In the rapidly evolving landscape of unmanned aerial vehicles (UAVs) and remote sensing, the integrity of the data link between the pilot and the aircraft is paramount. As drones transition from recreational toys to sophisticated tools for industrial inspection, mapping, and autonomous surveillance, the underlying protocols that govern their wireless communication have come under intense scrutiny. At the heart of most Wi-Fi-based drone control systems and mobile application interfaces lies a security standard known as WPA2-PSK.
WPA2-PSK, or Wi-Fi Protected Access II – Pre-Shared Key, represents a critical layer of defense in the “Tech & Innovation” sector of the drone industry. It is the protocol responsible for ensuring that the video downlink, telemetry data, and command signals remain private and shielded from unauthorized interference. To understand the future of drone connectivity, one must first master the mechanics, strengths, and limitations of the WPA2-PSK standard.
Understanding the Fundamentals of WPA2-PSK in Drone Communication
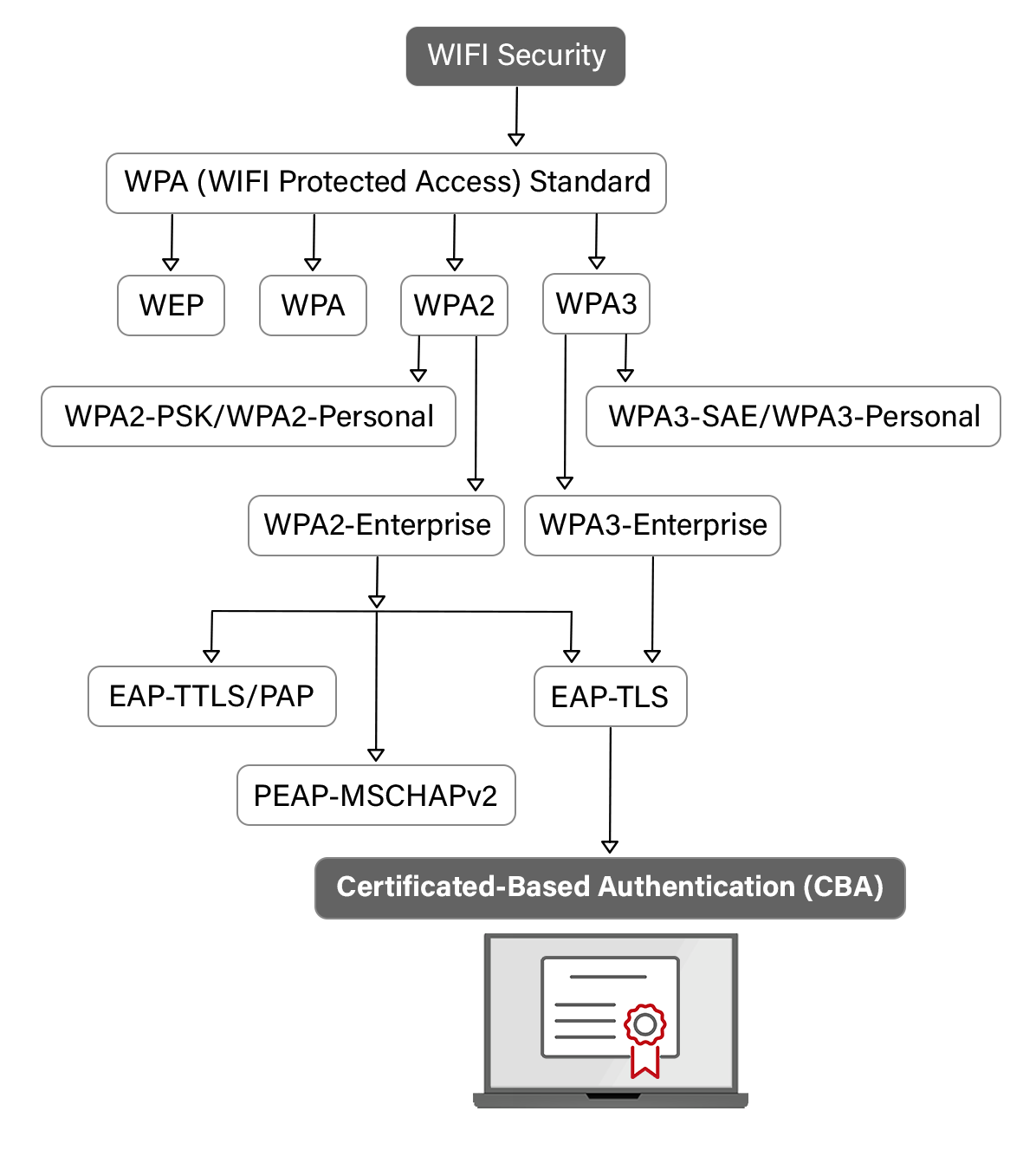
WPA2-PSK is a security method designed for use in residential and small-to-medium business wireless networks, but it has found a permanent home in the drone ecosystem. Unlike the enterprise version of WPA2, which requires a central authentication server, the Pre-Shared Key (PSK) version relies on a static password or “passphrase” shared between the drone (acting as the access point) and the ground control station or smartphone (the client).
