This article, while seemingly simple, touches upon a critical aspect of digital security and personal communication that is often overlooked until it becomes a point of frustration. In an era dominated by interconnected devices and cloud-based services, understanding how to access and secure personal digital communication channels, such as voicemail, is paramount. This exploration will delve into the nature of voicemail passwords, why they exist, how they are managed, and the common approaches to regaining access when forgotten. The underlying principles of secure authentication and the user’s responsibility in maintaining this security will be central to our discussion.
Understanding Voicemail Authentication
Voicemail, at its core, is a digital messaging system that allows callers to leave audio messages for a recipient when they are unavailable. To ensure the privacy and security of these messages, access to a voicemail box is typically protected by a password or a personal identification number (PIN). This security measure prevents unauthorized individuals from listening to private conversations or accessing sensitive information left on the voicemail.
The Role of the Service Provider
The management and security of voicemail systems are primarily the responsibility of the telecommunications service provider. Whether you are using a landline, a mobile phone from a major carrier, or a Voice over Internet Protocol (VoIP) service, the provider dictates the authentication methods and password management protocols. These can vary significantly from one provider to another.
- Initial Setup: When a voicemail service is first activated, users are often prompted to set up a unique PIN or password. This initial setup is a crucial step in securing the account. Some systems may assign a temporary, default PIN that the user is immediately required to change, while others allow for direct creation of a personalized code.
- Password Complexity Requirements: To enhance security, service providers often implement password complexity rules. These rules might include minimum length requirements, the necessity of using a combination of numbers, and sometimes even special characters, although for voicemail, numeric PINs are more common. The goal is to make it difficult for unauthorized users to guess the PIN through brute-force methods.
- Security Protocols: Service providers employ various security protocols to protect their voicemail servers from unauthorized access. This includes encryption of stored messages and secure transmission of audio data. The PIN or password acts as the key to unlock access to these protected messages.
User Responsibility in Password Management
While service providers implement security measures, the ultimate responsibility for safeguarding voicemail access lies with the user. A strong, unique, and regularly updated password is the first line of defense.
- Choosing a Strong PIN: Many users opt for easily memorable numbers, such as birthdates, simple sequences (like 1234), or repeating digits. These are highly insecure and represent a significant vulnerability. A strong PIN is one that is not easily guessable and ideally is changed periodically.
- Avoiding Default Passwords: If a service provider assigns a default PIN, it is imperative to change it immediately. These default PINs are often widely known or easily discoverable, rendering the voicemail system effectively unsecured.
- Keeping the PIN Confidential: Sharing your voicemail PIN with others, even trusted individuals, can lead to unauthorized access and potential misuse of your messages. It is akin to giving away the key to your digital mailbox.
Common Scenarios and Solutions for Forgotten Voicemail Passwords
The most frequent reason for needing to understand “what is the password for my voicemail” is, of course, forgetting it. This can be a frustrating experience, especially when urgent messages are waiting. Fortunately, service providers offer established procedures for password recovery or reset.
The “Forgot PIN” Process
Most telecommunication companies have a standardized process for users who have forgotten their voicemail PIN. This process is designed to verify the user’s identity before granting access to reset the PIN.
