In the ever-evolving landscape of advanced aerial technology, the seamless and secure integration of components is paramount. As drones become more sophisticated, capable of complex maneuvers, and integral to critical operations, the underlying communication and verification systems underpinning their functionality demand rigorous scrutiny. “Verify Connect” emerges as a crucial concept in this domain, representing the robust mechanisms by which a drone system ensures the authenticity, integrity, and reliable operation of its interconnected parts. This is not merely about establishing a link; it’s about guaranteeing that the link is sound, secure, and performing as intended, especially when dealing with sensitive data or high-stakes missions.
The term “Verify Connect” encapsulates a multifaceted approach to establishing and maintaining the trust between various elements of a drone ecosystem. This includes the interaction between the flight controller, the remote control, onboard sensors, communication modules, and potentially ground control stations or cloud-based platforms. In essence, it’s the technical assurance that what is connected is indeed what it claims to be, and that the data exchanged is uncorrupted and secure. Understanding Verify Connect is fundamental to appreciating the reliability, safety, and advanced capabilities of modern unmanned aerial systems.
The Pillars of a Secure and Reliable Drone Ecosystem
The integrity of a drone’s operation hinges on the trustworthiness of its interconnected components. Verify Connect is built upon a foundation of established technological principles, all working in concert to ensure that the system functions as a cohesive and dependable unit. This involves verifying both the physical and logical connections, ensuring that only authorized and properly functioning hardware and software are integrated, and that communication channels are secure against interference and tampering.
Authentication of Hardware and Software Components
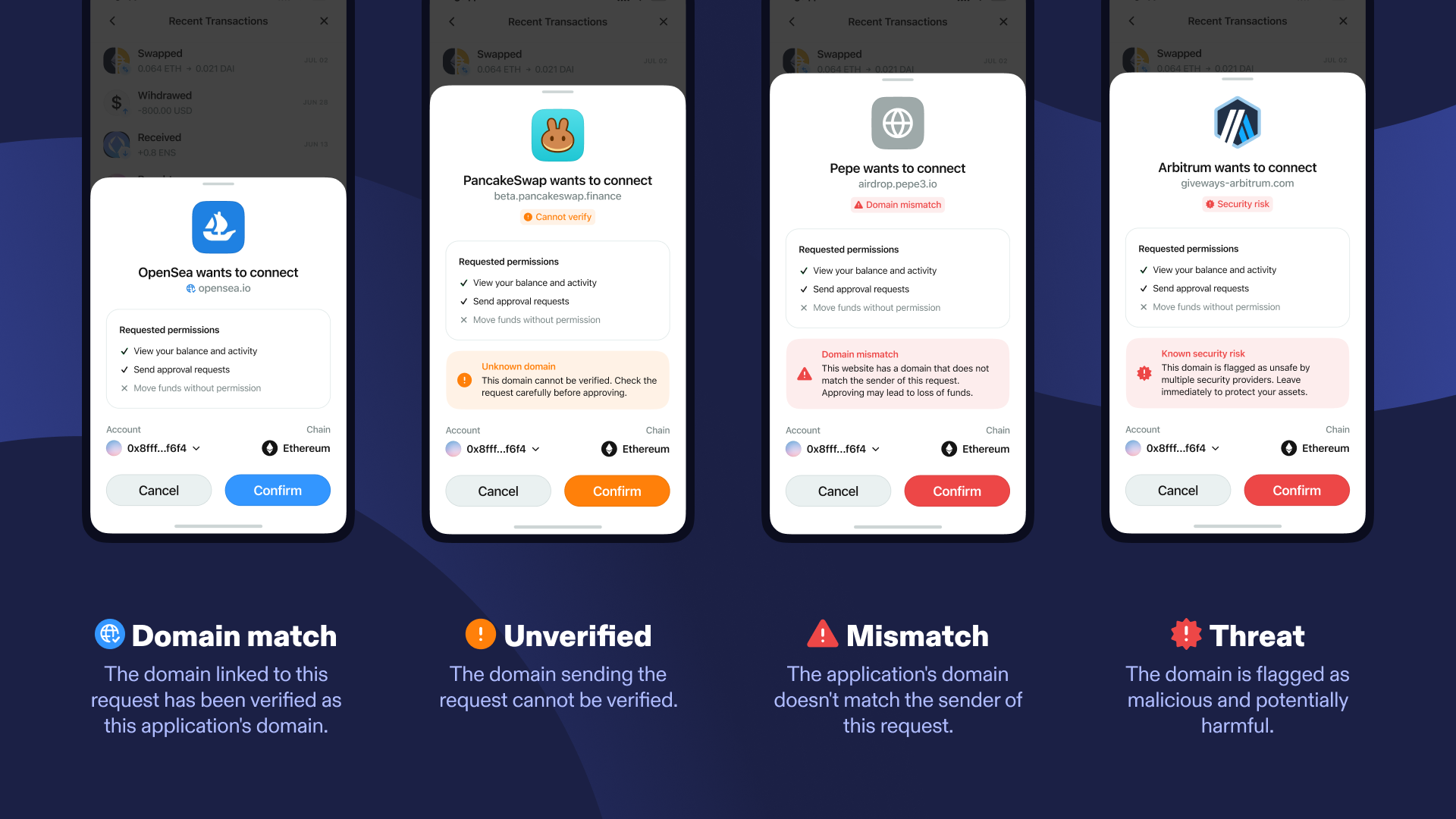
At its core, Verify Connect begins with ensuring that every component intended to be part of the drone system is recognized and approved. This process is akin to a digital handshake, where each piece of hardware and software presents its credentials to the central flight controller or system manager.
Unique Identification and Registration
Every legitimate component within a drone system is typically assigned a unique identifier. This could be a serial number, a hardware-specific ID, or a cryptographic key embedded during the manufacturing process. When a component is powered on or connected, it broadcasts this identifier. The flight controller then cross-references this ID against a pre-approved list or a secure registry. This ensures that no unauthorized or counterfeit parts are introduced into the system, which could compromise its safety or performance. For instance, a proprietary communication module designed for secure data transmission will only be recognized and enabled if its unique ID matches the expected parameters for that specific drone model or firmware version.