The Mechanism: How Pre-Shared Keys Secure the UAV Link
When a pilot powers on a drone that utilizes Wi-Fi for its control link, the drone broadcasts a Service Set Identifier (SSID). To establish a connection, the pilot enters a passphrase. Under the hood, WPA2-PSK uses this passphrase to initiate a “4-Way Handshake.” This process does not actually transmit the password over the air; instead, it uses the password to generate unique encryption keys for that specific session.
In the context of drone innovation, this handshake is vital. It ensures that even if a malicious actor is nearby with a high-gain antenna, they cannot simply “sniff” the password from the air. The session keys are used to encrypt every packet of data—whether it is a command to rotate the gimbal or a frame of 1080p video—ensuring that only the authorized controller can interpret the information.
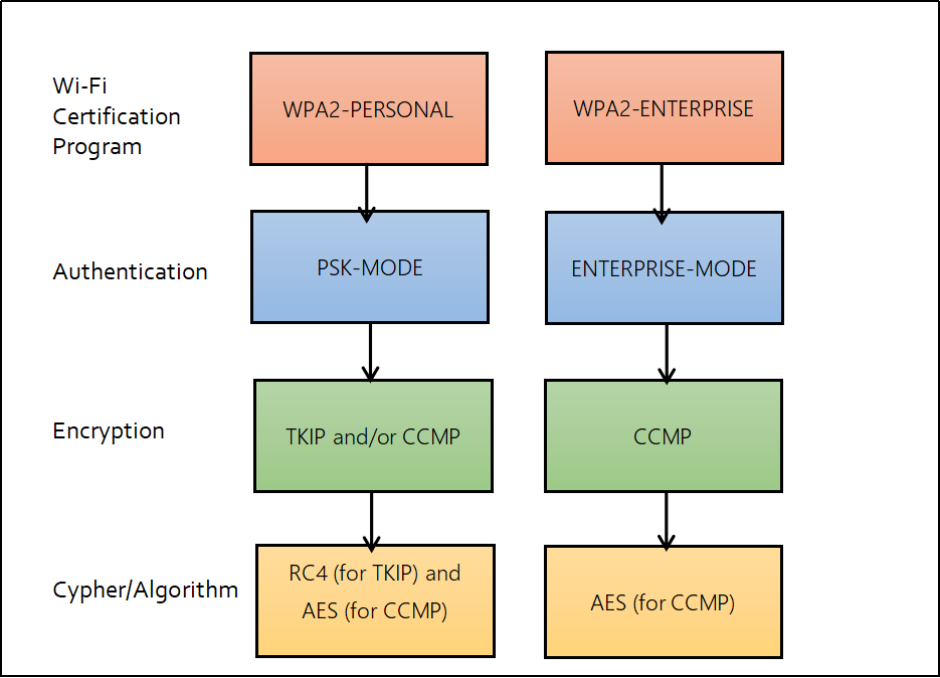
Encryption Standards: AES and CCMP in Data Transmission
WPA2-PSK is synonymous with the Advanced Encryption Standard (AES). Within drone tech, AES-CCMP (Counter Mode with Cipher Block Chaining Message Authentication Code Protocol) is the engine that drives data privacy. AES is a symmetric-key algorithm that is computationally efficient enough to be processed in real-time by the compact onboard processors found in modern UAVs.
This efficiency is crucial for drones. Because flight control requires low-latency communication, the encryption process must not introduce significant lag. If the WPA2-PSK encryption were too heavy, the delay between a pilot’s input and the drone’s reaction could lead to catastrophic crashes. Innovation in chipsets has allowed WPA2-PSK to offer robust 128-bit encryption without compromising the flight performance of the aircraft.
The Critical Role of Wi-Fi Security in Autonomous Flight and Remote Sensing
As drones become more autonomous, the stakes for wireless security rise. Autonomous flight relies on a constant stream of telemetry data—GPS coordinates, altitude, battery health, and obstacle detection sensor feeds. If the WPA2-PSK link is compromised, the consequences extend far beyond a lost video feed; the entire mission profile is at risk.
Preventing Signal Hijacking and Spoofing
One of the primary reasons WPA2-PSK remains a staple in drone innovation is its ability to prevent “man-in-the-middle” attacks and signal hijacking. Without encryption, an attacker could send forged packets to the drone, effectively taking over flight controls or triggering an emergency landing in an unsafe location.
