In the ever-expanding digital landscape, the security of our personal information and online credentials has become paramount. As we navigate a world increasingly reliant on online accounts and sensitive data, robust security measures are no longer a luxury but a fundamental necessity. Apple’s macOS, renowned for its user-friendly interface and integrated ecosystem, offers a powerful, yet often understated, security feature designed to safeguard this vital information: the Keychain. Far more than a simple password manager, Keychain represents a sophisticated piece of Tech & Innovation within the Apple platform, embodying a commitment to user privacy and streamlined digital access. Understanding its capabilities is crucial for anyone looking to enhance their digital security and experience a more seamless interaction with their Mac and its connected services.
The Core Functionality of Keychain: A Digital Vault for Your Secrets
At its heart, Keychain Access is a secure, encrypted storage system built directly into macOS. It acts as a central repository for a wide array of sensitive information, ensuring that your digital identity remains protected from unauthorized access. This innovative approach to credential management moves beyond simple password storage, offering a comprehensive solution for securing everything from Wi-Fi network passwords to complex cryptographic keys. The inherent design leverages advanced encryption techniques to shield this data, making it accessible only to the authorized user through their system login credentials.
Encrypted Storage and Secure Access Mechanisms
The fundamental innovation behind Keychain lies in its robust encryption protocols. When you save an item to Keychain, whether it’s a website password, an email account credential, or a secure note, the data is not stored in plain text. Instead, it is meticulously encrypted using sophisticated algorithms. This encryption is tied to your user account and, more importantly, to your login password for the Mac. This creates a direct link between your physical access to the device and your digital access to stored information.
When you log into your Mac, your user account’s credentials are used to decrypt the Keychain data. This means that even if someone were to gain physical access to your Mac’s hard drive, they would be unable to read the contents of your Keychain without your primary login password. This layered security approach is a testament to Apple’s commitment to innovation in user data protection. The system is designed to be transparent to the user during normal operation, providing seamless access to saved credentials when needed, while remaining an impenetrable fortress in the background.
What Can Be Stored in Your Mac’s Keychain?
The versatility of Keychain extends far beyond just website passwords. Its innovative design allows it to securely store a broad spectrum of sensitive information, serving as a comprehensive digital vault for various aspects of your online and offline digital life. This breadth of functionality makes it an indispensable tool for individuals and professionals alike, streamlining access while bolstering security.
Passwords for Websites and Applications
This is arguably the most common and widely recognized use of Keychain. When you log into a website or application for the first time and choose to save your credentials, Keychain offers to store them. The next time you visit that website or launch that application, Keychain will automatically populate the login fields with your saved username and password, eliminating the need to remember and manually enter them. This feature not only enhances convenience but also encourages the use of strong, unique passwords for each service, as you no longer need to recall them all. This is a direct application of technological innovation aimed at improving user experience and security simultaneously.
Wi-Fi Network Credentials
Connecting to various Wi-Fi networks, whether at home, at work, or at public hotspots, can be a repetitive task. Keychain intelligently stores the passwords for all the Wi-Fi networks your Mac has connected to. When you are within range of a saved network, your Mac can automatically connect without requiring you to re-enter the password. This feature simplifies your daily digital interactions and ensures you’re always connected to trusted networks, all managed securely in the background.
Secure Notes and Personal Information
Beyond login credentials, Keychain can also be used to store confidential notes, software license keys, or other sensitive personal information that you wish to keep private and readily accessible on your Mac. This feature allows you to encrypt and store small pieces of text-based data that might be too sensitive for a standard text file. The secure nature of Keychain ensures that this information is protected, even if your Mac is compromised in other ways.
