In the rapidly evolving landscape of digital threats and technological innovation, understanding the adversary is paramount. One of the most critical frameworks for achieving this understanding in cybersecurity is the concept of Tactics, Techniques, and Procedures (TTPs). TTPs provide a structured lens through which organizations can analyze the methods and behaviors of threat actors, moving beyond mere indicators of compromise (IOCs) to anticipate, detect, and respond to sophisticated attacks. For entities at the forefront of Tech & Innovation – developing autonomous systems, advanced AI, sophisticated mapping, and remote sensing capabilities – grasping TTPs is not just beneficial; it is foundational to building resilient and secure platforms against an ever-adapting cyber adversary.
Understanding the Foundation of Threat Intelligence
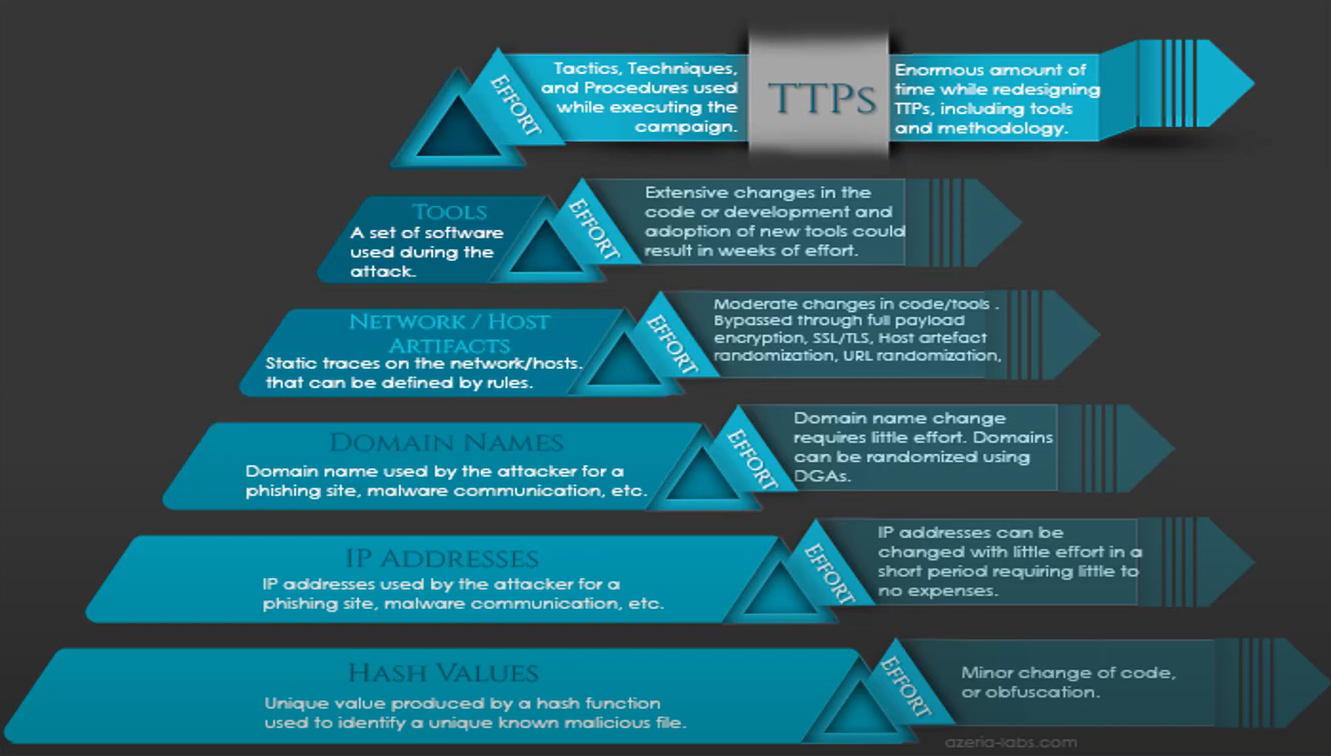
TTPs represent the full spectrum of an attacker’s methodology, from their strategic goals down to the granular steps they take to achieve them. This comprehensive view allows security professionals to develop more robust defenses that are less reliant on detecting known malware signatures and more focused on identifying malicious behavior patterns. This shift is particularly crucial when dealing with novel attack vectors targeting cutting-edge technological innovations where traditional signatures may not yet exist.
Tactics: The Attacker’s Strategy
Tactics describe the high-level objectives or strategic goals an attacker aims to achieve during an attack. These are the “why” behind an adversary’s actions. In the context of the MITRE ATT&CK framework, which is a globally accessible knowledge base of adversary TTPs, tactics represent the various phases of an attack lifecycle. Examples include initial access, execution, persistence, privilege escalation, defense evasion, credential access, discovery, lateral movement, collection, command and control, exfiltration, and impact.