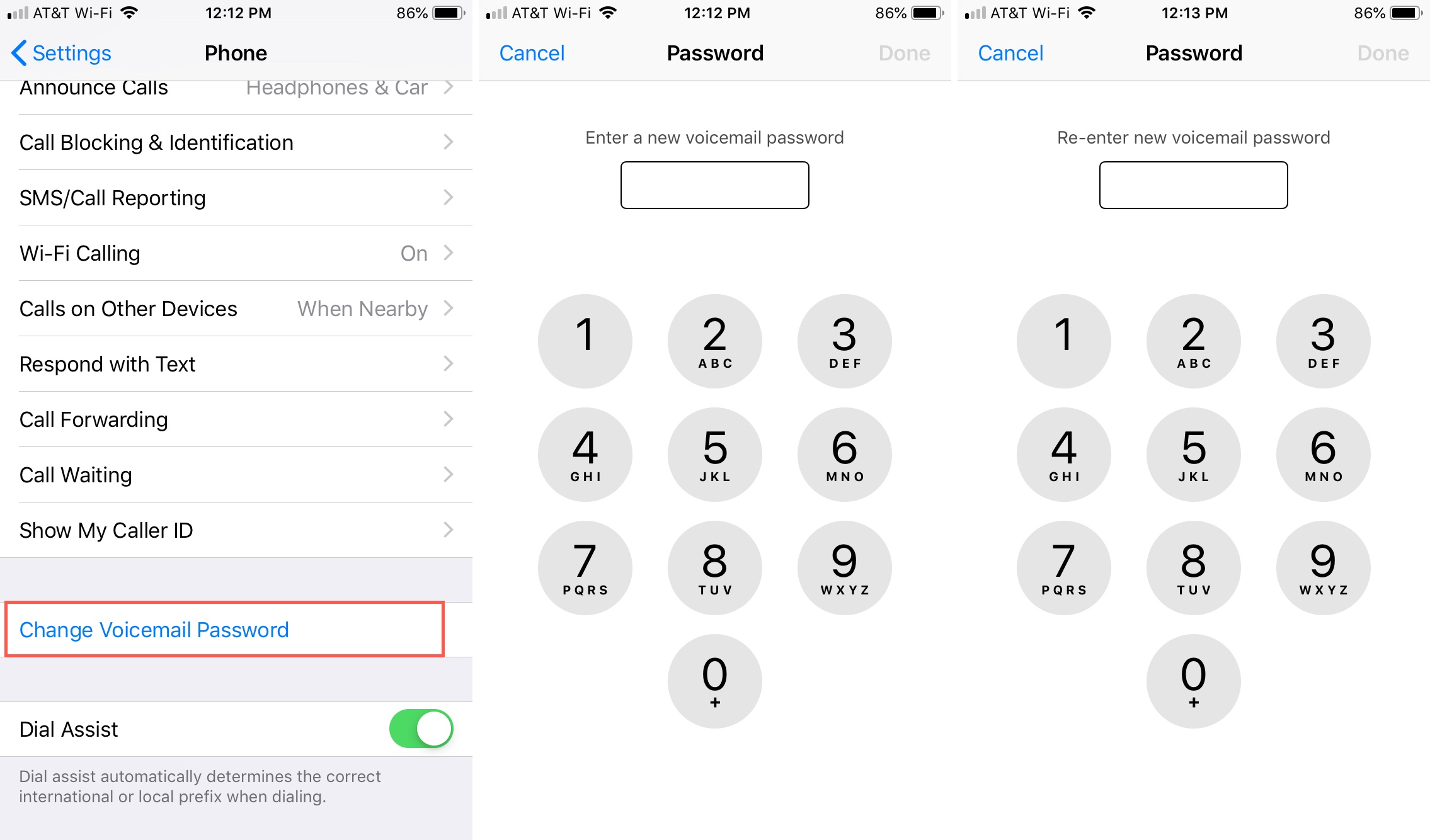
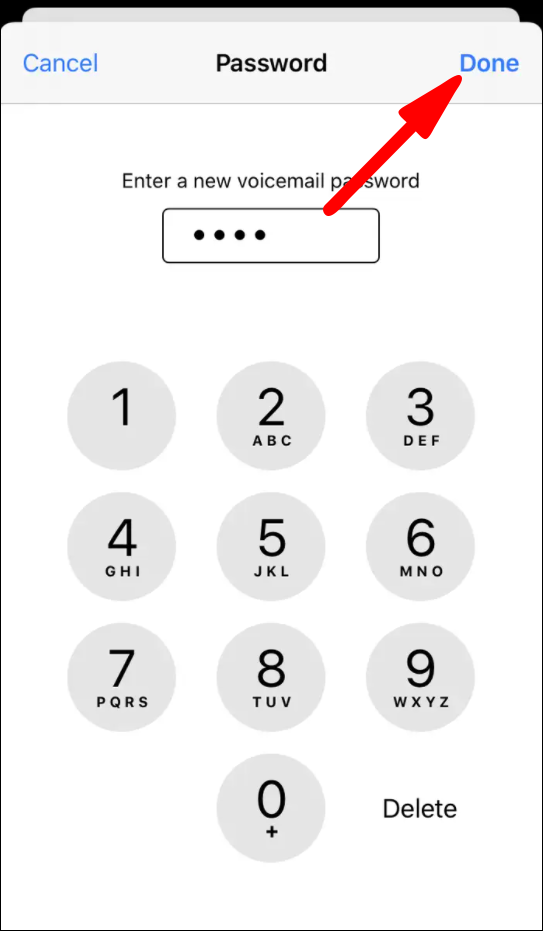
- Accessing the Reset Mechanism: Typically, this involves dialing into your voicemail system and selecting an option for forgotten PINs. Alternatively, some providers allow this through their online customer portal or mobile app.
