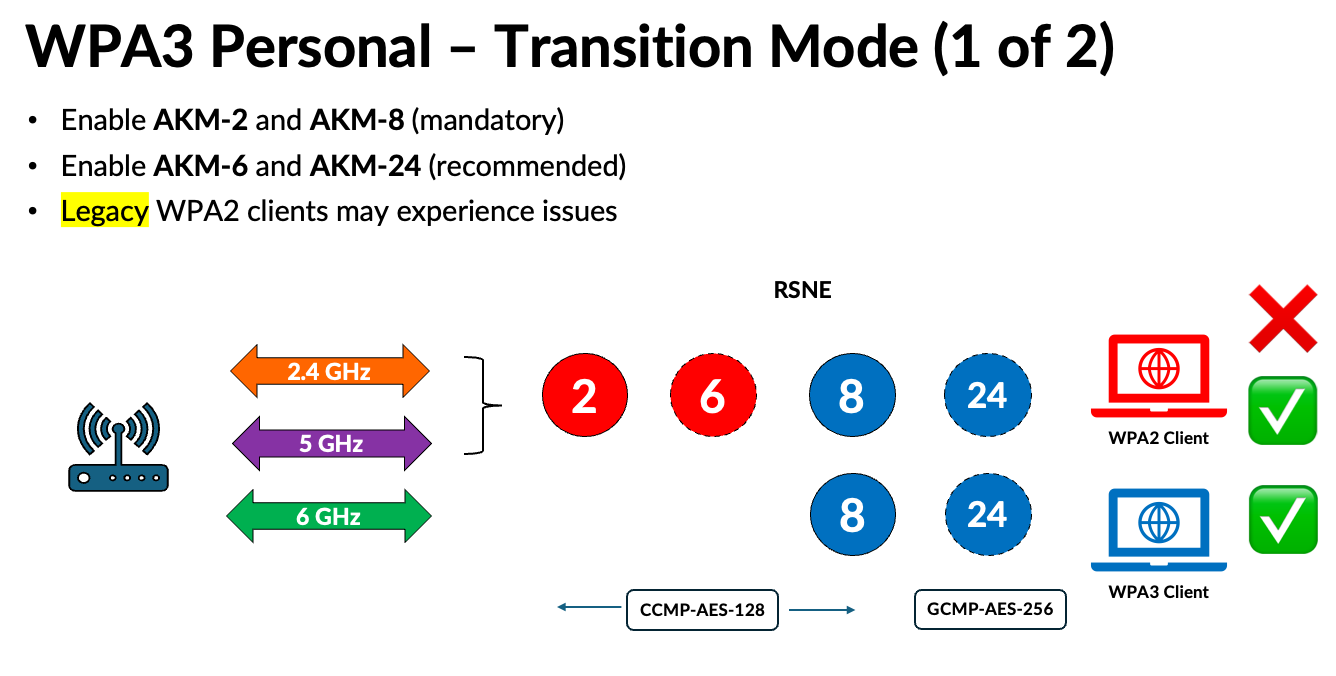
How WPA3 Personal Transition Works
In WPA3 Personal Transition mode, the access point advertises support for both WPA2 and WPA3. When a WPA2-compatible device attempts to connect, the access point negotiates a WPA2 connection, maintaining backward compatibility. Simultaneously, when a WPA3-compatible device attempts to connect, the access point offers a WPA3 connection, leveraging the enhanced security features of the new standard. This dual-mode operation ensures that all devices, regardless of their WPA3 support, can join the network without compromising the overall security of the network as much as possible during the transition.
The key to WPA3 Personal Transition’s functionality lies in its ability to support multiple security protocols concurrently. While WPA3-compatible devices benefit from the full suite of WPA3 security enhancements, WPA2 devices connect using their existing WPA2 protocols. The access point essentially acts as a translator or a gateway, managing connections based on the capabilities of the client device. This is achieved through sophisticated management frames and negotiation processes that allow the access point to identify the security capabilities of connecting clients and apply the appropriate security protocol.
Benefits of WPA3 Personal Transition
The primary benefit of WPA3 Personal Transition mode is its ability to facilitate a smoother and less disruptive upgrade path. It eliminates the need for an immediate, all-or-nothing replacement of network infrastructure and client devices. This allows organizations and individuals to prioritize upgrades based on critical needs or budget constraints, gradually phasing in WPA3 support over time.
Another significant advantage is the ability to maintain network connectivity for all users during the transition period. This avoids the user frustration and potential productivity losses that would occur if older devices were suddenly unable to connect. By offering a transitional period, IT administrators can systematically identify and upgrade or replace legacy devices without causing widespread network outages. This phased approach also allows for thorough testing of WPA3 on newer devices before a full rollout, ensuring stability and security.
Furthermore, by enabling WPA3 for compatible devices while still allowing WPA2 for others, the network begins to benefit from enhanced WPA3 security features for a portion of its clients. This means that even before all devices are upgraded, some users will already be experiencing stronger protection against common Wi-Fi attacks. This gradual enhancement of security posture is a valuable intermediate step towards a fully WPA3-secured network.
Key Security Enhancements in WPA3
WPA3 introduces several advanced security features that significantly improve upon WPA2. These enhancements are designed to provide a more robust defense against modern cyber threats and offer greater privacy for users. Understanding these core improvements is essential for appreciating the value of migrating to WPA3, even during a transitional phase.