Digital Signatures and Firmware Verification
Beyond mere identification, Verify Connect extends to ensuring the integrity of the software and firmware running on these components. Firmware is the low-level software that controls the hardware. Any tampering with this firmware could lead to unpredictable behavior, loss of control, or security vulnerabilities. Therefore, Verify Connect protocols often involve verifying digital signatures on firmware. When a component boots up or receives a firmware update, it checks the digital signature to confirm that the firmware is authentic, has not been altered since it was signed by the manufacturer, and is compatible with the rest of the system. This prevents the execution of malicious code or outdated, potentially unstable, firmware.
Ensuring Communication Integrity and Security
Once components are authenticated, the next critical aspect of Verify Connect is the assurance that the data exchanged between them remains accurate, uncorrupted, and protected from unauthorized interception or manipulation. This is particularly vital for command and control signals, telemetry data, and payload information.
Encryption and Data Obfuscation
To protect against eavesdropping and signal jamming, Verify Connect employs robust encryption protocols. All sensitive data transmitted between components, such as flight commands from the remote control to the drone or critical telemetry data from the drone back to the pilot, is encrypted. This means the data is scrambled using complex algorithms, making it unintelligible to anyone without the correct decryption key. Similarly, data obfuscation techniques can be used to mask the true nature of the data being transmitted, further hindering attempts at analysis by unauthorized parties.
Error Detection and Correction Codes
Despite the best encryption, communication channels are susceptible to noise and interference, which can lead to data corruption. Verify Connect incorporates error detection and correction codes within the communication protocols. These codes are mathematical techniques that allow the receiving component to identify if any bits of data have been altered during transmission. If errors are detected, these codes can often correct them automatically, ensuring that the commands received by the drone are precisely what the pilot intended, and that the telemetry data accurately reflects the drone’s status. This is essential for maintaining stable flight and preventing critical failures due to corrupted commands.