For organizations innovating in areas like autonomous navigation systems or advanced data analytics, understanding the tactics an adversary might employ is critical. An attacker might use “Initial Access” to gain a foothold in a network controlling autonomous vehicles, or “Exfiltration” to steal proprietary algorithms for AI-driven remote sensing. Recognizing these strategic goals helps in designing security controls that address entire phases of an attack, rather than just isolated incidents. It encourages a proactive approach to securing the entire technology stack from conception to deployment.
Techniques: The Methods of Execution
Techniques elaborate on the “how” – the specific ways an adversary achieves their tactical goals. These are the detailed methods or approaches used to carry out a particular tactic. For instance, if the tactic is “Initial Access,” techniques might include spearphishing attachments, exploitation of public-facing applications, or valid accounts. If the tactic is “Persistence,” techniques could involve creating new services, modifying boot-up scripts, or using scheduled tasks.
In the realm of Tech & Innovation, techniques are especially diverse. An adversary might employ specific techniques to compromise the firmware of an autonomous system, exploit vulnerabilities in cloud-based AI models, or manipulate sensor data from remote sensing platforms. Understanding these techniques allows security teams to identify the specific tools and methods attackers are likely to use against their unique technology. This granular insight enables the development of targeted detection rules, the hardening of specific system components, and the implementation of controls that disrupt attacker methodologies at various points. For example, if a common technique for persistence is through modifying system services, then robust monitoring and integrity checks on service configurations become a priority for new technology deployments.
Procedures: The Step-by-Step Blueprint
Procedures are the lowest level of detail within the TTP framework, describing the specific step-by-step implementation of a technique by a particular threat actor or group. These are the “what” and the “in what order.” Procedures often reveal the unique signatures or preferred methodologies of specific adversaries. For example, while “spearphishing attachment” is a technique, a procedure would detail the exact type of attachment (e.g., a macro-enabled Excel document), the social engineering lure used, the specific malware dropped, and the subsequent commands executed after successful compromise.
For security teams safeguarding cutting-edge technology, analyzing attacker procedures is invaluable. It helps in developing highly specific threat intelligence that can inform bespoke defense strategies. Knowing that a particular state-sponsored group targeting AI development firms consistently uses a specific sequence of commands after initial access, or favors certain data compression methods before exfiltration, allows for the creation of highly tuned detection and response protocols. This depth of understanding is critical for organizations that are high-value targets due to their innovative intellectual property or critical technological infrastructure, as it allows for the differentiation of common attacks from those specifically tailored to their unique systems.
TTPs in the Modern Innovation Landscape
The pace of technological innovation demands a corresponding evolution in cybersecurity strategies. New technologies like autonomous systems, advanced robotics, sophisticated AI algorithms, and widespread remote sensing capabilities introduce novel attack surfaces and require specialized defense mechanisms. TTPs are indispensable in this context because they provide a universal language for describing adversary behavior, enabling security professionals to think like attackers and anticipate threats to emerging technologies.
Securing the innovation landscape means protecting intellectual property, ensuring operational integrity, and maintaining data privacy across complex, interconnected systems. Adversaries target innovative organizations not just for financial gain but also for espionage, sabotage, and competitive advantage. Understanding their TTPs allows security architects to embed security from the design phase of new products and services. For instance, if a common TTP for a specific adversary group involves tampering with firmware or control systems, developers of autonomous platforms can prioritize secure boot mechanisms and continuous integrity monitoring. Similarly, if AI models are prone to data poisoning techniques, understanding the procedural steps an adversary might take to inject malicious data can inform robust data validation and integrity checks. This proactive, threat-informed approach ensures that security is an inherent feature, not an afterthought, in the development of next-generation technology.
Leveraging TTPs for Proactive Cyber Defense
Moving beyond reactive incident response, TTPs empower organizations to adopt a proactive stance against cyber threats. By focusing on adversary behavior rather than just their tools, security teams can anticipate attacks, hunt for threats within their networks, and design more resilient security architectures. This proactive posture is vital for protecting the delicate and often interconnected systems that characterize modern technological innovation.