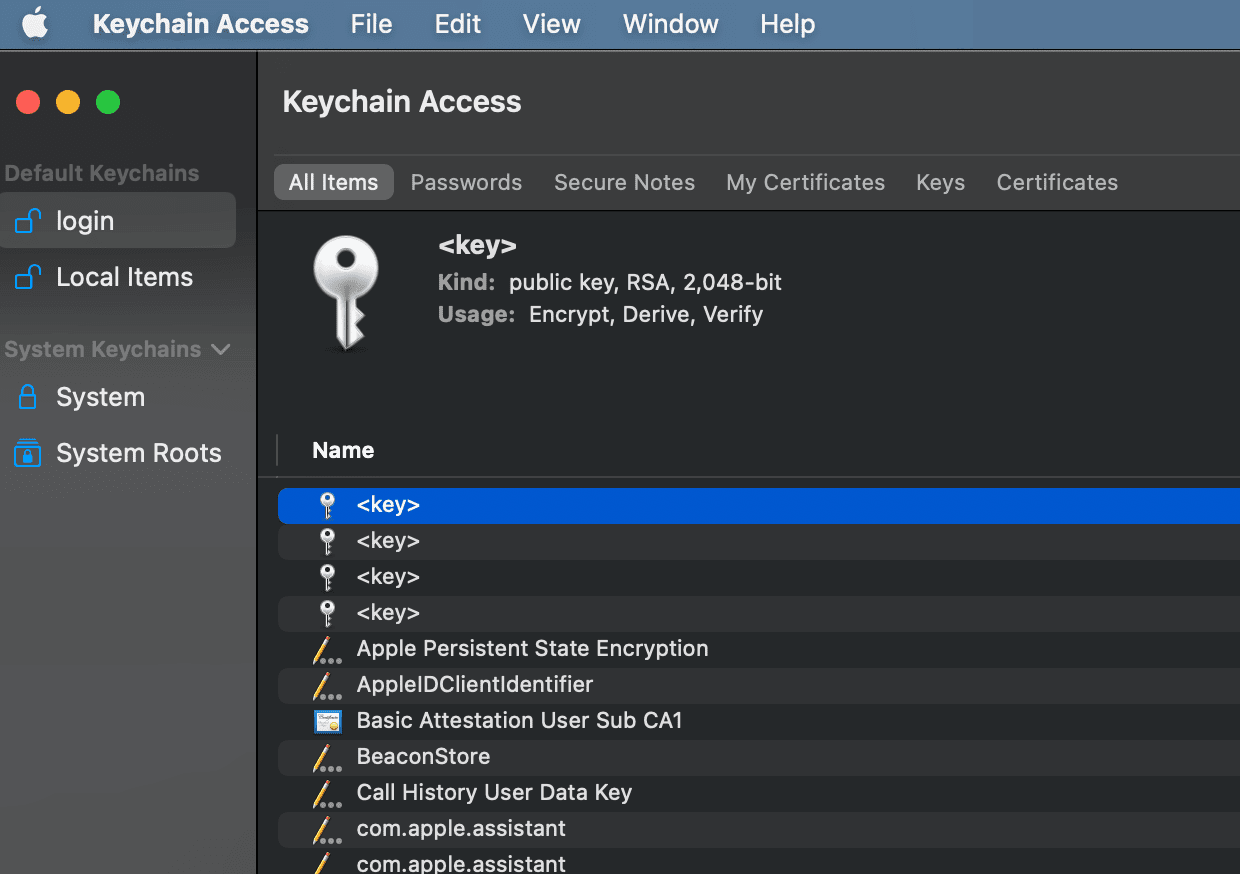
Certificates and Private Keys
For more advanced users, developers, and IT professionals, Keychain plays a critical role in managing digital certificates and private keys. These are fundamental to secure communication protocols like SSL/TLS, which are used for encrypting internet traffic. Keychain provides a secure environment for storing these cryptographic assets, ensuring that they are protected from theft or misuse, which is crucial for maintaining secure online transactions and communications. This advanced functionality highlights Keychain’s evolution as a sophisticated security innovation within macOS.
