In the digital age, the security of our personal computers is paramount. As we increasingly rely on our PCs for everything from online banking and remote work to entertainment and personal communication, the threat landscape has evolved dramatically. Malicious actors are constantly developing new and sophisticated methods to compromise our systems, steal our data, and disrupt our digital lives. This necessitates robust and comprehensive protection. When searching for “the best PC protection software,” it’s crucial to understand that no single solution is universally “best” for everyone. The ideal choice depends on a multitude of factors, including individual user needs, technical proficiency, budget, and the specific types of threats one is most concerned about.
PC protection software, often referred to as antivirus or anti-malware software, is designed to detect, prevent, and remove malicious software, commonly known as malware. This encompasses a broad spectrum of threats, including viruses, worms, Trojans, ransomware, spyware, adware, and more. Beyond just basic virus detection, modern PC protection suites offer a layered defense, incorporating features like firewalls, phishing protection, exploit prevention, identity theft protection, and secure browsing tools. Navigating the vast array of options can be overwhelming, but by breaking down the key features and considerations, we can make a more informed decision.
Understanding the Evolving Threat Landscape
The digital world is a dynamic and ever-changing environment, and the threats lurking within it are no exception. Understanding the nature and evolution of these threats is the first step in selecting the most effective PC protection software. What was considered a primary concern a decade ago might be a secondary threat today, superseded by newer, more insidious forms of attack.
The Proliferation of Malware Variants
Malware is no longer a monolithic entity. It has fragmented into a diverse and rapidly evolving ecosystem of malicious programs, each designed with specific objectives.
Viruses and Worms: The Classic Threats
While perhaps less prevalent than some newer threats, traditional viruses and worms still pose a significant risk. Viruses attach themselves to legitimate files and spread when those files are executed, while worms are self-replicating and can spread across networks without user interaction. Their primary aim is often data corruption or system disruption.
Trojans: The Deceptive Infiltrators
Trojans, named after the mythical Trojan Horse, are disguised as legitimate software or files. Once installed, they can perform a variety of malicious actions, including creating backdoors for remote access, stealing sensitive information, or downloading other malware onto the system.
Ransomware: The Digital Extortionist
Ransomware has become one of the most feared and impactful forms of malware. It encrypts a victim’s files, rendering them inaccessible, and demands a ransom payment for the decryption key. The financial and operational disruption caused by ransomware attacks can be devastating for both individuals and organizations.
Spyware and Adware: The Intruders of Privacy and Peace
Spyware operates stealthily, collecting information about a user’s activities without their knowledge or consent. This can include browsing history, login credentials, and financial details. Adware, while often less malicious, bombards users with unwanted advertisements, often interfering with their browsing experience and potentially leading to further security risks.
Fileless Malware: The Ghost in the Machine
A particularly insidious threat, fileless malware operates directly in a computer’s memory, leaving no trace on the hard drive. This makes it incredibly difficult for traditional signature-based antivirus programs to detect. It often exploits legitimate system tools and processes to execute its malicious payload.
The Rise of Sophisticated Attack Vectors
Beyond the types of malware, the methods used to deliver and execute these threats have also become more advanced and targeted.
Phishing and Social Engineering: Exploiting Human Psychology
Phishing attacks, often delivered via email or malicious websites, aim to trick users into divulging sensitive information such as usernames, passwords, and credit card numbers. These attacks are increasingly sophisticated, mimicking legitimate communications and exploiting users’ trust. Social engineering broadly encompasses any tactic that manipulates people into performing actions or divulging confidential information.
Zero-Day Exploits: The Unpatched Vulnerabilities
Zero-day exploits leverage previously unknown vulnerabilities in software or hardware. Because these vulnerabilities are unknown to the vendor, there are no patches or defenses available when the exploit is first used, making them extremely dangerous.
Advanced Persistent Threats (APTs): Targeted and Enduring Attacks
APTs are sophisticated, long-term, and targeted attacks, typically orchestrated by nation-states or organized criminal groups. They aim to gain and maintain unauthorized access to a network, often to steal sensitive data or conduct espionage.
Key Features to Consider in PC Protection Software
Given the diverse and evolving nature of cyber threats, effective PC protection software must offer a multi-layered approach. A comprehensive suite will go beyond basic virus scanning to provide a robust shield against a wide range of digital dangers.
Core Malware Detection and Prevention
At the heart of any PC protection software lies its ability to detect and neutralize malware. Modern solutions employ several advanced techniques to achieve this.
