Understanding and configuring Virtual Private Network (VPN) settings is crucial for enhancing online privacy, security, and accessibility. A VPN creates a secure, encrypted tunnel between your device and a remote server operated by the VPN provider. All your internet traffic is then routed through this tunnel, masking your IP address and encrypting your data. This effectively shields your online activities from your Internet Service Provider (ISP), government surveillance, and potential hackers.
The “settings” of a VPN refer to the various parameters and options that allow you to customize how the VPN connection is established and operates. These settings can range from simple on/off toggles to more complex configurations involving protocols, encryption levels, and server selection. Mastering these settings empowers users to tailor their VPN experience to their specific needs, whether it’s for bypassing geo-restrictions, securing public Wi-Fi connections, or ensuring anonymity for sensitive online tasks.
Understanding Core VPN Settings
The fundamental settings of a VPN are designed to establish and maintain a secure connection. These are the bedrock of your VPN experience and are often the first configurations users will encounter.
VPN Protocols: The Foundation of Security
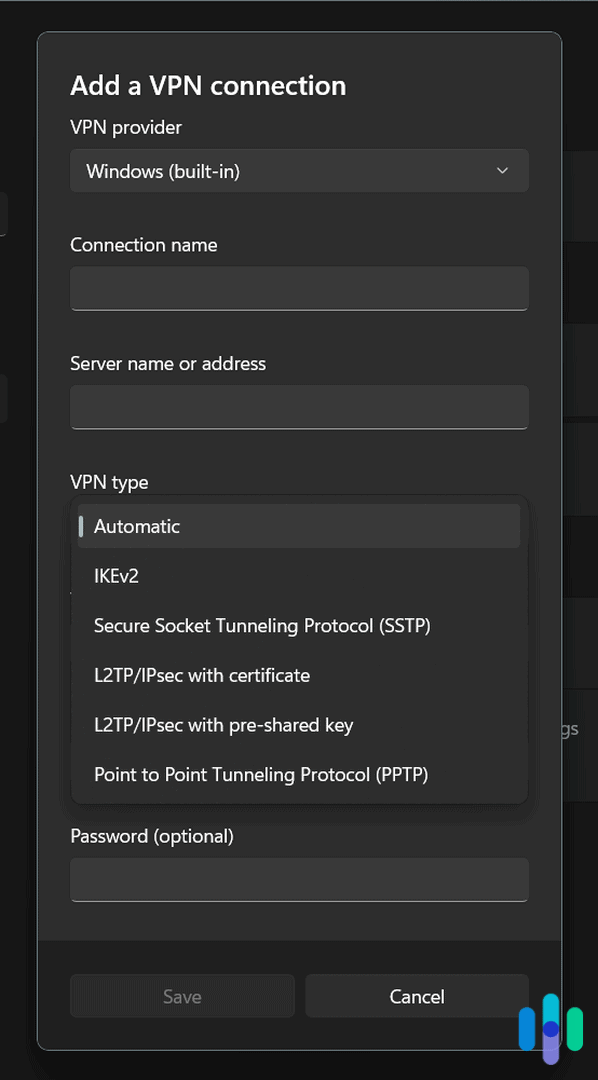
VPN protocols are the sets of rules and instructions that govern how the VPN tunnel is created and how data is transmitted through it. Different protocols offer varying balances between speed, security, and compatibility. Understanding these is key to choosing the right settings for your needs.
OpenVPN: The Industry Standard
OpenVPN is widely considered the most secure and versatile VPN protocol. It’s open-source, meaning its code is publicly available for scrutiny, which fosters trust and allows for continuous improvement by the community. OpenVPN can operate over TCP or UDP ports.
-
OpenVPN over TCP (Transmission Control Protocol): This protocol prioritizes reliability and error checking. It ensures that all data packets arrive in the correct order and without loss. This makes it excellent for activities where data integrity is paramount, such as downloading large files or browsing sensitive websites. However, TCP can be slower than UDP due to its overhead for error correction and retransmission. It’s also more easily detected and blocked by firewalls.
