The term “TFTP server” might not be as immediately recognizable as more mainstream networking terms, but it plays a crucial role in specific scenarios, particularly within the realm of network infrastructure and device management. TFTP, or Trivial File Transfer Protocol, is a simplified version of the File Transfer Protocol (FTP). Its “trivial” nature is its key characteristic – it’s designed for speed and simplicity, sacrificing some of the robustness and security features found in more complex protocols. This makes it ideal for situations where a lightweight, efficient method of transferring small files is needed, often during the initial boot-up or configuration of network devices.
Understanding a TFTP server requires delving into its core functionalities, its common use cases, and the inherent trade-offs that come with its design. While not a tool for everyday file sharing between users, it’s an indispensable component for network administrators and device manufacturers.
The Fundamentals of TFTP Protocol
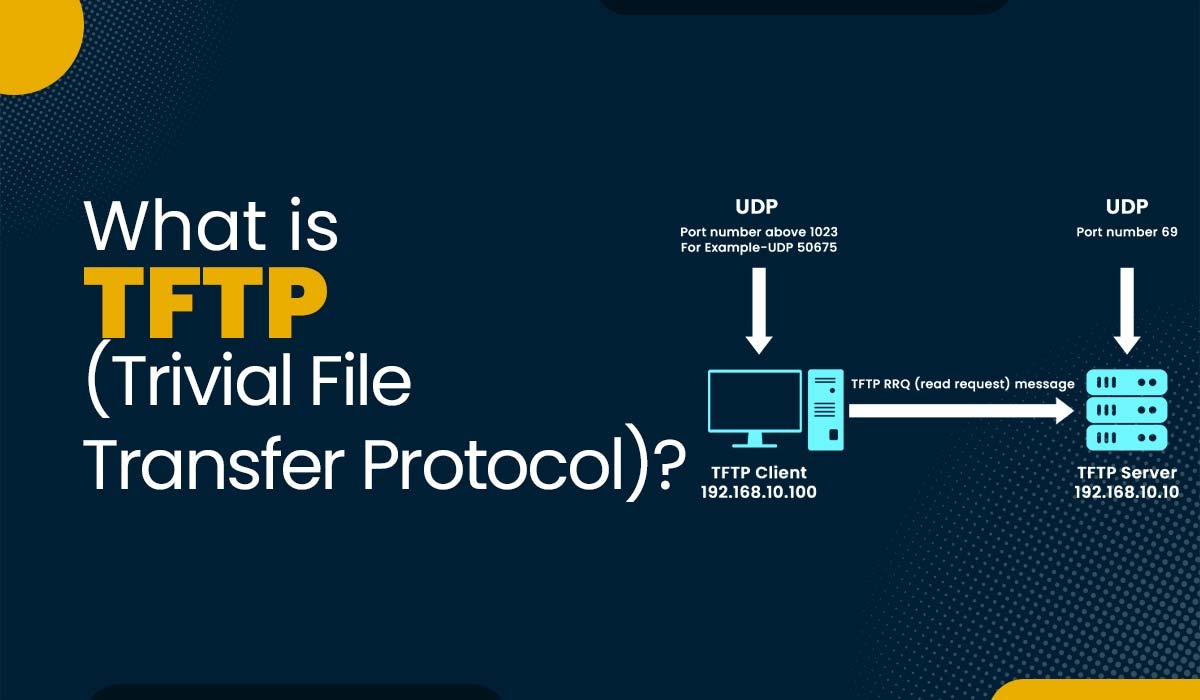
At its heart, TFTP operates on the User Datagram Protocol (UDP) rather than the Transmission Control Protocol (TCP) which FTP relies on. This choice has significant implications for its performance and reliability. UDP is a connectionless protocol, meaning it doesn’t establish a persistent connection between the sender and receiver before data transfer begins. Instead, it sends data packets independently, relying on the application layer to manage data integrity and order.
This inherent simplicity translates to several advantages:
- Speed and Efficiency: The absence of connection establishment and acknowledgments for every packet, as seen in TCP, makes TFTP significantly faster for small file transfers. This is crucial in environments where resources are limited, such as embedded systems or early boot stages of network devices.
- Low Overhead: TFTP has a minimal protocol header, further contributing to its lightweight nature. This is particularly beneficial for devices with limited processing power and memory.
