The Guardian of Digital Integrity in Flight Systems
In the rapidly evolving landscape of unmanned aerial vehicles (UAVs) and advanced flight technologies, security and trust are no longer afterthoughts but fundamental pillars of operational integrity. As drones become increasingly sophisticated, integrating with complex networks, and performing critical missions from delivery services to environmental monitoring, the need to safeguard their data and operational integrity intensifies. At the heart of this advanced security paradigm lies a critical component often unseen and unheard of by the end-user: the Trusted Platform Module (TPM) hardware chip. While its name might suggest a broad application, within the niche of flight technology and its interconnected systems, the TPM plays a pivotal role in establishing and maintaining a secure foundation for a drone’s entire lifecycle, from its initial boot-up to its operational commands and data transmission.
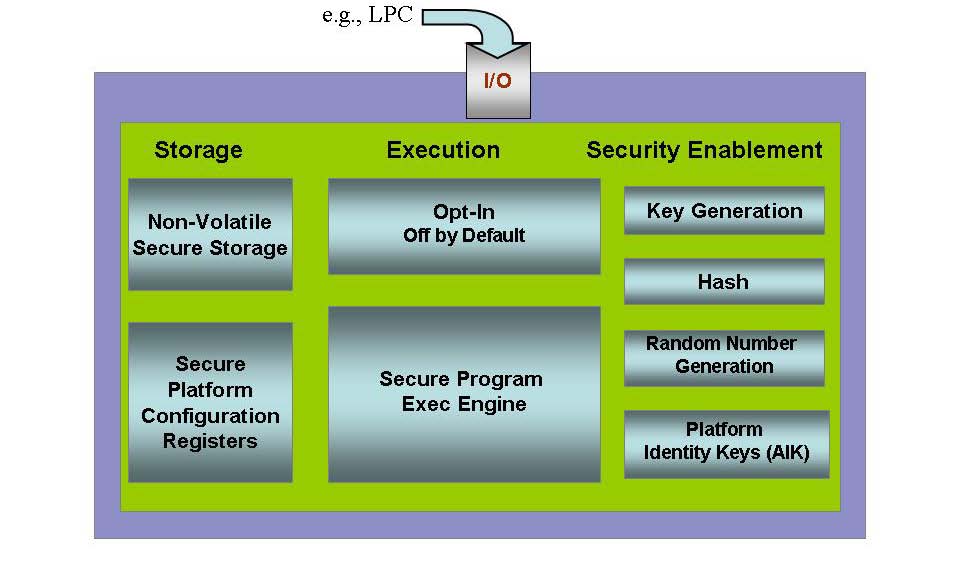
The primary function of a TPM hardware chip in flight technology revolves around providing a secure root of trust. This means it acts as a foundational element that verifies the authenticity and integrity of the drone’s firmware, software, and operating system during the boot process and throughout its operation. Think of it as a highly specialized, tamper-resistant vault embedded within the drone’s control system. This vault doesn’t store user data in the traditional sense, but rather cryptographic keys, certificates, and security-related measurements. By performing cryptographic operations and securely storing sensitive information, the TPM ensures that the drone’s software is exactly as intended by the manufacturer and has not been maliciously altered. This is crucial because any compromise in the flight control software, navigation algorithms, or communication protocols could have catastrophic consequences, leading to loss of control, data breaches, or even physical damage.
Establishing a Secure Boot Process
The journey of a drone’s operational integrity begins the moment it powers on. The secure boot process is a multi-stage verification that ensures each piece of software loaded is genuine and unaltered. The TPM is instrumental in this process by holding the cryptographic keys that sign the initial bootloader and subsequent firmware components.
The Chain of Trust
- Initial Measurement: When the drone boots, the first piece of code executed is typically a bootloader. The TPM measures this bootloader and stores a cryptographic hash (a unique digital fingerprint) of it within a protected memory area called Platform Configuration Registers (PCRs).
- Sequential Verification: As each subsequent piece of firmware or software is loaded – such as the operating system, flight control software, or navigation modules – the TPM performs a similar measurement. Each new measurement is extended into the PCRs, creating a cumulative record of what has been loaded.
- Attestation and Validation: At any point, the TPM can be queried to provide a cryptographic quote of its current PCR values. This quote, signed by the TPM’s unique private key, allows a remote server or another trusted entity to verify that the drone is running the expected, unaltered software. If the PCR values do not match the expected values, it indicates that the software has been tampered with, and the drone can be prevented from operating or flagged as compromised.