The Innovative Ecosystem Integration of Keychain
One of Keychain’s most significant strengths lies in its seamless integration across the Apple ecosystem. This isn’t just about a single feature on a single device; it’s about a harmonized approach to digital security that extends across your iPhone, iPad, and Mac. This innovative interconnectivity fundamentally changes how users manage their digital lives, offering a level of convenience and security that is difficult to replicate.
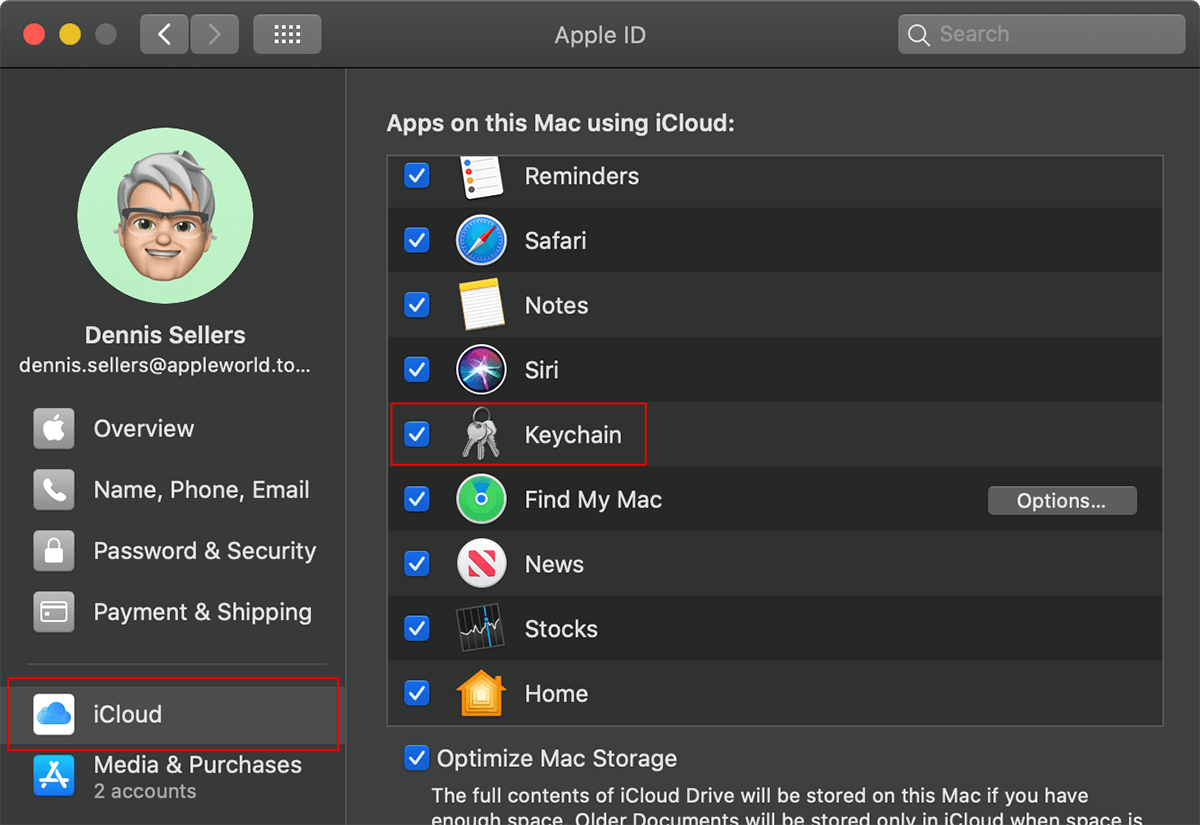