However, this simplicity also comes with notable limitations:
- No Authentication: TFTP does not offer any built-in security mechanisms for verifying the identity of users or devices. This means it’s not suitable for transferring sensitive data over untrusted networks.
- No Error Checking Beyond Basic Delivery: While TFTP can detect if a packet is lost or corrupted, it doesn’t have the robust error recovery mechanisms of TCP. If a packet is lost, it’s up to the application to detect this and retransmit, which can be complex to implement.
- Limited Functionality: Unlike FTP, TFTP supports only two basic operations: reading a file from the server (RRQ) and writing a file to the server (WRQ). There are no directory listing capabilities or other advanced file management features.
- Block-based Transfer: TFTP transfers files in fixed-size blocks, typically 512 bytes. Each block is acknowledged before the next is sent. This provides a basic level of flow control and error detection but contributes to the overhead for larger files.
The TFTP protocol itself defines a set of messages that facilitate these operations. The primary message types are:
- Read Request (RRQ): Initiated by a client to request a file from the TFTP server.
- Write Request (WRQ): Initiated by a client to send a file to the TFTP server.
- Data (DATA): Sent by the server to transfer file data to the client, or by the client to transfer data to the server. Each DATA packet is numbered sequentially.
- Acknowledgment (ACK): Sent by the receiver to confirm the receipt of a DATA packet.
- Error (ERROR): Sent by the server or client to indicate an error condition, along with an error code and message.
How a TFTP Server Operates
A TFTP server, therefore, is a software application or a service running on a host that listens for TFTP requests on a specific UDP port (typically port 69). When a client sends an RRQ or WRQ request, the TFTP server processes it.
For an RRQ, the server locates the requested file and begins sending it to the client in sequential data blocks. After each block is sent, the server waits for an ACK from the client. If an ACK is not received within a timeout period, the server retransmits the last block. This process continues until the entire file has been transferred, signaled by a final DATA packet smaller than the standard block size.
For a WRQ, the server expects data blocks from the client. It receives a block, sends an ACK back to the client, and then waits for the next block. This continues until the client sends a DATA packet smaller than the standard block size, indicating the end of the file.
The simplicity of this interaction makes it ideal for scenarios where a device needs to quickly download configuration files or firmware updates during its startup phase, without the need for complex authentication or session management.
Common Use Cases for TFTP Servers
