In the rapidly evolving landscape of unmanned aerial vehicles (UAVs) and remote sensing, data integrity is the silent backbone of every successful mission. Whether you are performing high-precision mapping, executing autonomous flight paths, or updating critical flight controller firmware, the digital information being transmitted must remain uncorrupted. At the heart of this data verification process lies the cryptographic hash function, most notably the Message Digest Algorithm 5, or MD5. For tech enthusiasts and drone engineers, understanding the specifics of this tool—starting with the fundamental question: “What is the length of an MD5 hash output?”—is essential for maintaining the reliability of modern aerial systems.
The Anatomy of an MD5 Hash: Understanding the 128-Bit Standard
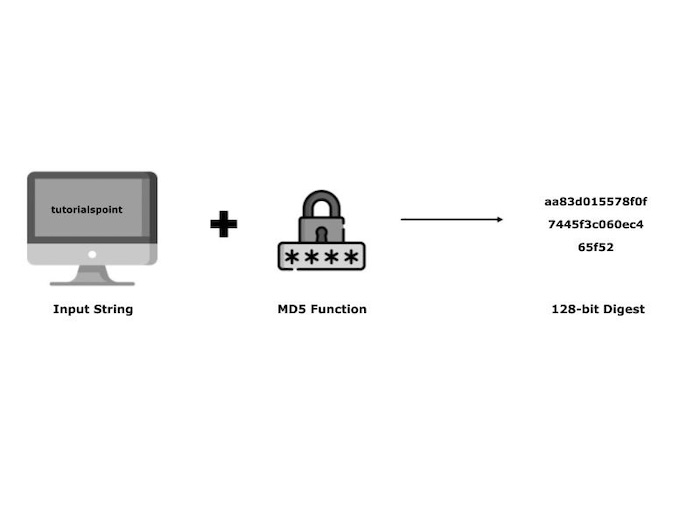
To answer the primary question directly: the length of an MD5 hash output is always 128 bits. Regardless of the size of the input data—be it a tiny 1-kilobyte configuration file for a racing drone or a massive 10-gigabyte orthomosaic map generated via remote sensing—the MD5 algorithm will always produce a fixed-length “fingerprint.”
Bit Length vs. Character Length
While the internal mathematical representation of the hash is 128 bits, most drone developers and tech innovators interact with the hash in its hexadecimal format. In this format, the 128-bit binary string is converted into a 32-character string consisting of numbers (0-9) and letters (a-f). This 32-character output is what you will typically see listed as a “checksum” on a firmware download page or within a drone’s log analysis software.
The Fixed-Length Property in Tech Innovation
The beauty of the MD5 algorithm in tech innovation is its consistency. In the world of autonomous flight and AI-driven mapping, systems need to process data quickly. Having a fixed-length output allows software developers to allocate specific memory spaces for these hashes, ensuring that verification processes are computationally efficient. Whether the drone is identifying a “follow-me” target or validating a GPS waypoint file, the 32-character MD5 hash provides a uniform method of identification that does not fluctuate with the complexity of the task.
MD5 in Drone Tech: Ensuring Firmware Integrity and Flight Safety
In the niche of Tech & Innovation within the drone industry, safety is paramount. One of the most critical applications of the MD5 hash is in the verification of firmware. When a drone manufacturer releases an update for a flight controller or a remote sensing payload, they provide an MD5 checksum alongside the download link.