iCloud Keychain: Synchronizing Your Secrets
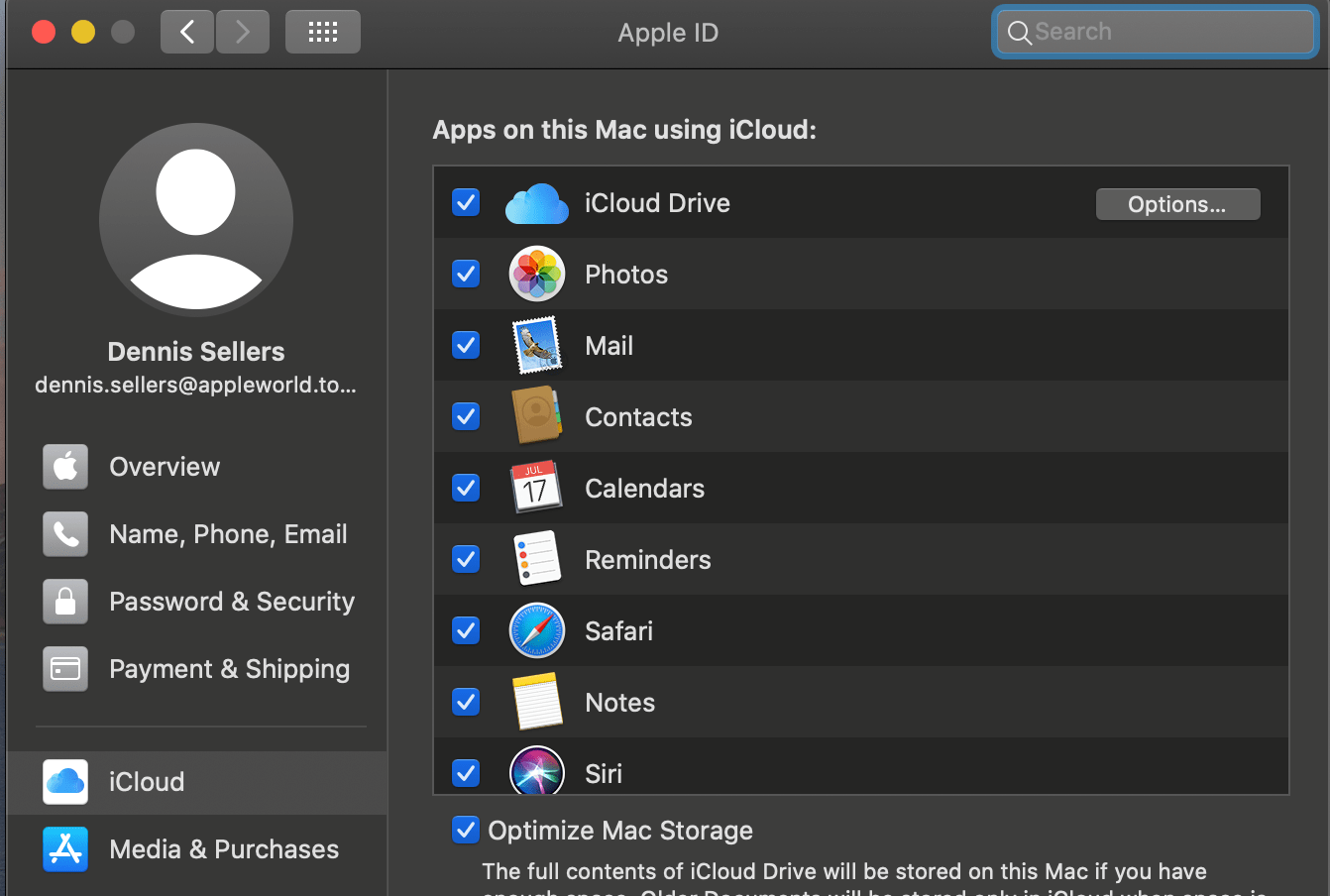
The introduction of iCloud Keychain was a major leap forward in the innovation of credential management. When enabled, iCloud Keychain securely synchronizes your Keychain data – including passwords, credit card information, and Wi-Fi network passwords – across all your Apple devices that are signed in with the same Apple ID. This means that if you save a password on your Mac, it becomes available on your iPhone and iPad almost instantly, and vice versa.