The unique characteristics of TFTP lend themselves to specific, critical applications within network management and device deployment. While not a general-purpose file transfer solution, its efficiency in certain contexts makes it indispensable.
Bootstrapping Network Devices
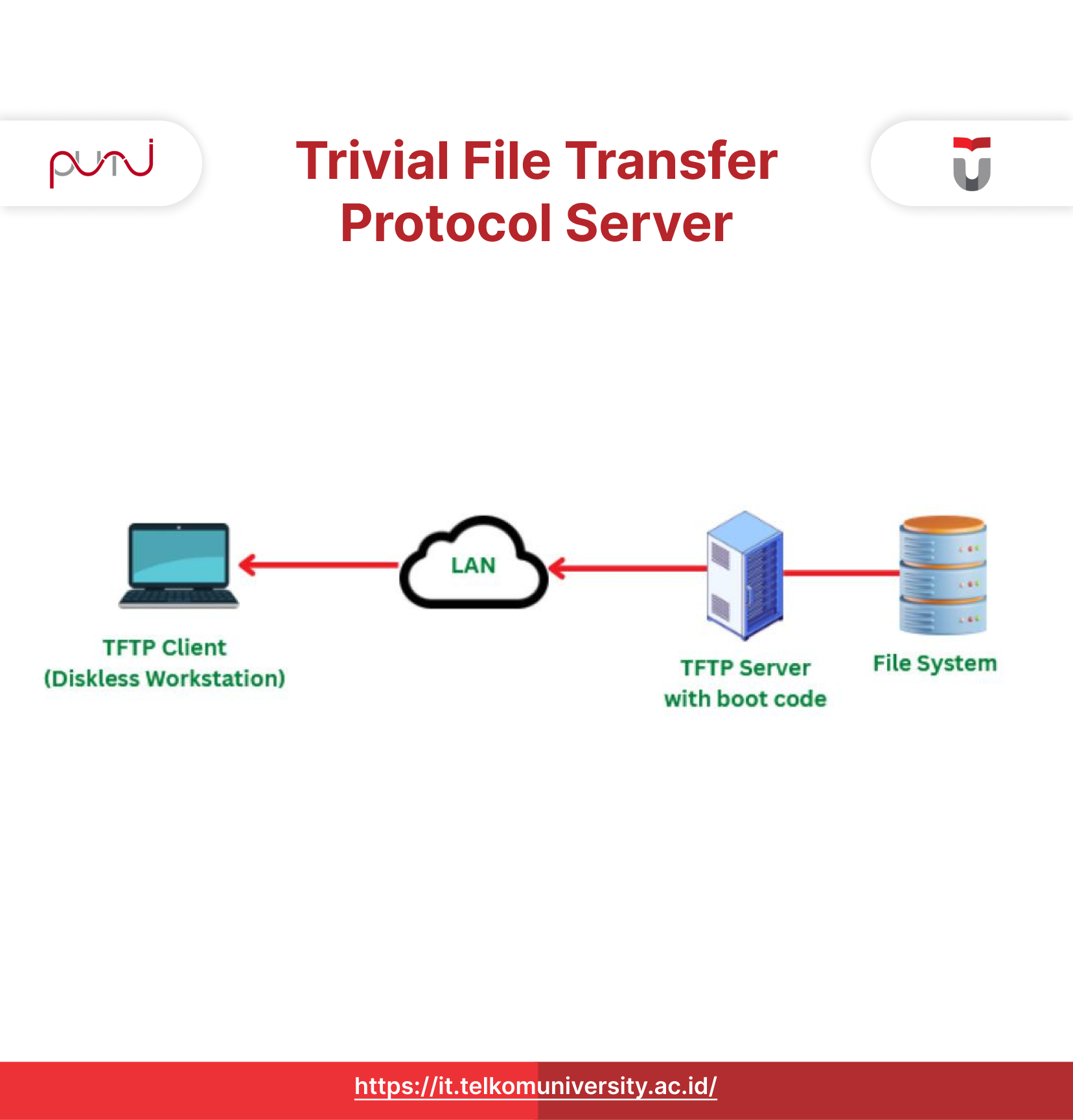
One of the most prevalent uses of TFTP servers is in the initial boot-up and configuration of network devices. When a new router, switch, or even a workstation boots for the first time or after a reset, it might not have a full operating system or configuration loaded. In such scenarios, the device can be configured to obtain its network settings and boot image from a TFTP server on the network.
- Network Booting (PXE): Preboot Execution Environment (PXE) is a standard for booting computers using a network interface. When a computer boots with PXE enabled, it sends out a broadcast request. A DHCP server responds with an IP address and the location of a TFTP server. The client then uses TFTP to download a bootloader or an entire operating system image from the TFTP server, allowing it to boot without local storage.
- Firmware Updates and Configuration Loading: Many network devices, such as routers and switches from vendors like Cisco, Juniper, and others, utilize TFTP to load their operating system images or configuration files. During the boot process, the device can be programmed to contact a designated TFTP server to fetch the necessary files, enabling it to become operational with the correct settings. This is particularly useful for mass deployments or for recovering devices that have lost their configuration.
Firmware Updates for Embedded Systems
Beyond traditional network infrastructure, TFTP servers are also commonly employed for updating the firmware of various embedded systems. These could include:
- IP Phones: Many Voice over IP (VoIP) phones use TFTP to download their configuration files and firmware updates from a central server. This simplifies the management of a large number of phones within an organization.
- Printers and Scanners: Networked printers and scanners may also use TFTP for firmware updates, ensuring they have the latest features and bug fixes.
- Other Network Appliances: A wide range of network-attached devices, from wireless access points to security cameras, can leverage TFTP for firmware management due to its simplicity and efficiency.
Disaster Recovery and System Restoration
In a disaster recovery scenario, where primary systems might be compromised or unavailable, TFTP can be a vital tool for restoring network devices to a known working state. By having a readily accessible TFTP server with boot images and essential configuration files, administrators can quickly reconfigure and bring critical network components back online. The ability to download a minimal operating system and configuration over the network is crucial when local storage might be inaccessible or corrupted.