Enhancing Threat Hunting and Detection
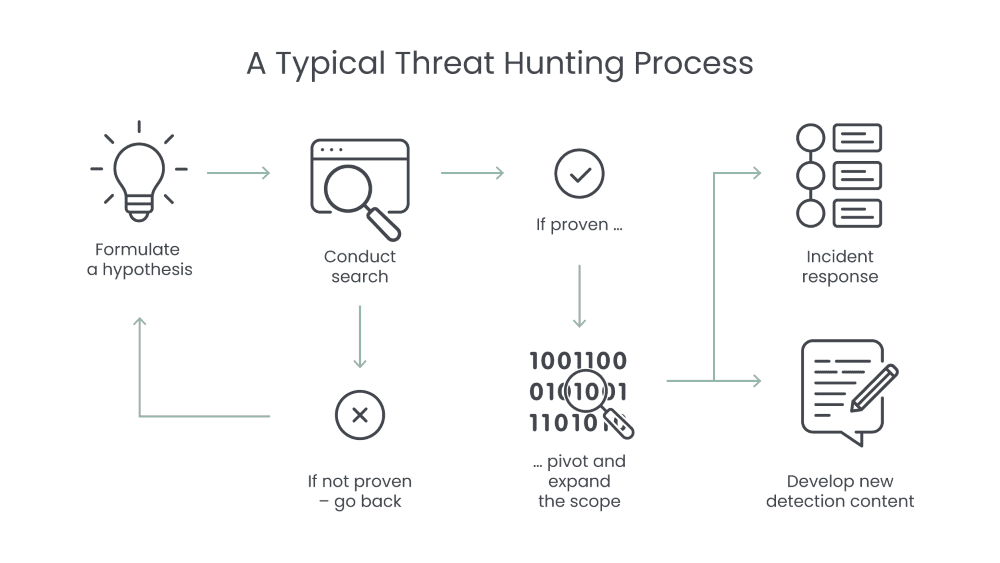
Threat hunting, the proactive search for threats that have evaded existing security controls, is significantly bolstered by TTP knowledge. Instead of waiting for an alert, threat hunters use TTPs as hypotheses. For example, if a known adversary targeting specific industry innovations often uses “Scheduled Task/Job” (a technique) for persistence, a threat hunter might actively search for unusual scheduled tasks across critical systems or autonomous vehicle control units. This approach allows security teams to uncover hidden intrusions before they cause significant damage.
For advanced detection, TTPs enable the creation of behavioral analytics that can identify malicious activity even if the specific malware variant is unknown. By monitoring for sequences of events that align with known TTPs – such as an unauthorized process attempting to access credential stores followed by network connections to unusual external IPs – security systems can flag suspicious activities that indicate an ongoing attack, rather than waiting for a definitive signature match. This is particularly effective against zero-day exploits or custom malware often deployed against high-value innovation targets.
Building Resilient Security Architectures
The insight gained from TTPs is invaluable for designing security architectures that are inherently resilient. When architects understand the common tactics and techniques adversaries use, they can implement controls that directly counter those behaviors. For instance, if “Lateral Movement” is a common tactic, network segmentation and stringent access controls become critical components of the architecture. If “Defense Evasion” through process injection is a frequent technique, then endpoint detection and response (EDR) solutions with advanced behavioral analysis become essential.
For organizations developing advanced tech, this means baking TTP-informed security into the very fabric of their platforms. Secure-by-design principles can directly address known adversary TTPs. For example, designing an autonomous system with segregated critical functions and enforcing least privilege access for internal components can directly mitigate tactics like privilege escalation and lateral movement. Regularly mapping security controls against frameworks like MITRE ATT&CK helps identify gaps in defensive capabilities and guides strategic investments in security technologies and practices.
Informing Incident Response and Recovery
When an incident does occur, a deep understanding of TTPs significantly streamlines the incident response and recovery process. Instead of merely removing malware, incident responders can analyze the TTPs employed by the attacker to understand the full scope of the breach, identify how the attacker gained access, what they did once inside, and how to prevent similar attacks in the future.
This understanding allows for more effective containment strategies. If the TTPs indicate specific methods of persistence, responders can systematically eliminate those footholds. For recovery, knowing the adversary’s TTPs helps in hardening the affected systems against recurrence and implementing stronger preventive measures. For instance, if an attack targeting a remote sensing data repository involved specific techniques for data exfiltration, the response team can focus on improving data loss prevention (DLP) measures and monitoring related network egress points more rigorously. Post-incident analysis informed by TTPs also contributes valuable intelligence back into the organization’s threat models, continuously improving overall security posture.

TTPs and the Future of Secure Technology
As technological advancements continue to accelerate, so too does the sophistication of cyber threats. The development of AI-driven autonomous systems, increasingly complex digital infrastructure for global communication, and the intricate ecosystems of remote sensing and data analysis represent the pinnacle of human innovation. Protecting these advancements from malicious actors is not merely a technical challenge but a strategic imperative.
TTPs will remain a cornerstone of this defense. They provide the necessary framework for security professionals to remain agile and adaptable in the face of evolving threats. By continuously analyzing and updating their understanding of adversary TTPs, organizations can proactively secure their innovations, ensuring the integrity, confidentiality, and availability of their cutting-edge technologies. This ongoing intelligence gathering and application of TTPs will drive the next generation of secure-by-design methodologies, advanced threat intelligence platforms, and automated defense systems. The future of secure technology hinges on our ability to understand not just what adversaries do, but how and why they do it, enabling a persistent, informed defense against all forms of cyber aggression.