Signature-Based Detection: The Foundation of Antivirus
This traditional method relies on a vast database of known malware signatures. When a file is scanned, its signature is compared against this database. If a match is found, the file is flagged as malicious. While effective against known threats, it struggles with new or polymorphic malware.
Heuristic Analysis: Detecting the Unknown
Heuristic analysis examines the behavior and characteristics of files to identify suspicious patterns that might indicate malware, even if a specific signature isn’t present in the database. This helps in detecting novel or modified threats.
Machine Learning and AI: The Predictive Power
Advanced PC protection software increasingly leverages machine learning and artificial intelligence. These technologies analyze vast amounts of data to identify patterns and predict potential threats before they even manifest. This allows for proactive defense against zero-day exploits and evolving malware.
Real-Time Scanning: Constant Vigilance
Real-time scanning ensures that files are checked for malware as they are accessed, downloaded, or executed. This provides immediate protection and prevents malicious code from infiltrating the system in the first place.
Essential Security Suites: Beyond Antivirus

Modern PC protection is not just about antivirus; it’s about a comprehensive security ecosystem designed to safeguard your digital life.
Firewall Protection: The Digital Gatekeeper
A firewall acts as a barrier between your computer and the internet, monitoring and controlling incoming and outgoing network traffic. It can block unauthorized access attempts and prevent malicious programs from communicating with external servers. Both software and hardware firewalls exist, but integrated software firewalls within security suites offer convenient, system-wide protection.
Web Protection and Phishing Prevention: Navigating the Web Safely
These features actively scan web pages for malicious content and known phishing sites. They can block access to dangerous websites, warn users about potential threats, and protect against drive-by downloads, which are malware downloads that occur without the user’s explicit consent.
Ransomware Protection: A Dedicated Defense
Given the significant threat posed by ransomware, many security suites offer dedicated ransomware protection modules. These typically work by monitoring for suspicious file encryption activities and isolating or rolling back any unauthorized changes.
Identity Theft Protection and Password Management: Safeguarding Your Personal Data
Some advanced suites include features to help protect your identity online. This can involve monitoring your personal information for signs of compromise, providing secure password management tools to generate and store strong, unique passwords for all your online accounts, and sometimes even offering credit monitoring services.
Secure Browsing and Online Banking Tools: Encrypting Your Transactions
These tools enhance the security of your online activities, particularly when it comes to sensitive transactions like online banking or shopping. They can encrypt your connection, prevent keyloggers from capturing your keystrokes, and ensure that your browsing sessions are private and secure.
Evaluating and Choosing the Right PC Protection Software
With numerous options available, each claiming to be the best, the selection process requires careful evaluation based on specific needs and preferences.
Performance and System Impact: The Balance Between Security and Speed
A common concern with PC protection software is its impact on system performance. A highly effective solution shouldn’t significantly slow down your computer.
Resource Consumption: CPU, RAM, and Disk Usage
When evaluating software, pay attention to its resource consumption. Does it hog your CPU or RAM, leading to noticeable slowdowns? Many reputable antivirus programs have optimized their resource usage over the years, but it’s still a factor to consider, especially on older or less powerful machines.
Scan Times: Efficiency in Detection
The time it takes for a full system scan can vary. While thoroughness is important, excessively long scan times can be inconvenient. Look for software that balances comprehensive scanning with reasonable speed.
Ease of Use and User Interface: Intuitive Security
For the average user, the software should be easy to install, configure, and use. A cluttered or confusing interface can be a barrier to effective security.
Installation and Setup: A Smooth Beginning
The initial installation process should be straightforward, with clear instructions and minimal technical hurdles.
Daily Operation and Updates: Effortless Maintenance
Once installed, the software should require minimal ongoing management. Automatic updates for virus definitions and program components are essential. The interface should provide clear status indicators and easy access to different features and settings.
Pricing and Licensing Models: Value for Money
PC protection software comes in various pricing tiers, from free versions with limited features to premium suites offering comprehensive protection.