-
OpenVPN over UDP (User Datagram Protocol): UDP is a faster, connectionless protocol that sacrifices some reliability for speed. It doesn’t guarantee packet delivery or order. This makes it ideal for real-time applications like online gaming and video streaming, where minor packet loss is often imperceptible, and low latency is critical. While faster, it’s less secure in terms of data integrity compared to TCP.
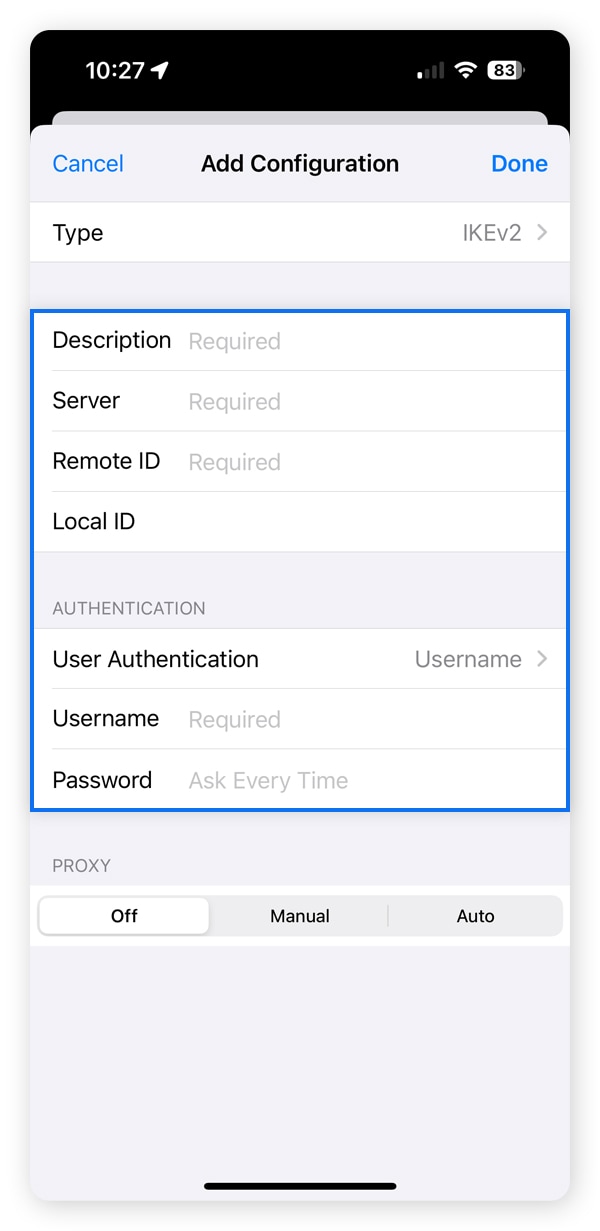
IKEv2/IPsec: Speed and Stability on Mobile
Internet Key Exchange version 2 (IKEv2) is a dynamic protocol often paired with the Internet Protocol Security (IPsec) suite. It’s known for its stability and speed, making it an excellent choice for mobile devices that frequently switch between networks (e.g., Wi-Fi to cellular data). IKEv2/IPsec is also adept at re-establishing connections quickly if they drop, which is particularly useful for users on the go. Its robust security features make it a strong contender for many users.
L2TP/IPsec: A Widely Compatible Option
Layer 2 Tunneling Protocol (L2TP) combined with IPsec provides a good balance of security and compatibility across various devices and operating systems. L2TP itself doesn’t offer encryption, but when paired with IPsec, it provides a secure tunnel. While generally considered secure, it can be slower than OpenVPN or IKEv2 due to double encapsulation. It is also more prone to being blocked by firewalls.