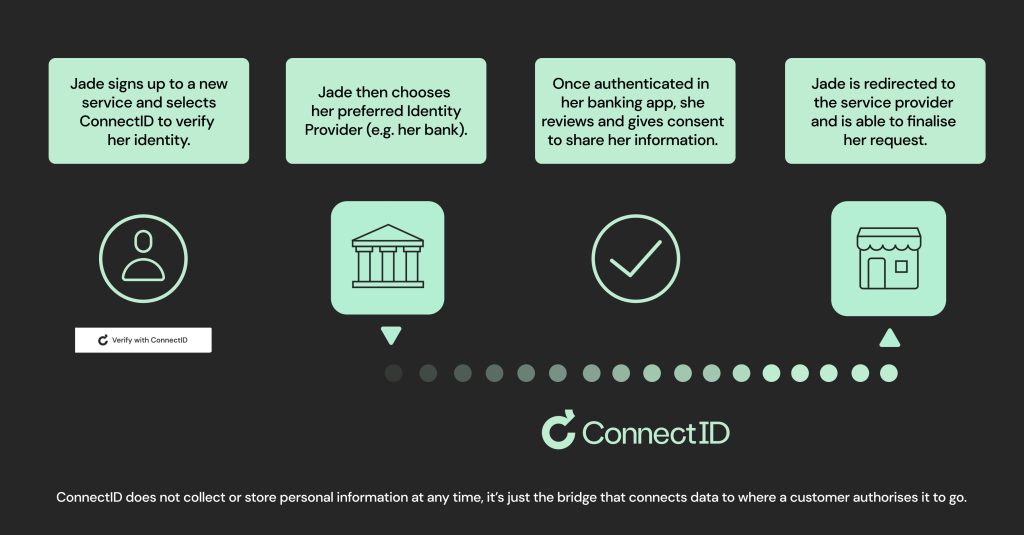
Secure Pairing and Key Management
The process of establishing a secure communication link between components, often referred to as pairing, is another vital element. For example, when a remote controller is paired with a drone, Verify Connect ensures that this pairing is done securely and exclusively between those specific devices. This often involves a one-time exchange of cryptographic keys. Secure key management practices are then employed to store and protect these keys, preventing them from being compromised. This prevents a malicious actor from intercepting a valid pairing process and subsequently taking control of the drone.
The Role of Verify Connect in Advanced Drone Operations
The implications of Verify Connect extend far beyond basic drone functionality. In specialized and demanding applications, the assurance of secure and authentic connections is not just a matter of convenience; it is a prerequisite for operational success and safety. This is where the nuanced application of Verify Connect protocols becomes indispensable.
Autonomous Flight and AI Integration
As drones increasingly undertake autonomous missions, the reliance on precise and reliable communication between various sensors, processors, and actuators intensifies. Verify Connect plays a critical role in ensuring that the data fueling these autonomous decisions is trustworthy.
Sensor Data Validation
Autonomous flight systems depend on a multitude of sensors – GPS for positioning, IMUs for orientation, LiDAR or cameras for obstacle avoidance, and barometers for altitude. Verify Connect ensures that the data streamed from these sensors is not only received but also validated for authenticity and integrity. This means the system can cross-reference data from multiple sensors, detect anomalies, and flag or discard data from a potentially compromised or malfunctioning sensor. For example, if GPS data suggests the drone is at an altitude of 500 feet but the barometer indicates 100 feet, Verify Connect’s validation layer would identify this discrepancy, potentially initiating a safety protocol.
AI Algorithm Assurance
The artificial intelligence algorithms that drive autonomous navigation, decision-making, and object recognition rely on clean, accurate, and verifiable data inputs. Verify Connect ensures that the data fed into these AI models is untainted. This protects the AI from making erroneous decisions based on corrupted sensor readings or manipulated communication signals. Imagine an AI designed to identify specific targets; if the image data is distorted or tampered with, the AI’s effectiveness is severely undermined. Verify Connect provides the assurance that the data being processed is a true representation of the environment, enabling the AI to perform its functions reliably.