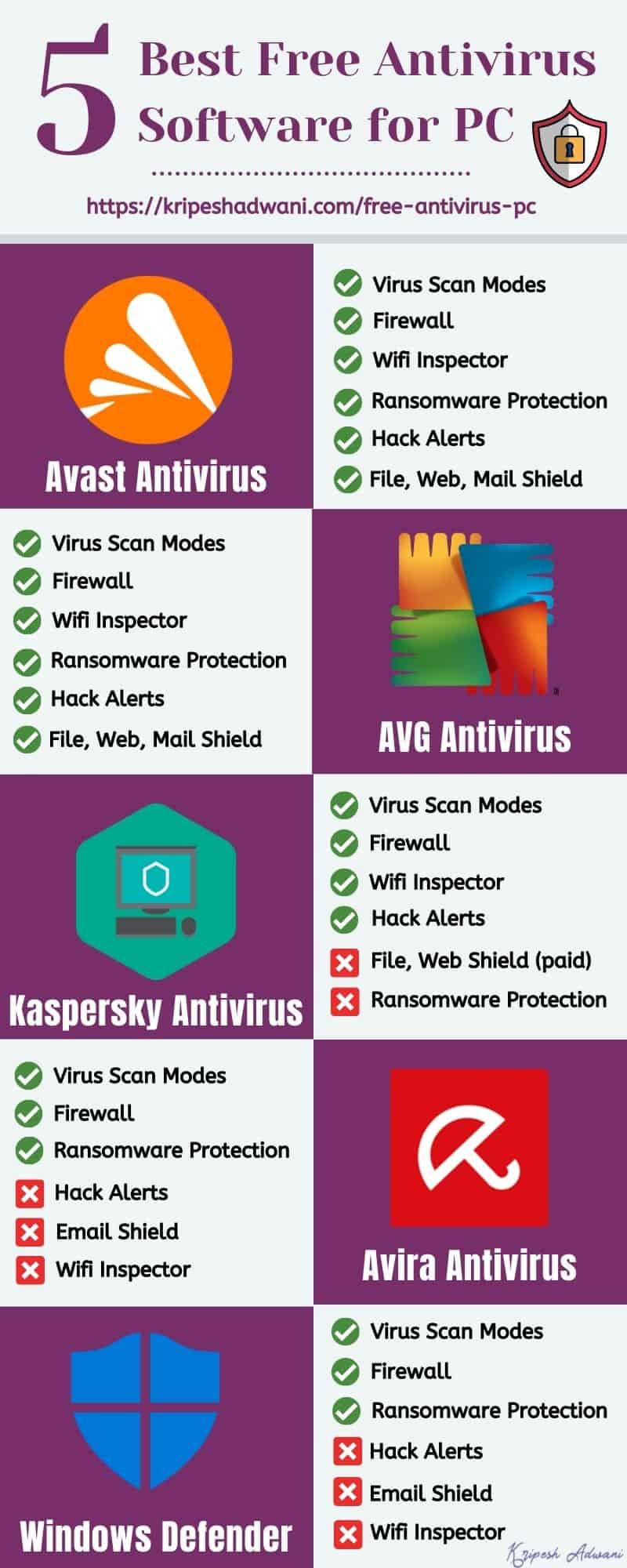
Free vs. Paid Solutions: What’s the Difference?
Free antivirus software can offer a basic level of protection, but it often lacks the advanced features found in paid versions, such as enhanced ransomware protection, identity theft tools, and dedicated customer support. Paid solutions generally provide a more robust and well-rounded security experience.
Subscription Models: Annual Renewals and Multi-Device Coverage
Most PC protection software operates on a subscription basis, typically requiring annual renewal. It’s also important to consider how many devices the license covers. Many suites offer packages that protect multiple computers, smartphones, and tablets, providing a unified security solution for your entire digital ecosystem.
Customer Support and Updates: Ongoing Reliability
Even the best software can sometimes encounter issues or require assistance. Reliable customer support and consistent updates are crucial for maintaining effective protection.
Technical Support Channels: Getting Help When You Need It
Look for providers that offer multiple support channels, such as email, phone, live chat, and a comprehensive knowledge base or FAQ section. Prompt and helpful support can be invaluable when dealing with security concerns.
Frequency and Quality of Updates: Staying Ahead of Threats
Regular and frequent updates to virus definitions are essential for keeping pace with the ever-evolving threat landscape. Beyond definitions, software updates that introduce new features or patch vulnerabilities in the protection program itself are also critical.
In conclusion, determining the “best” PC protection software is a nuanced process. It involves understanding the current threat landscape, identifying the essential features that provide a multi-layered defense, and carefully evaluating available options based on performance, usability, pricing, and support. By taking a proactive and informed approach, individuals can significantly enhance their digital security and protect their valuable data and privacy in an increasingly interconnected world.
