In the rapidly evolving world of uncrewed aerial vehicles (UAVs), the humble smartphone has transformed from a mere communication device into an indispensable accessory for drone pilots. Among the array of crucial tools and components, the iPhone stands out as a central hub for mission planning, flight control, data processing, and critical communication. While external batteries power the drone and its controller, and advanced propellers enhance flight dynamics, the internal mechanisms of the iPhone itself, particularly its security features, play an equally vital role in ensuring seamless, secure, and efficient drone operations. One such foundational feature is Apple’s “Keychain.”

The iPhone as a Central Drone Accessory
Modern drone piloting, whether for recreational flight, professional aerial filmmaking, or complex industrial inspections, is deeply intertwined with smartphone technology. The iPhone often serves multiple critical functions:
- Flight Controller Interface: Many consumer and prosumer drones rely on an iPhone mounted to the remote controller to display real-time FPV (First-Person View) feeds, telemetry data, and control drone functions via a dedicated companion app.
- Mission Planning Hub: Advanced mapping and surveying applications, like Pix4Dcapture or DroneDeploy, utilize the iPhone’s processing power and GPS capabilities to design complex flight paths, define survey areas, and set autonomous mission parameters.
- Data Processing and Management: After a flight, the iPhone can be used for initial review of captured footage, basic data analysis, uploading flight logs, and managing collected imagery or sensor data.
- Regulatory Compliance Tool: Many apps facilitate pre-flight checks, airspace authorization requests, and logging flight details required by aviation authorities.
Given this extensive integration, the security and reliability of the iPhone become paramount. Every interaction, from logging into a flight planning service to connecting to the drone’s Wi-Fi network, requires secure credential management. This is precisely where the iPhone’s Keychain comes into play.
Keychain’s Role in Drone App Security
At its core, Keychain is Apple’s robust, encrypted password management and secure information storage system built directly into iOS. It’s designed to securely store usernames, passwords, Wi-Fi network credentials, secure notes, digital certificates, and other sensitive data. When an app requests access to a piece of information stored in Keychain, the system verifies the app’s identity and user authorization (often via Face ID or Touch ID) before releasing the data. For drone pilots, this capability is invaluable, safeguarding critical access points throughout their workflow.
Secure Login Credentials
Almost every significant drone-related application, from DJI Fly and Autel Sky to enterprise solutions for photogrammetry and LiDAR processing, requires user accounts. These accounts manage flight logs, synchronize settings, enable cloud storage, facilitate firmware updates, and often provide access to premium features. Remembering complex, unique passwords for each of these services can be cumbersome and lead to pilots reusing weaker passwords, thus compromising security.
Keychain eliminates this vulnerability by securely storing these login credentials. When a pilot launches a drone app, Keychain can automatically fill in the username and password with user consent (typically a biometric scan or device passcode). This not only streamlines the pre-flight setup but also significantly enhances security by encouraging the use of strong, unique passwords for every service, knowing they are safely stored and accessible only by the authorized user. This protection extends beyond basic password security, guarding against phishing attempts or simple keylogging exploits by only providing credentials to trusted applications through system-level security prompts.
Wi-Fi and Bluetooth Connections
Drones frequently connect to the pilot’s iPhone via Wi-Fi or Bluetooth for direct control, data transfer, or to access a local network for ground station operations. These network connections often require passwords. Keychain seamlessly stores these Wi-Fi network passwords, allowing the iPhone to automatically connect to the drone’s ad-hoc network or a pre-configured ground station network without manual entry. This is particularly useful in dynamic field environments where time is often critical, ensuring a quick and secure link-up between the drone and its control interface. Similarly, secure Bluetooth pairings can also leverage Keychain for credential storage if necessary, enhancing the integrity of control signals.
API Keys and Cloud Service Access
For professional drone operators engaged in mapping, surveying, or advanced data analysis, applications often integrate with third-party cloud services or utilize specific API keys to access specialized processing engines. Examples include uploading data to a cloud-based photogrammetry platform like DroneDeploy for image stitching and 3D model generation, or connecting to specialized weather forecasting APIs to assess flight conditions. Keychain can securely store these API keys or access tokens, ensuring that sensitive integration points are protected while allowing the drone apps to function seamlessly in the background without constant re-authentication. This is crucial for maintaining data integrity and preventing unauthorized access to valuable aerial data.
Beyond Logins: Securing Operational Data
The scope of Keychain’s utility extends beyond just login credentials. Its robust encryption and secure storage capabilities make it a suitable repository for other sensitive information pertinent to drone operations.