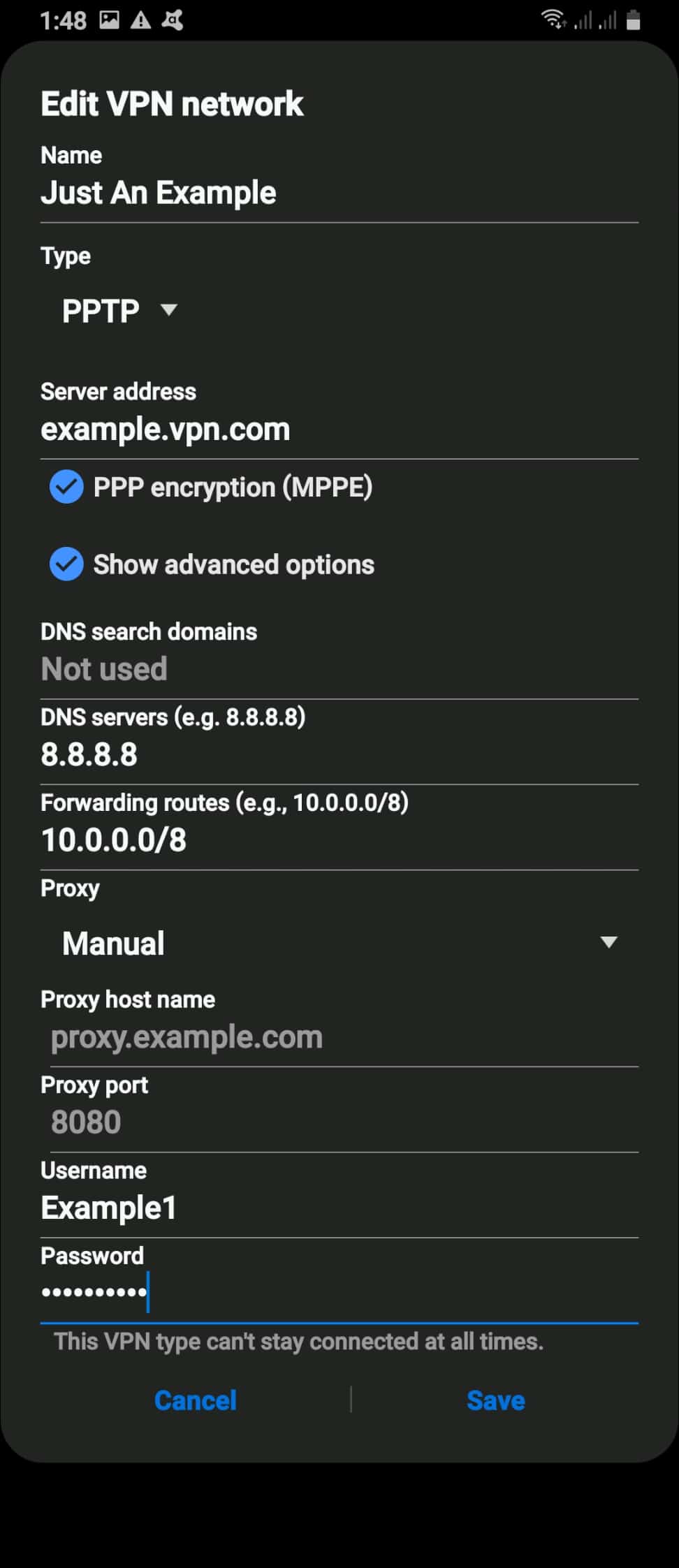
PPTP: Outdated and Insecure
Point-to-Point Tunneling Protocol (PPTP) is one of the oldest VPN protocols. It is known for its speed and ease of setup but suffers from significant security vulnerabilities. It is strongly advised against using PPTP for any sensitive activities as it is considered compromised. Modern VPN services typically no longer support it or recommend its use.
Encryption Levels: The Strength of Your Shield
Encryption is the process of scrambling your data so that it’s unreadable to anyone who intercepts it. The strength of this encryption is determined by the encryption algorithm and the key length used.
AES Encryption: The Gold Standard
Advanced Encryption Standard (AES) is the most widely used and highly regarded encryption algorithm. It’s a symmetric encryption algorithm, meaning the same key is used for both encryption and decryption.