Why Checksums Matter for Autonomous Systems
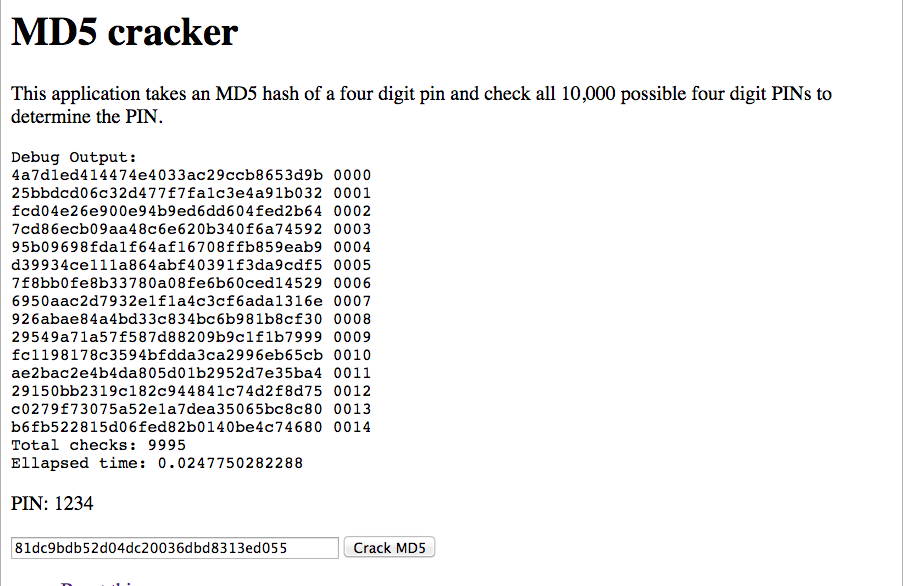
Autonomous drones rely on millions of lines of code to interpret sensor data and make real-time flight decisions. If a firmware file is corrupted during a download—perhaps due to a glitchy internet connection or a packet loss—the drone could behave unpredictably, leading to a “flyaway” or a catastrophic crash. By running the downloaded file through an MD5 generator, the user can compare the resulting 32-character string with the one provided by the manufacturer. If even a single bit of the firmware has changed, the hash will be entirely different, signaling that the file is unsafe to flash to the drone.
Verifying Remote Sensing and AI Models
Modern drones often carry onboard AI models for real-time object detection and obstacle avoidance. These models are large, complex files. When pushing updates to a fleet of enterprise drones, innovation-led companies use MD5 hashes to ensure that every unit in the field is running the exact same version of the AI model. This uniformity is crucial for fleet management and ensures that the “AI Follow Mode” behaves consistently across different hardware units.
The Role of Hashing in Mapping and Large-Scale Data Acquisition
Drone mapping and remote sensing represent some of the most data-intensive activities in the tech world. A single mission can generate thousands of high-resolution images, LIDAR point clouds, and multispectral data. Managing this data requires robust verification protocols.
Securing Telemetry and Log Files
Every time a drone flies, it generates a telemetry log—a record of its speed, altitude, battery health, and GPS coordinates. For professional surveyors and accident investigators, the integrity of these logs is non-negotiable. MD5 hashes are often used to “seal” these log files upon completion of a flight. By generating a 128-bit hash of the log at the moment the drone lands, organizations can later prove that the data has not been tampered with or edited, providing a digital “chain of custody” for drone-collected evidence.
Data Deduplication in Mapping Projects
Innovation in cloud-based drone mapping involves processing terabytes of imagery. To save storage space and bandwidth, many platforms use MD5 hashes for data deduplication. Since the MD5 hash is a fixed 32 characters, the system can quickly index and compare hashes of uploaded images. If two images have the exact same hash, the system knows they are identical copies, allowing it to store only one version and save significant computational resources during the photogrammetry process.
Security Considerations and Modern Alternatives in Drone Innovation
While the MD5 hash is a staple in the tech world due to its speed and 128-bit efficiency, it is important for drone innovators to understand its limitations, particularly regarding security.
The Vulnerability of MD5: Collisions
In the context of high-level cryptography, MD5 is no longer considered “secure” against intentional tampering. This is due to “collisions,” where two different inputs can theoretically produce the same 128-bit hash output. While this is extremely unlikely to happen by accident in a drone firmware download, a malicious actor could theoretically craft a corrupted file that mimics the MD5 hash of a legitimate update.