Remote Sensing and Data Security
Drones are increasingly utilized for sophisticated remote sensing tasks, collecting vast amounts of data for applications ranging from environmental monitoring and agricultural analysis to infrastructure inspection and law enforcement. The integrity and security of this data are paramount.
Payload Data Verification
When a drone carries specialized payloads, such as high-resolution cameras, multispectral sensors, or scientific instruments, the data generated by these payloads needs to be verified. Verify Connect ensures that the data collected by the payload is correctly timestamped, associated with the correct flight path, and has not been corrupted during transmission or storage. This is crucial for maintaining the scientific or operational value of the collected information. For example, in environmental surveys, verifying the authenticity of thermal imaging data is essential for accurate temperature readings and subsequent analysis.
Secure Data Transmission to Ground Stations
The process of transmitting collected data from the drone to a ground station or cloud-based server is a critical juncture for Verify Connect. This data, often sensitive, needs to be protected during its journey. Secure communication protocols, including robust encryption and authentication mechanisms, are employed to ensure that the data reaches its destination intact and uncompromised. This prevents unauthorized access, alteration, or deletion of valuable collected information, which could have significant implications for research, business operations, or public safety.
The Future of Verify Connect in the Drone Industry
As drone technology continues its rapid advancement, the demands placed upon Verify Connect systems will only increase. The drive towards greater autonomy, increased operational complexity, and wider adoption across critical sectors necessitates a parallel evolution in how connections are verified and secured. The future of Verify Connect promises more sophisticated, integrated, and proactive solutions.
Enhanced Cybersecurity and Threat Mitigation
The growing sophistication of cyber threats requires continuous innovation in drone system security. Future Verify Connect protocols will likely incorporate more advanced cybersecurity measures, including real-time anomaly detection, advanced intrusion prevention systems, and dynamic authentication methods that adapt to evolving threat landscapes. This proactive approach will be essential in safeguarding against increasingly persistent and intelligent adversaries seeking to exploit vulnerabilities.
Machine Learning for Anomaly Detection
The application of machine learning and artificial intelligence within Verify Connect itself is poised to revolutionize threat mitigation. By continuously analyzing communication patterns, data flows, and system behavior, AI can learn to identify subtle deviations that might indicate a security breach or hardware malfunction far earlier than traditional methods. This allows for the immediate isolation of compromised components or the flagging of suspicious activity, thereby minimizing potential damage.
Blockchain for Immutable Record Keeping
The inherent immutability and distributed nature of blockchain technology offer a compelling avenue for enhancing Verify Connect. Blockchain can be utilized to create a secure and tamper-proof ledger of all component identifications, firmware versions, and communication events. This would provide an indisputable audit trail, making it virtually impossible to falsify connection histories or introduce unauthorized components without leaving a trace. This level of transparency and accountability will be invaluable for regulatory compliance and operational integrity.
Standardization and Interoperability
For the drone industry to truly mature and scale, a degree of standardization in Verify Connect protocols will be essential. This will facilitate interoperability between components from different manufacturers, reducing vendor lock-in and fostering a more robust and competitive ecosystem.