-
AES-128: This uses a 128-bit key. While strong, it is considered less secure than AES-256 and is susceptible to brute-force attacks with sufficient computational power over time.
-
AES-256: This uses a 256-bit key and is currently the strongest commercially available encryption standard. It is considered virtually unbreakable by today’s computing technology, making it the preferred choice for maximum security. Many government agencies and cybersecurity experts rely on AES-256 for protecting sensitive data.
Server Selection: Your Gateway to the Internet
VPN providers operate servers in various locations around the world. The server you connect to determines your virtual location and influences your connection speed.
Choosing the Right Server Location
-
Bypassing Geo-Restrictions: To access content or websites that are only available in specific countries (e.g., streaming services, regional news sites), you’ll need to connect to a server located in that country.
-
Improving Speed: Connecting to a server physically closer to your actual location will generally result in faster connection speeds due to reduced latency.
-
Enhancing Privacy: Some users prefer to connect to servers in countries with strong data privacy laws, further shielding their online activities.
Server Load: Impact on Performance
VPN servers can become overloaded if too many users are connected to them simultaneously. This can lead to slower speeds and connection instability. Most VPN applications will display server load, allowing you to choose a less congested server for a better experience.
Advanced VPN Settings for Enhanced Control
Beyond the core settings, many VPN applications offer advanced options to fine-tune your privacy and security posture. These settings cater to users who require more granular control over their online activities.
Kill Switch: The Ultimate Safety Net
A kill switch is a critical security feature that automatically disconnects your device from the internet if the VPN connection drops unexpectedly. This prevents your real IP address and unencrypted data from being exposed.
How a Kill Switch Works
When the VPN connection fails, the kill switch acts as an immediate barrier. Instead of allowing your device to revert to a direct, unsecured internet connection, it severs all internet access until the VPN connection is re-established or manually disabled. This is invaluable for users who rely on VPNs for highly sensitive activities.
Types of Kill Switches
-
System-Level Kill Switch: This type blocks all internet traffic at the operating system level if the VPN disconnects. It’s the most comprehensive and effective.
-
Application-Level Kill Switch: This option allows you to specify which applications should be terminated if the VPN connection drops. This can be useful if you only need to protect specific programs.
Split Tunneling: Balancing Security and Accessibility
Split tunneling is a feature that allows you to choose which of your internet traffic goes through the VPN tunnel and which bypasses it. This provides a flexible way to manage your online activities.
When to Use Split Tunneling
-
Accessing Local Network Resources: If you need to access devices on your local network (e.g., printers, network drives) while connected to the VPN, split tunneling can route that traffic directly.
-
Improving Performance for Certain Apps: You might want to route non-sensitive traffic, like general web browsing, through the VPN for security, while allowing high-bandwidth applications (e.g., local streaming services, video conferencing) to bypass the VPN for better speeds.
-
Using Region-Specific Apps: Some applications may not function correctly when connected to a VPN. Split tunneling allows these apps to use your regular internet connection while the rest of your traffic remains protected.
DNS Leak Protection: Ensuring True Anonymity
Domain Name System (DNS) servers translate human-readable website names (e.g., google.com) into IP addresses that computers understand. A DNS leak occurs when your device sends DNS requests outside of the encrypted VPN tunnel, potentially revealing your online activity to your ISP.
How DNS Leak Protection Works
Reputable VPN services configure their servers to handle all DNS requests for connected users. VPN settings often include an option to enable DNS leak protection, which ensures that your DNS requests are routed through the VPN’s secure servers, preventing leaks and maintaining your anonymity.
Obfuscation (Stealth VPN): Evading Detection
In regions or networks that actively block VPN traffic, obfuscation techniques are used to disguise VPN connections as regular internet traffic. This makes it harder for network administrators or governments to detect and block your VPN usage.
The Role of Obfuscation Settings
When enabled, obfuscation technology can make your VPN traffic appear as standard HTTPS traffic, making it indistinguishable from normal web browsing. This is particularly useful in countries with strict internet censorship or on corporate or academic networks that restrict VPN use.