This chain of trust is fundamental for preventing sophisticated cyberattacks that aim to inject malicious code to take control of a drone, disrupt its flight path, or exfiltrate sensitive data. For applications like critical infrastructure inspection, aerial surveying, or public safety operations, the integrity of the drone’s software is paramount.
Protecting Sensitive Data and Cryptographic Keys
Beyond verifying the boot process, the TPM serves as a secure enclave for storing and managing cryptographic keys. In the context of flight technology, these keys are not just for authentication but also for encryption, digital signatures, and secure communication.
Secure Key Storage and Management
The TPM’s ability to store private keys securely, without exposing them to the main processor or system memory, is a game-changer for drone security.
On-Chip Cryptographic Operations

- Root Key Storage: The TPM typically contains a hardware-generated, unique primary storage root key (SRK) that is bound to the specific TPM chip. This SRK is never exposed and is used to encrypt other keys stored within the TPM.
- Key Derivation and Usage: When a specific cryptographic operation is needed, such as signing a command or decrypting a received message, the relevant key is “unsealed” or derived within the TPM itself. The operation is performed on the key inside the TPM, and only the resulting ciphertext or signature is released. The private key itself never leaves the secure confines of the TPM.
- Certificate Storage: Digital certificates, which bind public keys to identities, can also be securely stored in the TPM. This allows the drone to authenticate itself to ground stations or other networked components and to verify the authenticity of incoming commands or data.
This secure handling of cryptographic material is vital for several reasons:
- Preventing Key Extraction: If an attacker gains physical access to the drone or compromises its operating system, they cannot extract the private keys necessary for authentication or encryption. This significantly mitigates the risk of impersonation or decryption of sensitive flight data.
- Secure Communication: Drones often communicate wirelessly with ground control stations or other networked systems. The TPM can be used to establish secure communication channels using protocols like TLS/SSL, ensuring that commands are not intercepted and modified, and that data transmitted from the drone (e.g., sensor readings, video feeds) is protected from eavesdropping.
- Secure Software Updates: The integrity of software updates is critical. By using keys stored in the TPM to verify the digital signature of an update package, the drone can ensure that it is installing legitimate, manufacturer-provided firmware and not a malicious payload.
Enhancing Platform Integrity and Resilience
The TPM’s role extends beyond mere key management; it actively contributes to the overall integrity and resilience of the flight platform by providing mechanisms for secure identity, privacy, and protection against physical tampering.
Secure Identity and Remote Attestation
In complex drone operations, especially those involving multiple drones working collaboratively or integrated into larger air traffic management systems, a secure and verifiable identity for each drone is essential.
Verifiable Drone Identity
- Unique Hardware Identity: Each TPM chip has a unique, hardware-bound endorsement key (EK). This EK can be used to generate a unique identity for the drone.
- Remote Attestation: As mentioned earlier, the TPM’s ability to perform remote attestation allows a central authority or operator to continuously verify that the drone’s software and hardware configuration is legitimate and has not been compromised. This is crucial for maintaining situational awareness and ensuring that only trusted, properly functioning drones are allowed to operate in controlled airspace.
- Privacy Considerations: While the TPM provides a strong identity, it also supports privacy-preserving mechanisms. For instance, certain attestation processes can be designed to reveal only the necessary information about the platform’s state without exposing sensitive details that could be used for tracking or profiling.
Protection Against Physical Tampering
The physical security of a drone is a significant concern, particularly if it is operating in potentially hostile environments or is susceptible to theft or unauthorized access.

Tamper-Resistant Design
- Hardware-Based Security: TPMs are designed with physical security measures to resist tampering attempts. This can include features like voltage and temperature sensors, cryptographic countermeasures against side-channel attacks, and physical epoxy encapsulation that makes it difficult to extract the chip or its contents without destroying it.
- Secure Storage of Critical Data: In the event of a physical compromise, such as a drone being captured, the TPM can be configured to “zeroize” or erase sensitive keys and data, rendering the drone’s secure components useless to an attacker. This is a critical defense mechanism for high-value or mission-critical drones.
In conclusion, while the TPM hardware chip might operate in the background, its function within flight technology systems is profoundly significant. It is the silent guardian that ensures the integrity of the drone’s software, the security of its cryptographic keys, and the authenticity of its identity. As drones become increasingly integrated into our airspace for a myriad of applications, the robust security provided by TPMs will be indispensable in building trust, enabling advanced autonomous capabilities, and ensuring the safe and reliable operation of these powerful aerial platforms. Its role in establishing a root of trust is foundational, making it a critical component in the architecture of secure and resilient flight technology.