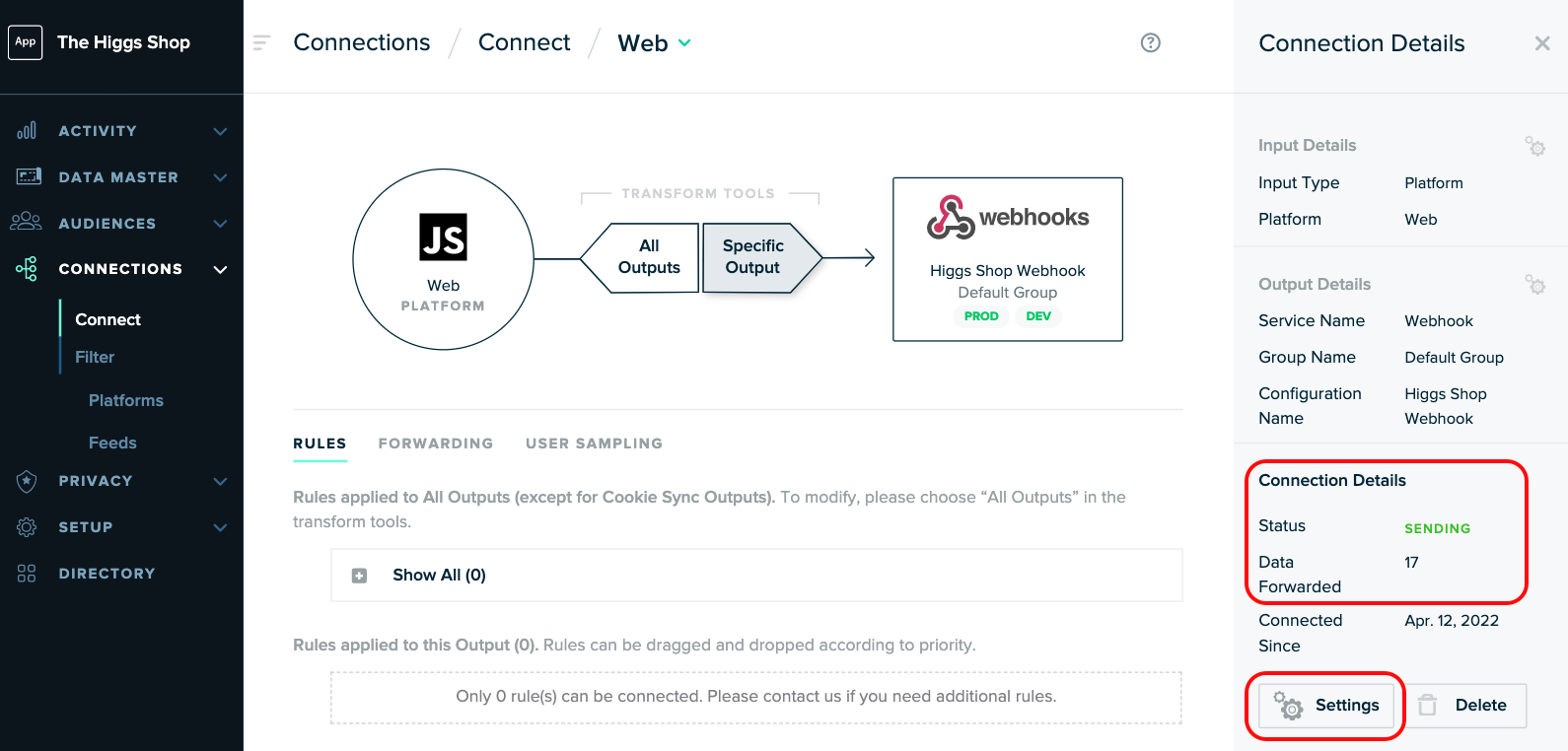
Open Standards and APIs
The development and adoption of open standards and Application Programming Interfaces (APIs) for Verify Connect will be crucial. This will allow for seamless integration of various hardware and software elements, enabling drone manufacturers and operators to build more flexible and customized systems. It will also simplify the process of updating and upgrading components, ensuring that systems can remain secure and functional over their lifecycle.
Regulatory Compliance and Trust Frameworks
As drones become integrated into mainstream air traffic and regulated sectors, robust Verify Connect frameworks will be necessary to meet stringent regulatory requirements. These frameworks will not only dictate technical specifications but also establish trust models for how drone systems are verified and approved for operation. This will be particularly important for applications in public safety, transportation, and critical infrastructure, where the consequences of failure are significant.
In conclusion, Verify Connect is not a singular technology but rather a comprehensive set of principles and practices that underpin the reliability, security, and trustworthiness of modern drone systems. From the initial authentication of hardware to the secure transmission of vast datasets and the anticipation of future threats, Verify Connect is an indispensable element that empowers drones to operate safely and effectively across an ever-expanding range of applications. As the technology evolves, so too will the sophisticated mechanisms that ensure every connection, every piece of data, and every command is verified, guaranteeing the integrity of the skies.