Regulatory Compliance Information
In an increasingly regulated airspace, drone pilots are often required to register their aircraft, obtain pilot licenses, and adhere to specific flight regulations. Some drone applications are designed to help pilots manage this compliance, storing drone registration numbers, pilot identification details, and certification expiry dates. Keychain can be used by these applications to securely store this personal and operational data, ensuring it is readily available for pre-flight checks or regulatory submissions while remaining protected from unauthorized access. This helps pilots stay compliant without compromising personal data security.
Encrypted Notes and Configuration
While not a primary function, certain sophisticated enterprise drone applications might leverage Keychain to store small, encrypted configuration files or sensitive operational notes directly related to specific missions. This could include encrypted details about critical infrastructure inspections, sensitive client information, or specific flight parameters that require an additional layer of security beyond standard app storage. Such data, when linked to Keychain, is protected by the device’s highest security protocols.
Digital Certificates for Secure Communication
For advanced commercial and government drone operations, ensuring secure communication channels and data authenticity is paramount. This often involves the use of digital certificates for encrypting data, verifying identities, or signing telemetry streams. Keychain is Apple’s native store for these digital certificates, allowing drone-related applications to securely access and utilize them for establishing encrypted connections with ground control stations, secure cloud storage, or other networked systems, thereby enhancing the overall security posture of critical drone missions.
Enhancing Pilot Workflow and Data Integrity
The seamless integration of Keychain into the iOS ecosystem offers significant practical benefits for drone pilots, streamlining operations and reinforcing data integrity.
- Seamless Access: Pilots can effortlessly switch between multiple drone applications—for flight planning, actual flight control, and post-flight analysis—without the friction of repeatedly entering credentials. This reduces setup time, allowing more focus on the mission at hand.
- Reduced Cognitive Load: By offloading the burden of remembering a myriad of complex passwords, Keychain frees up mental resources for pilots to concentrate on flight safety, environmental factors, and mission objectives.