By utilizing WPA2-PSK, drone manufacturers create a secure “tunnel” for communication. Even in congested urban environments where dozens of Wi-Fi signals overlap, the specific cryptographic binding between the controller and the drone prevents other devices from accidentally or intentionally interfering with the command frequency. This reliability is what enables complex innovations like swarm technology and automated perimeter patrols.
Protecting Telemetry and Real-Time Data Streams
For professional drone operators involved in remote sensing and mapping, the data being transmitted is often proprietary or sensitive. For example, a drone surveying a construction site or a sensitive government facility is capturing high-resolution imagery that must not fall into the wrong hands.
WPA2-PSK ensures that the downlink—the path from the drone to the ground station—is encrypted. This protects the “intellectual property” of the flight. In the world of tech and innovation, where data is the new currency, the security of the transmission protocol is just as important as the resolution of the camera or the accuracy of the LiDAR sensor.
WPA2-PSK vs. Modern Alternatives: OcuSync, Lightbridge, and WPA3
While WPA2-PSK is the standard for Wi-Fi-based drones, the industry is constantly pushing the boundaries of range and security. It is essential to distinguish between standard Wi-Fi protocols and the proprietary long-range transmission systems developed by industry leaders.
Why WPA2-PSK Remains a Standard for Prosumer Drones
Standard Wi-Fi protocols like WPA2-PSK are favored for “prosumer” and entry-level drones because of their compatibility. Since almost every smartphone and tablet supports WPA2-PSK, manufacturers can design drones that are controlled via an app without the need for a dedicated, bulky hardware remote. This accessibility has been a major driver of innovation, allowing for the “pocket drone” revolution.
However, WPA2-PSK is limited by the physics of standard Wi-Fi. In high-interference areas, the 2.4GHz or 5.8GHz bands used by WPA2-PSK can become crowded, leading to reduced range. Despite this, for short-range inspections (within 500 meters to 1 kilometer), WPA2-PSK provides an ideal balance of security and ease of use.
The Shift Toward Proprietary Long-Range Protocols
In the high-end professional and military sectors, the industry has moved toward specialized protocols like DJI’s OcuSync or Autel’s SkyLink. These systems often build upon the principles of WPA2 but incorporate frequency-hopping spread spectrum (FHSS) and more advanced error-correction algorithms.
Furthermore, the emergence of WPA3 is the next logical step for Wi-Fi-based drones. WPA3 improves upon WPA2-PSK by offering “Simultaneous Authentication of Equals” (SAE), which provides even stronger protection against brute-force password guessing. As drone hardware becomes more powerful, we can expect a shift where WPA3 becomes the new baseline for secure drone-to-app connectivity.
Implementation Best Practices for Drone Operators and Developers
Understanding WPA2-PSK is only half the battle; implementing it correctly is what ensures the safety of the drone and the integrity of the data. As part of the broader tech innovation landscape, developers and pilots must adhere to specific security hygiene practices.
Strengthening Handshake Security in Field Operations
One of the known vulnerabilities of WPA2-PSK is the “KRACK” (Key Reinstallation Attack), which targets the 4-way handshake. While most modern drone firmware has been patched to mitigate this, it highlights the importance of keeping drone software up to date.
For operators, this means performing regular “pre-flight” software checks. Ensuring that both the drone’s internal firmware and the ground control application are running the latest versions is a critical step in maintaining the security provided by WPA2-PSK. Innovation in “over-the-air” (OTA) updates has made this process seamless, but the responsibility still lies with the user.
Managing Password Complexity for Mobile Control Apps
Because WPA2-PSK relies on a pre-shared key, the strength of that key is the weak point in the system. Many drones ship with a default password (e.g., “12345678”). In a professional or industrial setting, leaving a drone at its factory default settings is a massive security risk.
Innovative drone management platforms now force users to change the default WPA2-PSK password upon the first activation. Using complex, non-dictionary passwords ensures that even if an unauthorized party attempts to “crack” the Wi-Fi signal, the time required to do so would exceed the duration of the flight.
Conclusion: The Future of Wireless Security in the Drone Industry
WPA2-PSK has served as a foundational technology in the rise of the modern drone era. It bridged the gap between complex military-grade communication and the accessible, consumer-friendly devices we see today. In the realm of Tech & Innovation, WPA2-PSK is a testament to how standardized networking protocols can be adapted to support the high-stakes environment of aerial robotics.
As we look toward the future, the integration of 5G, the adoption of WPA3, and the development of quantum-resistant encryption will likely supersede the current standards. However, the core principle remains the same: the link must be secure. Whether it is a drone delivering a package, a UAV inspecting a power line, or an autonomous craft mapping a forest, the “Pre-Shared Key” remains the silent guardian of our skies, ensuring that innovation and security fly hand-in-hand.