Setting Up and Securing a TFTP Server
While the setup of a TFTP server can be relatively straightforward, the lack of inherent security features necessitates careful consideration of its deployment environment and access controls.
Installation and Configuration
The installation of a TFTP server varies depending on the operating system.
- Linux: Many Linux distributions include TFTP server packages. For example, on Debian/Ubuntu-based systems, you can install
tftpd-hpausingsudo apt-get install tftpd-hpa. The configuration typically involves specifying the directory where TFTP files will be stored (often/srv/tftpor/tftpboot) and setting up the service to start automatically. - Windows: Windows Server operating systems can host TFTP services, often through features that need to be enabled. Third-party TFTP server applications are also readily available for Windows desktops and servers.
- Network Devices: Some routers and switches have built-in TFTP server capabilities, allowing them to serve files to other devices on the network.
Regardless of the platform, the core configuration involves defining:
- The Root Directory: The directory on the server where the files to be transferred are located.
- Listening Port: TFTP operates on UDP port 69.
- Access Control (if supported): Some TFTP server implementations offer basic access control mechanisms, such as restricting access to specific IP addresses or subnets.
Security Considerations and Best Practices
The absence of authentication and encryption in TFTP makes it inherently insecure for transferring sensitive data or over public networks. Therefore, it’s crucial to implement security measures:
- Network Segmentation: Deploy your TFTP server on a trusted and isolated network segment. Avoid exposing it directly to the internet or less secure parts of your network.
- Firewall Rules: Configure firewall rules to restrict access to the TFTP server’s UDP port 69 only to authorized IP addresses or subnets that require TFTP services.
- Secure File Permissions: Ensure that the files stored in the TFTP server’s root directory have appropriate file permissions. For WRQ operations, be particularly cautious to prevent unauthorized overwriting of critical files.
- Dedicated TFTP Server: Consider using a dedicated machine or virtual machine solely for running the TFTP server. This minimizes the attack surface and potential conflicts with other services.
- Limit Read/Write Operations: If possible, configure the TFTP server to only allow read operations (RRQ) for most devices, and only enable write operations (WRQ) for specific, trusted devices during firmware update procedures.
- Regular Auditing: Periodically audit logs, if available, for any suspicious activity or unauthorized access attempts.
By adhering to these best practices, the inherent vulnerabilities of TFTP can be mitigated, allowing its efficient use for its intended purposes without compromising network security.
Troubleshooting Common TFTP Issues
When working with TFTP, encountering issues is not uncommon. Common problems and their potential solutions include:
- “Timeout” or “Connection Refused” Errors:
- Firewall Blockage: The most frequent cause. Ensure UDP port 69 is open between the client and the server.
- Incorrect IP Address/Hostname: Verify the client is trying to connect to the correct IP address or hostname of the TFTP server.
- TFTP Server Not Running: Confirm that the TFTP server process is active on the server machine.
- Network Connectivity: Check basic network connectivity between the client and server (e.g., can they ping each other?).
- “File Not Found” Errors:
- Incorrect Filename: The client request might have a typo in the filename. Case sensitivity can also be an issue depending on the server’s operating system.
- File Not in Root Directory: Ensure the requested file is located in the directory configured as the TFTP root directory on the server.
- File Permissions: On Linux systems, ensure the TFTP server process has read permissions for the requested file.
- Interrupted or Corrupted Transfers:
- Network Instability: Unstable network conditions can lead to packet loss and corrupted transfers.
- Server Resource Issues: The TFTP server might be overloaded or experiencing resource constraints.
- Client Issues: Less common, but the client’s TFTP implementation or network stack could have issues.
Effective troubleshooting often involves a combination of network diagnostics (ping, traceroute), checking server logs, and meticulously verifying configurations on both the client and server sides.
In conclusion, a TFTP server, despite its “trivial” name and limited features, remains a vital tool for specific network management tasks. Its simplicity and speed make it an efficient choice for bootstrapping devices, deploying firmware, and performing system recovery operations. By understanding its protocol, its use cases, and by diligently applying security best practices, network administrators can leverage the power of TFTP to streamline operations and maintain robust network infrastructure.