This synchronization is not a simple data transfer; it’s an encrypted and secure process. Apple uses end-to-end encryption to ensure that only you can access your Keychain data. Even Apple itself cannot decrypt and read the information stored in your iCloud Keychain. This commitment to privacy and security during synchronization is a hallmark of their innovative approach to cloud-based services. The result is a unified and secure digital experience, where your credentials are always at your fingertips, regardless of the device you are using, without compromising your security.
AutoFill and Enhanced User Experience
Leveraging the synchronized data from iCloud Keychain, macOS and iOS/iPadOS offer a sophisticated AutoFill feature for websites and apps. When you visit a login page or a form that requires personal information, your device can intelligently suggest and automatically fill in the relevant saved credentials or information from your Keychain. This significantly speeds up the login process and form completion, enhancing the overall user experience.
This innovation goes beyond mere convenience. By making it effortless to use strong, unique passwords, AutoFill, powered by Keychain, indirectly encourages better security practices. Users are less likely to resort to weak or reused passwords when the system handles the complex task of remembering and inputting them. This is a prime example of how technological innovation can subtly guide users towards more secure behaviors, making the digital world safer for everyone.
Two-Factor Authentication Integration
Keychain also plays a role in supporting and streamlining the use of two-factor authentication (2FA), a critical layer of modern digital security. While Keychain itself doesn’t perform the second factor of authentication, it can securely store the generated verification codes from authenticator apps, making them readily available for AutoFill. This further simplifies the 2FA process, ensuring that you can quickly and securely access your accounts without the friction often associated with manual code entry. This integration showcases how Keychain is evolving to support the broader security landscape.
Advanced Features and Management of Your Keychain
Beyond its core functionalities, Keychain offers a range of advanced features and management options that empower users to take greater control of their digital security. These tools allow for the fine-tuning of security settings, the management of certificates, and the ability to create distinct Keychains for different purposes, showcasing the depth of this innovative security feature.
Creating and Managing Multiple Keychains
For users who require a higher degree of organizational separation for their sensitive data, macOS allows for the creation of multiple Keychains. This is particularly useful for individuals who manage different sets of accounts for personal and professional use, or for those who work with sensitive client data and need to maintain strict segregation.
By creating separate Keychains, users can group specific passwords, certificates, and notes. For example, you might have a “Work Keychain” and a “Personal Keychain.” This allows for more granular control over access and makes it easier to manage credentials for different contexts. This feature is a testament to the thoughtful design and innovative flexibility of Keychain, catering to a diverse range of user needs and security requirements.
Managing Certificates and Identity Management
Keychain is an indispensable tool for managing digital identity and security certificates. Users can import and export certificates, view their details, and manage their trust settings. This is crucial for applications that rely on digital signatures, secure email (S/MIME), and VPN connections. By providing a secure and centralized location for these cryptographic assets, Keychain ensures the integrity and authenticity of digital interactions. This advanced capability highlights Keychain as a serious security innovation for both individuals and enterprises.
Auditing and Securing Your Keychain
macOS provides tools within Keychain Access to help users audit and secure their stored information. Users can review saved passwords, identify outdated or weak passwords, and even generate strong, unique passwords for new accounts directly through the interface. Furthermore, the system regularly prompts users to review and update saved passwords, especially if they are being used across multiple sites or are considered less secure.
Keychain also offers advanced security settings, such as the ability to require a password for accessing certain items or to set an automatic logout timer for Keychain Access. These granular controls allow users to tailor their security posture to their specific needs, further reinforcing Keychain’s role as a comprehensive and innovative security solution. The ability to proactively manage and secure your digital assets is a key aspect of modern cybersecurity, and Keychain provides the tools to do so effectively.
In conclusion, the Keychain on Mac is far more than a simple password manager; it is a sophisticated and integral component of the macOS security architecture. It represents a significant Tech & Innovation that empowers users to protect their digital lives through encrypted storage, seamless ecosystem integration, and robust management tools. By understanding and utilizing the full capabilities of Keychain, users can navigate the digital world with greater confidence, convenience, and security.