Configuring VPN Settings for Different Use Cases
The ideal VPN settings will vary depending on your individual needs and the tasks you intend to perform online. Understanding these specific use cases can help you optimize your configuration.
Optimizing for Streaming and Gaming
For streaming and online gaming, speed and low latency are paramount.
- Protocol: Opt for UDP-based protocols like OpenVPN UDP or IKEv2/IPsec for the best performance.
- Server Location: Connect to a server that is geographically close to your location or the location of the streaming service/game server.
- Encryption: While strong encryption is always recommended, you might consider slightly less demanding settings if speed becomes a significant issue, though always ensure AES-128 at a minimum.
- Kill Switch: Keep this enabled to prevent accidental data leaks, even if it might introduce a slight delay in re-establishing connection if dropped.
Securing Public Wi-Fi
Public Wi-Fi networks are notoriously insecure and prone to eavesdropping. A VPN is essential for protecting your data.
- Protocol: OpenVPN over TCP or IKEv2/IPsec are excellent choices for their security and reliability.
- Encryption: Always use AES-256 for the highest level of security.
- Kill Switch: Absolutely essential. Enable it to ensure your connection is always encrypted when using public Wi-Fi.
- DNS Leak Protection: Ensure this is enabled to prevent your browsing activity from being revealed.
Maintaining Anonymity and Privacy
For users prioritizing anonymity and privacy, every setting should be scrutinized.
- Protocol: OpenVPN (both TCP and UDP, depending on preference for reliability vs. speed) or IKEv2/IPsec are highly recommended.
- Encryption: AES-256 is non-negotiable.
- Server Location: Consider servers in countries with strong privacy laws and no mandatory data retention policies.
- Kill Switch: Essential for preventing any accidental exposure.
- DNS Leak Protection: Crucial.
- Obfuscation: If you suspect your VPN traffic might be monitored or blocked, enable obfuscation settings.
- No-Logs Policy: While not a setting, ensure your VPN provider has a strict, independently audited no-logs policy.
Troubleshooting Common VPN Settings Issues
Even with the best configurations, you might encounter issues. Understanding common problems and their solutions can save you frustration.
Connection Failures
If you’re unable to establish a VPN connection, try the following:
- Check Credentials: Ensure your username and password are correct.
- Switch Protocols: Try a different VPN protocol (e.g., if OpenVPN UDP fails, try OpenVPN TCP or IKEv2).
- Change Server: Connect to a different server location. The current server might be down or overloaded.
- Restart Device and VPN Client: A simple restart can often resolve temporary glitches.
- Check Firewall/Antivirus: Ensure your firewall or antivirus software isn’t blocking the VPN client. You may need to add an exception.
Slow Internet Speeds
Slow speeds are a common complaint, but often manageable:
- Change Server: Connect to a server closer to your physical location.
- Switch Protocols: UDP protocols are generally faster than TCP.
- Disable Other Network-Intensive Applications: Close any programs that are consuming significant bandwidth.
- Check VPN Server Load: Choose a server with lower reported load.
- Test Without VPN: Compare your speed with and without the VPN to see if the VPN is the sole cause of the slowdown.
IP Address or DNS Leaks
If you suspect leaks, even with protection enabled:
- Run Leak Tests: Use online tools likeipleak.net or dnsleaktest.com to check for IP and DNS leaks.
- Enable All Protection Features: Ensure kill switch and DNS leak protection are fully activated within your VPN client.
- Verify Protocol Settings: Double-check that your chosen protocol is correctly configured for your VPN service.
- Contact Support: If leaks persist, reach out to your VPN provider’s customer support for assistance.
By understanding and effectively configuring your VPN settings, you can unlock a more secure, private, and unrestricted online experience. From choosing the right protocols and encryption levels to utilizing advanced features like kill switches and split tunneling, informed settings management is the key to maximizing the benefits of your VPN.