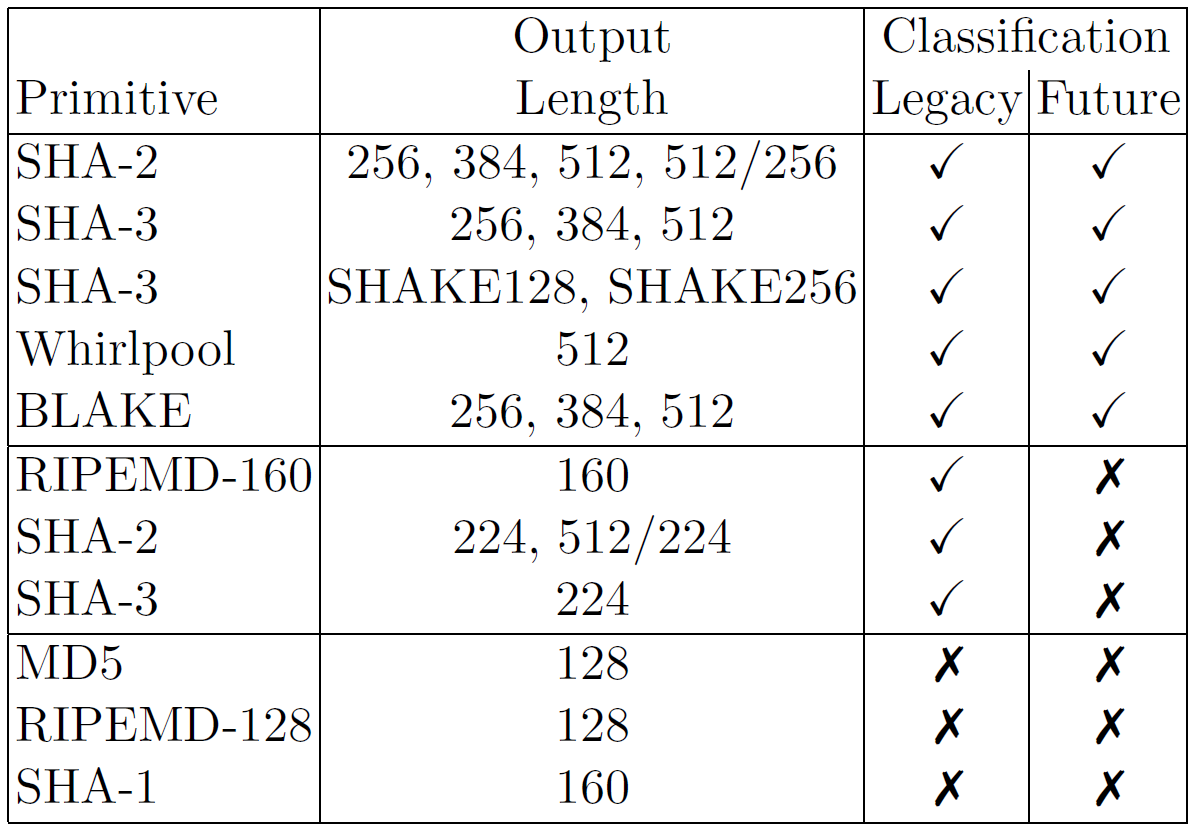
Moving Toward SHA-256 for Advanced Remote Sensing
As drone technology pushes further into the realms of government defense and sensitive infrastructure inspection, many innovators are transitioning from MD5 to SHA-256 (Secure Hash Algorithm 256-bit). As the name suggests, SHA-256 produces a 256-bit output, resulting in a 64-character hexadecimal string. This longer output provides a significantly higher level of security and a much lower probability of collisions.
However, MD5 remains the industry standard for non-security-critical tasks, such as verifying that a mapping file wasn’t corrupted during a transfer from an SD card to a laptop. Its 128-bit length offers the perfect balance between speed and reliability for everyday drone operations.
Conclusion: The Enduring Utility of the 128-Bit Hash
The question “what is the length of an MD5 hash output” opens the door to a deeper understanding of how data is managed within the drone ecosystem. The 128-bit (32-character) output of MD5 is a fundamental building block in drone tech and innovation. It provides the necessary verification for firmware that keeps our skies safe, the data integrity required for professional remote sensing, and the efficiency needed for large-scale aerial mapping projects.
As autonomous flight and AI integration continue to advance, the role of hashing will only grow. While the drone industry may eventually migrate toward longer, more secure hashes like SHA-256 for high-security applications, the MD5 hash remains a vital tool for the modern pilot and developer. By ensuring that our digital “fingerprints” are accurate, we can continue to push the boundaries of what is possible in the world of unmanned aerial technology, confident that the data guiding our drones is as precise as the flight paths they follow.