- Identity Verification: To prevent fraudulent access, the service provider will require you to prove your identity. This usually involves answering security questions that were set up during account activation or providing specific account details. Common verification methods include:
- Account PIN/Password: The PIN or password associated with your main phone account.
- Billing Information: The last four digits of your Social Security number, a security code from your bill, or answers to pre-set security questions.
- Mobile Device Authentication: For mobile phones, the process might involve sending a temporary code to your device via SMS, or using biometric authentication (fingerprint, facial recognition) if supported by the app.
- Resetting the PIN: Once your identity is verified, you will be prompted to create a new PIN. It is essential to choose a new PIN that is strong and memorable, following the principles discussed earlier.
Direct Access via Online Portals and Apps
Modern telecommunication providers have increasingly moved towards self-service options for managing accounts, including voicemail.
- Customer Account Management: Logging into your account on the provider’s website or through their dedicated mobile application often provides direct access to voicemail settings. Here, you can usually view, change, or reset your voicemail PIN without needing to call customer support.
- Benefits of Digital Management: This method is often quicker and more convenient than traditional phone-based resets. It also allows users to manage other aspects of their phone service simultaneously.
- Security of Online Portals: It is crucial to ensure that your online account itself is secured with a strong password and, where available, multi-factor authentication (MFA). This adds an extra layer of protection to your overall account, including your voicemail settings.
When All Else Fails: Contacting Customer Support
If you are unable to reset your voicemail PIN through self-service options, or if you encounter difficulties with the verification process, contacting the service provider’s customer support is the next step.
- Gathering Account Information: Before contacting support, have all relevant account information readily available. This will expedite the process and help the representative assist you more efficiently. This may include your account number, phone number, name, and address associated with the account.
- Escalation Procedures: Customer support agents are trained to handle such requests and have access to more robust identity verification procedures if needed. They can guide you through the reset process, potentially requiring more in-depth personal information for verification.
- Patience and Persistence: While customer support can resolve most issues, it might require a degree of patience, especially during peak call times. Persistence is key if the initial interaction does not yield immediate results.
The Evolution of Voicemail Security
The concept of voicemail passwords has been a part of telecommunications for decades, but the methods of access and security have evolved significantly with technological advancements.
From Basic PINs to Advanced Authentication
Early voicemail systems often relied on simple, four-digit PINs. While functional, these were susceptible to guesswork. As technology progressed, providers began implementing more robust security measures.
- Longer PINs and Complexity: The introduction of longer PINs and requirements for mixed numeric and alphanumeric characters (though less common for voicemail) aimed to increase the difficulty of brute-force attacks.
- Account-Based Security: The integration of voicemail security with the broader mobile or landline account security became standard. This means that compromising your main account password could potentially lead to access to your voicemail.
- Biometric Authentication: For mobile devices, some applications and operating systems now support biometric authentication for accessing voicemail, such as fingerprint scanning or facial recognition. This offers a highly convenient and secure method of access, bypassing the need to remember a PIN altogether.
- Visual Voicemail and App Integration: Visual voicemail, available through many smartphone apps, often streamlines access. While a PIN might still be required for initial setup or when logging into the app from a new device, the day-to-day experience can be more seamless, with messages displayed as a list and playable directly within the app.
The Importance of Regular Security Audits
For both service providers and users, maintaining strong security practices is an ongoing process.
- Provider-Side Audits: Telecommunications companies regularly conduct security audits of their systems to identify and address potential vulnerabilities. This includes monitoring for suspicious access patterns and updating security protocols.
- User-Side Best Practices: Users should periodically review their voicemail security settings. This might involve changing the PIN every few months, reviewing security questions, and ensuring that any linked devices or apps are still authorized.
- Staying Informed: Keeping abreast of security best practices recommended by your service provider is essential. This includes being aware of potential phishing scams that might try to trick you into revealing your voicemail credentials.
In conclusion, the question “what is the password for my voicemail” often arises from a lapse in memory, but it underscores a fundamental aspect of personal digital security. Understanding how voicemail is protected, the role of the service provider, and your own responsibilities in maintaining a strong password are key to safeguarding your communications. By following best practices for password creation, utilizing available self-service reset options, and staying vigilant about security, users can ensure that their voicemail remains a private and secure communication channel.