Simultaneous Authentication of Equals (SAE)
One of the most significant advancements in WPA3 Personal is the introduction of Simultaneous Authentication of Equals (SAE), also known as Dragonfly handshake. SAE replaces the Pre-Shared Key (PSK) authentication method used in WPA2 Personal. Unlike PSK, which is vulnerable to offline dictionary attacks, SAE is designed to be resistant to these types of attacks. SAE utilizes a more complex cryptographic handshake process that is resistant to offline cracking. Even if an attacker captures the handshake packets, they cannot perform offline brute-force attacks to deduce the password. Instead, each authentication attempt requires interaction with the access point, making brute-force attacks significantly more time-consuming and computationally expensive, rendering them largely impractical.
Protected Management Frames (PMF)
Protected Management Frames (PMF), also known as 802.11w, is another critical security feature in WPA3. Management frames are used for various network operations, such as joining and leaving a network, reconfiguring connections, and maintaining communication between the access point and client devices. In WPA2, these management frames are often unencrypted and unprotected, making them susceptible to spoofing and injection attacks. Attackers could use these vulnerabilities to deauthenticate legitimate users or inject malicious frames, disrupting network operations or facilitating man-in-the-middle attacks. WPA3 mandates the use of PMF, which encrypts and authenticates these management frames, preventing unauthorized modification and ensuring the integrity of network control messages. This significantly enhances the resilience of the Wi-Fi network against denial-of-service and other disruption attacks.
Enhanced Open Network Security
For public Wi-Fi networks, WPA3 introduces a significant improvement in security with Wi-Fi Enhanced Open™. While WPA2 offered “open” networks that provided no encryption, leaving all traffic exposed, WPA3 Enhanced Open™ provides individualized data encryption for each user connecting to an open network, even without a password. This is achieved through Opportunistic Wireless Encryption (OWE), a protocol that establishes an encrypted tunnel between the client device and the access point for each user. This means that even in open, unauthenticated networks (like those found in cafes or airports), your internet traffic is protected from eavesdropping by other users on the same network. This is a critical step towards improving the security and privacy of users on public Wi-Fi.
Navigating the Transition: Best Practices for WPA3 Personal Transition
Successfully implementing WPA3 Personal Transition mode requires careful planning and execution. While it offers a valuable bridge, it’s important to have a strategy for eventually moving to a full WPA3 deployment. Adopting best practices can ensure a smooth transition and maximize the security benefits along the way.
Planning for a Full WPA3 Migration
The WPA3 Personal Transition mode is an interim solution. The ultimate goal should be to migrate to a network that exclusively uses WPA3 for all connections. This requires a proactive approach to device management. Start by auditing your existing network devices to identify which ones support WPA3 and which ones do not. Prioritize the replacement or upgrade of devices that are critical to your network operations or that pose the most significant security risks. Consider the lifecycle of your hardware and plan for future purchases to be WPA3-compatible.
Develop a phased rollout plan for WPA3. This might involve deploying WPA3 on a subset of access points first, testing its performance and compatibility with your WPA3-enabled devices. Gradually expand the WPA3 deployment as more devices are upgraded or replaced. Communicate clearly with your users about the upcoming changes and provide them with the necessary information and support for upgrading their devices or connecting to the WPA3-enabled network.
Identifying and Managing Legacy Devices
During the transition, it’s crucial to maintain visibility of legacy devices that are still connecting via WPA2. Implement network monitoring tools to identify these devices and track their usage. This will help you understand which devices are holding back the full adoption of WPA3 and inform your upgrade or replacement strategy. For devices that cannot be immediately upgraded, consider implementing additional security measures, such as network segmentation or access controls, to mitigate potential risks.
For devices that are essential but do not support WPA3, explore potential firmware updates or workarounds. In some cases, manufacturers may release updates that enable WPA3 support. If no such updates are available, you may need to consider alternative solutions, such as using a separate network for these legacy devices or investing in hardware that bridges the gap. The key is to have a clear inventory and a plan for each non-WPA3-compliant device.
Educating Users and Providing Support
User education is a vital component of any network security upgrade. Inform your users about the benefits of WPA3 and what the transition means for them. Provide clear, step-by-step instructions on how to connect their WPA3-compatible devices to the network. Offer support channels where users can get assistance if they encounter any issues. A well-informed user base is more likely to embrace the changes and comply with security policies, reducing support overhead and enhancing overall network security.
Explaining the “why” behind the transition can foster a sense of partnership in maintaining a secure environment. Highlighting improved protection against common online threats can empower users to take an active role in safeguarding their data. Offering clear and accessible support, whether through FAQs, IT helpdesks, or online tutorials, will be crucial for a seamless user experience throughout the WPA3 adoption process.
In conclusion, WPA3 Personal Transition mode represents a pragmatic and essential step in the evolution of Wi-Fi security. By enabling a gradual migration, it allows networks to benefit from the enhanced security of WPA3 without the immediate disruption and cost of a full hardware overhaul. Understanding its mechanics, the underlying security enhancements, and implementing sound transition strategies are key to building and maintaining secure, resilient wireless networks in an increasingly connected world.