- Improved Security Posture: By enforcing strong, unique passwords through its secure suggestions and storage, Keychain significantly reduces the risk of account compromise, which could otherwise lead to unauthorized drone access, data breaches, or manipulation of flight logs.
- Data Integrity and Accountability: Secure access to drone systems and cloud platforms ensures that flight plans are executed as intended, and collected data is uploaded and stored without unauthorized alteration. This is crucial for maintaining the integrity of professional aerial surveys, inspections, and cinematic projects.
- Protection Against Device Loss/Theft: Should an iPhone be lost or stolen, the data stored in Keychain remains encrypted and inaccessible without the device passcode or biometric authentication. This provides a crucial layer of protection for sensitive drone operational data and personal accounts.
Best Practices for Keychain and Drone Safety
While Keychain provides robust security, its effectiveness ultimately relies on good user practices. For drone pilots, adhering to these best practices can further fortify their operational security:
- Strong Device Passcode: Keychain’s security is fundamentally tied to the iPhone’s device passcode. A strong, alphanumeric passcode is essential.
- Enable Face ID or Touch ID: Biometric authentication provides quick, secure, and convenient access to Keychain items, adding an immediate layer of protection.
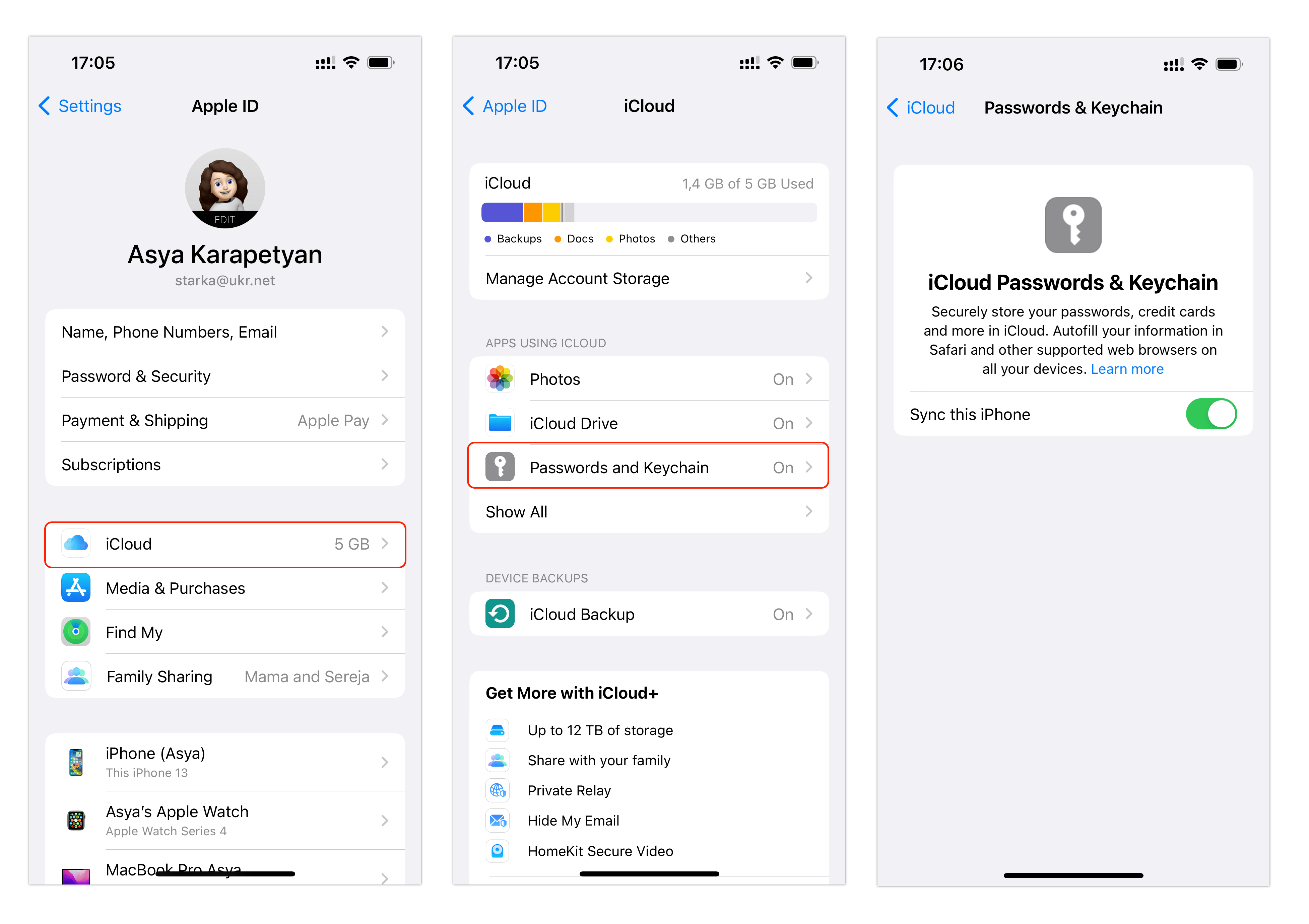
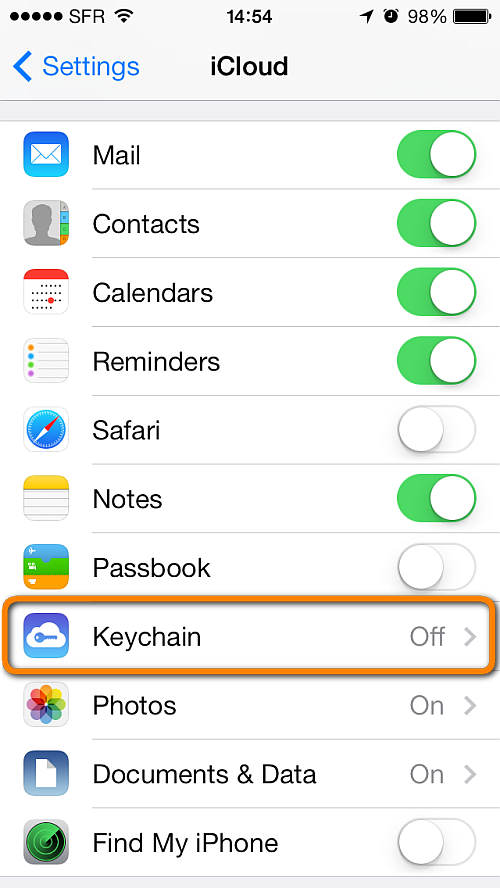
- Utilize iCloud Keychain Judiciously: iCloud Keychain syncs your credentials across all your Apple devices. While convenient for multi-device workflows (e.g., planning on an iPad, flying with an iPhone), ensure all linked devices are equally secured.
- Regular Security Audits: Periodically review saved passwords in Keychain Access (Settings > Passwords) and update any weak or reused credentials.
- Mindful App Permissions: Be aware of which apps you grant access to your Keychain, ensuring they are trusted drone applications.
- Enable Two-Factor Authentication (2FA): Even with Keychain, 2FA adds an indispensable second layer of security for critical drone accounts and cloud services, protecting against scenarios where a password might be compromised through other means.
In conclusion, the iPhone, as a versatile and powerful drone accessory, becomes an even more secure and efficient tool thanks to the underlying capabilities of Keychain. By safeguarding the myriad of credentials and sensitive data required for modern drone operations, Keychain ensures that pilots can focus on the skies, confident that their digital access points are robustly protected.
