The Address Resolution Protocol (ARP) table, often referred to as the ARP cache, is a fundamental component of local area networks (LANs) that plays a crucial role in facilitating communication between devices. In essence, it acts as a dynamic directory, mapping IP addresses (the logical addresses used for routing across networks) to MAC addresses (the physical, hardware-bound addresses of network interface cards). Understanding the ARP table is paramount for anyone seeking to delve into the inner workings of network communication, troubleshooting connectivity issues, or gaining a deeper appreciation for the seamless flow of data on our digital highways.

The Genesis of ARP: Bridging the Logical and Physical Divide
At its core, the challenge ARP addresses is a fundamental one: how do devices on the same local network find each other when they only know each other’s logical (IP) address? While IP addresses are essential for directing traffic across the internet and between different subnets, they are not directly usable for communication at the hardware level within a single LAN segment. This is where MAC addresses come into play. Every network interface card (NIC) in every device connected to a network is assigned a unique, globally recognized MAC address by its manufacturer. These MAC addresses are what Ethernet switches and other Layer 2 devices use to physically deliver frames of data to the correct recipient.
The Role of IP Addresses in Network Communication
IP addresses, governed by protocols like IPv4 and IPv6, provide a hierarchical and logical addressing scheme. They allow for the identification and location of devices across vast and complex networks. When a device wants to send data to another device, it first determines the destination IP address. This IP address is used by routing devices (like routers) to forward the data packet towards its final destination. However, once a packet reaches the correct local network segment (the subnet), the IP address alone is insufficient for the final hop to the target device.
The Indispensable Nature of MAC Addresses
MAC addresses, on the other hand, are designed for local network delivery. They are typically burned into the hardware of the NIC and are intended to be unique and permanent. When a device needs to send data to another device on the same LAN, it must know the destination MAC address. This is because Ethernet switches, the workhorses of most LANs, operate at the Data Link Layer (Layer 2) of the OSI model and use MAC addresses to forward frames directly to the intended recipient’s port.
The ARP Resolution Process: A Dynamic Mapping
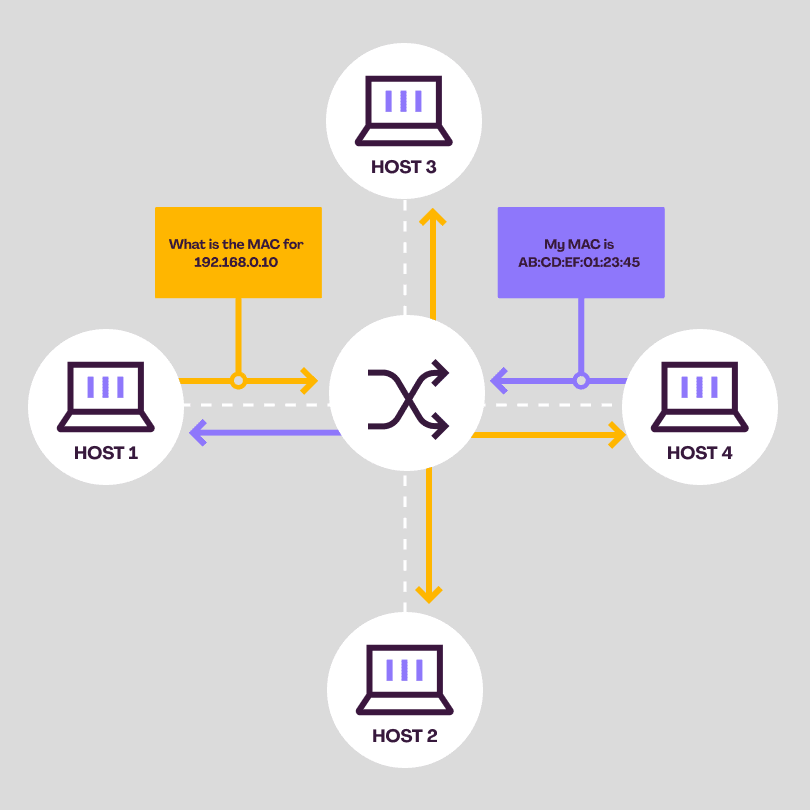
The ARP protocol acts as the bridge between these two addressing schemes. When a device, let’s call it Device A, needs to send an IP packet to another device on the same local network, Device B, and Device A doesn’t already know Device B’s MAC address, it initiates the ARP resolution process.
-
ARP Request: Device A broadcasts an ARP request packet onto the local network. This packet essentially says, “Who has the IP address [Device B’s IP address]? Tell [Device A’s IP address] your MAC address.” This broadcast is sent to all devices on the segment.
-
ARP Reply: Only the device that actually owns the requested IP address (Device B) will respond. Device B sends back an ARP reply packet directly to Device A, containing its MAC address. This reply is a unicast message, meaning it’s sent only to Device A.
-
ARP Table Population: Upon receiving the ARP reply, Device A adds an entry to its ARP table. This entry associates Device B’s IP address with its corresponding MAC address. Now, Device A can directly send IP packets destined for Device B, encapsulated within Ethernet frames addressed to Device B’s MAC address.
This process is dynamic because IP addresses can, in some network configurations, be assigned dynamically (e.g., via DHCP), and devices can join or leave the network. The ARP table needs to reflect these changes.
Understanding the Structure and Contents of an ARP Table
An ARP table is not a static file but rather a temporary cache maintained in the memory of network devices, including computers, routers, and switches. Its primary purpose is to store recent mappings of IP addresses to MAC addresses, thereby speeding up subsequent communications. Instead of initiating an ARP request every single time a device needs to communicate with another on the local network, it can simply consult its ARP table.
Key Information Stored in an ARP Entry
Each entry in an ARP table typically contains the following critical pieces of information:
- IP Address: This is the logical network address of the device for which the MAC address is known.
- MAC Address: This is the physical hardware address of the network interface card associated with the corresponding IP address.
- Interface: This indicates the network interface on the local device that is associated with this ARP entry. For instance, a computer with multiple network cards would specify which card is being used for the ARP mapping.
- State/Type: ARP entries can exist in different states. The most common are “dynamic” and “static.” Dynamic entries are learned automatically through the ARP process and have a timeout period. Static entries are manually configured by an administrator and do not expire.
- Age/Timeout: Dynamic ARP entries are not permanent. They are automatically removed from the table after a certain period of inactivity (the timeout) to ensure that stale mappings are purged. This timeout period is configurable and varies depending on the operating system and network device.
Dynamic vs. Static ARP Entries
The distinction between dynamic and static ARP entries is significant:
- Dynamic ARP Entries: These are the most common. They are created automatically by the ARP protocol when an ARP reply is received. Their purpose is to capture active mappings. They are temporary and will expire after a configurable timeout period if the mapping is not used or refreshed. This dynamic nature is essential for networks where IP addresses might change or devices are frequently added or removed.
- Static ARP Entries: In certain scenarios, administrators may choose to manually configure static ARP entries. This is typically done for specific security reasons or to ensure a permanent mapping for critical devices. For example, a static ARP entry might be configured for a network printer or a server to prevent its MAC address from being inadvertently changed or to protect against ARP spoofing attacks. Static entries do not expire and must be manually removed.
The Importance of the Timeout Mechanism
The timeout mechanism for dynamic ARP entries is crucial for network health and efficiency. Without it, ARP tables could become bloated with outdated information, leading to incorrect address mappings and communication failures. When a device’s IP address changes, or it leaves the network, its old ARP entry would ideally be removed. The timeout ensures that eventually, these stale entries are purged, allowing for new, correct mappings to be established. The typical timeout period can range from a few minutes to several hours, depending on the operating system and network configuration.
Accessing and Interpreting ARP Tables on Different Operating Systems
The ability to view and understand the ARP table is a valuable diagnostic tool for network administrators and IT professionals. Most operating systems provide command-line utilities to display the contents of the ARP cache.
Windows: The arp -a Command
On Windows operating systems, the command prompt is used to access the ARP table.
- Open the Command Prompt: Press
Windows Key + R, typecmd, and press Enter. - Execute the ARP command: Type
arp -aand press Enter.
The output will display a list of IP addresses, their corresponding physical (MAC) addresses, and the type of entry (dynamic or static). You might see entries for your default gateway, other devices on your local network, and even broadcast addresses.
Linux and macOS: The arp and ip neigh Commands
Linux and macOS, being Unix-like systems, offer similar functionalities, often with more comprehensive tools.
Using arp:
- Open the Terminal.
- Execute the command:
arp -aorarp -n(the-noption displays numerical addresses, which can be faster).
Using ip neigh (more modern and preferred on Linux):
- Open the Terminal.
- Execute the command:
ip neighorip neighbour
This command provides a more detailed view of the network neighbor cache, which includes ARP entries. The output will show the IP address, the MAC address (referred to as lladdr or link-layer address), the interface, and the state of the entry (e.g., REACHABLE, STALE, DELAY).
Troubleshooting and Security Implications of ARP Tables
The ARP table, while essential for network operations, can also be a source of connectivity problems and a target for malicious attacks. Understanding these implications is vital for maintaining a secure and functional network.
Common Network Problems Related to ARP
- Incorrect IP Address Configuration: If a device has an incorrect IP address or subnet mask, it might fail to communicate with other devices, and its ARP entries could reflect this misconfiguration.
- IP Address Conflicts: When two devices on the same network are assigned the same IP address, it can lead to unpredictable behavior and communication issues. ARP requests might be met by both devices, causing confusion and packet loss.
- ARP Cache Poisoning/Spoofing: This is a significant security vulnerability where an attacker sends forged ARP messages onto a LAN. The attacker’s goal is to associate their MAC address with the IP address of another host (like the default gateway). This effectively reroutes traffic intended for the legitimate host through the attacker’s machine, allowing them to intercept, modify, or drop data.
- Stale ARP Entries: If a device leaves the network without its ARP entry being properly purged from other devices’ caches, those devices might continue to try sending traffic to the old MAC address, leading to communication failures.

Securing Your Network Against ARP-Related Threats
ARP spoofing is a prevalent threat on local networks. Several measures can be employed to mitigate this risk:
- Static ARP Entries for Critical Devices: As mentioned earlier, configuring static ARP entries for important devices like servers and gateways makes them resistant to ARP spoofing.
- ARP Inspection (Port Security): Many managed switches offer features like Dynamic ARP Inspection (DAI). DAI intercepts ARP packets on a switch port and validates them against a trusted database of IP-to-MAC address bindings. Invalid ARP packets are dropped, preventing spoofing.
- Network Monitoring Tools: Using network monitoring tools that can detect unusual ARP activity, such as a sudden surge in ARP requests or replies, or multiple MAC addresses claiming the same IP address, can help identify potential attacks.
- Firewalls: While firewalls primarily operate at higher layers, they can help by blocking unwanted traffic that might be used to facilitate ARP spoofing.
By understanding the mechanics of the ARP table, how to inspect it, and its associated vulnerabilities, network professionals can significantly enhance their ability to troubleshoot network issues and bolster their network’s security posture. The ARP table, though often working silently in the background, remains an indispensable element of modern local area networking.
